Table of Contents
A PayPal invoice cancellation notice arrived at a professional services firm with flawless authentication, every link pointing to real paypal.com pages, and a $50 charge the recipient never initiated. The email was not a spoof. PayPal's own infrastructure sent it, which is exactly what made it dangerous.
PayPal Sent It, and That Is the Problem
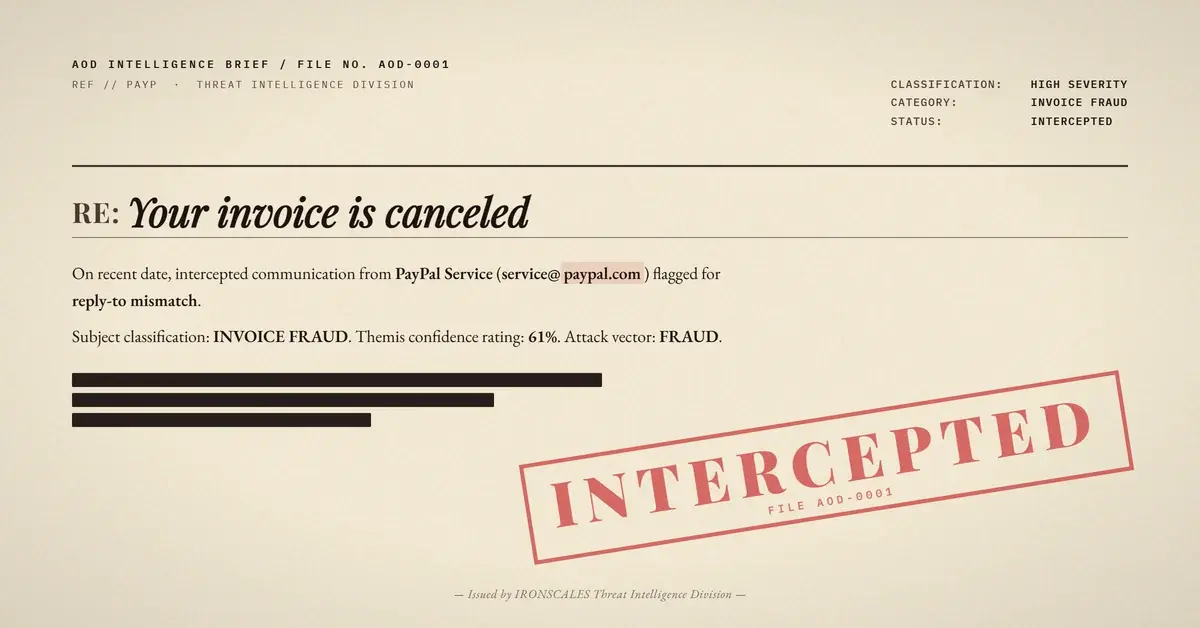
The message originated from mx17.slc.paypal.com at IP 173.0.84.6. SPF passed. DKIM passed, signed under d=paypal.com with selector pp-dkim1. DMARC passed. Microsoft's composite authentication returned compauth=pass with reason code 100, the highest trust score possible. SCL was 1. BCL was 4, a mixed-reputation bulk sender, but nothing that triggers quarantine.
The invoice template was pixel-perfect PayPal: "Your invoice is canceled," invoice number 1113, $50.00 from "kissimmee mobile notary public." It greeted the recipient by name. The CTA buttons linked to legitimate paypal.com invoice view pages. Every URL in the message resolved to PayPal-owned infrastructure.
A secure email gateway evaluating this message against its standard checks (sender reputation, link scanning, authentication results) would find nothing to flag. The platform is real. The authentication is real. The links are real.
One Header, One Domain, Zero Protection
The From address showed service@paypal.com. But the Reply-To header was set to support@kissimmeenotarypublic[.]com, a domain registered in 2017 through GoDaddy. That domain publishes DMARC=none and has no discoverable DKIM selectors, meaning it offers no authentication enforcement whatsoever.
This is where the attack lives. The invoice itself is not the payload. The conversation is. If the recipient replies to dispute the charge or request a refund, that reply routes to the merchant address, not to PayPal. An attacker who compromised or registered that merchant account controls the inbox and can steer the conversation toward payment fraud or credential collection.
The invoice also contained structural anomalies: duplicated invoice content blocks and an empty href on the "report abuse" link. These are tells that the invoice was generated programmatically, not through a standard merchant workflow.
Where the Signals Were
IRONSCALES Themis flagged this message at 61% confidence based on behavioral signals: the Reply-To mismatch between a platform sender and an external merchant domain, the first-time sender pattern, and the unsolicited invoice cancellation for a transaction with no prior history. The community confirmed it as phishing, and the incident was resolved with one mailbox quarantined.
Authentication told the gateway this email was legitimate. Behavioral analysis told Themis it was not.
See Your Risk: Calculate how many threats your SEG is missing
Indicators of Compromise
| Type | Indicator | Context |
|---|---|---|
| Email (From) | service@paypal.com | Legitimate PayPal sender |
| Email (Reply-To) | support@kissimmeenotarypublic[.]com | Merchant domain, DMARC=none |
| Domain | kissimmeenotarypublic[.]com | Registered 2017-08-16, GoDaddy, no DKIM |
| IP | 173.0.84.6 | PayPal mail server (mx17.slc.paypal.com) |
| DKIM | d=paypal.com, s=pp-dkim1 | Valid PayPal signature |
When a canceled invoice for a transaction you never started arrives with perfect authentication, the link scanner will not save you. Check where the Reply-To points before you respond.
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)