Table of Contents
SPF passed. DKIM passed (twice, for both canva.com and amazonses.com). DMARC passed. Composite authentication: pass, reason 100. Every protocol designed to verify sender identity confirmed this email was legitimate.
It was. Canva sent it. Through Amazon SES, from IP 54.240.76.85, signed with valid cryptographic keys. The Return-Path matched. The DKIM body hash matched. There was no spoofing, no forgery, no header manipulation.
The email was also phishing.
An attacker created a Canva account, built a malicious design, and clicked "Share." Canva's own platform infrastructure handled the rest: the email template, the sending servers, the tracking redirects, the authentication signatures. The recipient at a regional accounting firm received a perfectly formatted share notification with a single purple button: "Open in Canva." One click away from whatever credential harvesting page the attacker had staged inside a Canva design.
When the Attacker's Infrastructure IS the Platform
The traditional phishing model requires attacker-owned infrastructure: a spoofed domain, a lookalike login page, a compromised relay. Each of those components creates a signal that security tools can evaluate. SaaS platform abuse inverts that model entirely.
In this case, the attacker needed nothing beyond a free Canva account. The MITRE ATT&CK framework classifies this as T1583 (Acquire Infrastructure), but "acquire" is doing a lot of work here. The attacker didn't buy a domain, rent a server, or configure an MX record. They signed up for a design tool that 190 million people use.
The share notification that arrived at the accounting firm was indistinguishable from a legitimate one because it was a legitimate one. Same HTML template. Same Canva branding. Same Australian business address (110 Kippax St, NSW 2010) and ABN in the footer. Same tracking pixel at trail.canva.com. Even Canva's own safety warning appeared in the body: "Do you know this person? This Canva invite is from someone you may not know. Be alert for scams and report if suspicious."
The platform tried to warn the recipient. The authentication layer told them everything was fine.
The Redirect Chain That Scanners Called Clean
Every link in the email routed through Canva's click-tracking domain before resolving to canva.com:
`` hxxps://trail[.]canva[.]com/CL0/hxxps:/www[.]canva[.]com/design/DAG3Lwj7Yzs/share?accessToken=[token]&invite=[token] ``
This is standard behavior for Canva share notifications. The trail.canva.com redirect exists for Canva's own analytics. Automated link scanners evaluated the chain and returned a clean verdict. They weren't wrong. The redirect resolved to canva.com. The design page loaded behind a Cloudflare verification challenge ("Verify you are human"), which itself is a legitimate anti-bot mechanism that also happens to prevent automated security scanners from evaluating the content behind it.
This is Spearphishing Link (T1566.002) at its most effective: the link IS the legitimate platform. There is no attacker domain to block, no IP to blacklist, no certificate to flag. According to the Verizon 2024 Data Breach Investigations Report, phishing remains the dominant initial access vector for data breaches. Campaigns like this one explain why: when the delivery infrastructure is indistinguishable from legitimate business communication, volume-based and reputation-based defenses have nothing to work with.
Five Months, Four Quarantines, One Design ID
The original incident hit the accounting firm in late October 2025. IRONSCALES auto-resolved it as phishing and quarantined the message. Then it came back.
March 11, 2026: quarantined. March 18: quarantined. April 1: quarantined. April 9: quarantined again.
Same design ID (DAG3Lwj7Yzs). Same share notification template. Same subject line. Different mailboxes each time. The attacker didn't rotate the lure because they didn't need to. Each new target was a first-time recipient who had never seen the design before.
See Your Risk: Calculate how many threats your SEG is missing
This persistence pattern reveals a fundamental gap in point-in-time email evaluation. A gateway that clears a message on arrival based on authentication results has no mechanism to correlate that same campaign resurfacing weeks later across different recipients. According to the Microsoft Digital Defense Report 2024, attackers increasingly exploit this gap by running low-volume, long-duration campaigns that stay below velocity-based detection thresholds.
Microsoft's own systems flagged one signal in this case: SFTY:9.25 in the X-Forefront-Antispam-Report header, a safety code indicating potential phishing despite valid authentication. But the email still reached the inbox. The flag was advisory, not blocking.
