S/MIME
What is S/MIME? S/MIME (Secure/Multipurpose Internet Mail Extensions) is a standard for public key encryption and digital signing of email messages. It enables two core security capabilities: encryption, which ensures only the intended recipient can read a message, and digital signatures, which ...
Read nowData Detection and Response (DDR)
Data Detection and Response (DDR) Defined Data detection and response (DDR) is a security approach that continuously monitors sensitive data across cloud, SaaS, and on-premises environments to detect unauthorized access, anomalous movement, and potential exfiltration in real time. The category ...
Read nowGet your phishing prevention guide
Stay up to date with our latest news, articles and resources.
Multi-Tenancy Security
What is Multi-Tenancy Security? Multi-tenancy security is the set of isolation mechanisms, access controls, and operational safeguards that protect data and ensure privacy when multiple organizations share a single application instance. NIST SP 800-145 defines resource pooling in cloud computing as ...
Read nowESP Abuse (Email Service Provider Abuse)
ESP Abuse Explained ESP abuse is a phishing technique where attackers route malicious email campaigns through legitimate email service providers such as SendGrid, MailerLite, Mailgun, Brevo, ActiveCampaign, or Amazon SES. Because these platforms are authorized senders with established ...
Read nowDisplay Name Spoofing
Display Name Spoofing Explained Display name spoofing is a sender impersonation technique where an attacker configures the From header display name to match a trusted contact while sending the email from a completely unrelated address. RFC 5322 defines the From header as containing both a display ...
Read nowSession Hijacking
Session Hijacking Explained Session hijacking is an attack where a threat actor steals, intercepts, or forges a valid session token to take over an authenticated user session without needing the user's credentials. NIST defines it as an attack where the adversary inserts themselves into the ...
Read nowthe Cyber Kill Chain
Cyber Kill Chain Explained The Cyber Kill Chain is a seven-stage framework developed by Lockheed Martin in 2011 that models the sequential phases an adversary must complete to successfully execute a cyberattack. Introduced by analysts Eric Hutchins, Michael Cloppert, and Rohan Amin, the framework ...
Read nowInfostealer
Infostealer Explained An infostealer is a category of malware engineered to extract sensitive data from compromised systems, including saved passwords, browser cookies, session tokens, cryptocurrency wallet keys, and autofill form data. Unlike ransomware that announces its presence with encryption ...
Read nowAdversary-in-the-Middle (AiTM)
Adversary-in-the-Middle (AiTM) Explained Adversary-in-the-Middle (AiTM) is a phishing technique that uses a reverse proxy to intercept authentication credentials and session tokens in real time, enabling attackers to bypass multi-factor authentication (MFA). The term originates from MITRE ...
Read nowMulti-Factor Authentication (MFA)
Multi-Factor Authentication Explained Multi-factor authentication (MFA) is a security method that requires users to verify their identity using two or more distinct factors before gaining access to an account, application, or system. The three recognized factor categories are something you know (a ...
Read nowCrowdsourced Threat Intelligence
Crowdsourced Threat Intelligence Explained Crowdsourced threat intelligence is a threat detection model where security insights are aggregated from a community of organizations rather than generated by a single vendor or research team. When one organization identifies a new threat, that detection ...
Read nowImage-Based Phishing
Image-Based Phishing Explained Image-based phishing is a social engineering technique where the entire email body is delivered as an embedded image rather than rendered HTML text. Instead of writing the phishing message in a format that email clients render as selectable text, attackers compose the ...
Read nowPrompt Injection
Prompt Injection Explained Prompt injection is an attack technique that manipulates artificial intelligence and large language model (LLM) applications by inserting crafted instructions into input that the model processes. The OWASP Top 10 for LLM Applications ranks prompt injection as the ...
Read nowBIMI (Brand Indicators for Message Identification)
BIMI Explained BIMI (Brand Indicators for Message Identification) is an email specification that enables domain owners to display a verified brand logo next to authenticated messages in recipient inboxes. It sits at the top of the email authentication stack, building on SPF, DKIM, and DMARC to add ...
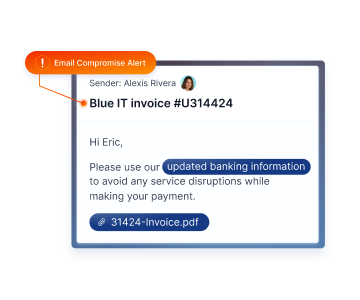
Read nowEmail Account Compromise (EAC)
Email Account Compromise Explained Email account compromise (EAC) is a cyberattack where a threat actor gains unauthorized access to a legitimate email account and operates from inside it. The attacker controls the actual mailbox rather than spoofing the account holder from outside, giving them the ...
Read nowZero-Day Attack
Zero-Day Attack Explained A zero-day attack is a cyberattack that exploits a previously unknown vulnerability in hardware, firmware, or software before the vendor has released a patch. NIST defines a zero-day attack as "an attack that exploits a previously unknown hardware, firmware, or software ...
