Table of Contents
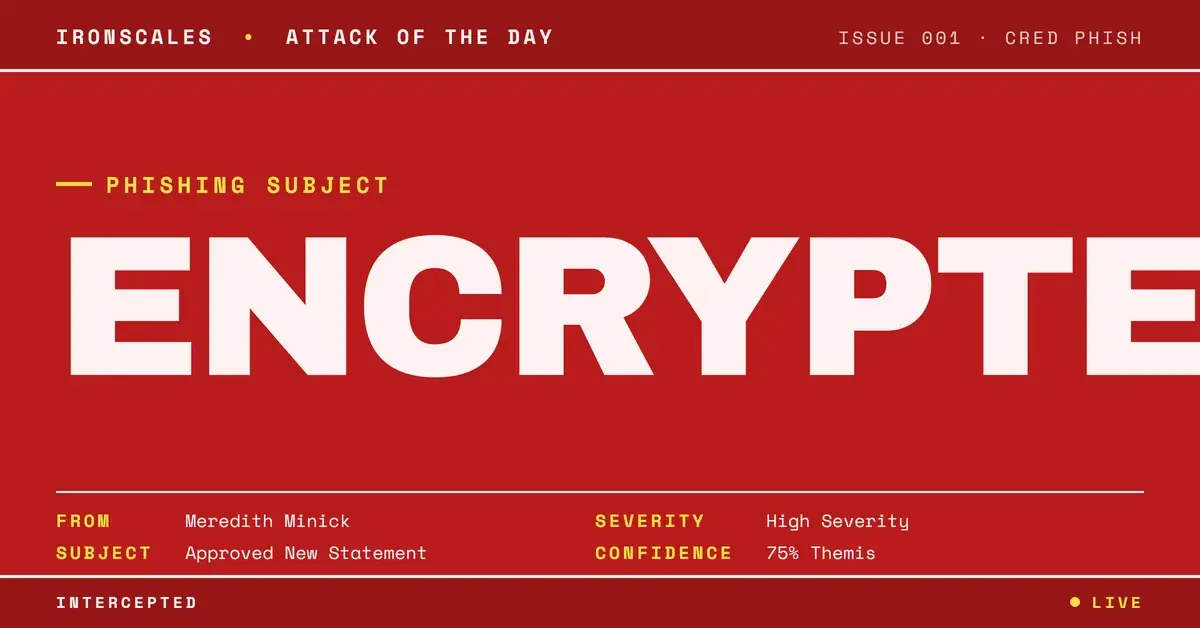
The email looked like routine government correspondence. A state education department, a professional signature block, an attached PDF described as an "Approved New Statement." The subject line was bureaucratic enough to be boring. Every authentication check passed. SPF, DKIM, DMARC, ARC: all green.
There was just one small detail that changed everything. The PDF was password-protected, and the passcode was sitting right there in the body of the email.
The Attachment That Every Scanner Declared Safe
Automated security scanners are built to open files, inspect their contents, and render a verdict. They do this millions of times a day, and they do it well. But they have a blind spot that attackers increasingly exploit: encrypted files.
When a scanner encounters a password-protected PDF, it cannot decrypt the contents without the passcode. Most systems handle this by returning a default clean verdict or simply skipping the file entirely. According to MITRE ATT&CK's documentation on obfuscated files and information, this is a well-known evasion technique (T1027) that continues to be effective precisely because it exploits how automated tools process attachments in isolation from email body content.
In this case, the 112KB PDF named Georgia Department of Education_protected.pdf passed through multiple scanning layers. Every one returned the same result: clean. Not because the file was safe, but because none of them could open it.
The FBI's 2024 Internet Crime Report documented over $2.9 billion in losses from business email compromise alone. Password-protected attachments are a growing vector within that category because they turn the scanner's own security model against itself.
