Table of Contents
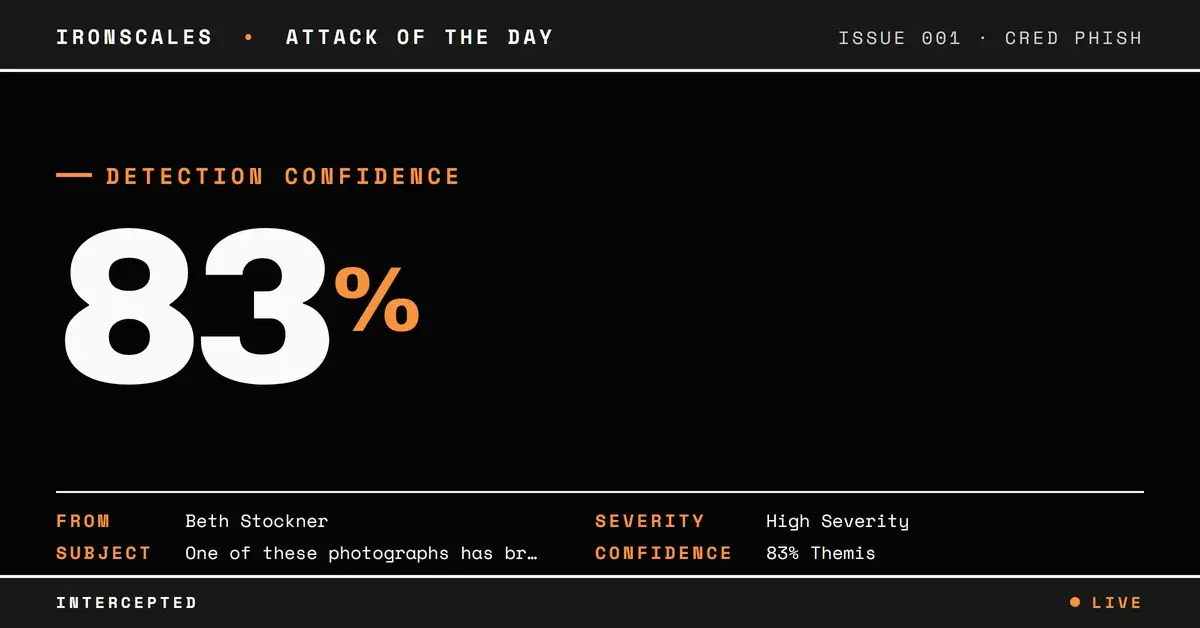
A compromised university account in India sent a phishing email to a school district employee in the United States, impersonating a known contact by exact display name. The payload link pointed to a domain registered that same day. By the time automated link investigation attempted to inspect the landing page, the domain had already gone NXDOMAIN, returning no DNS records at all.
Full SPF, DKIM, and DMARC authentication passed. The message was not spoofed in any technical sense. It was sent from a legitimate Microsoft 365 tenant that the attacker had compromised, using infrastructure that was fully authorized to send on behalf of the university domain.
One mailbox was quarantined after automated and community detection flagged the incident.
A Familiar Name From an Unfamiliar Address
The email arrived from sukhbir_s@ch[.]iitr[.]ac[.]in, an address belonging to the chemical engineering department of a major Indian technical university. The display name, however, read "Beth Stockner," a name the recipient's organization had seen before from an entirely different address at a Taiwanese university (m365[.]fju[.]edu[.]tw). This is exact display-name impersonation: the attacker set the From header's friendly name to match a known contact while using a compromised account that has no relationship to that person.
The message body was brief and conversational: "One of these photographs has brought back bittersweet memories to me," followed by a single HTTP link. The signoff was a joke, "If at first you don't succeed, then skydiving isn't for you," designed to lower suspicion with casual humor. No urgency, no credential request, no invoice. Just a link.
See Your Risk: Calculate how many threats your SEG is missing
The Domain That Existed for Hours
The link pointed to hxxp://yujmt[.]eacftwlh[.]com/AdoFoQB_. WHOIS records show the parent domain eacftwlh[.]com was registered on the same day the email was sent, through Namecheap, with privacy protection enabled. The subdomain "yujmt" and the path token "AdoFoQB_" are randomized strings consistent with disposable phishing infrastructure, where each target or campaign gets a unique, short-lived URL.