Read nowMalware
Malware Explained Malware is any software or firmware intentionally designed to perform unauthorized actions that compromise the confidentiality, integrity, or availability of a computer system. NIST defines it as software "intended to perform an unauthorized process that will have adverse impact ...
Read nowURL Rewriting
URL Rewriting Explained URL rewriting is an email security technique that replaces hyperlinks in inbound messages with modified URLs that route through a security proxy at the moment a recipient clicks. This enables time-of-click analysis, where the destination is inspected for malicious content ...
Read nowSecure Email Gateway (SEG)
Secure Email Gateway Explained A secure email gateway (SEG) is a perimeter-based email security solution that inspects inbound and outbound messages for spam, malware, phishing attempts, and policy violations before they reach an organization's mail server. NIST SP 800-45 outlines the foundational ...
Read nowThreat Intelligence
Threat Intelligence Explained Threat intelligence is evidence-based knowledge about existing or emerging cyber threats, produced by collecting, processing, and analyzing raw data to provide the context needed for security decisions. NIST defines cyber threat intelligence as "threat information that ...
Read nowSandbox Evasion
Sandbox Evasion Explained Sandbox evasion is a collection of techniques that malware uses to detect whether it is executing inside a sandbox or virtual machine (VM) analysis environment, then alter its behavior to appear benign. MITRE ATT&CK catalogs these methods under T1497: ...
Read nowCallback Phishing (TOAD)
Callback Phishing Explained Callback phishing is a phishing technique where the initial email contains no malicious links or attachments, only a phone number and a pretext designed to make the recipient call. MITRE ATT&CK classifies this approach under T1566.004: Spearphishing Voice, which ...
Read nowThread Hijacking New
Thread Hijacking Explained Thread hijacking is an email attack technique where threat actors gain access to a legitimate mailbox, harvest existing email conversations, and reply within those real threads to deliver malicious links, attachments, or fraudulent requests. MITRE ATT&CK documents the ...
Read nowSteganography New
Steganography Explained Steganography is the practice of concealing data within other data so the hidden content is invisible to anyone not specifically looking for it. NIST defines it as "the art, science, and practice of communicating in a way that hides the existence of the communication." The ...
Read nowKeylogger
Keyloggers Explained Modern keyloggers are stealthy, lightweight, and built for one purpose: covert data capture. They quietly collect usernames, passwords, credit card numbers, email content, and other confidential inputs, often without any visible signs of infection. Credential theft is now one ...
Read nowJailbreaking (AI) New
What is AI Jailbreaking? AI jailbreaking (also called AI jailbreak or jailbreaking AI) is the process of overriding or bypassing the safety restrictions built into AI systems such as LLMs. When successful, a jailbreak allows threat actors to manipulate AI tools into generating malicious content ...
Read nowDMARC 2.0 (DMARCbis) New
DMARC 2.0, officially known as DMARCbis (pronounced "dee-mark-biss"), is the next generation of the Domain-based Message Authentication, Reporting, and Conformance protocol. This enhanced email authentication standard builds upon the foundation of DMARC 1.0 while addressing critical limitations ...
Read nowWormGPT
The Fundamentals of WormGPT WormGPT operates as a fine tuned language model exposed to code corpora, exploit write ups, and phishing kits, and it is distributed through darknet marketplaces, encrypted chat channels, and private forums.
Read nowFraudGPT
How FraudGPT Works FraudGPT is believed to operate as a fine-tuned large language model (LLM) that has been trained or prompted with datasets drawn from malicious code repositories, phishing templates, and prior breach data. It is typically distributed through darknet marketplaces, encrypted chat ...
Read nowYARA Rules New
How YARA Rules Work YARA stands for "Yet Another Ridiculous Acronym", a tongue-in-cheek name given by its creator, Victor M. Alvarez of VirusTotal. Despite the playful origin, YARA has become an industry standard in malware research, powering detection across security labs, sandboxes, and ...
Read nowDeepfake Vishing
Why Deepfake Vishing is a Serious Threat The goal of a deepfake voice call is to socially engineer the recipient into taking an action such as transferring funds, revealing credentials, or approving access. This tactic merges two attack methods: Deepfake voice cloning, powered by generative AI. ...
Read nowGhostGPT
GhostGPT Explained GhostGPT operates as an unrestricted AI chatbot available on platforms like Telegram and dark web forums. Unlike traditional AI models, it does not block harmful prompts. Threat actors use it to generate phishing emails, exploit code, and impersonation scripts quickly and ...
Read nowPreemptive Security
Understanding Preemptive Security Preemptive Security involves identifying potential vulnerabilities and implementing measures to mitigate risks before they are exploited. In email security, this translates to deploying advanced threat detection systems that monitor for suspicious activities, such ...
