Table of Contents
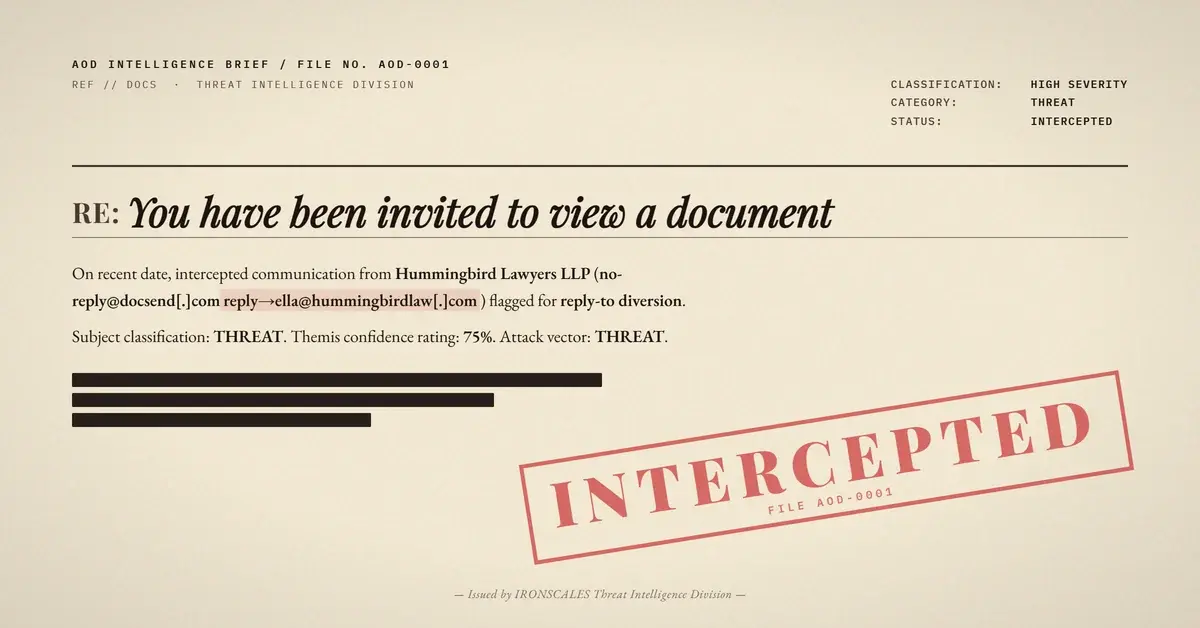
A forensics consulting firm received a document-sharing notification from Dropbox DocSend. The email passed SPF, DKIM, and DMARC. Every link resolved to legitimate DocSend and Dropbox domains. Microsoft assigned it a Spam Confidence Level of just 1. The only anomaly: a Reply-To header that silently routed every response to an unverifiable law firm domain. Four mailboxes received the message before IRONSCALES quarantined it.
How the Attack Works
The attacker leveraged DocSend's legitimate notification system to deliver a share invitation claiming to be from a named individual at "Hummingbird Lawyers LLP." The email arrived from no-reply@docsend[.]com, signed with valid DKIM keys for both docsend[.]com and pm.mtasv[.]net (Postmark's transactional email infrastructure). SPF passed for pm-bounces.docsend[.]com. DMARC passed with compauth=100.
This is the core problem with platform abuse attacks: the attacker never needs to configure their own sending infrastructure. DocSend handled authentication, delivery, and formatting. The result was an email that looked identical to any legitimate DocSend share because it was a legitimate DocSend share, generated through the platform's own notification pipeline.
The payload was not in the links. It was in the Reply-To header.
The From address pointed to no-reply@docsend[.]com, but the Reply-To header redirected responses to ella@hummingbirdlaw[.]com. Any recipient who clicked "reply" to ask about the proposal, request context, or confirm the sender's identity would unknowingly initiate a conversation with the attacker rather than DocSend or the claimed sender's actual organization.
This is a business email compromise setup. The initial email establishes a pretext (a legal proposal requiring review), and the Reply-To diversion captures engagement. From there, the attacker controls the conversation and can escalate to credential requests, payment redirection, or document-based malware delivery.
