Table of Contents
Every security check passed. SPF: pass. DKIM: pass. DMARC: pass with a p=REJECT policy. The sending IP was on Brightwheel's authorized list. The email looked exactly like a legitimate childcare billing notification, down to the logo, the branded button, and a real child's name in the subject line.
The only thing wrong was a single header nobody looks at: Reply-To.
How the Attack Was Constructed
The email arrived at a K-12 school employee's inbox on December 1, 2025. Subject: "Your most recent billing statement for [Student Name] is now available." The display name appeared to match a known internal contact. The sending address was no-reply@notify[.]mybrightwheel[.]com.
Brightwheel is a widely used childcare management platform. Schools and daycare centers use it for attendance, messaging, and billing. Transactional emails go out through Postmark (pm.mtasv[.]net). This message came through that exact infrastructure, with full authentication credentials in place.
The body was a standard Brightwheel HTML template: logo, "View statement" button, footer with social links. All links pointed (via Postmark's track.pstmrk[.]it tracking proxy) to legitimate mybrightwheel[.]com destinations.
One line betrayed everything.
"If you have questions, please contact kstpierre@seniorlifestyle[.]com."
That email address, which also appeared in the Reply-To header, belongs to a domain with no relationship to Brightwheel, childcare, or the school. seniorlifestyle[.]com is an attacker-controlled address used to intercept any replies from the victim.
What the Attacker Actually Needed
The goal here was not a credential-harvesting link. The links in the email went to real Brightwheel pages. The play was social engineering through reply.
The attacker's model: a school employee receives a billing notification for a child named in the subject line. The name creates assumed legitimacy. The employee either clicks "View statement" (a real page, no harvest there) or, more likely, replies with a question. "I don't recognize this charge." "Can you explain this?" "I think there's a mistake."
That reply goes to kstpierre@seniorlifestyle[.]com. The attacker now has an open conversation thread with someone who believes they're talking to Brightwheel support. From there, the social engineering writes itself: incorrect charges, verification requests, payment redirects, or credential collection through a follow-up "support" link.
This is Business Email Compromise (BEC) without a spoofed domain, without a credential harvest page, and without any malicious links. The entire attack surface is one misconfigured header.
Why Authentication Checks Are Not Enough Here
The email authentication system worked exactly as designed. Brightwheel's DMARC policy is p=REJECT, meaning unauthenticated mail claiming to be from their domain should be blocked outright. This email was authenticated, because it was sent through Brightwheel's own platform or through a Postmark account that has been given Brightwheel's signing credentials.
This is the core tension in email authentication as a defense layer. SPF, DKIM, and DMARC verify that a message was sent from authorized infrastructure for a given domain. They say nothing about whether the person who authorized that send intended to phish someone.
When an attacker gains access to a SaaS platform's email-sending capability, or simply creates an account on a platform that sends on their behalf under the platform's own domain, authentication becomes irrelevant. According to the Verizon 2024 Data Breach Investigations Report, social engineering was involved in 73% of all breaches, and the effectiveness of these attacks depends far less on technical sophistication than on contextual credibility. A billing email with a child's name in the subject line has contextual credibility in abundance.
See Your Risk: Calculate how many threats your SEG is missing
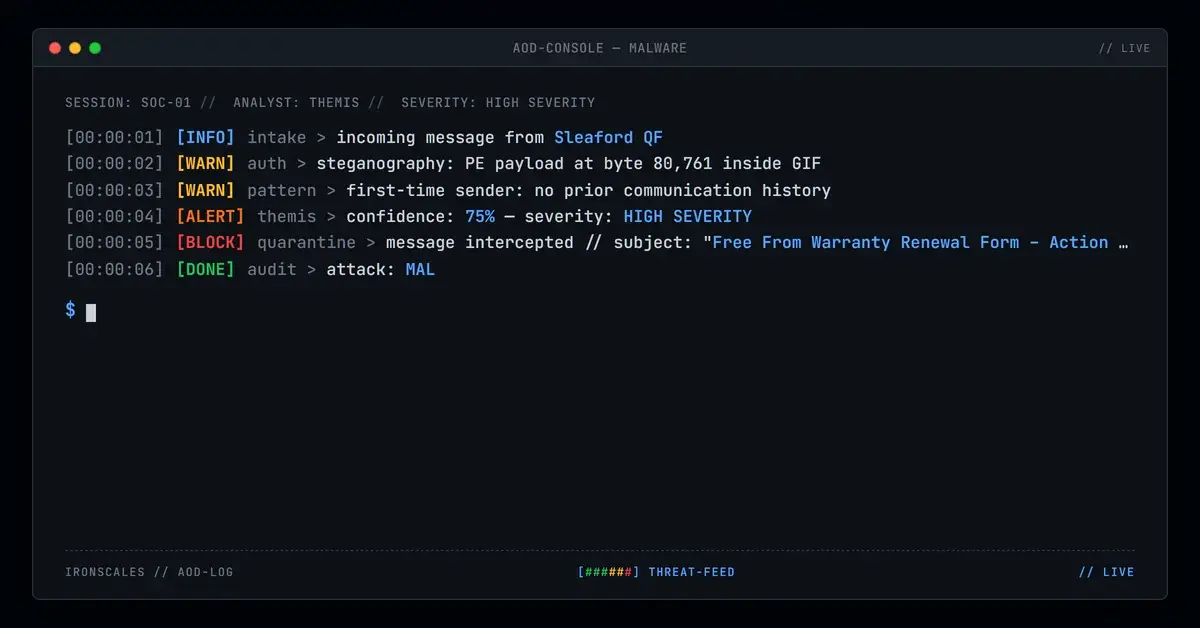
The Tell Themis Caught
The IRONSCALES platform had prior knowledge of Brightwheel-associated addresses. The display name was known in the IRONSCALES community as associated with support@mybrightwheel[.]com, not no-reply@notify[.]mybrightwheel[.]com.