When automated link investigation attempted to resolve the domain, it returned NXDOMAIN. The domain had already been deprovisioned or had never been fully provisioned with DNS records by the time the scan ran. No SSL certificate was observed. No page content could be retrieved. The automated risk score was 0.85 (high), and the recommendation was BLOCK, but the verdict was based on behavioral indicators rather than page content because there was no page to inspect.
This is the operational challenge of ephemeral phishing domains. The malicious page may be live for a window measured in hours, long enough to capture credentials from anyone who clicks within the first few minutes, but gone before time-of-click scanners or retrospective URL analysis can evaluate it. Same-day registration, privacy-protected WHOIS, randomized subdomains, and rapid deprovisioning are the fingerprints of this technique.
Authentication Passed Because the Infrastructure Was Real
The message transited Microsoft's outbound protection infrastructure from the Indian university's M365 tenant. The sending IP (2a01:111:f403:c409::2) resolved to mail-southindiaazlp170110002[.]outbound[.]protection[.]outlook[.]com. SPF passed because the university's SPF record authorizes Microsoft's outbound IPs. DKIM passed because the message was signed by the iitracin[.]onmicrosoft[.]com selector. DMARC passed with p=QUARANTINE policy.
None of these checks can distinguish between a legitimate user and an attacker who has taken over that user's account. Authentication verifies that the mail originated from the claimed sending infrastructure. It does not verify that the person behind the keyboard is authorized to use that account. When the compromise is at the account level rather than the infrastructure level, authentication becomes a trust signal that actively works in the attacker's favor.
IRONSCALES Adaptive AI flagged the message at 83% confidence based on behavioral signals, specifically the display-name impersonation pattern: the system recognized "Beth Stockner" from a different address and flagged the mismatch. Community intelligence reinforced the classification based on resolutions of similar incidents across the network. The mailbox was quarantined by automated threat detection.
MITRE ATT&CK Alignment
| Technique | ID | Application |
|---|---|---|
| Phishing: Spearphishing Link | T1566.002 | Conversational lure with single embedded link to ephemeral domain |
| Compromise Accounts: Email Accounts | T1586.002 | University M365 account compromised to send authenticated phishing |
| Acquire Infrastructure: Domains | T1583.001 | Same-day domain registration with privacy protection for phishing payload |
IOC Summary Table
| Type | Indicator | Context |
|---|---|---|
| Sending Email | sukhbir_s@ch[.]iitr[.]ac[.]in | Compromised university M365 account |
| Display Name | Beth Stockner | Exact display-name impersonation of known contact |
| Payload Domain | eacftwlh[.]com | Registered same day, Namecheap, WHOIS privacy, went NXDOMAIN |
| Payload URL | hxxp://yujmt[.]eacftwlh[.]com/AdoFoQB_ | Ephemeral phishing link, no content retrievable |
| Sending IP | 2a01:111:f403:c409::2 | Microsoft outbound protection (South India region) |
| DKIM Domain | iitracin[.]onmicrosoft[.]com | Legitimate DKIM signature from compromised tenant |
| SPF Result | Pass | University SPF authorizes Microsoft IPs |
| DMARC Result | Pass (p=QUARANTINE) | Alignment intact because compromise is at account level |
What Ephemeral Domains Demand From Detection
This attack pairs two techniques that individually are common but together create a compounding detection gap. Account compromise delivers authentication that satisfies every policy check. Ephemeral domain registration defeats retrospective URL analysis by removing the evidence before it can be examined.
Treat display-name mismatches as a first-class signal. When the friendly name matches a known contact but the underlying address does not, that discrepancy should generate an alert regardless of authentication results. Display-name impersonation is a behavioral signal that authentication cannot detect and that humans routinely miss.
Do not rely solely on time-of-click scanning for link protection. Ephemeral domains that resolve for hours and then vanish will produce clean or inconclusive results from scanners that evaluate links after delivery. Detection models need to evaluate domain age, registration patterns, and URL structure at time of delivery, not just page content at time of click.
Monitor for compromised .edu accounts as high-risk senders. University tenants are frequent targets for account compromise because they maintain large user populations with variable security practices. An email from a .edu domain that passes all authentication checks but carries an unrelated display name and a link to a same-day domain should receive elevated scrutiny.
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)