Table of Contents
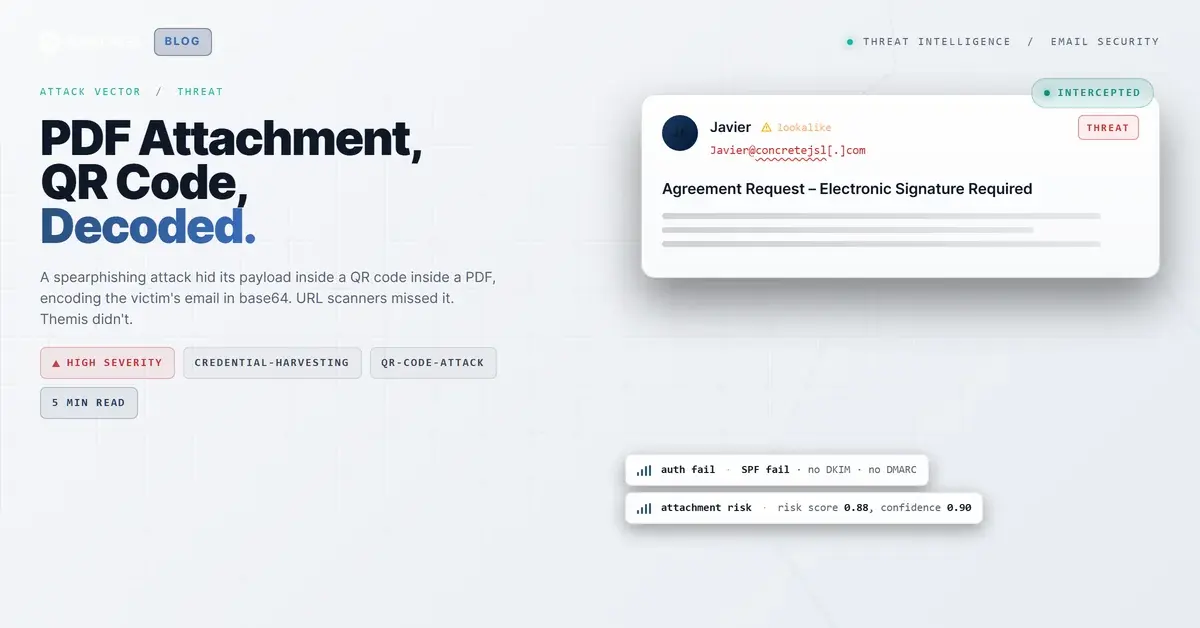
The link scanner came back clean. So did the PDF analysis. The email subject mimicked a DocuSign workflow, the attached PDF looked like a real agreement request, and every automated defense in the chain gave it a pass.
What they all missed was a QR code.
Buried inside the PDF was a code that decoded to a credential harvesting page, pre-loaded with the recipient's email address encoded in base64. This was not a bulk campaign. Somebody built a personalized payload for a specific target at a specific organization. Themis flagged it on arrival and quarantined it within six minutes.
---
Two Layers of Evasion, One Image
Most phishing attacks put a URL somewhere. In the body, in a button, in a redirect chain. That URL is what link-scanning tools are built to find and evaluate. Remove the URL from the email entirely, and the scanner has nothing to check.
That is exactly what this attack did.
The email body contained no links whatsoever. It was plain text, telling the recipient they had received an agreement requiring an electronic signature. The instruction to "scan the QR code" appeared only inside the attached PDF, _Agreement_Project2026.pdf. No scanner saw a URL to evaluate at the email level because there was no URL to find.
The PDF itself is the second layer. Modern PDF analysis tools extract text and embedded objects looking for malicious content: JavaScript, AcroForm fields, suspicious URLs in metadata. This file had none of those. No JavaScript. No form fields. The entire payload was an image, a QR code, which contains data that text extraction tools cannot read without first decoding the image as a QR symbol. Most pipeline scanners do not do that step.
The QR code decoded to hxxps://werkmastercom[.]userfocusedtech[.]de/yskuH/#Y3dpbHNvbkBpcm9uc2NhbGVzLmNvbQ==. The fragment after the # is base64. Decoded, it is the recipient's exact email address.
That is not a coincidence. The attacker encoded the target's email into the URL before sending. When the phishing page loads, it reads the fragment, pre-fills the credential form, and the harvesting feels seamless. It also means the attacker was tracking individual targets, not blasting a campaign at thousands of inboxes.
According to MITRE ATT&CK, this maps to T1566.001 (Spearphishing Attachment) and T1566.002 (Spearphishing Link) for the QR-encoded delivery, along with T1598 (Phishing for Information) for the credential harvesting objective. The QR delivery mechanism specifically is what CISA has flagged in its 2023 advisory on quishing attacks, noting that the technique exploits the gap between email security tools and mobile device behavior.
