Table of Contents
The email arrived with no body. No text. No links. No images. Nothing for a content scanner to evaluate. Just a subject line ("Hincol Voicemail Notification"), a sender from a Japanese industrial company, and a single attachment: Ambac_Voicemail.ics.
Three different organizations referenced across one email. A Japanese manufacturer in the From header. An Indian chemical company in the display name. A US financial services firm in the calendar attachment. And an empty body that gave every content-based scanner exactly nothing to work with.
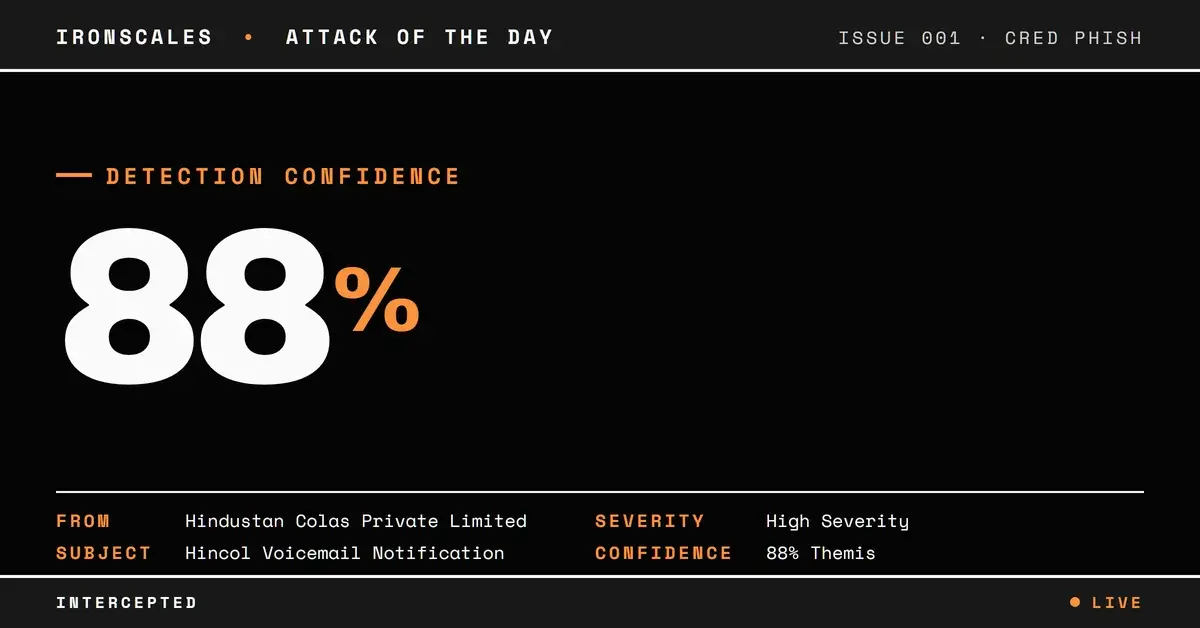
IRONSCALES Themis flagged it with 88% confidence and auto-resolved it as phishing. Here's what made this attack worth examining, and why calendar-based phishing is a vector that most organizations aren't watching.
Get a Demo: See how IRONSCALES detects attacks that bypass traditional content scanning
The Empty Body Problem
Email security has spent decades getting better at analyzing what's inside email bodies. Natural language processing catches social engineering. URL analysis follows redirect chains. Image recognition identifies brand impersonation. Keyword filters flag urgency language.
All of those capabilities depend on having content to analyze.
This email had none. The body field was completely empty, a state that legitimate business emails almost never have. Yet most email security systems don't flag empty bodies as inherently suspicious, because calendar invites, read receipts, and delivery notifications sometimes arrive with minimal or no body content.
The attacker exploited this blind spot by putting the entire payload into the .ics attachment. Calendar files can contain event descriptions with embedded URLs, organizer fields with spoofed email addresses, and DESCRIPTION properties with social engineering text. When a recipient opens (or their email client auto-processes) the .ics file, the malicious content enters their calendar rather than their inbox.
According to Microsoft's 2024 Digital Defense Report, calendar-based phishing has been growing as attackers seek vectors that sidestep traditional email body analysis. The technique is particularly effective against mobile users, where calendar apps may auto-accept invites without displaying the full context.
