Table of Contents
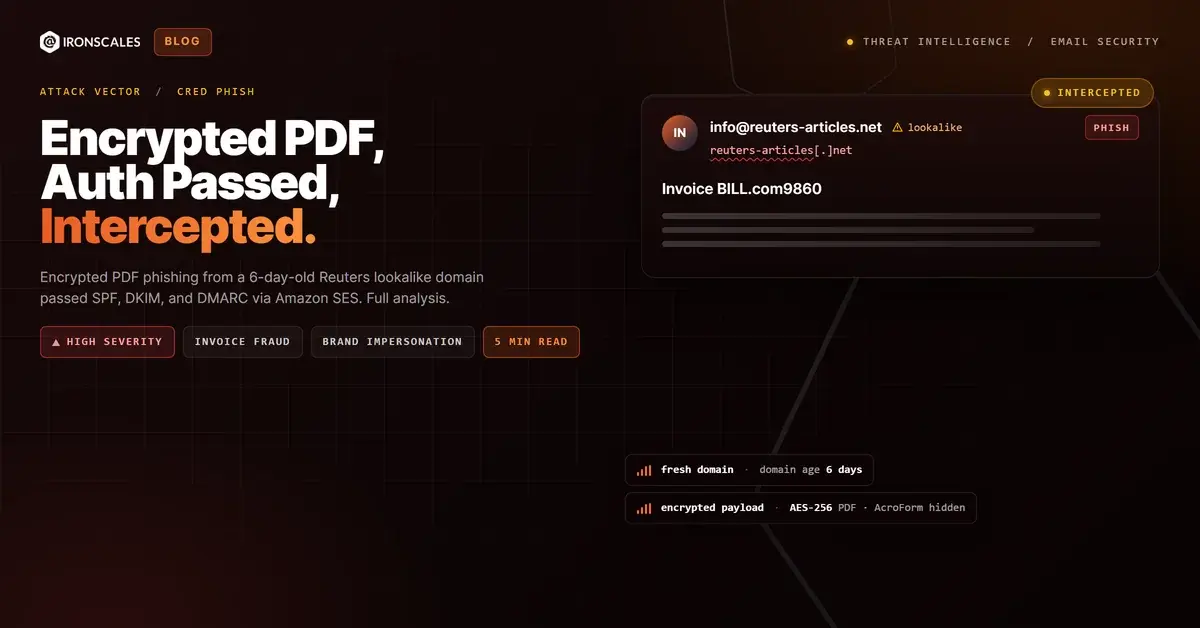
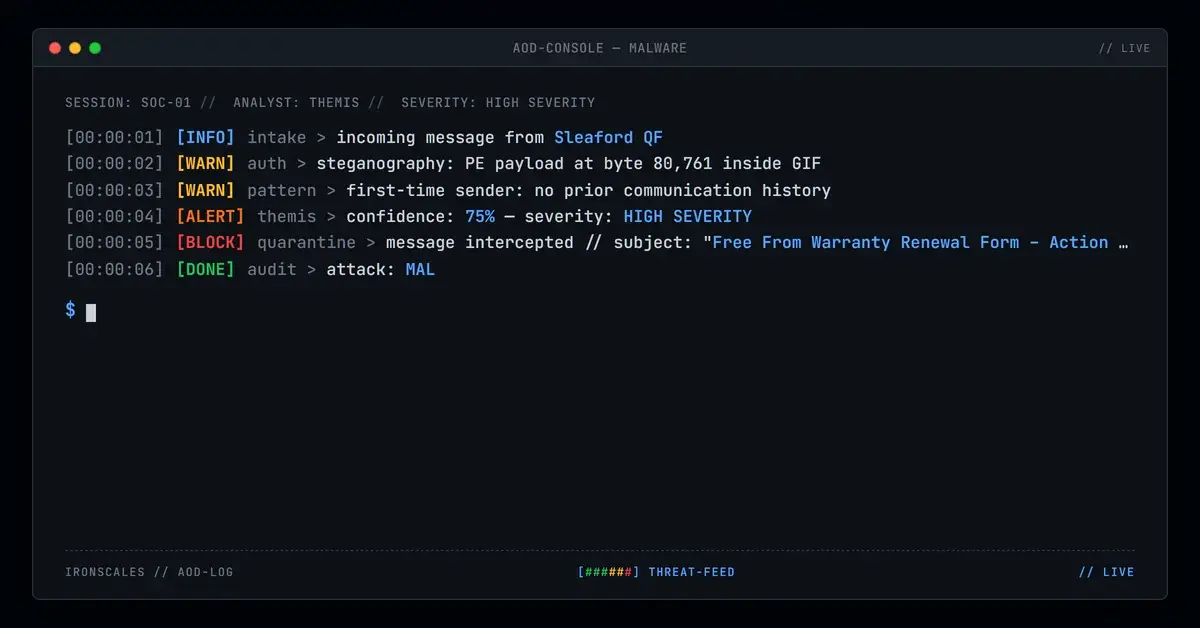
A password-protected PDF named BILL.com9860.pdf landed in the inbox of an employee at a metals manufacturing firm on April 9, 2026. The email passed SPF, DKIM, and DMARC. The sending domain, reuters-articles[.]net, had existed for exactly six days. Inside the PDF: AES-256 encryption and hidden AcroForm fields that no automated scanner could read. This is what modern invoice phishing looks like when the attacker understands email authentication better than most defenders do.
