Table of Contents
The email could have come from any B2B content marketing platform. A professional header. A well-known brand's logo. A call to action offering an executive pricing guide for HR management software. The layout was polished, the tone was measured, and the offer was specific enough to be plausible: "HR Management Software Executive Pricing Guide 2025."
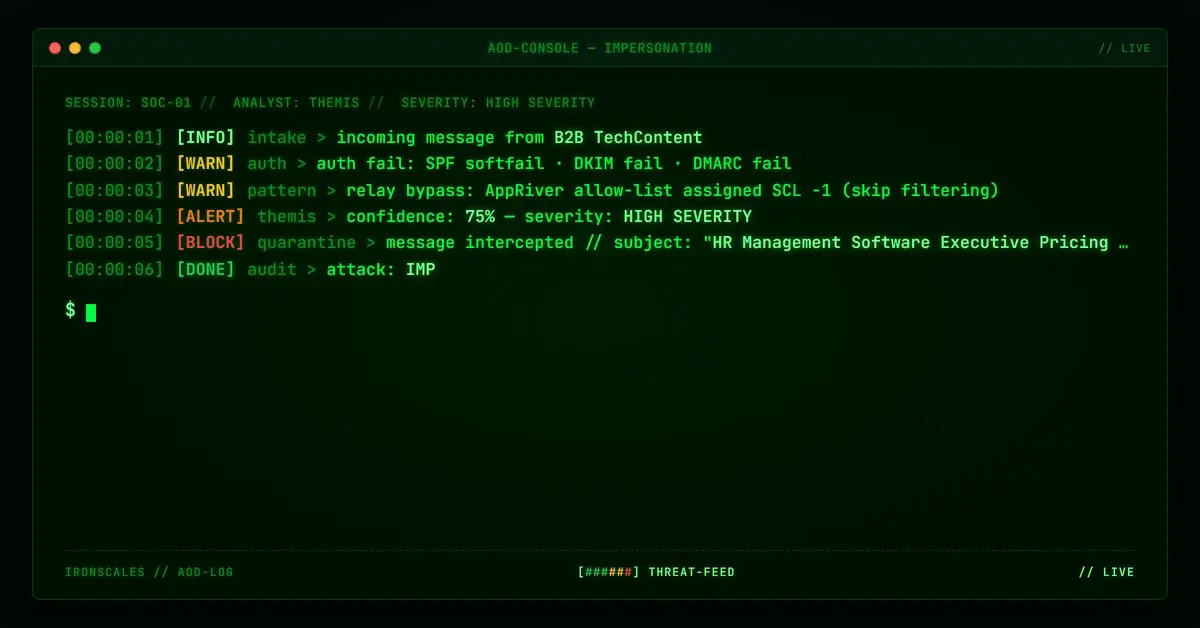
It arrived in four mailboxes. SPF softfailed. DKIM failed. DMARC failed. And the email security stack assigned it an SCL of -1, meaning it skipped spam filtering entirely.
That last part is the one worth understanding.
Borrowed Brand, Borrowed Trust
The email presented itself as a SelectHub research report, a recognizable name in the B2B software evaluation space. The logo matched. The layout matched. The typography was consistent with SelectHub's published content style. To a recipient evaluating the email at face value, this looked like a legitimate marketing offer from a company that produces software comparison guides.
The sender address told a different story. The From header showed "B2B TechContent" with an address at ehrtechbook[.]com, a domain registered through IONOS in June 2023 with privacy-protected WHOIS. The domain had a DMARC policy of p=none (monitor only, no enforcement) and an SPF record using the ~all softfail qualifier, meaning messages from unauthorized IPs would not be rejected.
Every link in the email, including the prominent "View Report" button, pointed to ehrtechbook[.]com rather than any SelectHub property. The recipient was being invited to click through to attacker-controlled infrastructure while looking at another company's branding.
This is brand impersonation at its most operationally mature. The attacker did not need to compromise SelectHub's infrastructure or spoof their domain. They built a visual replica and hosted it on their own sending domain, counting on the professional appearance to do the work that authentication could not.
The Relay That Overwrote the Verdict
The email's relay path explains how a message with triple authentication failure reached the inbox with a skip-filtering designation. The message transited through AppRiver (IP 8[.]31[.]233[.]206), a cloud email security relay. At the AppRiver hop, SPF and DKIM both recorded as passing. By the time the message reached the recipient's Microsoft 365 environment, the results had flipped:
- SPF: Softfail (AppRiver's IP is not authorized for
ehrtechbook[.]com) - DKIM: Fail (body hash mismatch, meaning the message body was modified after signing)
- DMARC: Fail (neither SPF nor DKIM aligned)
Despite these failures, the SCL was -1. This value is assigned when a message comes from a source on the organization's allow list, effectively telling the filtering stack to trust it regardless of what authentication returned. The allow-list entry for AppRiver was doing its job, trusting the relay, but the relay was passing through a message that failed every downstream check.
The Microsoft Digital Defense Report 2024 documents this class of problem: relay allow-lists create implicit trust that attackers exploit by routing messages through intermediaries that organizations have pre-approved. The authentication failure happens after the trust decision has already been made.
