Table of Contents
Microsoft's composite authentication engine returned compauth=pass with reason code 109 for an email carrying a malicious link. The sending domain had been registered less than a year earlier, published no DMARC record, and hosted a link flagged as malicious by threat intelligence feeds. None of that mattered. SPF passed. DKIM passed. Microsoft filled the DMARC gap with bestguesspass, assigned SCL=1, and delivered the message to three mailboxes at a regional telecommunications provider.
This is the structural flaw that authentication alone cannot fix. When a domain publishes SPF and DKIM but omits DMARC, receiving servers have no rejection policy to enforce. Microsoft's fallback logic treats the absence of a policy as implicit permission, and the email sails through.
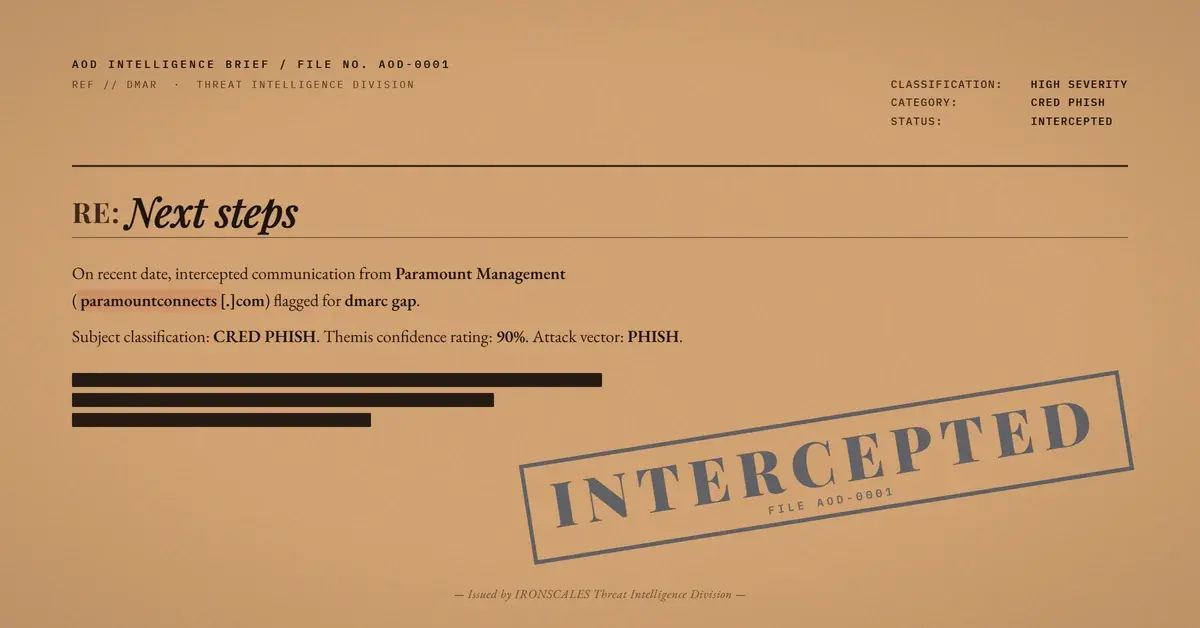
The Vendor Onboarding Pretext
The email arrived with the subject line "Next steps" from a display name of "Paramount Management." The body was two sentences: a claim that insurance documentation had been submitted per the recipient organization's specifications, followed by a request for remaining requirements to begin onboarding technicians for upcoming fieldwork.
The message targeted a group mailbox and a named employee at the recipient organization. A second sender address was CC'd on the same domain. The signature block included a title (President), a company name (Paramount Management Worldwide), a phone number, an email address, and the domain URL. The recipient organization's external email warning banner rendered at the bottom of the message, confirming the email originated from outside the organization's tenant.
Everything about the email's construction was designed to look like routine B2B correspondence. No urgency language. No payment demands. No credential forms. Just a short, professional message with a malicious domain embedded in the signature.
Infrastructure: Fresh Domain, Full Auth, Zero Policy
The attacker domain paramountconnects[.]com was registered on 2025-05-28 through Network Solutions, with HostGator nameservers. WHOIS records contained no registrant name, organization, or contact information beyond a generic domain.operations@web[.]com administrative address. DNSSEC was unsigned.
Despite the domain's opacity, its email authentication was properly configured:
- SPF:
v=spf1 ip4:50.6.160.62 a mx include:websitewelcome.com ~all(pass) - DKIM: Signed via Google Workspace (
header.d=paramountconnects-com.20251104.gappssmtp.com), signature verified - DMARC: No record published. Microsoft applied
bestguesspass action=none - CompAuth:
pass reason=109(implicit authentication, no DMARC)
The reason code 109 in Microsoft's compauth result specifically indicates that the message passed composite authentication without an explicit DMARC policy. This is distinct from reason codes like 100 (explicit DMARC pass) or 000 (explicit fail). It means the domain's authentication was inferred, not declared.