Read nowSMTP Relay
How SMTP Relay Works SMTP Relay uses the Simple Mail Transfer Protocol (SMTP) to move emails from one server to another. This process ensures that emails sent from one domain can be successfully delivered to recipients on other domains.
Read nowAPI-Based Email Security
How API-Based Email Security Works API-based email security leverages native integrations with cloud email platforms to provide continuous protection across the entire email lifecycle. By analyzing email content, metadata, and user behavior in real time, API-based solutions enable advanced threat ...
Read nowSPF Flattening
SPF Flattening Explained SPF flattening is a workaround technique that converts include statements in your SPF record into direct IP address entries to reduce DNS lookups. Instead of your SPF record telling receiving email servers to "go look up what IP addresses Salesforce uses," flattening lists ...
Read nowAgentic Security
Agentic Security Explained Agentic security represents a paradigm shift in cybersecurity, moving from reactive, human-dependent processes to proactive, AI-driven operations.
Read nowDomain Spoofing
Domain Spoofing Explained Domain spoofing, also known as domain impersonation, is a sophisticated cyberattack where threat actors pretend to be a trusted domain. Their goal is to deceive recipients into believing a message or website is from a legitimate source and compromise sensitive information.
Read nowCyber Insurance New
A Brief History The first cyber insurance policy emerged in the late 1990s, as the world began to embrace the internet and a new wave of digital technologies, leading to new risks for businesses. Lloyd’s of London is recognized for underwriting some of the earliest cyber insurance policies, ...
Read nowIdentity and Access Management
Identity and Access Management (IAM) Explained IAM is built around the management of electronic identities, which governs how individuals are identified in a system, how roles are assigned, and how permissions are granted or revoked.
Read nowSOAR
SOAR Explained SOAR (Security Orchestration, Automation, and Response) platforms are designed to address the challenges of modern cybersecurity by integrating with existing security tools, automating repetitive tasks, and providing a centralized platform for incident management. By leveraging ...
Read nowMDR (Managed Detection and Response)
Managed Detection and Response (MDR) Explained MDR services are designed to enhance an organization’s ability to handle and respond to cyber threats. They combine cutting-edge tools for threat detection with the knowledge and experience of security professionals who actively monitor, investigate, ...
Read nowXDR (Extended Detection and Response)
Extended Detection and Response (XDR) Explained XDR represents the evolution of traditional detection and response tools, addressing the growing complexity and sophistication of modern cyber threats. Traditional security solutions like Endpoint Detection and Response (EDR) focus solely on endpoint ...
Read nowDNS Exfiltration
Domain Name Systems (DNS) Exfiltration Explained Domain Name Systems (DNS) Exfiltration, a type of DNS Tunneling attack, is a sophisticated technique employed by cybercriminals to covertly transmit sensitive data from a target network to external servers using the DNS protocol. This method allows ...
Read nowDrive-by Download Attack
Drive-by Download Attacks Explained A drive-by download attack is a type of cyberattack in which malicious code or software is unintentionally downloaded to a user's computer or mobile device without their consent or interaction. These attacks exploit vulnerabilities in applications, web browsers, ...
Read nowPhishing Kit
Phishing Kits Explained Phishing kits typically include web development software with a low-code/no-code graphical user interface (GUI), email templates, graphics, and sample scripts. These elements help create convincing imitations of legitimate correspondence. Some kits also offer additional ...
Read nowTargeted Attack Protection (TAP)
Targeted Attack Protection Explained Targeted attacks, also known as advanced threats, involve highly sophisticated techniques to infiltrate an organization's network or compromise individuals within the organization. These attacks can be difficult to detect and mitigate due to their tailored ...
Read nowThreat Response Auto-Pull (TRAP)
Threat Response Auto-Pull Explained Threat Response Auto-Pull (TRAP) is a crucial tool for messaging and security administrators, providing an automated solution to manage and mitigate email-based threats. Given that email remains the primary vector for cyberattacks, accounting for over 90% of data ...
Read nowDNS Sinkhole
DNS Sinkholes Explained DNS sinkholes, also called sinkhole domains, are specialized domains created and managed by cybersecurity professionals to intercept and redirect malicious traffic. Instead of allowing malicious traffic to reach its intended target, DNS sinkholes capture this traffic, ...
Read nowData Loss
Data Loss Explained Data loss refers to the intentional or unintentional destruction or compromise of digital information, leading to the permanent or temporary loss of data. It can occur due to various reasons, including hardware malfunctions, software corruption, human error, natural disasters, ...
Read nowHoneypot
Honeypot Explained A honeypot is a cybersecurity technique that involves setting up a network-attached system with the purpose of luring cyber attackers. It acts as a decoy or trap designed to detect, divert, and study hacking attempts. The primary objective of a honeypot is to gather information ...
