Table of Contents
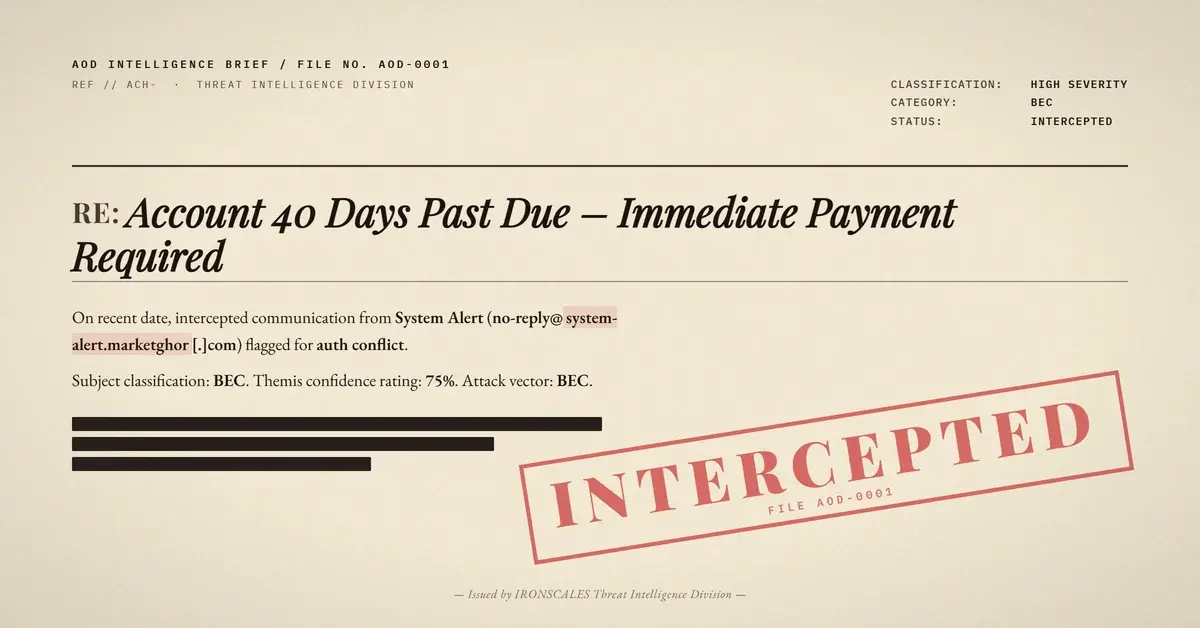
An employee at a mid-size manufacturing firm received what looked like a routine document share from a county government official. The subject referenced a board of commissioners statement. Attached: a single password-protected PDF with the passcode printed in the email body.
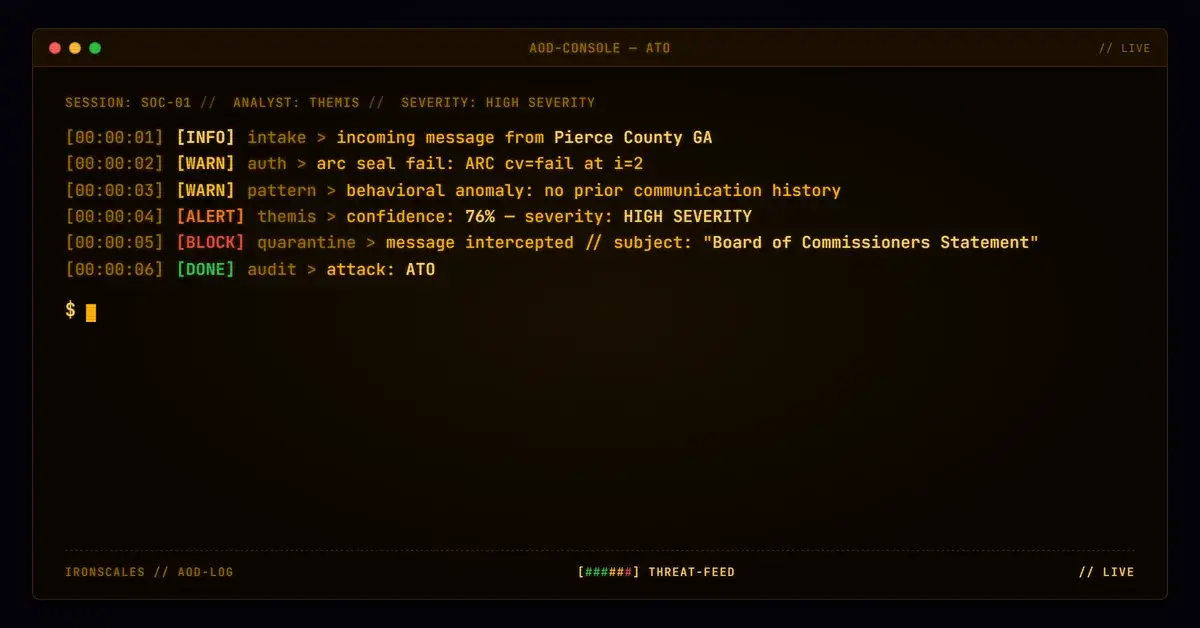
SPF passed. DKIM passed. DMARC passed. Composite authentication returned a perfect 100. Microsoft rated it SCL 1 (not spam). But the original authentication headers told a different story.
The Headers Tell Two Stories
The Authentication-Results-Original header, capturing the pre-relay state, showed dkim=none (message not signed) and dmarc=none. The email left the compromised tenant with no cryptographic signature.
After transiting Microsoft outbound protection (outbound[.]protection[.]outlook[.]com), the receiving gateway saw DKIM pass against the county domain via selector2, SPF resolve against Microsoft's authorized infrastructure, and DMARC align. The message that started with zero authentication arrived with full authentication.
The ARC seal at i=2 returned cv=fail, confirming the prior hop's signing did not validate. This is the forensic fingerprint of authentication laundering: the original state was washed through Microsoft's outbound relay, and the receiving SEG had no reason to question the result.
The Attachment No Scanner Could Open
The 112 KB PDF was password-protected. Every scanner returned a clean verdict, not because the file was safe, but because none could decrypt it. The verdict field read "clean, scanning," the default when encryption blocks inspection.
The attacker included the passcode in the email body. This is purely an anti-analysis technique. Legitimate senders deliver passwords through a separate channel. When the password and the encrypted file travel together, the encryption serves one purpose: defeating automated inspection.