According to the FBI IC3 2024 Internet Crime Report, phishing and its variants generated the highest volume of cybercrime complaints in 2024, with losses exceeding $9.3 billion. Relay trust exploitation is one of the mechanisms that keeps those numbers climbing.
The Security Vendor's URL Wrapper as a Trust Signal
The links in the email carried an additional layer of apparent legitimacy. Each URL was wrapped through link[.]edgepilot[.]com, the URL protection service operated by Inky, an email security vendor. EdgePilot rewrites URLs in transit so they pass through Inky's scanning infrastructure before reaching the final destination.
In a normal deployment, this wrapping protects users by scanning the destination before allowing the click-through. In this context, the wrapping had the opposite effect. A recipient (or a downstream scanner) seeing a link[.]edgepilot[.]com URL might reasonably conclude that the link had already been vetted by a security product. The security vendor's own domain became part of the attack's trust surface.
The destination domain, b2b-techcontent[.]com, was registered through GoDaddy in December 2023, used Cloudflare nameservers, and was flagged as malicious. This is the domain the recipient would have landed on after clicking through the EdgePilot wrapper. A freshly registered domain with no legitimate web presence, hidden behind a security vendor's URL rewrite.
See Your Risk: Calculate how many threats your SEG is missing
BCL 9: The Infrastructure Tells on Itself
Microsoft assigned this message a Bulk Confidence Level (BCL) of 9, the highest possible score. BCL 9 means the sending infrastructure is a confirmed high-volume bulk sender. This is not an occasional marketing email. This is infrastructure purpose-built to send at scale.
Combined with the brand impersonation, authentication failures, and a malicious landing domain, the BCL score fills in the operational picture. The attacker invested in sending infrastructure (registered domains, configured mail servers, volume capacity), built a professional template borrowing a recognizable brand's visual identity, and relied on relay trust and URL wrapping to paper over the technical signals that should have flagged the message.
The Verizon 2024 Data Breach Investigations Report found that 68% of breaches involved the human element. Attacks like this one succeed precisely because they target human pattern recognition. The email looks like marketing. It reads like marketing. The brand is familiar. The offer is relevant. The only tell is in the infrastructure, and that infrastructure was laundered through two layers of borrowed trust before it reached the inbox.
What Behavioral Detection Caught
Themis flagged this message at 89% confidence across all four affected mailboxes, tagging it for VIP recipient targeting. The detection was not based on the link destination or the authentication result. It was based on the behavioral fingerprint: a first-time sender using another company's brand assets, a mismatch between the displayed brand and the sending domain, and a bulk sending pattern inconsistent with legitimate B2B content distribution.
The email was quarantined before any recipient clicked through the EdgePilot-wrapped links to the malicious landing domain.
Indicators of Compromise
| Type | Indicator | Context |
|---|---|---|
| Sending Domain | ehrtechbook[.]com | Registered Jun 2023, IONOS, privacy WHOIS, DMARC p=none |
| Sender Address | olivia@ehrtechbook[.]com | Display name "B2B TechContent" |
| Landing Domain | b2b-techcontent[.]com | Registered Dec 2023, GoDaddy, Cloudflare NS, flagged MALICIOUS |
| URL Wrapper | link[.]edgepilot[.]com | Inky EdgePilot URL protection service |
| Relay IP | 8[.]31[.]233[.]206 | AppRiver relay, allow-listed at recipient org |
| SCL | -1 | Skip filtering (relay allow-list override) |
| BCL | 9 | Confirmed bulk sender infrastructure |
| SPF | Softfail | AppRiver IP not authorized for ehrtechbook[.]com |
| DKIM | Fail | Body hash mismatch (message modified in transit) |
| DMARC | Fail | Neither SPF nor DKIM aligned |
MITRE ATT&CK Mapping: - T1566.002: Phishing, Spearphishing Link (malicious link delivery via B2B content marketing lure) - T1036.005: Masquerading, Match Legitimate Name or Location (SelectHub brand impersonation)
Related attacks
| Attack | What happened |
|---|---|
| Every Link Was Real: DocuSign Reply-To Diversion With a Same-Day Domain | A phishing email sent through legitimate DocuSign infrastructure passed SPF, DKIM, and DMARC with perfect scores. |
| The Button Text Was the Weapon: Unicode RTL Obfuscation Inside a DocuSign Lure | Attackers embedded Unicode right-to-left marks directly inside a CTA button label to scatter the string for NLP scanners. |
| The DocuSign Lure That Used Google as a Trust Shield (And Encoded Your Email in the Link) | A DocuSign phishing email hid its harvest domain behind a google.com redirect and encoded the recipient's exact email address into the link as base64. |
| The Email That Passed Every Security Check (Because Adobe Sent It) | A phishing campaign targeting school district staff used Adobe's own sending infrastructure, real DKIM signatures. |
| The Phishing Infrastructure Was Canva. The Delivery Mechanism Was Canva. The Authentication Was Canva. | An attacker signed up for Canva, built a phishing lure as a design, and used the platform's own sharing feature to deliver it. |
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)