Read nowData Leak
Data Leak Explained A data leak refers to an unauthorized and unintentional release or exposure of sensitive or confidential information from a secure location to an untrusted environment. In the context of the digital era, data leaks most commonly occur within computer networks, cloud services, or ...
Read nowTyposquatting
Typosquatting Explained Typosquatting is a malicious practice where cybercriminals register domain names that are similar to popular websites but contain typographical errors. The goal is to deceive users into visiting these fake websites and potentially steal sensitive information, distribute ...
Read nowVishing
Vishing Attacks Explained Vishing is a social engineering attack delivered through phone calls or voicemails that attempts to fool people into revealing sensitive information. The caller usually masquerades as someone from a trusted company or government department. Attempts to elicit the desired ...
Read nowRansomware as a Service
Ransomware as a Service (RaaS) Explained Ransomware as a Service (RaaS) is a cybercrime model where ransomware tools are developed and leased out by creators to other criminals, often with minimal technical expertise, for the execution of ransomware attacks. This service-based model mirrors ...
Read nowWatering Hole Attack
Watering Hole Attacks Explained A watering hole attack is a type of targeted cyber attack that aims to compromise users within a specific industry or group by infecting websites they frequently visit. It derives its name from the behavior of predators in the animal kingdom, who wait near watering ...
Read nowThreat Exposure Management
Threat Exposure Management Explained Threat Exposure Management (TEM) is a comprehensive and strategic approach to managing the increasing risks and vulnerabilities faced by organizations in the modern threat landscape. It encompasses a set of processes, methodologies, and capabilities that enable ...
Read nowCommon Vulnerabilities and Exposures
Common Vulnerabilities and Exposures (CVE) Explained Common Vulnerabilities and Exposures (CVE) is a comprehensive list of publicly disclosed information security vulnerabilities and exposures. It was launched in 1999 by the MITRE Corporation, a nonprofit organization that operates federally funded ...
Read nowSMTP
SMTP Explained Simple Mail Transfer Protocol (SMTP) is a standard for sending email messages between servers. It was first defined in 1982 and is now the de facto standard for email delivery across the internet. It supports both text and binary attachments, as well as providing authentication and ...
Read nowDKIM
DKIM Explained DKIM (DomainKeys Identified Mail) is an email authentication technique that helps protect both senders and recipients from fraudulent emails. DKIM uses digital signatures to analyze incoming emails from the sending domain, and then compares this signature with public information ...
Read nowUser Behavior Analytics (UBA)
User Behavior Analytics (UBA) Explained User Behavior Analytics (UBA) involves tracking, collecting, and assessing user data and activities through monitoring systems. Initially focused solely on users, the term has evolved into User and Entity Behavior Analytics (UEBA) to reflect that users are ...
Read nowUnicode Domain Phishing
Unicode Domain Phishing Explained Unicode Domain Phishing, also known as script spoofing or internationalized domain name (IDN) homograph attack, is a type of cyber attack where attackers exploit the visual similarity of characters from different scripts to deceive users. By registering domain ...
Read nowNatural Language Understanding
Natural Language Understanding Explained Natural language understanding (NLU), a subset of Natural Language Processing (NLP), is a field of artificial intelligence that focuses on enabling machines to understand and interact with humans in their own natural language. NLU processes linguistic input ...
Read nowContent Disarm and Reconstruction (CDR)
Content Disarm and Reconstruction (CDR) Explained Content Disarm and Reconstruction (CDR), also known as Threat Extraction, is a security technology that proactively protects against known and unknown threats contained in documents by removing executable content. It is designed to prevent ...
Read nowPharming
Pharming Explained Pharming is a type of cyberattack that involves redirecting website traffic from a legitimate website to a fake one designed to steal personal information or financial data from the user. Unlike phishing, where the user is tricked into clicking on a link that takes them to a fake ...
Read nowData Broker
Data Brokers Explained A data broker, often referred to as an information broker, is a business that collects, aggregates, organizes, and sells or distributes information about individuals to other businesses, organizations, or entities. This data can be utilized for various purposes, including ...
Read nowCompliance Monitoring
Compliance Monitoring Explained Compliance monitoring is a dynamic process that ensures organizations adhere to policies, procedures, and regulatory requirements to identify and address compliance risks. It involves the surveillance, review, and analysis of organizational performance and risk ...
Read nowIndicators of Compromise (IOC)
Indicators of Compromise (IOC) Explained Indicators of Compromise (IOC) are digital artifacts or traces left behind by cybercriminals that suggest a network or endpoint has been breached, providing valuable clues for identifying security threats such as data breaches, insider threats, or malware ...
Read nowSmishing
Smishing Explained Smishing is a type of social engineering scam that uses mobile texting rather than emails to deliver nefarious messages that dupe people into taking specific actions. The term is a combination of phishing and SMS, and its increasingly widespread use reflects a belief among ...
