Table of Contents
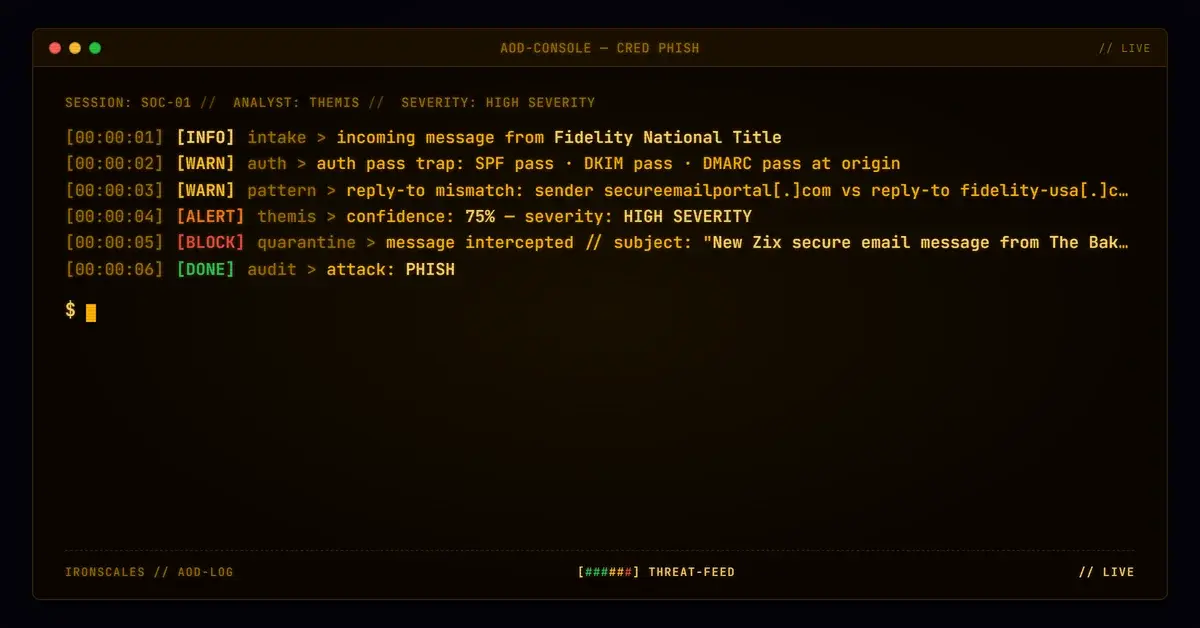
The sender address looked like a Zix secure portal notification from Fidelity National Title. That part was real. What wasn't real was that the subdomain fidelityusa.secureemailportal.com had anything to do with Fidelity National Title at all.
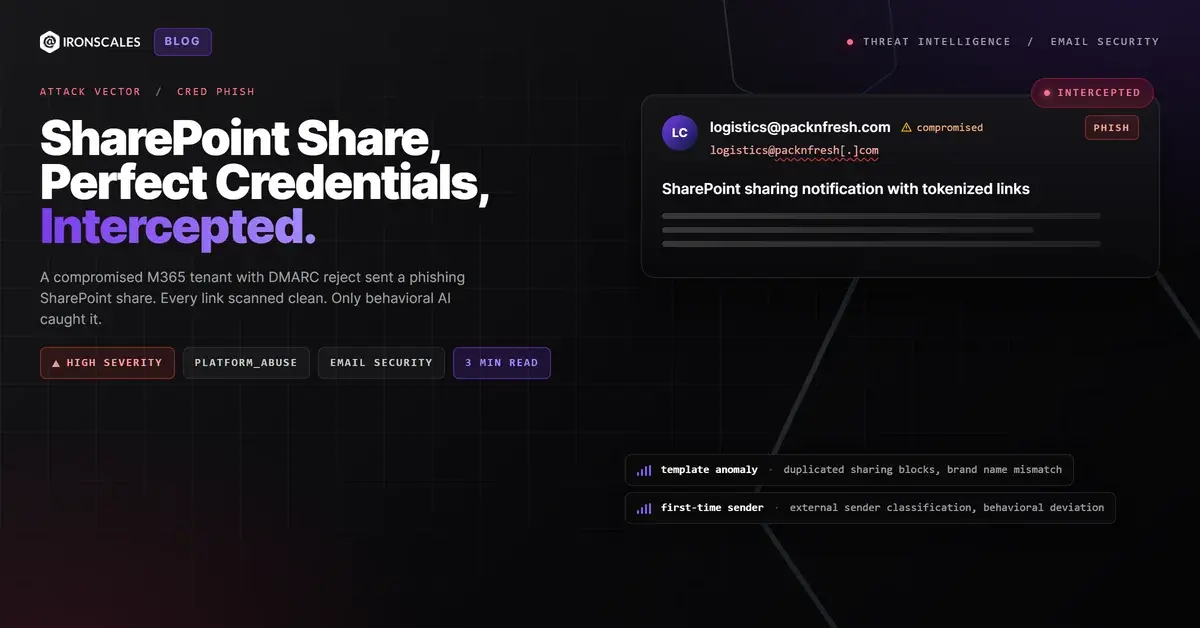
Attackers provisioned a subdomain under Zix's legitimate secure email portal infrastructure, named it after a major financial brand, and used the resulting address to target a community bank's business banking portal. The message passed DKIM, SPF, and DMARC at origin. Every automated filter in the chain called it clean.
