Table of Contents
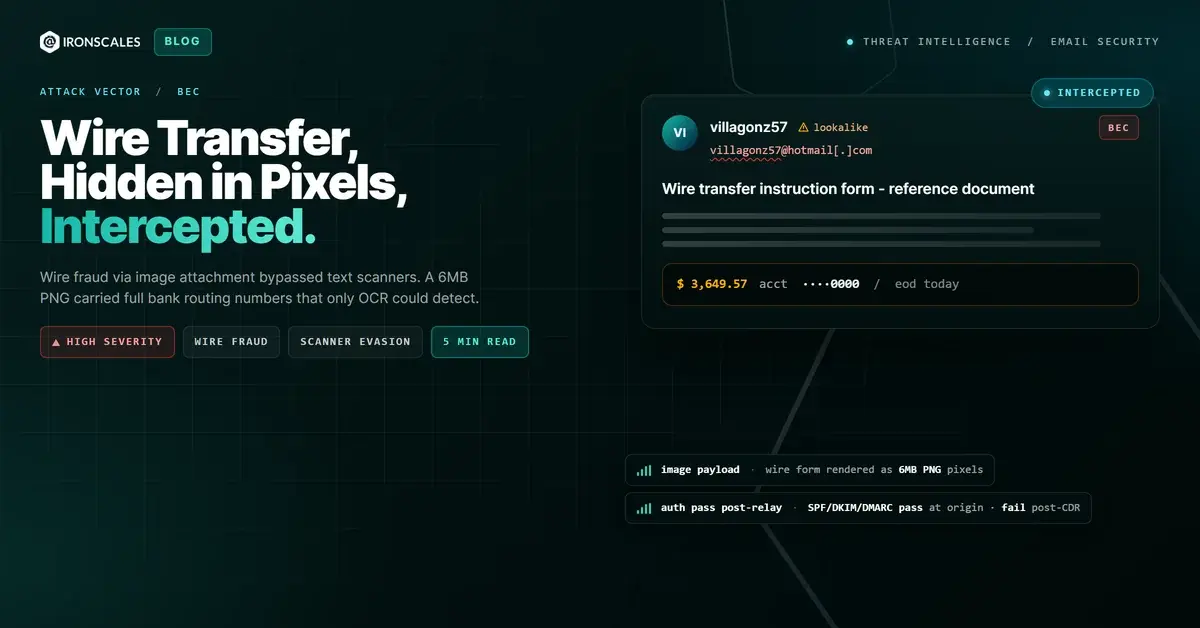
A 6MB PNG file containing a full wire transfer instruction form landed in the inboxes of four people at a regional bank. The image showed originator and beneficiary account numbers, an ABA routing number, a beneficiary address, and a $3,649.57 transfer amount. Every text-based scanner in the delivery path saw a clean image file. The Votiro Content Disarm and Reconstruction gateway sanitized the attachment and marked it safe. The real payload was visible only to the humans who opened it.
The sender was a first-time external contact using a free Hotmail account. The email was written in Spanish, addressed a bank employee by first name, and referenced a signed document. The attachment filename included the bank's name and a date. Nothing in the email body or attachment metadata triggered a single content-based detection rule.
The Visual Payload That Scanners Cannot Read
The attack delivered its entire payload as pixels. The attached PNG was a scanned image of what appeared to be a completed wire transfer instruction form. OCR extraction reveals the scope of exposed financial data:
| Field | Value (Redacted) |
|---|---|
| Originator Account | [redacted] |
| Beneficiary Account | [redacted] |
| ABA / Routing Number | [redacted] |
| Receiving Bank | [major U.S. bank] |
| Transfer Amount | $3,649.57 |
| Beneficiary Address | [U.S. residential address] |
| Purpose | "Closing Account" |
This is not a credential harvesting link disguised in an image. This is a direct financial instruction containing every detail a bank employee needs to initiate a wire transfer. The attacker did not need the victim to click anything, visit a phishing page, or enter credentials. They needed the victim to read the image and act on it.
The FBI IC3 2024 Internet Crime Report documented $2.77 billion in BEC losses for the year, with wire fraud remaining the dominant payment method exploited by attackers. Image-based delivery adds a layer of evasion that traditional business email compromise defenses are not built to catch.
Authentication Tells Two Different Stories
The email's journey through the delivery infrastructure created a split authentication narrative that illustrates a common blind spot in gateway architectures.