---
The Infrastructure Behind the Sender
The sender was Javier@concretejsl[.]com. The domain was registered in November 2024, four months old at time of attack. Purpose-built phishing domains rarely need to age. They exist to send one campaign and disappear.
Sending IP 104[.]168[.]56[.]196 is ColoCrossing-hosted out of Buffalo, NY, and is not an authorized sender for concretejsl[.]com. SPF returned a hard fail. No DKIM signature. No DMARC policy. The Verizon 2024 Data Breach Investigations Report consistently finds that social engineering attacks reaching inboxes exploit exactly this combination: domains that look plausible on the surface but fail every authentication check underneath.
The receiving mail system still delivered it.
The landing page domain userfocusedtech[.]de ran Cloudflare nameservers, a deliberate choice that obscures origin infrastructure and complicates takedown. The FBI IC3's 2024 Internet Crime Report regularly flags CDN and hosting-provider layering as a standard attacker technique for this reason.
---
What the Attack Chain Looked Like
Step by step:
- Delivery (02:53): Email arrives impersonating an e-signature workflow. SPF fails, no DKIM, no DMARC, no URLs in the body.
- Attachment open: Recipient sees a PDF instructing them to scan the QR code to sign the agreement.
- QR scan (intended): Phone opens
hxxps://werkmastercom[.]userfocusedtech[.]de/yskuH/#[base64-encoded-email]in a mobile browser, outside the corporate security perimeter. - Credential harvest (intended): Phishing page decodes the base64 fragment, pre-fills the target email, presents a credential prompt.
- Quarantine (02:59): Themis flagged on arrival using attachment risk scoring (0.88 risk, 0.90 confidence, MALICIOUS verdict), sender authentication failures, PDF language patterns, and community reputation signals. Six minutes from delivery to quarantine.
The URL scanner evaluated the decoded QR destination separately and returned a clean verdict. The evasion worked against the scanner. It did not work against behavioral AI.
The Proofpoint 2024 State of the Phish report documented a 51% year-over-year increase in quishing attacks, with organizations noting QR code detection required different tooling than URL-based defenses. This case is why: the URL was clean by reputation because the domain was new, not because it was safe. Reputation databases are backward-looking by design.
| Type | Indicator | Context |
|---|---|---|
| Domain | concretejsl[.]com | Sender domain, registered Nov 2024, SPF fail, no DKIM/DMARC |
| Domain | userfocusedtech[.]de | Phishing page host, Cloudflare-fronted |
| IP | 104[.]168[.]56[.]196 | Sending IP, ColoCrossing / Buffalo NY, unauthorized sender |
| File Hash (MD5) | 4c61313575a456669695711353bb03f5 | _Agreement_Project2026.pdf, risk 0.88 |
| URL | hxxps://werkmastercom[.]userfocusedtech[.]de/yskuH/#[base64-email] | QR-encoded credential harvesting destination |
---
What Security Teams Should Take From This
Microsoft's 2024 Digital Defense Report identifies QR-based phishing as one of the fastest-growing attachment-based attack vectors. The reason is structural: most security pipelines evaluate URLs, not images that encode URLs. If your stack cannot decode a QR code from inside a PDF, you have a gap that attackers are actively exploiting.
Three things to validate against this pattern:
- QR code extraction in attachment analysis. Your pipeline should decode QR codes in PDFs and evaluate the destination URL. Most legacy Secure Email Gateways (SEGs) do not. IRONSCALES' SEG replacement capabilities address this specifically.
- Authentication signal weighting. SPF fail from a four-month-old domain with no DKIM and no DMARC should be a high-confidence block signal, not a soft demerit overridden by a clean URL verdict. Here, the URL was clean because the domain was new. That is not the same as safe.
- Behavioral AI over reputation lists. The domain concretejsl[.]com had no threat reputation because it had never been reported. Behavioral detection and community signals from IRONSCALES' 17,000+ customer base catch new infrastructure that blocklists have not seen yet.
One investigative note: if you encounter a QR phishing URL with a fragment that looks like garbled text, decode it as base64. If it resolves to an email address, the campaign is individually targeted with per-recipient tracking tokens. That is a different threat posture than bulk phishing. Treat it accordingly.
The social engineering here was convincing enough that recipients focused on the DocuSign-style presentation, not the authentication failures underneath. Attackers invest in that presentation precisely because they know where defenders are looking.
Book a demo to see Themis catch attacks like this before they reach your users
---
Sources
- MITRE ATT&CK: T1566.001, T1566.002, T1598
- CISA: Phishing Guidance: Stopping the Attack Cycle at Phase One, 2023
- Verizon: 2024 Data Breach Investigations Report
- FBI IC3: 2024 Internet Crime Report
- Proofpoint: 2024 State of the Phish
- Microsoft: Digital Defense Report 2024
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)