Table of Contents
The entire email body was six words: "Did you get my previous email?"
No links. No attachments. No embedded images. No QR codes. No malware payload of any kind. And yet, buried in the message headers was a Reference to a Gmail conversation the recipient had never been part of, silently fabricating a history of prior engagement that never existed. The goal was not to steal credentials or deliver malware. It was to get someone to reply, confirming the mailbox was active, monitored, and responsive.
A reply would have opened the door to everything that comes next.
Anatomy of a Ghost Thread
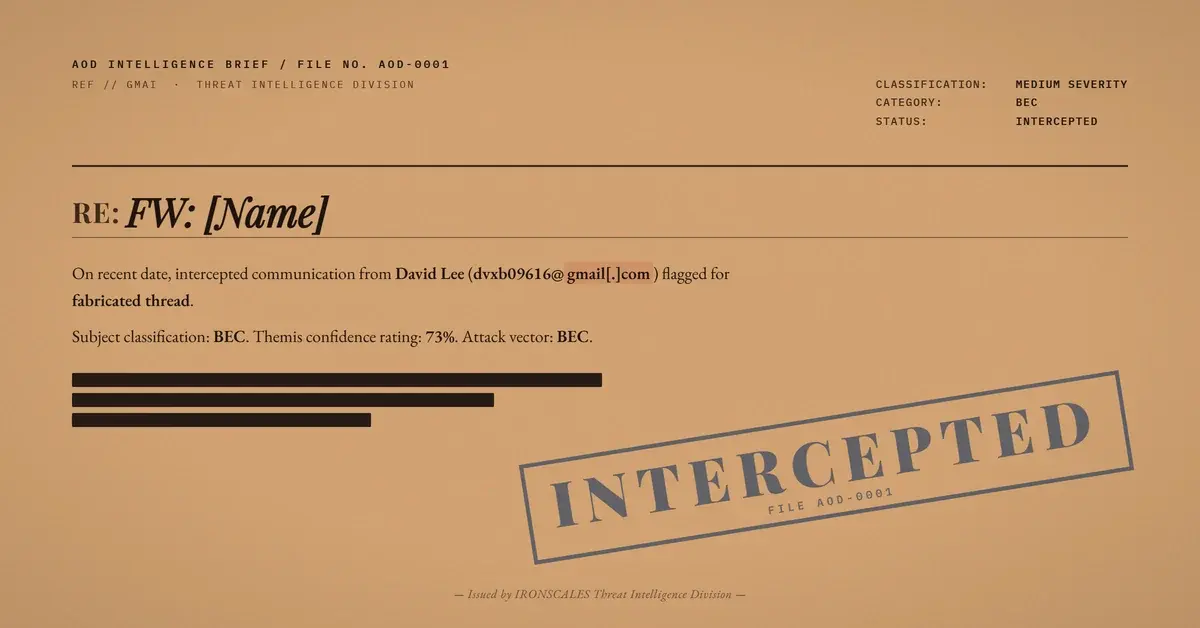
The message arrived at a shared helpdesk mailbox at a professional services company. The sender appeared to be an employee at an established law firm, with the email routing through the firm's Mimecast secure email gateway before entering the recipient's Microsoft 365 environment. The subject line was simply the sender's own first name, forwarded: "FW: [Name]."
What made this message technically interesting was its References header. The In-Reply-To and References fields both pointed to a Message-ID originating from mail[.]gmail[.]com. The forwarded thread visible in the email screenshot confirmed the original message came from a Gmail address (dvxb09616@gmail[.]com) using the display name "David Lee." That Gmail message was sent to the law firm employee, who then forwarded it to the target helpdesk mailbox with the single-line follow-up.
This creates a two-layer trust exploit. First, the forwarded Gmail thread manufactures the appearance of a prior conversation. Email clients use References and In-Reply-To headers to group messages into threads, so a recipient's mail application may present this as a continuation of an ongoing exchange. Second, the forward comes from a legitimate law firm domain with established infrastructure, lending institutional credibility to what is essentially a cold probe from an unknown Gmail account.
The FBI IC3 2024 Internet Crime Report documented $2.77 billion in BEC losses, with reconnaissance probes like this one serving as the opening move in the majority of those campaigns. The attack costs nothing. The information it returns is worth everything.
Authentication: A Passing Grade With a Missing Exam
The email passed SPF. The sending IP (170[.]10[.]133[.]107) belongs to Mimecast's outbound delivery infrastructure, which is explicitly authorized in the law firm domain's SPF record. DMARC passed with action=none because SPF alignment was sufficient under the domain's p=none policy.