The attack targeted a specific individual at the organization, arriving through Amazon SES infrastructure that gave it the same delivery characteristics as legitimate transactional email. Without adaptive AI analysis correlating domain age, attachment behavior, and community threat intelligence, this email would have sat in the recipient's inbox looking perfectly routine.
Six Days From Registration to Weaponization
The timeline tells the story. On April 3, 2026, someone registered reuters-articles[.]net through NameSilo with full WHOIS privacy via PrivacyGuardian. Within hours, the domain was configured behind Cloudflare nameservers (lilith.ns.cloudflare.com and randall.ns.cloudflare.com), SPF records were published to authorize Amazon SES, and DKIM keys were generated. By April 9, the domain was sending authenticated phishing.
That six-day window is deliberate. It is long enough to avoid some newly registered domain (NRD) blocklists that only flag domains under 24 or 48 hours old, but short enough that the domain has zero sending reputation or history for security tools to evaluate. According to the FBI IC3 2024 Annual Report, business email compromise and invoice fraud accounted for over $2.9 billion in adjusted losses. Attacks like this one are a significant contributor.
The brand choice matters too. "Reuters" carries implicit trust in professional contexts. A domain like reuters-articles[.]net is close enough to pass a quick visual check, especially when the recipient is focused on the invoice attachment rather than scrutinizing the sender address.
How the Payload Evades Every Scanner in the Chain
The attachment, BILL.com9860.pdf (SHA-256: 42a0d8a715adb636abe114fe15bdab11f0705d3ca0052484b949e44bf2312c4c), uses AES-V2 encryption with the Standard security handler. This is the critical evasion mechanism. When a security gateway or sandbox attempts to analyze the PDF, it encounters a password wall. Text extraction fails. JavaScript analysis fails. URL extraction fails. The scanner sees an encrypted blob and, in many configurations, passes it through.
But the PDF is not just encrypted for secrecy. Static analysis confirmed the presence of /AcroForm and /Encrypt objects in the file structure. AcroForm fields are interactive form elements (T1566.001) that can collect text input, trigger JavaScript, or embed clickable URLs. Because the file is encrypted, none of these interactive elements can be inspected without the password.
This is a calculated move mapped to MITRE ATT&CK T1036.005 (Masquerading: Match Legitimate Name or Location). The filename BILL.com9860.pdf mimics the naming convention of Bill.com, a widely used accounts payable platform. A recipient in finance or operations sees a filename that looks like a legitimate invoice export and instinctively opens it.
The email body itself was crafted to reinforce legitimacy. It contained a Portuguese-language legal discussion thread referencing municipal tax law (ISSQN), construction contract negotiations, and specific legislative citations from leis[.]org. The two embedded links both pointed to legitimate Brazilian municipal legislation pages and scanned clean. This is content padding, a technique where attackers surround the malicious payload with genuine, contextually appropriate content to reduce suspicion and improve delivery rates.
See Your Risk: Calculate how many threats your SEG is missing
Infrastructure Built to Authenticate, Not to Last
The relay analysis reveals a clean, professional delivery chain. The email originated from a7-37.smtp-out.eu-west-1.amazonses.com (IP: 54[.]240[.]7[.]37), traversed Microsoft Exchange Online Protection, and landed in the recipient's M365 mailbox. Every authentication check passed:
| Check | Result | Detail |
|---|---|---|
| SPF | Pass | 54[.]240[.]7[.]37 authorized for mail.reuters-articles[.]net |
| DKIM | Pass | Valid signatures for both reuters-articles[.]net and amazonses[.]com |
| DMARC | Pass | action=none for header.from=reuters-articles[.]net |
| SCL | 1 | Microsoft assigned minimal spam confidence |
Microsoft's own antispam engine scored this email at SCL 1, the lowest non-zero spam confidence level. The Forefront report categorized it as CAT:NONE. For organizations relying solely on native M365 security, this email was indistinguishable from legitimate business correspondence.