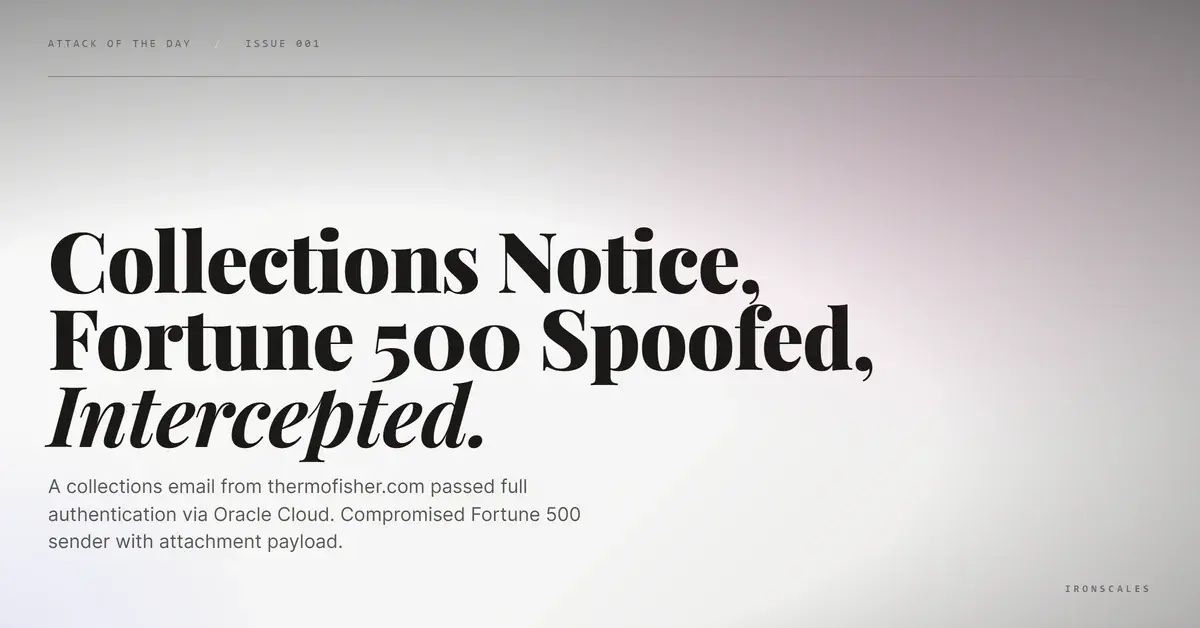
A Sender Who Checked Every Box
The email arrived from a legitimate state government domain, doe[.]k12[.]ga[.]us, which belongs to the Georgia Department of Education. The sending infrastructure was Microsoft 365, routed through outbound[.]protection[.]outlook[.]com. Authentication headers confirmed full alignment:
- SPF: Pass (authorized sending IP)
- DKIM: Pass (signature verified for
doe[.]k12[.]ga[.]us) - DMARC: Pass (policy alignment confirmed)
- ARC: Pass (chain of custody intact through relay)
The signature block was detailed and convincing, listing a named staff member, a title (Paraprofessional), a physical address at a real facility in Macon, Georgia, a local phone number, and links to legitimate government websites. The email even included branded banners for the Georgia Department of Education and a promotional graphic for the PEACH Education Tax Credit.
According to the Verizon 2024 Data Breach Investigations Report, the human element is involved in 68% of breaches. This attack was engineered to ensure the human element did the attacker's work: read the passcode, open the file, and trust the contents because everything around it looked right.
The Gap Between Machine Logic and Human Behavior
This is the core of the technique, classified under MITRE ATT&CK T1566.001 (Spearphishing Attachment). The attacker bet on a simple asymmetry. Machines process email components (headers, body text, attachments) through separate analysis pipelines. A scanner inspecting the PDF has no access to the body text containing PDF Passcode: 0937728736. It sees an encrypted file and moves on.
The human recipient experiences the email as a single unit. They read the greeting, see the passcode, open the attachment, and follow whatever instructions are inside, whether that means clicking a link, entering credentials, or enabling macros.
This separation is not a bug in any single product. It is a structural limitation in how most Secure Email Gateways process messages. SEGs miss an average of 67.5 phishing emails per 100 mailboxes per month (IRONSCALES, 2025 SEG analysis), and password-protected attachments represent one of the hardest categories for static scanning to address.
See Your Risk: Calculate how many threats your SEG is missing
What the Authentication Couldn't Tell You
Full authentication passage is not a trust signal when the sending account itself may be compromised. The Microsoft Digital Defense Report 2024 highlights that compromised legitimate accounts are one of the most effective ways attackers establish trust with their targets.
In this case, the sender was a first-time correspondent to the recipient, a professional at a regional law firm. A state education paraprofessional sending an "Approved New Statement" to an attorney with no prior communication history is exactly the kind of contextual anomaly that behavioral AI detection is designed to catch.
That is what happened here. Within seconds of delivery, Themis flagged the message based on the convergence of first-time sender status, the presence of an encrypted attachment, and community threat intelligence from IRONSCALES global network of over 35,000 security professionals. The email was quarantined across both affected mailboxes before either recipient could act on it.
Indicators of Compromise
| Type | Indicator | Context |
|---|---|---|
| Sender Domain | doe[.]k12[.]ga[.]us | Legitimate domain, likely compromised account |
| Sender Email | Meredith[.]Minick@doe[.]k12[.]ga[.]us | First-time sender to target organization |
| Attachment | Georgia Department of Education_protected.pdf | Password-protected PDF (112,382 bytes) |
| Attachment Hash (MD5) | bc4b336fd7a461d05da3e00d68e9975d | PDF file hash |
| Image | image001.png (MD5: 2d589e67f48e7b9b97dc8841cc2e43c4) | Embedded branding image |
| PDF Passcode | 0937728736 | Provided in email body for recipient |
| Linked Domain | gabmacon[.]org | Legitimate site used for trust-building |
| Linked Domain | gadoe[.]org | Legitimate site used for trust-building |
MITRE ATT&CK Mapping: - T1566.001: Phishing, Spearphishing Attachment (encrypted PDF delivery) - T1027: Obfuscated Files or Information (password protection as scanner evasion)
Why This Pattern Keeps Working
Password-protected attachment phishing works because it exploits a design constraint, not a vulnerability. Scanners are built to respect encryption. They cannot brute-force every protected file in a mail stream, and most organizations would not want them to.
The defensive answer is not better scanning. It is context-aware analysis that evaluates the combination of signals: first-time sender, encrypted attachment, passcode in body text, mismatch between sender role and recipient function. Each signal alone might be benign. Together, they form a pattern that human-trained, community-powered AI recognizes as high risk.
For security teams evaluating their email defenses, the question is straightforward. If an attacker sends a password-protected PDF to your users tomorrow, with the passcode in the body and perfect authentication on the envelope, what in your stack catches it?
If the answer depends on opening the file, you have a gap.
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)