That mismatch, display name tied to a known address now appearing from a different address, is an exact display name impersonation signal. Themis flagged it. Combined with community intelligence showing similar patterns flagged as phishing across other organizations, the confidence threshold crossed.
Four mailboxes were quarantined on April 2, 2026. The emails never got a reply.
There is also a secondary tell any analyst can spot: the greeting reads "Hello ," with no name. The mail merge token failed to populate. Legitimate transactional platforms always fill in the recipient name from account data. A blank greeting in a billing notification means the sender lacks access to actual account data, or is running a bulk send with a broken template. Neither is reassuring.
Why Filtering Tools Miss This
Microsoft's 2024 Digital Defense Report notes that attackers increasingly exploit trusted cloud infrastructure to deliver malicious content, because reputation-based filtering cannot penalize legitimate services without unacceptable false positive rates.
The pattern works because of how tooling is scoped. URL scanners check destinations. IP reputation scores sending infrastructure. DMARC enforcement blocks unauthorized domain use, not authorized misuse. None of these gates inspect the Reply-To header against behavioral expectations.
What this attack required was behavioral analysis: display name history against sending address, Reply-To domain against From domain, and a failed personalization token. None of those signals are in the authentication layer. The FBI's 2024 Internet Crime Report documented $2.9 billion in BEC losses, with a significant portion in this exact category: legitimate infrastructure, intercepted reply, social engineering close.
Phishing through trusted third-party services maps to MITRE ATT&CK T1598.003 (Spearphishing via Service). The technique is documented. The defenses have not kept pace.
What to Do About It
The standard advice does not fully apply here. You cannot block Brightwheel or Postmark without creating significant collateral damage for schools and childcare organizations that legitimately use both.
What works:
1. Flag Reply-To mismatches. If the Reply-To domain does not match the From domain, that is an anomaly worth investigating, particularly for billing, HR, and financial communications. Most email security platforms can surface this. Most organizations have not turned it on.
2. Check display name history. A display name that has appeared previously associated with a different address is a red flag. This requires a behavioral baseline, something static reputation scoring cannot provide.
3. Train on reply-chain attacks. Most phishing awareness training focuses on malicious links and attachments. Reply-To hijacks leave no malicious links. The payload is the reply. Train users to verify contact addresses before responding to billing or financial communications, even when the email looks perfect.
4. Look for broken personalization. "Hello ," is not subtle. A missing name in a billing notification is worth a second look. This is a teachable pattern.
The IRONSCALES platform detected this attack not by scanning links or checking sender reputation, but by comparing what it knew about the display name against the sending address, then cross-referencing with community intelligence from across its global deployment. That combination caught what authentication headers could not.
Indicators of Compromise
| Indicator | Type | Context |
|---|---|---|
kstpierre@seniorlifestyle[.]com | Attacker-controlled Reply-To and contact address | |
seniorlifestyle[.]com | Domain | Attacker-controlled domain used for reply interception |
no-reply@notify[.]mybrightwheel[.]com | Legitimate Brightwheel sending address (abused) | |
track[.]pstmrk[.]it | Domain | Postmark tracking proxy (legitimate, used to wrap all links) |
104[.]245[.]209[.]210 | IP | Postmark MTA (mta210a-ord.mtasv[.]net), legitimate Brightwheel-authorized sender |
| Subject: "Your most recent billing statement for [Student Name] is now available" | Subject line | Lure subject, child name used for credibility |
For business email compromise incidents that exploit trusted SaaS infrastructure, IOCs have limited defensive value. The sending infrastructure is legitimate and will keep being used that way. The response priority is behavioral detection, not IP or domain blocking. See CISA phishing guidance for organizational reporting frameworks.
The same technique works against any SaaS platform that allows transactional email customization. Review your threat intelligence posture accordingly.
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)