Table of Contents
The email arrived on a Tuesday afternoon and looked, at a glance, like every other Google Calendar notification. A meeting invite. A subject line referencing a transaction. RSVP buttons. The Google logo at the top.
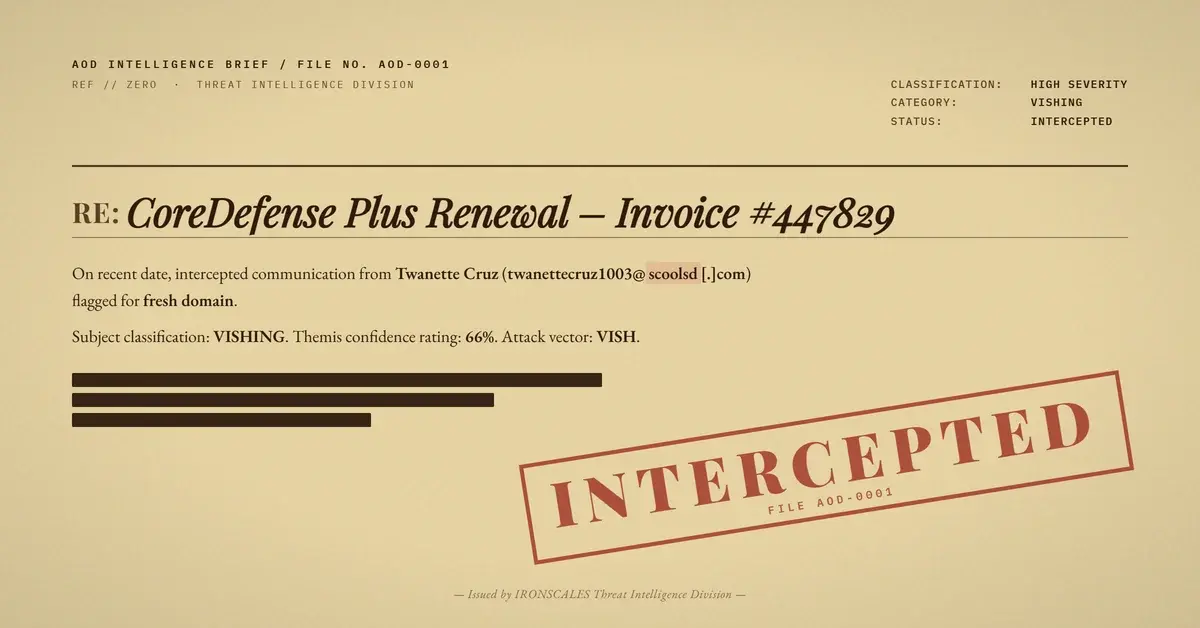
Below the invitation metadata was a billing notice: "CoreDefense Plus" renewed, $399.77 charged. "If you didn't make this purchase... call our customer care representative (808)-321-8085 (Toll Free)."
No link to a phishing page. No malicious attachment. No credential harvest form. The entire payload was a phone number.
When the Attack Surface Is Your Calendar
The security team's stack had no technical artifact to flag. The links in the email resolved to calendar.google.com and scanned clean. The .ics attachment contained no executable code, no embedded URLs, no alarm actions fetching external resources. Attachment sandboxes gave it a clean verdict. URL reputation engines had nothing to analyze.
DKIM passed. Google signed the outbound message from its own mail infrastructure, as it does for any Google Workspace account. That signature confirms Google sent the message. It says nothing about whether the sender's domain is legitimate.
The domain it came from, scoolsd[.]com, had been registered a few hours before the email was sent. Created March 17, 2026, same day as the attack. Registered through Hosting Concepts B.V. via Registrar.eu, privacy-protected, DNSSEC unsigned. No SPF record published, so the authentication result for the return-path was spf=none. No reputation. No history.
None of that registered in URL scan results, because there were no URLs to scan.
The Script Behind the Call
Callback phishing, also called Telephone-Oriented Attack Delivery (TOAD), has been a growing share of the vishing (voice phishing) threat landscape. According to the FBI's 2024 Internet Crime Report, BEC (Business Email Compromise) and related fraud cost U.S. businesses over $2.9 billion in reported losses, with phone-based social engineering a significant and undercounted contributor (FBI IC3 2024).