Read nowWhitelist
Whitelists (Allowlists) Explained Whitelists, also known as allowlists, are a fundamental cybersecurity strategy employed to enhance the security of computer systems, networks, and applications. These lists serve as a proactive access control mechanism by explicitly permitting only a predefined set ...
Read nowSpyware
Spyware Explained Spyware is a broad term that encompasses malicious software designed to infiltrate computer devices and mobile devices with the primary intent of gathering data about users without their consent. This data is typically transmitted to a third party, often for malicious purposes, ...
Read nowData Loss Prevention (DLP)
Data Loss Prevention (DLP) Explained Data Loss Prevention (DLP) is a proactive cybersecurity strategy designed to safeguard sensitive data from breaches, leaks, and unauthorized access. In an increasingly digital world, protecting valuable information is paramount for organizations to maintain ...
Read nowAbuse Mailbox
Abuse Mailbox Explained An Abuse Mailbox refers to a designated destination where users can report suspicious emails to IT and security teams for further investigation and analysis. It serves as a crucial component in tracking and preventing potential email threats within an organization. The Abuse ...
Read nowPolymorphic Attacks
Polymorphic Phishing Attacks Explained A polymorphic attack is a type of cyber attack that uses a constantly changing code, content, or structure in order to evade detection by security systems. In the context of email, polymorphic phishing attacks may use a different sender's address, subject ...
Read nowQuantum Cryptography
Quantum Cryptography Explained Quantum cryptography is an encryption method that leverages the principles of quantum mechanics to secure data transmission. Unlike traditional cryptographic systems, which rely on mathematical algorithms, quantum cryptography utilizes the inherent properties of ...
Read nowDMARC
DMARC Explained DMARC (Domain-based Message Authentication, Reporting, and Conformance) is an email authentication protocol that uses specifically formatted messages to verify the authenticity of the sender’s domain. DMARC helps protect a company from unauthorized use of its domain name by ...
Read nowDark Web Monitoring
Dark Web Monitoring Explained Dark web monitoring involves the use of specialized technology and expertise to scan, identify, and assess threats that emerge within the dark web. This proactive security measure aims to detect and alert individuals or organizations to potential threats, such as ...
Read nowIdentity Cloning
Identity Cloning Explained Identity cloning is a sophisticated form of identity theft in which an individual maliciously assumes another person's identity, typically for personal gain or to evade legal consequences. This deceptive act involves the replication of various personal details, such as a ...
Read nowThreat Assessment
Threat Assessment Explained Threat assessment refers to the process of evaluating and analyzing potential risks and vulnerabilities to an organization's digital assets, networks, and systems. It involves identifying and understanding various threats that may compromise the confidentiality, ...
Read nowCredential Stuffing
Credential Stuffing Explained Credential stuffing is a cyber attack technique that exploits the common practice of reusing the same username and password combinations across multiple websites and services. The attack relies on leaked or stolen credentials, which are typically obtained from previous ...
Read nowAdvanced Persistent Threat
Advanced Persistent Threat Explained An advanced persistent threat (APT) is a type of attack in which an intruder or group of intruders gain unauthorized access to a network and remain undetected for long periods of time in order to steal sensitive data. Some APTs will sit dormant for long periods ...
Read nowMFA Bypass
MFA Bypass Attacks Explained MFA bypass attacks encompass various strategies employed by cybercriminals to overcome the additional security measures introduced by MFA. These attacks often leverage social engineering tactics, phishing, or exploitation of vulnerabilities in the authentication process ...
Read nowQuishing Attack
Quishing Explained In the realm of cyber threats, quishing attacks, also known as QR code phishing, have emerged as deceptive tactics employed by cybercriminals. These attacks manipulate QR codes to lure unsuspecting individuals into visiting fraudulent websites, with the ultimate aim of either ...
Read nowIoT Security
IoT (Internet of Things) Security Explained IoT security, or Internet of Things security, refers to the practices and measures implemented to protect Internet-connected devices from unauthorized access, data breaches, and cyberattacks. These devices, ranging from smart home appliances to industrial ...
Read nowSpear Phishing Attack
Spear Phishing Explained Spear phishing, a form of business email compromise (BEC), is a highly targeted form of phishing that uses deceptive emails to trick recipients into taking certain actions, such as providing sensitive information or downloading malware. In spear phishing, the attacker ...
Read nowCredential Harvesting Attack
Credential Harvesting Explained Credential harvesting, also known as password harvesting or username harvesting, is a form of cyberattack that involves the theft of personal or financial data such as usernames and passwords, typically carried out through phishing, malicious websites, email scams, ...
Read nowGraymail
Graymail Explained Graymail is a term used to describe emails that are not exactly spam but are not wanted by the recipient either. These emails may come from reputable sources such as newsletters or mailing lists, but the user may no longer be interested in receiving them. Unlike spam, Graymail is ...
