Table of Contents
Most phishing emails want you to click the big shiny button. This one wanted you to click the small, gray "Unsubscribe" text at the bottom.
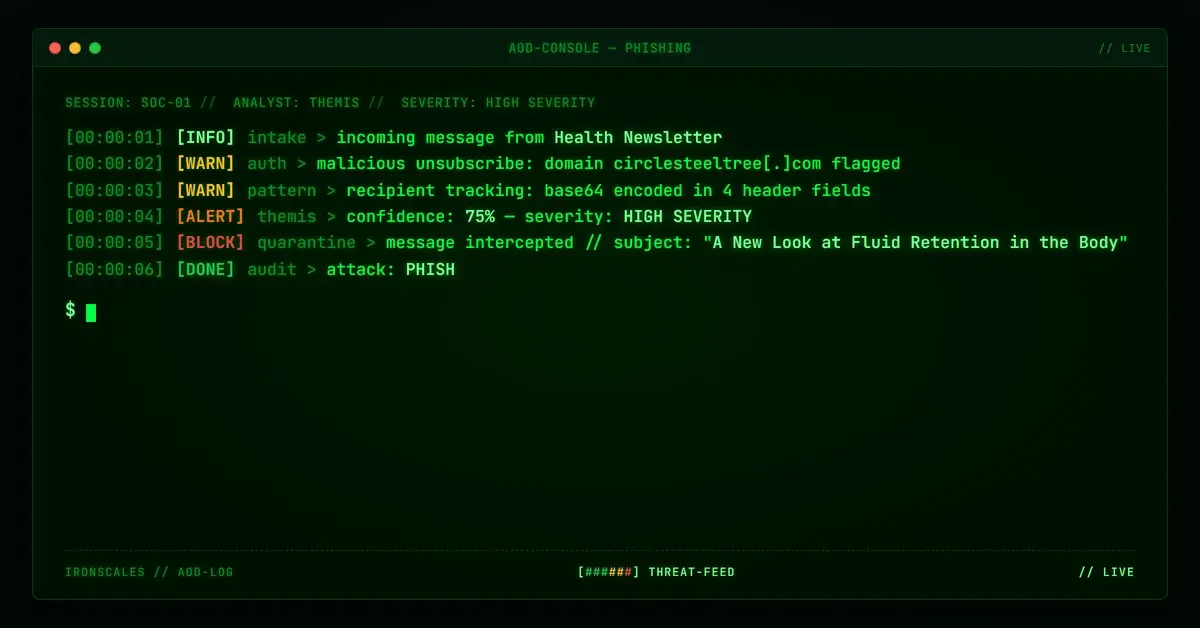
On April 5, 2026, a health newsletter titled "A New Look at Fluid Retention in the Body" landed in the inbox of a staff member at a large nonprofit. The email looked like standard wellness spam: vague research claims, a green "Learn More" CTA, and no organizational branding. Microsoft's anti-spam systems scored it SCL 9 (highest severity) and routed it to quarantine. But the real story was hiding in two places most security teams never check: the unsubscribe link and the message headers.
The unsubscribe link pointed to a domain flagged as malicious. The headers contained the recipient's email address encoded in base64 across four separate fields. This was not a careless spam blast. It was an instrumented campaign with layered monetization and deliberate exploitation of user trust in opt-out mechanisms.
A Health Newsletter That Never Mentions Health
The email body was crafted to be almost believable. It referenced "researchers associated with a medical college in Chicago" and described a biological process involving a "compound involved in how the body balances fluids and eliminates waste." No institution named. No study cited. The tone landed somewhere between a WebMD article and a late-night infomercial.
The visible CTA ("Learn More About This Discovery") linked to two destinations: a product sales page at hxxps://flushfactorplus[.]com/text[.]php and a ClickBank affiliate redirect at hxxps://hop[.]clickbank[.]net/?affiliate=ommnamah&vendor=flushplus. Both carried affiliate tracking parameters tying the click revenue to a specific affiliate account (ommnamah). This is a well-documented monetization pattern in which attackers earn commission on every click or purchase, regardless of whether the product is legitimate.
But the primary payload was elsewhere.
The Unsubscribe Trap
The "Unsubscribe" link pointed to hxxps://www[.]circlesteeltree[.]com/o-rmbl-r56-7dbb2e92d4771d0ae36aaf4fec90091c. WHOIS shows this domain was registered in 2019, sits behind Cloudflare, and uses privacy protection via Domain Protection Services, Inc. It has no visible web presence beyond serving as an endpoint for campaigns like this.
The URL rendered a clean "We are sorry to see you go" page with a single form field: "Your email address." The design was polished, complete with a blue "Unsubscribe" button and a subtle "Still receiving emails after unsubscribing?" help link.
This is the attack surface. A user who did the "right thing" by clicking unsubscribe would land on a page that harvests their email address. Submitting the form confirms the address is active and monitored, making it more valuable for future campaigns. The link was flagged as malicious by IRONSCALES Adaptive AI, which identified the URL's behavioral pattern as inconsistent with legitimate unsubscribe infrastructure.