The model is straightforward. The attacker sends a notification that creates financial urgency, then waits for the victim to call. On the other end of the line is a live operator, or a convincing automated script, ready to socially engineer credentials, payment details, or remote access under the guise of "customer support."
In this case, the fake product name ("CoreDefense Plus") mimics legitimate antivirus software names well enough to be plausible. The charge amount ($399.77) is high enough to alarm but not so high as to seem implausible for a software renewal. The reference numbers and "Register Client UID" fields add just enough bureaucratic texture to look like a real receipt.
The organizer identity in the invite, "Twanette Cruz," has no verifiable presence tied to that domain. The email account (twanettecruz1003@scoolsd[.]com) was almost certainly created minutes before sending. The phone number is toll-free, making it cost-free to operate at scale.
See Your Risk: Find out how many threats like this your current security stack is missing
What Passed, What Flagged, and Why It Matters
This attack is specifically engineered to be invisible to the tools most email security stacks rely on.
URL reputation checks had nothing to evaluate. The only URLs in the email pointed to calendar.google.com. Sandbox detonation of the attachment found a clean .ics file. DKIM validation returned pass. SPF returned none, which many tools treat as inconclusive rather than suspicious.
Verizon's 2024 DBIR found that the human element is involved in 68% of breaches, and social engineering remains one of the top initial access techniques used by threat actors (Verizon DBIR 2024). Attacks like this one are designed to route around technical controls entirely and land directly in human psychology: you got charged $400 for something you didn't buy, here's the number to call.
The Microsoft Digital Defense Report 2024 also notes the growing use of legitimate cloud services as attack delivery infrastructure, precisely because those services have high reputation scores that defeat URL filtering (Microsoft Digital Defense Report 2024). Google Calendar is not a malicious service. That's the point.
Themis flagged this incident based on a combination of signals: the freshly-registered domain (scoolsd[.]com with a same-day creation date), the absence of any SPF policy, behavioral patterns in the invite content consistent with financial-urgency social engineering, and community-level confidence signals from similar incidents reported across the IRONSCALES platform. The confidence score came in at 66%, labeled as a vishing attack. The platform routed it for review rather than letting it sit in the inbox.
MITRE ATT&CK maps this to Spearphishing Attachment (T1566.001) for the .ics delivery vector, Phishing for Information (T1598) for the off-channel voice harvest, and User Execution (T1204) for the required victim action (calling the number). The attack chain is simple, which is part of why it works.
Indicators of Compromise
| Type | Indicator | Context |
|---|---|---|
| Domain | scoolsd[.]com | Attacker-registered domain, created 2026-03-17 |
twanettecruz1003@scoolsd[.]com | Attacker organizer account | |
| Phone | (808)-321-8085 | Vishing callback number in ICS DESCRIPTION |
| ICS Hash (MD5) | 849e769d4923a487f109e07aed005041 | invite.ics attachment |
Closing the Gap That Wasn't on Your Map
The uncomfortable reality of zero-link vishing is that it doesn't fail against well-tuned URL filtering or a mature sandboxing solution. It doesn't need to. It bypasses them by design.
Defending against it requires a different set of controls. Domain age and reputation checks at the envelope level, not just for URLs. Behavioral analysis of calendar invite content, not just attachment sandboxing. Community intelligence that surfaces patterns across organizations, not just local telemetry. And user training that specifically addresses callback phishing scenarios, since this attack lives or dies on whether the recipient picks up the phone.
Security awareness training that covers TOAD and callback fraud scenarios is increasingly important as these attacks scale. The FBI's IC3 data shows the phone-based social engineering vector growing year over year, often targeting finance and accounting roles who are already primed to respond to billing and payment alerts. Vishing simulations that include the calendar-as-delivery-mechanism specifically would help build recognition before it matters.
Traditional email defenses are built around the assumption that attacks have a technical payload. A URL to block, a file to sandbox, a domain to blacklist. When the payload is a phone number buried in a calendar description, that assumption is wrong.
Across 1,921 organizations in the IRONSCALES customer base, the pattern of abusing legitimate cloud services for social engineering delivery, where the infrastructure is trusted even when the content is not, shows up consistently in callback phishing campaigns. The signal isn't always in the link. Sometimes it's in the domain registration date, the missing SPF record, and the phone number your employee is about to call.
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)