Read nowBusiness Email Compromise
Business Email Compromise (BEC) Explained Business email compromise is a type of targeted phishing (spear phishing) in which a threat actor either accesses or mimics a genuine business email account to defraud the business. This tactic relies on exploiting the assumed trust that victims have in ...
Read nowIntegrated Cloud Email Security (ICES)
Email has become the essential communication tool in the digital age, but it also exposes us to increased risk of cyberattacks targeting email systems. Integrated Cloud Email Security (ICES) solutions are designed to address this concern by providing advanced protection against various email-based ...
Read nowSandbox
Sandbox Explained A Sandbox is a cybersecurity tool that uses an isolated and controlled environment designed to test, analyze, and execute potentially malicious or suspicious code, software, or applications. The primary purpose of a sandbox is to provide a secure space where the unknown code can ...
Read nowSPF
SPF Explained SPF (Sender Policy Framework) is an email authentication system that works by verifying the IP address of any message sent from a specific domain. SPF allows ISPs and email services to make sure that the messages they receive are actually coming from a legitimate source. SPF assists ...
Read nowClickjacking
Clickjacking Explained Clickjacking is a malicious technique used by attackers to trick users into clicking on a webpage element that is disguised or hidden. The objective of clickjacking is to deceive users into unknowingly performing actions that they did not intend to do, such as downloading ...
Read nowBrute Force Attack
Brute Force Attack Explained A brute force attack is a trial-and-error method used by cybercriminals to gain unauthorized access to sensitive information or systems by systematically attempting to guess credentials, such as passwords, encryption keys, or personal identification numbers (PINs). ...
Read nowSecurity Operations Center (SOC)
SOC (Security Operations Center) Explained A Security Operations Center (SOC) is a central function within an organization dedicated to monitoring, detecting, analyzing, responding to, and reporting security incidents and threats. It serves as the frontline defense against cyber attacks, staffed by ...
Read nowSecurity Awareness Training
Security Awareness Training Explained Security Awareness Training refers to educational programs designed to teach individuals about potential security risks and how to mitigate them. These programs aim to increase knowledge and awareness of security best practices, policies, and procedures within ...
Read nowHTML Smuggling
HTML Smuggling Explained HTML Smuggling is an advanced cyberattack technique where attackers use HTML5 and JavaScript features to create malicious files on the fly within a victim's browser. This method bypasses traditional security measures that scan files at the network perimeter, as the ...
Read nowIdentity Fabric
Identity Fabric Explained Identity Fabric refers to a deployment architecture that enables organizations to establish and manage identities in a digital environment. It allows individuals to securely use their personal identities across various online platforms and services. Your Identity Fabric ...
Read nowFake Login Page
Fake Login Page Attacks Explained A fake login page, also known as a phishing page, is a type of cyberattack that attempts to trick users into providing their login credentials for a particular service, such as an email account, social media platform, or even an online banking account. The fake ...
Read nowGenerative AI
Generative AI Explained Generative AI is a subset of artificial intelligence that focuses on the development of algorithms and models capable of generating new data that resembles existing patterns and distributions. Unlike traditional AI systems that are used for prediction and classification, ...
Read nowMX Record
MX Records Explained MX records (Mail Exchange records) are a type of DNS (Domain Name System) record that identifies which mail server is responsible for accepting incoming email messages on behalf of a domain. In other words, MX records provide the information needed for email to be delivered to ...
Read nowAccidental Data Exposure
Accidental Data Exposure Explained Accidental Data Exposure, also known as Sensitive Data Exposure, refers to unintended instances where sensitive data becomes accessible to unauthorized individuals or entities. This could range from personal information such as social security numbers and banking ...
Read nowOutbound Email Protection
Outbound Email Protection Explained Outbound email protection is a security measure implemented by organizations to prevent data breaches originating from emails sent within the organization to external entities. It ensures that sensitive data, whether shared intentionally or by mistake, doesn’t ...
Read nowMFA Fatigue Attacks
MFA Fatigue Attacks Explained MFA Fatigue Attacks leverage the reliance on MFA as an additional layer of security beyond traditional passwords. By bombarding users with a high volume of MFA prompts—typically push notifications to mobile devices—attackers exploit the tendency of users to eventually ...
Read nowCEO Fraud
CEO Fraud Explained CEO fraud (commonly referred to as executive phishing or ‘whaling’) is when an attacker successfully impersonates a company executive in order to gain sensitive information or coerce a financial transaction from targeted executives or employees.
Read nowZero Trust
Zero Trust Explained Zero Trust is a cybersecurity framework that operates on the principle of never trusting any user or device by default. It requires continuous authentication, authorization, and validation of users and devices before granting or maintaining access to applications and data. ...
Read nowConversation Overflow
Conversation Overflow Explained Conversation Overflow attacks involve crafting emails with two distinct sections: a visible portion prompting the recipient to take action, such as clicking a link or providing sensitive information, and a concealed segment containing benign text. The hidden text is ...