MITRE ATT&CK Mapping
| Technique | ID | Role in Attack |
|---|---|---|
| Phishing: Spearphishing via Service | T1566.003 | DocSend notification system used as delivery mechanism |
| Establish Accounts: Email Accounts | T1585.002 | Reply-To address created at hummingbirdlaw[.]com to capture victim responses |
| Trusted Relationship | T1199 | DocSend/Postmark infrastructure provides full authentication pass |
Why Traditional Defenses Miss It
Every signal that legacy email security gateways rely on came back clean:
- SPF: Pass (pm-bounces.docsend[.]com is an authorized sender for DocSend)
- DKIM: Pass (dual signatures from docsend[.]com and pm.mtasv[.]net)
- DMARC: Pass (compauth=100, the highest possible composite authentication score)
- Link scanning: All URLs resolved to docsend[.]com and dropbox[.]com with clean verdicts
- Attachment scanning: No attachments present
- SCL: 1 (Microsoft's own spam filter gave it a near-clean score)
The Reply-To mismatch is the single technical indicator. But Reply-To mismatches are common in legitimate business email. Sales teams use CRMs that send from a platform address with Reply-To pointing to the rep. Marketing platforms do the same. A static rule blocking Reply-To mismatches would generate thousands of false positives per day.
According to the Microsoft Digital Defense Report 2024, attackers increasingly abuse legitimate cloud services as delivery infrastructure, specifically because it neutralizes domain reputation and authentication-based filtering. The FBI IC3 2024 Annual Report documented $2.9 billion in BEC losses, with law firm impersonation among the most effective pretexts due to the inherent authority and urgency associated with legal communications.
The Verizon 2024 DBIR found that pretexting (the social engineering category that includes BEC) now accounts for more than 40% of breaches involving social actions. A legal proposal from an unfamiliar firm is precisely the kind of message that triggers a reply rather than suspicion.
Indicators of Compromise
| Indicator | Type | Context |
|---|---|---|
| ella@hummingbirdlaw[.]com | Reply-To address | Attacker-controlled reply diversion |
| hummingbirdlaw[.]com | Domain | Registered 2012, GoDaddy, WHOIS privacy-shielded, no verifiable public footprint for claimed entity |
| no-reply@docsend[.]com | From address | Legitimate DocSend notification (abused) |
| 104.245.209.196 | Sending IP | Postmark transactional MTA (mta196a-ord.mtasv[.]net), Chicago, US |
| hxxps://docsend[.]com/view/s/bu99ue75kaarc8r6 | Link | DocSend document share (clean verdict, content unverified) |
| pm-bounces.docsend[.]com | SPF envelope | Return-Path for bounce handling |
The Reply-To Gap in Email Security
WHOIS records for hummingbirdlaw[.]com reveal a domain registered in December 2012 through GoDaddy with full registrant privacy enabled. AWS Route 53 nameservers host the DNS. No public directory listing corroborates the existence of "Hummingbird Lawyers LLP" as a registered legal entity. The domain has the appearance of legitimacy (13+ years old, active DNS) without any verifiable identity behind it.
This is what makes Reply-To diversion effective. The attacker does not need to compromise a domain, register a lookalike, or defeat authentication. They just need a plausible-sounding Reply-To address and a legitimate platform to send the initial notification. The platform handles everything else.
IRONSCALES detected this attack through community-driven threat intelligence and behavioral analysis. The combination of first-time sender status, Reply-To domain mismatch against the authenticated From domain, and community signals from similar reported incidents produced an 84% Themis confidence score. All four affected mailboxes were quarantined automatically.
Across the 1,921 organizations and 35,000+ security professionals in the IRONSCALES community, platform abuse attacks like this one generate some of the strongest community consensus signals. When multiple organizations report similar DocSend, SharePoint, or Google Docs notifications with mismatched Reply-To headers, that pattern propagates across the entire network within minutes.
What Defenders Should Do
Reply-To diversion attacks require detection logic that goes beyond authentication results. CISA's phishing guidance recommends verifying sender identity through independent channels before responding to unexpected document shares. The IBM Cost of a Data Breach Report 2024 found that BEC attacks carry an average cost of $4.88 million per incident, making early detection of the initial pretext email critical.
Organizations should treat Reply-To mismatches on platform-generated notifications as a high-priority signal when combined with first-time sender status and unverifiable sender identity. Static authentication checks will never catch this pattern because the authentication is real. The detection has to happen at the behavioral layer.
See Your Risk: Calculate how many threats your SEG is missing
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)