Table of Contents
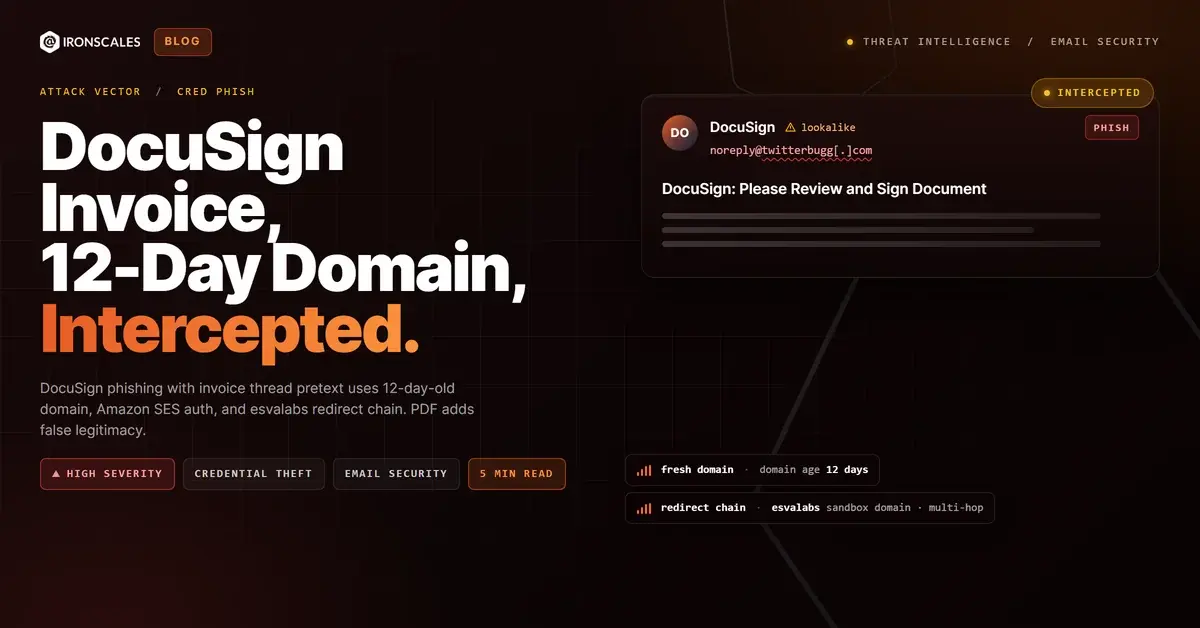
The email carried two pretexts. The first: a DocuSign notification requesting a document signature. The second: an invoice thread referencing an outstanding payment. Either one alone would be a standard phishing lure. Together, they created something more convincing. A recipient who might question a standalone DocuSign notification could rationalize it when paired with an invoice context. The sending domain had existed for 12 days.
In April 2026, IRONSCALES detected a phishing campaign that layered brand impersonation, dual pretexting, and a multi-hop redirect chain into a single delivery. The domain twitterbugg[.]com was registered on April 3, 2026, with privacy-protected WHOIS. The email was sent through Amazon Simple Email Service (SES) with valid authentication. The call-to-action links routed through urlsand[.]esvalabs[.]com, a URL analysis domain with known associations to sandbox and malware report flags, before redirecting to the final credential harvesting page. And the attached PDF? Clean. Static scanning returned zero indicators.
According to the FBI IC3 2024 Annual Report, phishing was the most reported cybercrime category with over 298,000 complaints. The campaigns driving those numbers look exactly like this: layered, infrastructure-aware, and designed to pass automated inspection.
Two Pretexts Are Better Than One
Most phishing emails commit to a single story. This one ran two simultaneously. The DocuSign branding provided visual credibility. The familiar purple and white template, the "Review Document" button, the signature request language. Recipients who process DocuSign requests regularly (finance teams, legal departments, procurement) see these elements as routine.
The invoice thread added a second layer of legitimacy. By framing the DocuSign request within a payment context, the attacker created a scenario where the recipient had both a procedural reason (sign the document) and a financial reason (resolve the invoice) to engage. The Verizon 2024 Data Breach Investigations Report found that pretexting attacks have doubled since 2022 and that financial pretexts remain the most effective social engineering vector in enterprise environments.
The PDF attachment reinforced the story. It contained what appeared to be invoice-related content with static images. No embedded JavaScript, no macro payloads, no malicious objects. Static scanning returned clean results. But the attachment's purpose was not to deliver a payload. It was to lower the email's overall suspicion score. When a scanner finds a clean attachment alongside a link, the aggregate risk assessment can drop below the quarantine threshold.