See Your Risk: Calculate how many threats your SEG is missing
Four Layers of Base64 Recipient Tracking
The headers revealed the most technically interesting aspect of this campaign. The attacker embedded the recipient's email address (encoded in hexadecimal and base64) across four different header fields:
DKIM-Signature i= field: The identity parameter contained the recipient's address hex-encoded as 76697267696e69612e736c617940...@mail[.]dormiyol[.]com, which decodes to the target's email at the organization's domain. This is unusual. The DKIM i= field should reflect the sender's identity, not the recipient's.
Sender field: Same hex-encoded recipient address used as the envelope sender at mail[.]dormiyol[.]com.
Message-ID: A base64-encoded string that, when decoded, revealed the full sending infrastructure: a Unix timestamp, the sending IP (88[.]150[.]227[.]90), the sender address, and the recipient address, all concatenated with pipe delimiters.
List-Unsubscribe mailto: The unsubscribe mailto address contained two base64 segments. One decoded to a campaign identifier (OCCZ_112). The other decoded to the recipient's full email address.
This per-recipient instrumentation enables delivery tracking without visible pixels, correlates clicks to specific recipients, and confirms address validity when the unsubscribe form is submitted. According to the Microsoft Digital Defense Report 2024, phishing campaigns increasingly use metadata-level tracking to refine target lists without triggering traditional detection signals.
Infrastructure Built for Disposability
The sending infrastructure followed a pattern common in affiliate-driven phishing operations. The email originated from 88[.]150[.]227[.]90 (a UK-based IP) via a randomized hostname (terfw45tedfdsrtr[.]go[.]dalvasmart[.]com). The sending domain mail[.]dormiyol[.]com was registered through GoDaddy in September 2024, less than seven months before this campaign. DKIM and DMARC both passed because the attacker controlled the domain and configured authentication correctly, mapping to MITRE ATT&CK T1566.002 (Spearphishing Link) and T1036.005 (Masquerading).
The product domain flushfactorplus[.]com (Namecheap, April 2024) and relay domain dalvasmart[.]com (GoDaddy, August 2022) both use Cloudflare and privacy-shielded WHOIS records.
The message also passed through the recipient organization's Microsoft 365 tenant, where EOP assigned the SCL 9 score but routed it to quarantine rather than blocking outright.
Why the Unsubscribe Vector Works
Email users are trained to use unsubscribe links. CAN-SPAM requires them. Google and Yahoo's 2024 bulk sender requirements enforce one-click unsubscribe. Security awareness programs rarely warn against clicking unsubscribe because it is usually the correct action.
Attackers exploit this gap. The FBI IC3 Internet Crime Report 2024 documented over $12.5 billion in reported losses from phishing and related schemes. By placing the payload in the unsubscribe mechanism rather than the primary CTA, this campaign targeted the exact behavior that compliance frameworks encourage.
Community threat intelligence from across the IRONSCALES network of 35,000+ security professionals confirmed this pattern matched previously reported affiliate phishing activity, contributing to the 90% confidence classification.
Campaign Infrastructure
| Type | Indicator | Context |
|---|---|---|
| Domain | mail[.]dormiyol[.]com | Sending domain (GoDaddy, registered Sep 2024) |
| Domain | circlesteeltree[.]com | Malicious unsubscribe landing page (Cloudflare) |
| Domain | flushfactorplus[.]com | Affiliate product/sales page (Namecheap, Cloudflare) |
| Domain | dalvasmart[.]com | SMTP relay infrastructure (GoDaddy) |
| URL | hxxps://www[.]circlesteeltree[.]com/o-rmbl-r56-7dbb2e92d4771d0ae36aaf4fec90091c | Malicious unsubscribe page (verdict: malicious) |
| URL | hxxps://flushfactorplus[.]com/text[.]php?affop=1&hop=ommnamah | Affiliate product funnel |
| URL | hxxps://hop[.]clickbank[.]net/?affiliate=ommnamah&vendor=flushplus | ClickBank affiliate redirect |
| IP | 88[.]150[.]227[.]90 | Sending server IP (UK) |
leannelebsack@mail[.]dormiyol[.]com | Sender address | |
| Hostname | terfw45tedfdsrtr[.]go[.]dalvasmart[.]com | SMTP relay HELO hostname |
What to Do About It
Inspect unsubscribe links before clicking. Hover over the link and verify it points to the sender's actual domain or a recognized email service provider. If the unsubscribe URL uses an unrelated domain, report the email instead.
Flag first-time external senders with high spam scores. This message passed DKIM and DMARC but scored SCL 9. Authentication alone is not a sufficient trust signal. Combine authentication results with sender reputation, behavioral signals, and community intelligence for classification decisions.
Decode obfuscated headers during investigation. Base64 and hex encoding in DKIM selectors, Sender fields, and Message-IDs can reveal recipient tracking, campaign identifiers, and infrastructure details invisible in standard header views. A DKIM i= field that does not match the sending domain's expected identity is a high-confidence indicator of malicious intent.
Block or sandbox links to recently registered domains. The sending domain was less than seven months old. Domain age remains one of the strongest predictive signals for phishing infrastructure, as documented in the Verizon DBIR 2024.
Report affiliate abuse. ClickBank and similar platforms have abuse reporting mechanisms. Reporting affiliate parameters from phishing campaigns disrupts attacker monetization and can lead to account termination.
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)