But DKIM was absent. The message carried no DKIM signature at all.
This is a significant gap. SPF validates the sending server's IP address. DKIM provides cryptographic proof that the domain owner authorized the specific message content. Without DKIM, there is no assurance that the law firm's domain administrators sanctioned this particular email. The message could have been sent by anyone with access to the firm's Mimecast relay, including a compromised account.
The domain itself was registered in 2008 through Cloudflare, with an expiration date in 2028. It publishes SPF records that include both Microsoft 365 and Mimecast. A DKIM selector (selector1) exists in DNS, but no signature appeared on this message. The DMARC record is set to p=none, meaning failed authentication generates reports but never blocks delivery. Microsoft's own composite authentication (compauth) returned a score of 100, and the spam confidence level (SCL) was just 1.
Every technical gate said "legitimate." The behavioral signals told a different story.
What the Scanners Cannot See
Traditional email security operates on a detect-what-is-there model. Scan links. Detonate attachments. Match known bad signatures. When there is nothing to scan, there is nothing to flag.
According to the Microsoft Digital Defense Report 2024, BEC attacks have increased 15% year over year, with reconnaissance probes and reply-solicitation tactics comprising a growing share of initial attack vectors. The Verizon 2024 DBIR found that pretexting, which includes reconnaissance-stage social engineering, appeared in over 40% of breach-related social actions.
Zero-payload probes exploit a fundamental assumption in legacy email security architectures: that threats must contain a detectable artifact. When the artifact is the reply itself, signature-based detection has no surface to work with.
See Your Risk: Calculate how many threats your SEG is missing
This is where behavioral analysis changes the equation. IRONSCALES flagged this message at 73% confidence based on signals that exist independent of payload:
- First-time sender. The law firm address had never communicated with this organization before.
- Shared mailbox targeting. Helpdesk and shared role-based addresses are high-value targets because replies often come from multiple team members, expanding the attacker's map of active respondents.
- Fabricated thread context. The References header pointed to a Gmail Message-ID with no corresponding inbound message in the recipient's environment. The conversation it referenced did not exist.
- Missing DKIM on a DKIM-capable domain. The domain publishes a DKIM selector, but the message arrived unsigned, a behavioral anomaly that purely technical checks overlook when DMARC passes on SPF alone.
The IRONSCALES platform synthesizes these signals into a risk assessment that operates on sender behavior and communication patterns, not just technical artifacts. The sender was classified as high-risk before the message reached a single inbox.
The Reconnaissance Playbook
If anyone had replied, the attacker would have confirmed four things: the mailbox is active, it is monitored by a human, the human is willing to engage with unknown senders, and the response time indicates how quickly the organization reacts to external messages. That intelligence shapes the timing, targeting, and pretext of the follow-up attack.
The IBM Cost of a Data Breach Report 2024 found that BEC attacks carry an average cost of $4.88 million per incident. Every one of those incidents started with a moment exactly like this: an innocuous-seeming message that extracted just enough information to make the next one work.
The pattern follows MITRE ATT&CK T1598 (Phishing for Information) and T1589.002 (Gather Victim Identity Information: Email Addresses). The fabricated thread reference maps to T1656 (Impersonation), using a forwarded message to adopt the credibility of an established professional services firm.
Observed Indicators: Fabricated Thread Probe
| Indicator | Type | Context |
|---|---|---|
| dvxb09616@gmail[.]com | Original Gmail sender in fabricated thread | |
| 170[.]10[.]133[.]107 | IP | Mimecast outbound delivery relay |
dkim=none | Auth | Missing DKIM signature on DKIM-capable domain |
dmarc=pass action=none (p=none) | Auth | Permissive DMARC policy, SPF-only alignment |
compauth=pass reason=100 | Auth | Microsoft composite authentication passed |
SCL=1 | Spam Score | Microsoft assigned low spam confidence |
Stopping the Probe Before the Payload Arrives
Organizations relying solely on authentication-based filtering will miss this class of attack entirely. When SPF passes, DMARC passes, and the payload is empty, the only detection surface is behavior.
Implement behavioral AI that evaluates first-time sender risk, fabricated thread indicators, and shared mailbox targeting patterns. Enforce DKIM signing at the organizational level and flag inbound messages from domains that publish DKIM selectors but fail to sign. Upgrade DMARC policies from p=none to p=quarantine or p=reject to close the SPF-only alignment loophole.
Train helpdesk and shared mailbox operators to verify "previous email" claims through independent channels before engaging. Six words can be the most dangerous payload in your inbox.
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)