The 12-Day Domain Problem
The sending domain twitterbugg[.]com was registered on April 3, 2026, just 12 days before delivery. WHOIS records were privacy-protected, revealing no registrant name, organization, or contact details. The domain had no web presence, no email sending history, and no DNS records beyond the minimum required for SES integration.
Newly registered domains are one of the strongest phishing indicators available. Research from the Interisle Consulting Phishing Landscape 2024 report found that over 70% of phishing domains are used within 30 days of registration. Yet domain age alone is not sufficient for blocking. Legitimate businesses register new domains daily for product launches, marketing campaigns, and acquisitions. The signal requires context.
In this case, the context was clear: a 12-day-old domain with privacy-protected registration, sending DocuSign-branded invoice emails through Amazon SES, with redirect links pointing to a flagged sandbox analysis domain. No single indicator was a guaranteed phishing signal. The combination was.
The esvalabs Redirect Chain
The call-to-action links pointed to urlsand[.]esvalabs[.]com with encoded parameters. esvalabs operates URL scanning and sandbox analysis tools, and the urlsand subdomain is part of that infrastructure. The attacker weaponized this by using the scanning service as a redirect hop.
The technique is clever. URL reputation systems evaluate the domain of the link target. esvalabs[.]com is a known security analysis platform, which means its domain reputation is high. A SEG evaluating the link sees a connection to a recognized security vendor's infrastructure, not a phishing host. The redirect chain then passes through at least one additional hop before delivering the recipient to the credential harvesting page.
See Your Risk: Calculate how many threats your SEG is missing
Microsoft's Safe Links and similar URL rewriting services provide partial protection by following redirects at click time. But "partial" is the operative word. Redirect chains that terminate at dynamically generated pages, or that serve different content based on the visitor's IP address or user agent, can evade time-of-click scanning. The Microsoft Digital Defense Report 2024 documented a 40% increase in evasive URL techniques targeting click-time protection systems.
Authentication Through Amazon SES
The email passed SPF and DKIM checks through Amazon SES infrastructure. Like SendGrid, Mailjet, and other cloud email platforms, SES handles authentication on behalf of its users. An attacker who creates an AWS account and configures SES for a new domain immediately inherits Amazon's delivery infrastructure reputation.
This is the DMARC paradox for newly registered domains. A domain can have a valid DMARC policy, pass all authentication checks, and still be a purpose-built phishing asset. The protocols verify infrastructure authorization. They do not evaluate intent. The IBM Cost of a Data Breach 2024 report found that phishing was the costliest initial attack vector at $4.88 million per incident, precisely because these attacks pass the technical checks that organizations rely on.
Themis, the IRONSCALES Adaptive AI, evaluated the convergence of signals: domain age under 30 days, privacy-protected registration, redirect chain through a flagged sandbox domain, dual pretext construction, and zero prior sending history with the target organization. The message was quarantined across all affected mailboxes before any user clicked through the redirect chain.
MITRE ATT&CK Mapping
- T1566.001 (Phishing: Spearphishing Link): Email with embedded credential harvesting links disguised behind redirect chain.
- T1036.005 (Masquerading: Match Legitimate Name or Location): DocuSign branding and invoice pretext to mimic trusted business communications.
- T1204.001 (User Execution: Malicious Link): Attack requires user to click through the redirect chain.
- T1608.005 (Stage Capabilities: Link Target): Attacker staged the redirect chain through esvalabs infrastructure to obscure the final payload.
Indicators of Compromise
| Type | Indicator | Context |
|---|---|---|
| Sender Domain | twitterbugg[.]com | 12-day-old domain, privacy-protected WHOIS |
| Redirect URL | urlsand[.]esvalabs[.]com | URL sandbox domain used as redirect hop |
| Email Platform | Amazon SES | Authenticated sending infrastructure |
| Registration Date | April 3, 2026 | Domain registered 12 days before delivery |
| Attachment | PDF (static scan clean) | False legitimacy, no embedded payload |
| Pretext | DocuSign + Invoice thread | Dual social engineering pretext |
When Clean Attachments Make Dirty Emails Look Safe
The most subtle element of this campaign is the PDF. It did nothing malicious. That was the point. A clean attachment shifts the balance of a risk score. Scanners that weight attachment analysis heavily may lower the overall threat assessment when the attachment passes inspection, even if the links in the same email are suspicious. The attacker understood this and included the PDF not as a weapon, but as cover.
This is why layered email security that evaluates messages holistically matters. Domain age, sender history, redirect chain behavior, brand impersonation signals, attachment context, and authentication results all need to feed into a single risk model. When any one of those signals is evaluated in isolation, attacks like this pass. When they converge, the pattern is unmistakable. A 12-day-old domain sending DocuSign invoices through Amazon SES with links to a flagged sandbox service and a clean PDF decoy is not a legitimate business communication. It is a credential harvesting campaign built to exploit the gaps between individual security checks.
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)