Read nowVendor Email Compromise
Vendor Email Compromise Explained Vendor Email Compromise (VEC), sometimes referred to as Vendor Impersonation or Vendor Spoofing, is a type of cyber attack in which an attacker gains access to a vendor’s email account and uses it to send fraudulent emails to the vendor’s customers. The emails ...
Read nowAccount Takeover
Account Takeover Explained Account takeover (ATO) is a form of cybercrime that occurs when a cybercriminal gains access to a victim’s online account. The attacker can then use the account to commit fraud, steal money or sensitive data, or commit other malicious activities. ATO is a subset of ...
Read nowDeepfake Phishing
Deepfake Phishing Explained Deepfake phishing uses AI algorithms to fabricate audio, video, or image content that appears to be authentic. This content is then used to manipulate the target into taking actions beneficial to the attacker. For example, an attacker might create a deepfake voice note ...
Read nowData Breach
Data Breach Explained A data breach refers to any incident where unauthorized individuals gain access to sensitive or confidential data. This can include personal information like social security numbers, financial data, healthcare records, or corporate information such as customer databases and ...
Read nowRansomware
Ransomware Explained Ransomware is a type of malicious software that encrypts a victim’s files, rendering them inaccessible, and demands a ransom payment in exchange for the decryption key. Ransomware can infect computers and networks through various channels, including phishing emails, malicious ...
Read nowSecurity Information and Event Management (SIEM)
Security Information and Event Management (SIEM) is a technology that aids in threat detection, compliance, and security incident management by collecting, analyzing, and correlating security events and contextual data from various sources. SIEM solutions provide organizations with a centralized ...
Read nowMachine Learning
Machine Learning (ML) Explained Machine Learning is a subfield of artificial intelligence and computer science that involves the development of algorithms and models that enable computers to learn and improve their performance on specific tasks based on data inputs. It is an integral component of ...
Read nowImpersonation
Impersonation Explained Impersonation is a deceptive technique used by cybercriminals to masquerade as someone else, typically a trusted individual or entity, with the aim of tricking individuals into performing malicious actions or divulging sensitive information. Impersonation attacks often rely ...
Read nowHuman-centric Security
Human-centric Security Explained Human-centric security (i.e., Human Centricity) refers to an approach to cybersecurity that prioritizes the understanding and integration of human behavior, psychology, and interaction within the context of security measures. It recognizes that humans play a ...
Read nowEmail Encryption
Email Encryption Explained Email encryption is a security method that uses encryption algorithms to encode email messages, making them unreadable to anyone who doesn't have the decryption key. When an email message is encrypted, its contents are transformed into a coded language that can only be ...
Read nowPretexting
Pretexting Explained Pretexting is a social engineering technique used by threat actors in business email compromise attacks to manipulate individuals into divulging sensitive information. It involves creating a fictional scenario or pretext to deceive victims and gain their trust. By posing as a ...
Read nowOCR Deep Learning
OCR Deep Learning Explained Optical Character Recognition (OCR) is a technology used to convert various types of documents, such as scanned paper documents or images, into editable and searchable text data. Traditional OCR systems rely on predefined rules and templates to recognize text characters ...
Read nowIP Reputation
IP Reputation Explained IP reputation is a measure of the trustworthiness of an IP address based on its past behavior. IP reputation is important because it is used by email filters, firewalls, and other security tools to identify and block potentially malicious traffic. An IP address with a good ...
Read nowPhishing
Most employees are required to take security awareness training during their first week of work. Normally these courses outline company policies, talk about the importance of online security, what is phishing, and share examples of email attacks so that employees can detect and report them in the ...
Read nowEmail Security
Email Security Explained Email security refers to the tools, techniques, procedures, and software used to defend against malicious attempts to access and compromise sensitive data. In 2019, Verizon’s Data Breach Investigations Report found that 90% of cyber attacks can be attributed to email. ...
Read nowEmail Spoofing
Email Spoofing Explained Email spoofing is a technique scammers use to make fraudulent emails appear as if they came from a known entity. By impersonating someone familiar, scammers use phishing attacks to obtain sensitive information such as company credit card numbers, payroll data, and even ...
Read nowWhaling
Whaling Explained Whaling is a type of spear phishing in which threat actors directly target C-level executives at an organization. This type of social engineering attack sends fraudulent messages to individuals with high levels of seniority to exploit three particular characteristics of these ...
Read nowSPAM
Email SPAM Explained Email spam, also known as junk email, refers to unsolicited and unwanted messages that are sent in bulk to a large number of recipients. These messages are typically commercial in nature and driven by a financial motive. Spammers use various techniques to deceive recipients, ...
Read nowImpossible Travel
Impossible Travel Explained Impossible travel is a cybersecurity detection method used to identify potential compromise or unauthorized access to user accounts. It detects instances where a user's account is accessed from two different countries within an unreasonably short timeframe, suggesting ...