Identity Fragmentation: Three Organizations, One Email
The most technically interesting aspect of this attack is how many different identities the attacker layered across the message:
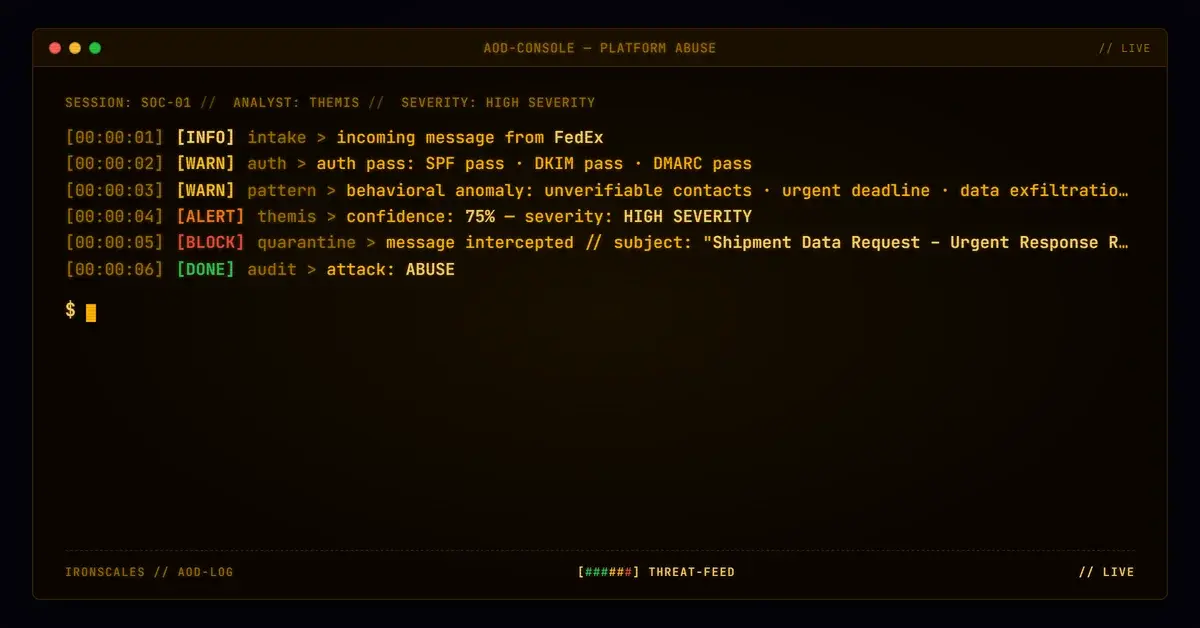
The envelope sender: admin@fujimisangyo[.]co[.]jp, a legitimate Japanese industrial company (registered since 2001). SPF passed for this domain, meaning the sending IP (120[.]137[.]171[.]108, a Japanese mail host at mgsp105.cybermail[.]jp) was authorized to send on behalf of the domain.
The display name: "Hindustan Colas Private Limited," an Indian chemical and infrastructure company. This name appeared in the incident metadata as the sender identity, creating confusion about who actually sent the email.
The calendar organizer: calendar@ambac[.]com, referencing Ambac Financial Group, a US financial services company. The .ics file's organizer field used this address, making the calendar event appear to originate from a legitimate financial institution.
The recipient header: lng@ambac[.]com, but the email was actually delivered to employees at a cybersecurity company.
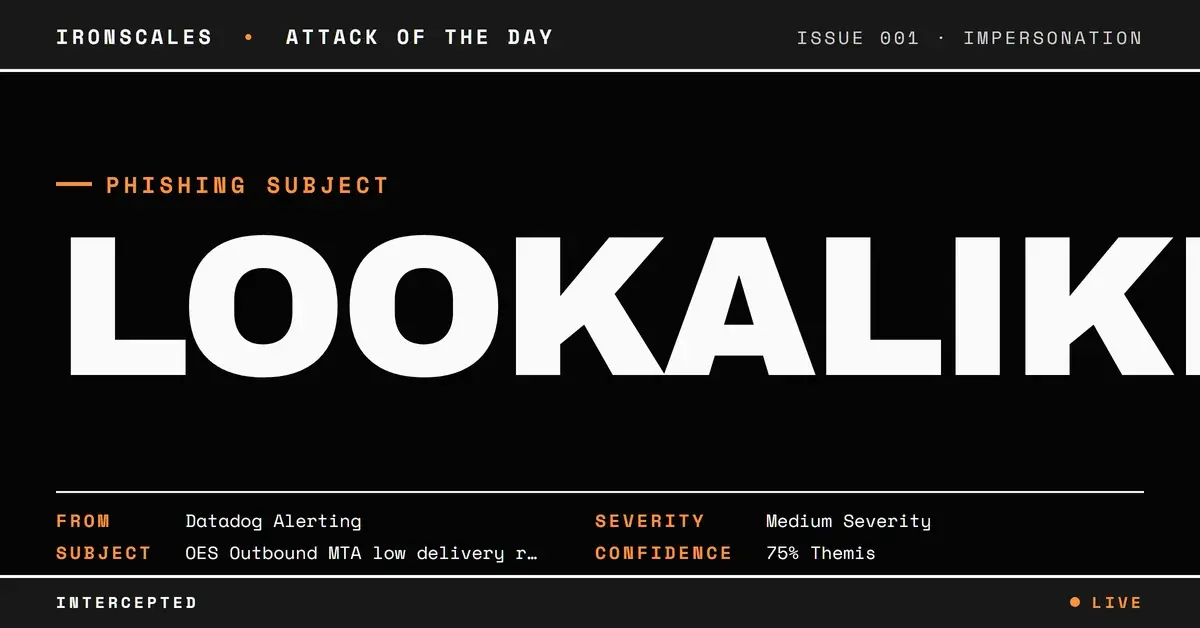
This identity fragmentation isn't random. It serves a specific purpose: it makes it extremely difficult for automated systems to determine the email's "true" sender identity. Different security tools examine different header fields, and when each field references a different legitimate organization, the signals cancel each other out rather than reinforcing a verdict.