What Caught It
IRONSCALES Adaptive AI flagged the message at 76% confidence based on behavioral signals authentication could not surface: a county government public works superintendent writing to a manufacturing firm with no prior communication history, an encrypted attachment paired with an inline passcode, and evasion patterns tracked across the IRONSCALES community of 35,000+ security professionals. Four mailboxes were quarantined before any recipient opened the file.
The ARC failure was the tell. Authentication said "trusted." The chain of custody said "broken."
Indicators of Compromise
| Type | Value | Context |
|---|---|---|
| Sender Domain | piercecountyga[.]gov | County government domain, registered 2014, likely compromised account |
| Relay | outbound[.]protection[.]outlook[.]com | Microsoft 365 outbound infrastructure |
| Relay IP | 2a01:111:f403:c10c::1 | IPv6 Microsoft outbound relay |
| DKIM Selector | selector2 (d=piercecountyga[.]gov) | Microsoft-applied DKIM signature |
| Attachment | Password-protected PDF (112,556 bytes) | Named after county board of commissioners |
| ARC Result | i=2 cv=fail | Prior hop signing did not validate |
| Original Auth | dkim=none; dmarc=none | Pre-relay authentication state |
| SCL | 1 | Microsoft anti-spam: not spam |
MITRE ATT&CK Mapping
| Technique | ID | Relevance |
|---|---|---|
| Compromise Accounts: Email Accounts | T1586.002 | Compromised county government M365 account used as sending infrastructure |
| Phishing: Spearphishing Attachment | T1566.001 | Password-protected PDF delivered as email attachment |
| Obfuscated Files or Information | T1027 | PDF encryption prevents automated content inspection |
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)