Read nowLink Jacking
Link Jacking Explained Link jacking is a digital strategy involving the redirection of internet traffic from its original source to an alternative website. This can be achieved by copying content from one site and reposting it on another, often on aggregator websites that consolidate various ...
Read nowInvoice Fraud
Invoice Fraud Explained Invoice fraud is a well-coordinated ploy in which an attacker attempts to scam a business into paying a fake invoice–or paying a legitimate invoice to a fake account–by impersonating a vendor or partner. The lure of large transactions makes invoice fraud very appealing to ...
Read nowPhishing Simulation Testing
Phishing Simulation Explained Phishing simulation is the process of using a phishing simulator to mimic real-world phishing attacks by sending simulated phishing emails to test targeted recipients within an organization. The primary objective of using phishing simulation testing (PST) is to assess ...
Read nowClone Phishing
Clone Phishing Explained Clone phishing is a type of cyberattack where an attacker clones or replicates a legitimate email and modifies it to spread malware or steal sensitive information. The cloned email appears to come from a trusted source, such as a well-known brand or organization, making it ...
Read nowSupply Chain Attacks
Supply Chain Attacks Explained A supply chain attack is a sophisticated cyberattack strategy that strategically targets trusted third-party vendors or suppliers within an organization's intricate supply chain network. These malicious attacks take advantage of the established trust between ...
Read nowLog4j
Log4j Exploit Explained Log4j is an open-source logging library that is widely used by software applications and online services to track and record system activities and events. It is part of the Apache Logging Services Project, developed by the Apache Software Foundation. The library provides ...
Read nowArtificial Intelligence
Artificial Intelligence Explained Artificial Intelligence (AI) is a field of computer science that focuses on creating intelligent machines capable of performing tasks that typically require human intelligence. It involves developing algorithms and systems that can learn from data, reason, and make ...
Read nowConsent Phishing
Consent Phishing Explained Consent phishing relies on the OAuth 2.0 authorization protocol, which enables users to grant applications access to their resources without divulging their passwords. Attackers exploit this process by registering malicious applications with OAuth 2.0 providers, tricking ...
Read nowComputer Vision
Computer Vision Explained Computer vision is a field of artificial intelligence that focuses on giving machines the ability to interpret, analyze and understand visual data from images or videos. This can include recognizing objects in an image, understanding the context of an image or scene, ...
Read nowMan-in-the-Middle Attack
Man-in-the-Middle Attack Explained A Man-in-the-Middle (MITM) Attack is a cyberattack in which an attacker intercepts communication between two parties, such as a user and an application, to eavesdrop or impersonate one of the parties. The attacker can steal personal information like login ...
Read nowTransport Layer Security (TLS)
Transport Layer Security (TLS) Explained Transport Layer Security (TLS) operates as a client-server handshake protocol, facilitating the establishment of an encrypted connection and verifying the authenticity of communication. This handshake involves negotiation between the client and server to ...
Read nowInsider Threat
Insider Threat Explained Insider threats in cybersecurity are risks originating from within an organization, often involving individuals with legitimate access to systems and data. These threats can be intentional or unintentional, leading to compromises in data confidentiality, availability, and ...
Read nowGenerative AI Fraud
Generative AI Fraud Explained Generative AI fraud refers to the deceptive use of artificial intelligence models, particularly generative models, to create fraudulent content that can be used for malicious purposes. These purposes include identity theft, financial fraud, and spreading ...
Read nowSocial Engineering
Social Engineering Explained Social engineering is a type of malicious attack used by cybercriminals to gain access to an organization’s sensitive data and resources. This attack usually involves manipulating individuals into providing confidential information or performing actions that can put the ...
Read nowBarrel Phishing
Barrel Phishing Explained Barrel phishing, also known as double-barrel phishing or multi-stage phishing, while not a specific attack, typically refers to a general phishing tactic that involves two or more separate emails, to steal sensitive information or data from unsuspecting victims. This type ...
Read nowEmergency Inbox
Emergency Inboxes Explained During an email service outage, the Emergency Inbox automatically captures incoming messages, ensuring that critical communications are not lost. It differs from regular email inboxes as it only displays messages received during the outage period and does not show those ...
Read nowAI TRiSM
AI TRiSM (Trust, Risk & Security Management) Explained AI TRiSM is a proactive approach to identify and mitigate risks inherent in AI models and applications. It aims to integrate governance measures upfront to ensure compliance, fairness, reliability, and privacy protection from the initial ...
Read nowLarge Language Model
Large Language Model Explained A Large Language Model (LLM) is a type of deep-learning model based on transformer architecture that has been trained on a massive amount of text data. LLMs are designed to understand and generate human-like text in a coherent and contextually relevant manner. These ...
Read nowSubscribe to Our Blog Newsletter
Stay up to date with our latest news, articles and resources.
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