The Behavioral Signals Authentication Cannot See
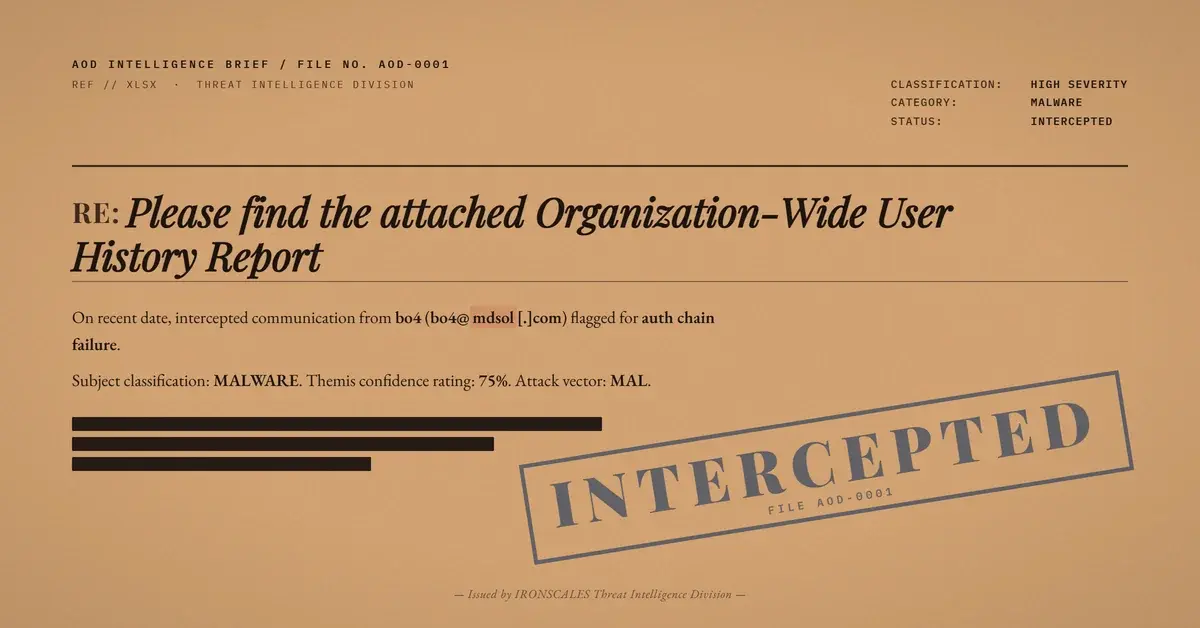
Themis, the IRONSCALES Adaptive AI, classified this as a vendor scam at 68% confidence on the first encounter. That classification held across every subsequent quarantine event.
The signals that drove that classification had nothing to do with SPF, DKIM, or DMARC. They were behavioral: first-time sender to the organization, a collaboration tool share notification arriving without any prior business relationship, a CTA directing the recipient to content that couldn't be pre-evaluated, and cross-mailbox correlation showing the same campaign targeting multiple recipients. The IRONSCALES community of 35,000+ security professionals contributed additional signal through crowdsourced threat intelligence, strengthening classification as the campaign spread.
None of these signals exist in email headers. All of them require understanding context, not just cryptographic verification.
What This Means for Your SaaS Allow-List
If your email security policy auto-allows messages from canva.com, google.com, dropbox.com, or docusign.com based on domain reputation or authentication results, you have a bypass. CISA has flagged legitimate cloud service abuse as a growing vector specifically because these platforms clear every reputation and authentication check by default.
The FBI IC3 2024 Internet Crime Report documented over $2.9 billion in BEC losses. An increasing share of those attacks begin with exactly this technique: legitimate platform infrastructure delivering the initial lure.
Three things worth evaluating in your environment:
Audit your SaaS sender allow-lists. Any rule that permits all mail from a major SaaS platform's sending domain creates a blind spot. Canva, Google, Dropbox, DocuSign, and SharePoint are all actively abused for credential harvesting delivery.
Evaluate whether your link scanner follows redirect chains past Cloudflare challenges. In this case, the Canva design page sat behind a Cloudflare "Verify you are human" interstitial. Scanners that stop at the challenge page never see the payload.
Correlate across mailboxes and time. A single Canva share notification is ambiguous. The same design ID hitting four different recipients over five months is a campaign. Per-message evaluation misses that pattern entirely.
Authentication-based defenses answered exactly the question they were designed to answer: did canva.com send this email? Yes. The question they can't answer is whether the person who triggered that send created a design with malicious intent. That requires a different kind of analysis altogether.
---
Indicators of Compromise
| Type | Indicator | Context |
|---|---|---|
| Sender | no-reply@canva[.]com | Legitimate Canva sending address (platform-native) |
| Sending IP | 54[.]240[.]76[.]85 | Amazon SES (legitimate Canva infrastructure) |
| Tracking domain | trail[.]canva[.]com | Canva click-tracking redirect |
| Design URL | hxxps://www[.]canva[.]com/design/DAG3Lwj7Yzs/share | Attacker-created Canva design (phishing lure) |
| Design ID | DAG3Lwj7Yzs | Persistent across 5-month campaign |
| Subject | A design has been shared with you! | Standard Canva share template |
| DKIM domains | canva[.]com, amazonses[.]com | Both signatures valid |
| Microsoft safety flag | SFTY:9.25 | Phishing pattern match despite valid auth |
| Message ID pattern | @email.amazonses[.]com | Amazon SES message identifier |
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)