At the first hop, Microsoft's outbound protection servers evaluated the message directly from the sender's Hotmail account:
- SPF: Pass (Microsoft's outbound IP is an authorized sender for hotmail[.]com)
- DKIM: Pass (signature verified against hotmail[.]com selector)
- DMARC: Pass (p=none, both SPF and DKIM aligned)
- CompAuth: 100 (full composite authentication)
The message then transited through the recipient organization's Votiro CDR gateway at IP 44[.]206[.]213[.]130, an AWS-hosted relay that sanitizes attachments before final delivery. Because the gateway re-originates the message, the authentication chain broke at the second evaluation point:
- SPF: Fail (Votiro's IP is not in hotmail[.]com's SPF record)
- DKIM: Fail (body hash changed during CDR processing)
- DMARC: Fail (neither SPF nor DKIM align post-relay)
- ARC: Fail (chain validation failed at i=3)
The receiving mail server set SCL to -1 (trusted) based on the Votiro gateway's allowlist status, overriding the failed authentication results entirely. This is expected behavior for organizations that route mail through third-party security gateways. But it means the final delivery decision was made on gateway trust, not on message authentication (MITRE T1566.001).
See Your Risk: Calculate how many threats your SEG is missing
Why CDR Saw Nothing Wrong
Votiro's CDR technology is designed to strip active content from files: macros, embedded scripts, executable objects, OLE exploits. A PNG image contains none of these elements. The gateway correctly identified the file as a static image, sanitized it (the X-MTConnectorResult: Sanitized header confirms processing), and passed it through.
This is not a failure of the CDR product. It is a categorical limitation. CDR evaluates what a file does, not what a file shows. A wire transfer form rendered as pixels has no executable behavior to disarm. The Microsoft Digital Defense Report 2024 noted the increasing use of image-based evasion techniques specifically because they exploit this gap between content analysis and visual analysis.
The same limitation applies to text-based email security rules. DLP policies that scan for patterns like account numbers, routing numbers, or wire instructions in email body text will find nothing here. The sensitive data exists only in the image's pixel grid.
MITRE ATT&CK: Image Payload and Wire Fraud Techniques
| Technique | ID | Application |
|---|---|---|
| Phishing: Spearphishing Attachment | T1566.001 | Wire transfer form delivered as PNG attachment |
| User Execution: Malicious File | T1204.002 | Victim must open and act on image contents |
| Obfuscated Files or Information | T1027 | Financial data encoded as image pixels, invisible to text-based scanning |
Observed Indicators: Image-Based Wire Fraud
| Indicator | Type | Context |
|---|---|---|
| villagonz57@hotmail[.]com | Sender address, first-time contact | |
| 44[.]206[.]213[.]130 | IP | Votiro CDR relay (legitimate gateway, not attacker infrastructure) |
| votiro-relay1[.]prod[.]votiro[.]com | Hostname | CDR gateway relay |
| [Bank Name] transfer 03032026.png | Filename | 6MB PNG, scanned wire transfer form |
| a5558b7bf7f166ef315a4ce5b33d09da | MD5 | Attachment file hash |
How Behavioral Detection Caught What Content Scanning Missed
IRONSCALES Adaptive AI flagged this email at 55% confidence through behavioral analysis rather than content inspection. The signals that triggered detection were contextual, not payload-based:
- First-time sender. The Hotmail address had never contacted any employee at this organization. Across the IRONSCALES network of 1,921 organizations, first-time external senders correlate with elevated risk when combined with financial context.
- Free webmail targeting bank staff. A consumer email provider sending wire transfer documentation to institutional banking addresses is a pattern mismatch. Legitimate wire instructions typically arrive through established banking channels or known corporate domains.
- Attachment context without body content. The email body contained no account references, no invoice numbers, and no contextual detail. The entire substance was deferred to the attachment, a pattern consistent with social engineering that forces manual review rather than automated processing.
The Verizon 2024 Data Breach Investigations Report found that the human element was involved in 68% of breaches. In this case, the attack was designed so that only a human could process it. A bank employee who opens the image, reads the wire instructions, and initiates the transfer without independent verification completes the entire attack chain with no technical exploit required.
The Takeaway
Image-based payloads represent a growing blind spot in email security architectures that rely on text analysis, URL scanning, and executable content disarmament. When the payload is a photograph of a financial document, no scanner in the delivery path has anything to flag. The defense must shift from content inspection to behavioral context: who is sending this, have they sent before, does the attachment pattern match established communication norms, and does the combination of signals warrant human review before action? Organizations in financial services should treat image-only attachments from first-time external senders as a high-risk pattern, particularly when the email references wire transfers, payments, or account closures.
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)