Table of Contents
The email came from the CEO. At least, that is what the display name said. It landed in the payroll distribution group inbox with a polite request to update banking details before the next pay cycle. No links. No attachments. Just a direct ask from the person whose name sits at the top of the org chart.
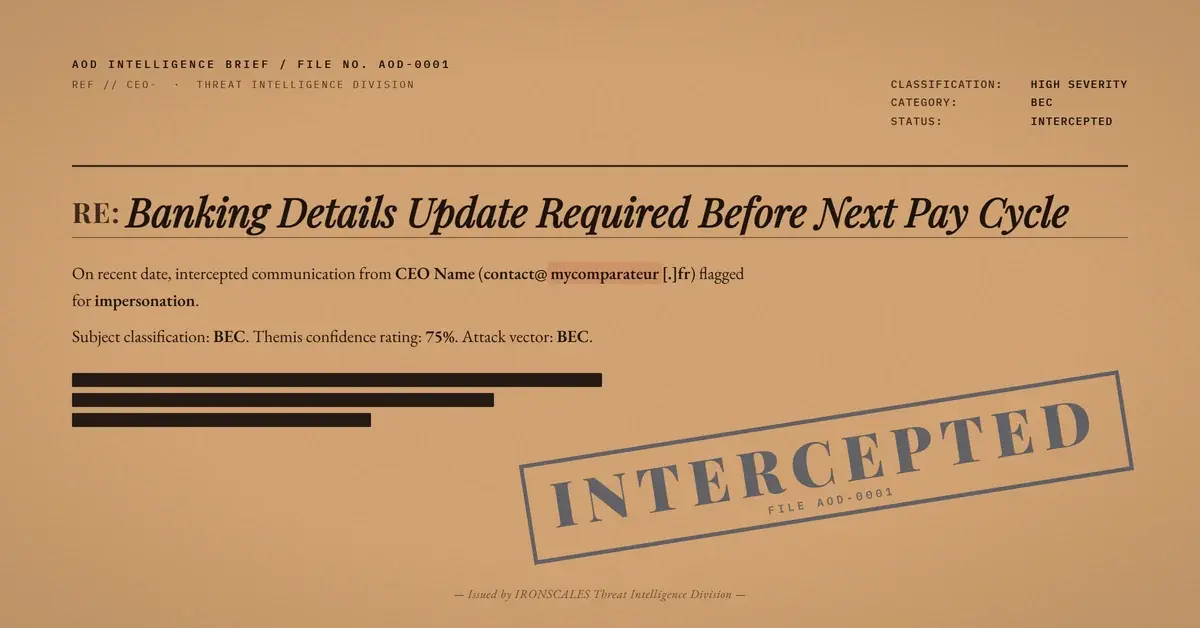
In April 2026, IRONSCALES detected a Business Email Compromise (BEC) campaign targeting the payroll team at a mid-size enterprise. The attack used three separate domains, each serving a distinct function in the kill chain, and routed everything through Mailjet, a legitimate Email Service Provider (ESP) with strong deliverability reputation. The FBI IC3 2024 Annual Report recorded $2.9 billion in BEC losses last year. Payroll diversion is one of the fastest-growing subcategories, and this case shows why the tactic keeps working.
The CEO Who Never Sent It
The display name matched the organization's CEO. The recipient, a payroll distribution group, had no reason to question it. The message was brief, professional, and referenced an upcoming payroll cycle. It asked the team to process a bank account update and confirmed availability for follow-up.
But the envelope told a different story. The From address was contact@mycomparateur[.]fr, a French domain with no connection to the target organization. The Reply-To pointed to mail@exceeo[.]com, a completely separate domain positioned to capture any responses. And the CEO's identity was borrowed from the organization's own domain, visible only in the display name field.
Three domains. Three roles. The sending domain (mycomparateur[.]fr) handled delivery and authentication. The reply domain (exceeo[.]com) intercepted responses. The impersonated domain (the organization's own) provided the credibility. This separation is deliberate. It prevents simple "does the From domain match the display name domain" rules from catching the mismatch, because the display name is freeform text with no authentication binding.
Mailjet, Tracking, and the Trust Problem
The message was routed through Mailjet infrastructure, confirmed by the tracking pixel domain xrv3t[.]mjt[.]lu in the email headers. Mailjet handles SPF and DKIM signing for its customers, which means messages sent through the platform pass authentication checks for the sending domain. SPF for mycomparateur[.]fr? Pass. DKIM signed by Mailjet's keys? Valid.