| Type | Indicator | Context |
|---|---|---|
admin@fujimisangyo[.]co[.]jp | Envelope sender (Japanese industrial) | |
calendar@ambac[.]com | Calendar organizer (US financial) | |
| Domain | fujimisangyo[.]co[.]jp | Sending domain (SPF pass, no DKIM) |
| Domain | ambac[.]com | Impersonated in .ics organizer field |
| IP | 120[.]137[.]171[.]108 | Sending server (Japan) |
| Attachment | Ambac_Voicemail.ics | Calendar payload (15,659 bytes) |
| Hash (MD5) | e03894deb5d6f904456707011a8a6441 | .ics file hash |
See Your Risk: Calculate how many threats your SEG is missing
The Voicemail Pretext
The voicemail angle is deliberate. "You have a voicemail" creates urgency without requiring specific context. The recipient doesn't need to be expecting a call from Ambac Financial Group. They just need to be curious enough to open the .ics file and click whatever link is inside.
Voicemail lures have been a reliable social engineering vector since the early days of phishing. CISA's phishing guidance specifically calls out voicemail notification phishing as a growing category, particularly when combined with callback phishing (sometimes called TOAD, Telephone-Oriented Attack Delivery).
In this case, the voicemail theme serves an additional purpose: it provides a plausible reason for the email body to be empty. Recipients expect voicemail notifications to be brief, system-generated messages. An empty body with an attachment feels normal in that context.
Authentication: Partial Signals, Full Delivery
The authentication picture was mixed, which is exactly how the attacker wanted it:
- SPF: Pass (the sending IP was authorized by
fujimisangyo[.]co[.]jp) - DKIM: None (the message wasn't signed)
- DMARC: bestguesspass (Microsoft's heuristic pass when no explicit DMARC record exists)
The SPF pass was enough to prevent outright rejection. The lack of DKIM meant there was no cryptographic proof of message integrity, but many organizations don't enforce DKIM-only policies. The "bestguesspass" DMARC result is Microsoft's way of handling domains without published DMARC records, essentially giving the benefit of the doubt.
Themis didn't need authentication to tell the story. IRONSCALES Adaptive AI analyzed the behavioral pattern: first-time sender, empty body, calendar attachment with financial services branding, identity mismatches across headers. Combined with community intelligence from similar .ics-based attacks reported across the platform, Themis auto-resolved the incident as phishing with 88% confidence. Two affected mailboxes were quarantined within minutes.
Defending Against Calendar-Based Attacks
Don't auto-accept calendar invites from external senders. Configure email clients and mobile devices to require manual acceptance of .ics files from unknown senders. This single setting prevents calendar injection from gaining a persistent foothold.
Scan attachments beyond file type. Calendar files should be inspected for embedded URLs, organizer field spoofing, and DESCRIPTION content, not just checked for malware signatures.
Flag empty-body emails with attachments. Legitimate business emails almost always have body content. An empty body combined with an attachment from a first-time external sender is a strong composite signal for phishing.
Correlate identities across header fields. When the From domain, display name, calendar organizer, and To header all reference different organizations, that's identity fragmentation, and it's a reliable indicator of a constructed phishing message.
Try It Free: Start your free trial of IRONSCALES
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)