The mail path confirms the attacker used Google Workspace as the sending platform. The message originated from mail-yx1-xb144.google.com (IPv6: 2607:f8b0:4864:20::b144), transited through Google's SMTP infrastructure, and entered Microsoft 365's Exchange Online Protection (EOP) at DS3PEPF000099DB.mail.protection.outlook.com. ARC seals from both Google (i=1) and Microsoft (i=2) passed validation.
This configuration represents a low-cost, high-reliability attack infrastructure. Google Workspace accounts cost nothing to create for small organizations. Once configured with valid SPF and DKIM, the sending domain inherits Google's mail delivery reputation. The missing DMARC record is the deliberate gap: it prevents the receiving server from ever rejecting the message based on policy, while SPF and DKIM pass results push the email past content-agnostic authentication filters.
See Your Risk: Calculate how many threats your SEG is missing
Why Authentication-Only Filters Miss This Pattern
The 2024 Verizon Data Breach Investigations Report found that phishing remains the top initial access vector in confirmed breaches. The FBI IC3 2024 Internet Crime Report documented $2.77 billion in business email compromise (BEC) losses. These numbers persist because attackers have learned to build infrastructure that satisfies authentication checks.
The problem is not that SPF, DKIM, and DMARC are broken. The problem is that their absence is not treated as a signal. Microsoft's bestguesspass verdict is designed to reduce false positives for legitimate senders who have not yet adopted DMARC. But it also provides a clean delivery path for attacker-controlled domains that intentionally skip DMARC to avoid rejection policies.
According to the Microsoft Digital Defense Report 2024, the volume of phishing attacks intercepted by Microsoft exceeded 700 million per month. A significant portion of these leverage newly registered domains with partial authentication, exactly the pattern observed in this case.
IRONSCALES identified this email at 90% confidence based on behavioral signals that authentication filters ignore: the malicious link verdict on the sender's own domain, the domain's registration age, opaque WHOIS data, and the absence of prior communication history with the recipient organization. These are the signals that close the DMARC enforcement gap where traditional Secure Email Gateways (SEGs) stop evaluating.
Technique Classification
| Technique | ID | Application |
|---|---|---|
| Phishing: Spearphishing Link | T1566.002 | Malicious URL embedded in email signature |
| Acquire Infrastructure: Domains | T1583.001 | paramountconnects[.]com registered 2025-05-28 via Network Solutions |
| Establish Accounts: Email Accounts | T1585.002 | Google Workspace email accounts on attacker domain |
Attacker Infrastructure and IOCs
| Type | Value | Context |
|---|---|---|
| Sending Domain | paramountconnects[.]com | Registered 2025-05-28, Network Solutions, HostGator NS |
| Sender Email | kwanell[.]boston@paramountconnects[.]com | Display name "Paramount Management" |
| CC Email | renzo[.]vasquez@paramountconnects[.]com | Second attacker-controlled address |
| Malicious URL | hxxp://www[.]paramountconnects[.]com | Flagged malicious, embedded in signature |
| Sending IP | 2607:f8b0:4864:20::b144 | Google Workspace (mail-yx1-xb144.google.com) |
| A Record | 50.6.160.66 | HostGator shared hosting |
| SPF Record | v=spf1 ip4:50.6.160.62 a mx include:websitewelcome.com ~all | SoftFail policy (permissive) |
| DKIM Selector | paramountconnects-com.20251104.gappssmtp.com | Google Workspace default signing domain |
| DMARC | None published | Enables bestguesspass fallback |
| Message-ID | CALfaByqScoY4cRrApOujfPvqPL9B1ATaXzXvCfUiPvMPMtai+g@mail[.]gmail[.]com | Google infrastructure origin |
| WHOIS Contact | domain.operations@web[.]com | Generic, no registrant identity |
Closing the BestGuessPass Gap
Organizations relying on authentication results alone to filter inbound email will miss this class of attack. Three immediate actions reduce exposure:
- Treat missing DMARC as a negative signal. Any inbound message from a domain with no published DMARC record should receive elevated scrutiny, regardless of SPF and DKIM results. CISA's phishing guidance recommends DMARC adoption as a baseline control, and its absence from a sending domain is itself an indicator.
- Layer behavioral analysis over authentication. Domain age, WHOIS opacity, first-time sender status, and link reputation are signals that exist outside the authentication framework. The IBM Cost of a Data Breach 2024 report found that organizations using AI-driven security tools reduced breach costs by an average of $2.2 million. Behavioral detection platforms like IRONSCALES evaluate these signals in real time, catching what authentication-only filters pass.
- Audit your own DMARC posture. If your organization has not published a DMARC record with
p=rejectorp=quarantine, you are giving attackers the same structural advantage on your domain. Monitor, enforce, and close the gap from both sides.
The email in this case contained two sentences and a signature block. It carried no attachments, no urgency, no payment demand. It passed SPF. It passed DKIM. Microsoft called it compauth=pass. And it delivered a malicious link to three mailboxes. Authentication is necessary. It is not sufficient.
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)