The attacker also leveraged Mailjet's List-ID header, indicating the message was sent through a list or campaign function rather than a single transactional send. This is operationally significant. It means the attacker likely had a Mailjet account configured with a mailing list, allowing batch targeting of multiple payroll group members in a single campaign. The Verizon 2024 Data Breach Investigations Report found that 68% of breaches involved a human element, with pretexting (the social engineering technique behind CEO impersonation) doubling since 2022.
The tracking domain xrv3t[.]mjt[.]lu also reveals that the attacker had open and click tracking enabled. Every interaction with the email, from opening it to clicking any embedded element, would be reported back to the Mailjet dashboard. This is reconnaissance built into the delivery infrastructure.
See Your Risk: Calculate how many threats your SEG is missing
Why Authentication Passed and Detection Still Happened
Here is the core problem. SPF, DKIM, and DMARC are designed to verify that the sending infrastructure is authorized to send on behalf of a domain. They verified that Mailjet was authorized to send for mycomparateur[.]fr. They said nothing about whether the person using that infrastructure was the CEO of the target organization.
This is the gap that every ESP-routed BEC exploits. The sending domain is legitimate. The authentication is valid. The content is the weapon, and content analysis requires behavioral context that protocol-level checks do not provide. The Microsoft Digital Defense Report 2024 reports that BEC attacks increasingly use legitimate cloud infrastructure to avoid reputation-based detection, with ESP abuse growing 38% year over year.
Themis, the IRONSCALES Adaptive AI, caught what the protocols could not. The detection was driven by the mismatch between the display name identity (a known executive) and the actual sending infrastructure (a French domain routed through Mailjet). Combined with the anomalous Reply-To domain and the fact that this sender had never previously communicated with the payroll group, the behavioral signals were clear. The message was quarantined before anyone on the payroll team could respond.
According to the IBM Cost of a Data Breach 2024 report, BEC-initiated breaches carry an average cost of $4.88 million. Payroll-targeted variants are particularly dangerous because the financial impact is immediate and the attack can repeat across pay cycles before discovery.
MITRE ATT&CK Mapping
This campaign maps to several MITRE ATT&CK techniques:
- T1566.001 (Phishing: Spearphishing Link): Email-based social engineering targeting a specific organizational function.
- T1534 (Internal Spearphishing): Leveraged knowledge of the CEO's identity and the payroll group's existence to craft a convincing pretext.
- T1036.005 (Masquerading: Match Legitimate Name or Location): Display name spoofing to match a known executive.
Indicators of Compromise
| Type | Indicator | Context |
|---|---|---|
| Sender Email | contact@mycomparateur[.]fr | Sending domain (authenticated via Mailjet) |
| Reply-To Email | mail@exceeo[.]com | Attacker-controlled reply capture |
| Tracking Domain | xrv3t[.]mjt[.]lu | Mailjet open/click tracking |
| Display Name | CEO name (organization's executive) | Identity impersonation |
| Target | Payroll distribution group | Organizational function targeted |
| Header | List-ID present | Campaign/list-based send via ESP |
The Payroll Team Cannot Be the Last Line of Defense
Payroll teams process requests from executives every week. Asking them to verify every email against header data is not realistic. The CISA phishing guidance recommends out-of-band verification for all financial change requests, but that only works when employees recognize the request as suspicious in the first place. When the display name says "CEO" and the message is professionally written, suspicion is the first casualty.
Organizations need behavioral detection that evaluates the relationship between who the email claims to be from, who actually sent it, and whether that communication pattern has ever occurred before. Protocol authentication answers a narrow question: is this infrastructure authorized? Behavioral analysis answers the question that matters: is this person who they claim to be? Without that layer, the next payroll cycle is one reply away from fraud.
Related attacks
| Attack | What happened |
|---|---|
| The CEO's Name, a Legitimate Email Service, and a Bank Account Request That Passed Every Filter | A BEC attack impersonated a company CEO using a legitimate ESP for clean authentication, then routed replies to a freshly registered external domain. |
| Past Due Invoice, Future Wire Fraud: How a BEC Campaign Passed Every Authentication Check | A BEC invoice diversion attack impersonated a known vendor contact through SendGrid, passed SPF/DKIM/DMARC. |
| One Missing Letter, One Stolen Payment: A Reply-To Typosquat That Beat the Spam Score | A typosquatted Reply-To domain misspelled 'Missouri' as 'Missuori' to intercept invoice payments. |
| Every Authentication Check Passed. There Was Nothing to Scan. The Attack Was the Reply. | A fully authenticated email with no links, no attachments, and no malicious content asked recipients to reply all. |
| The Reply-To Was One Letter Off: How a Typosquat Domain Turned a Gmail BEC Into a Payment Diversion | A Gmail-authenticated BEC used a typosquat Reply-To domain and a hidden HTML mailto mismatch to impersonate a steel distributor's credit manager. |
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)