| IOC | Type | Context |
|---|---|---|
reuters-articles[.]net | Domain | Sender domain, registered 2026-04-03 |
info@reuters-articles[.]net | Sender address | |
54[.]240[.]7[.]37 | IP | Amazon SES EU-West-1 relay |
mail[.]reuters-articles[.]net | Domain | SPF envelope sender |
29d1d46435a72cd73c172eda35bab8f6 | MD5 | BILL.com9860.pdf |
42a0d8a715adb636abe114fe15bdab11f0705d3ca0052484b949e44bf2312c4c | SHA-256 | BILL.com9860.pdf |
NameSilo / PrivacyGuardian | Registrar | WHOIS privacy enabled |
lilith.ns.cloudflare[.]com | Nameserver | Domain DNS |
randall.ns.cloudflare[.]com | Nameserver | Domain DNS |
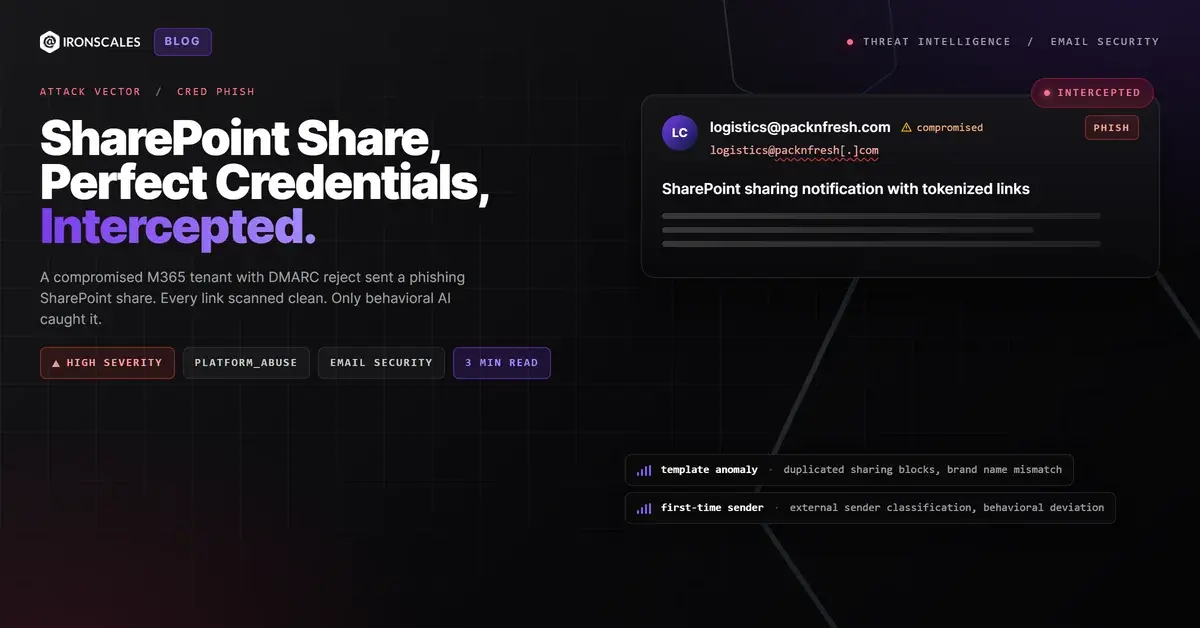
Why Authentication Alone Is a False Floor
This attack is a textbook demonstration of why DMARC, SPF, and DKIM are necessary but insufficient. The attacker did not spoof an existing domain. They built their own, configured it properly, and sent authenticated email through a reputable cloud provider. Every protocol worked exactly as designed. The email was still phishing.
The Verizon 2024 Data Breach Investigations Report found that phishing remains a top initial access vector, with the median time to click a phishing link measured at under 60 seconds. Encrypted attachments add another layer of difficulty: even security-aware users may assume a password-protected PDF is a privacy measure rather than an evasion technique.
For defenders, the actionable takeaways are specific:
- Block or quarantine encrypted attachments by default. If your email gateway cannot inspect the contents, it should not deliver the file without additional review. Password-protected PDFs with no prior sender relationship are high-risk.
- Flag newly registered domains aggressively. A domain registered within the past 30 days sending invoice-themed email with attachments should trigger immediate quarantine, regardless of authentication results.
- Deploy behavioral AI that correlates signals beyond authentication. Domain age, attachment encryption, sender history, and community intelligence patterns are the signals that caught this attack. Authentication alone gave it a clean bill of health.
- Treat Amazon SES, SendGrid, and Mailgun as neutral infrastructure. Cloud email providers are tools. Attackers use them too. A "pass" from SES means the sender configured their account correctly, nothing more.
The CISA phishing guidance emphasizes that technical controls must be layered with user awareness and AI-driven analysis. This case proves why. The email authenticated. The links were clean. The body was contextually appropriate. The only anomalies were the domain age, the encrypted attachment, and the behavioral pattern, exactly the signals that adaptive AI and community intelligence are built to catch.
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)