MEDIA ALERT: IRONSCALES & SNDBOX IDENTIFY A NEW MALWARE VARIANT BEING SENT OVER EMAIL EFFECTING MS OFFICE 365 USERS
New threat uses a malicious #RTF file to infect machines with maldoc file currently going fully undetected
November 30, 2018 - TEL AVIV & ATLANTA - IRONSCALES, the world’s first automated phishing prevention, detection, and response platform and SNDBOX (aquired by OPSWAT in 2021), an artificial intelligence malware research platform, today announced that researchers have identified a new variant of the maldoc malware. Using a malicious #RTF file to infect a machine, the malware uses a known vulnerability, a CVE (sometimes can be named 1-day) to download and execute malicious files without the user consent. These vulnerabilities are catching speed on DOC files recently, as Microsoft found it hard to patch the EQNEDT32.EXE process, as they might have lost their source code for this process, thus they can’t successfully patch against attacks.
Initial analysis suggests that the attack is a variant to the known malware “Formbook,” which is a form-grabber and stealer malware written in C and x86 assembly language. It’s a ready to sell malware, that can be used by cyber-criminals who don’t have any skill in malware development. The malware uses advanced techniques for lateral movement, stealing an already executing thread of the `explorer.exe` process in order to execute their own code. This technique has already been seen in a family of malware called "Formbook.”
The exploit itself is being executed as a service, and the communication between the Service process (EQNEDT32.EXE), and office (winword.exe) is done through a windows mechanism called ALPC (sometimes RPC) - Advanced Local Procedure Call. These advanced mechanisms usually cannot be detected by antivirus, as there is no simple way to monitor for them.
SNDBOX have crucial hooks on the kernel, allowing researchers to see all ALPC traffic on the system. When integrated with the IRONSCALES advanced phishing threat protection platform, researchers were able to identify these specific types of files, which are actually very evasive for simple antivirus programs.
MALWARE FAST FACTS:
When was the malware first discovered? November 30, 2018
Who discovered the malware variant? Researchers from SNDBOX and IRONSCALES’ advanced phishing threat protection platform.
How is it downloaded? The malware finally downloads a payload from a legitimate URL shortener domain (bit.ly/2SkO8Iu), which then forwards with HTTP CODE 301 (Redirect) to the actual URL.
What is the actual URL? The actual URL is: https://f.coka.la/2RTMHs.png, which is an EXE file, but hidden under the cover of a .PNG file. Also, notice the HTTPS prefix. The URL is actually legitimately encrypted, and the traffic will bypass regular proxy servers, and the malicious content will remain hidden (Encrypted on the network). The SSL certificate is also valid (today
What does the malware variant resemble? Initial analysis suggests that the attack is a variant to the known vulnerability “Formbook,” which is a form-grabber and stealer malware written in C and x86 assembly language.
How is the malware executed? Using a malicious #RTF file to infect a machine, the variant attempts to trick users into downloading an exe file payload, covered with a png extension.
Was the malware discovered in any specific country or industry? We have not been able to identify and specific geographic pattern or industry-specific focus at this time.
For Interviews: For more information or to speak with the researchers, please contact evan@arpr.com
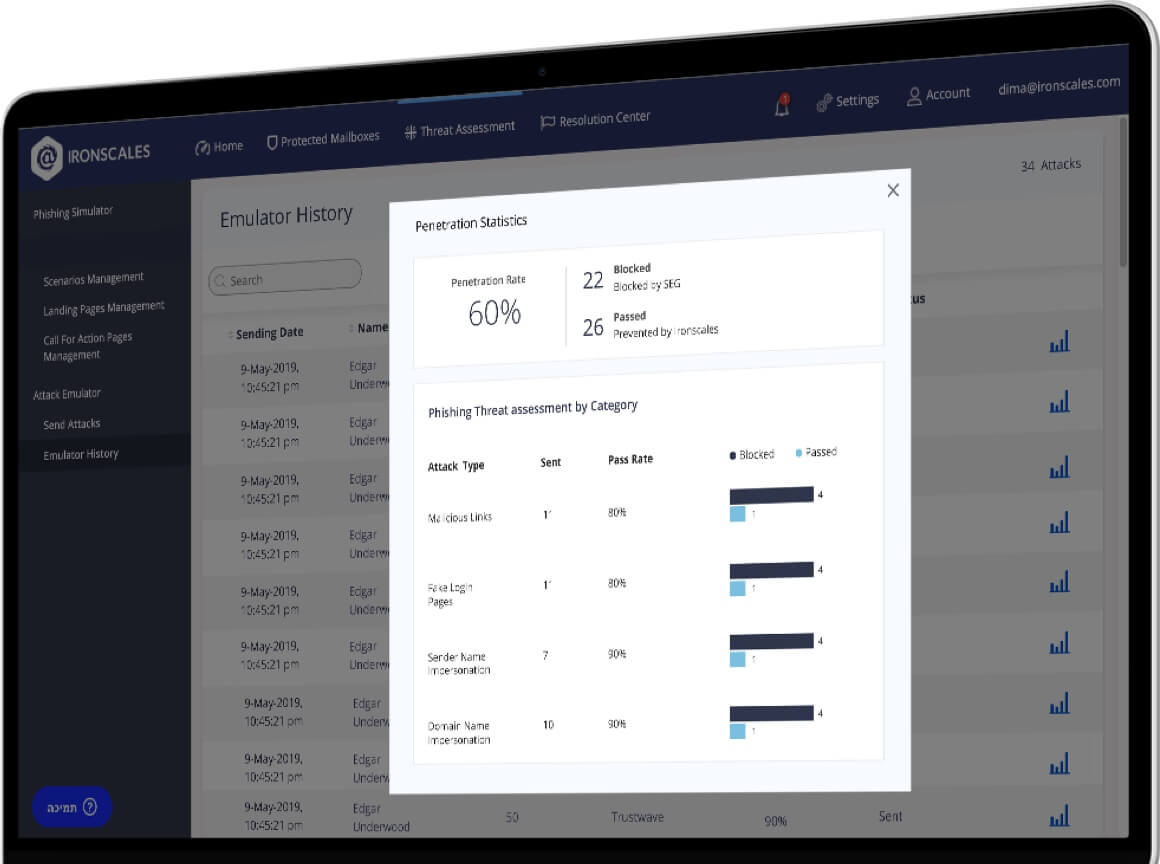
About IRONSCALES
IRONSCALES is the leader in advanced phishing threat protection, combining human intelligence with machine learning to prevent, detect, and respond automatically to advanced email phishing threats. By combining technical and end-user controls into one integrated, automated, and multi-layered platform, IRONSCALES drastically reduces the workload burden of SOC and security teams, while expediting the time from phishing-attack discovery to enterprise-wide remediation from hours, weeks, or months to only seconds. Headquartered in Tel Aviv, IRONSCALES was incubated at the 8200 EISP, the top program for cybersecurity ventures, founded by alumni of the Israel Defense Forces’ elite Intelligence Technology unit.
About SNDBOX
Developed by researchers for researchers, SNDBOX is the first malware research solution to leverage multiple AI detection vectors and undetectable kernel driver analysis. Working together, SNDBOX technology delivers in-depth results, quickly while granting the AI and big data insights necessary for comprehensive malware research and false positive rate reduction.

November 30, 2018