This is what brand-fusion phishing looks like when it's done by someone who understands how email authentication actually works.
How You Build a Convincing Lie Out of Two Real Names
The attacker's first move was strategic. Rather than registering a throwaway lookalike domain that would age-check as days old and fail reputation filters, they used an established platform's subdomain provisioning to operate under secureemailportal.com.
That domain was registered in 2017 and runs on Zix nameservers (NS01.ZIXCORP.COM through NS03.ZIXCORP.COM). It carries enterprise-grade reputation. DKIM signing, SPF authorization, and DMARC enforcement are all handled by Zix infrastructure. When an attacker provisions a subdomain under that platform, they inherit all of it.
The subdomain label they chose was fidelityusa. Combined with the parent domain, the full sender address became:
fidelityusa-notification@fidelityusa[.]secureemailportal[.]com
To anyone reading that address, it signals: a Fidelity entity, using a Zix secure portal, sending a legitimate notification. Two trusted brands, fused into one address. Neither name alone is a red flag. The combination implies an institutional relationship that does not exist.
The target was a business banking portal inbox at a community bank. Not a random employee, not a generic info@ address. A BusinessOnline inbox handles wire transfer notifications, ACH confirmations, and account management messages. Attackers picked this target because the credential value is high.
The Attack Chain, Step by Step
The relay chain is where the technical sophistication becomes clear.
The message originated from mail3239.smtp25.com, routing into Zix's outbound infrastructure at out.zixmt1.zixworks.com, through mx1.zp.prod.zixcorp.com, and out via smtpout.zixmail.net. That exit point is secureemailportal.com at IP 199.30.236.16.
At that hop, the authentication record is clean. SPF passes. DKIM passes with a verified body signature. DMARC passes with action none. Microsoft's composite authentication score (compauth) marks it as pass reason=100.
The message then hit a Votiro content sanitization relay at 44.206.213.130 (an Amazon EC2 host, ec2-44-206-213-130.compute-1.amazonaws.com). Votiro performs content inspection and reconstruction, which modifies the message body. That modification invalidated the DKIM body hash. By the time the message reached Microsoft's inbound protection layer, the authentication picture had changed: SPF softfail, DKIM body-hash failure, DMARC fail.
But Microsoft had already seen the earlier passing authentication headers. The message was marked as previously validated and delivered.
The full delivery path:
- Attacker sends via
mail3239.smtp25.com - Routes through Zix enterprise relay chain
- Exits
secureemailportal.com(199.30.236.16) with full auth pass - Passes through Votiro sanitization relay (44.206.213.130), which breaks DKIM body hash
- Arrives at Microsoft inbound protection nodes
- Delivered to target inbox
MITRE ATT&CK mappings: T1566.002 (Spearphishing Link) for the primary delivery mechanism, T1036.005 (Masquerading: Match Legitimate Name or Location) for the subdomain brand fusion technique.
What the Email Said, and What It Was Trying to Do
The email body was minimal by design. A Zix secure-message template, gray header bar, a single "Open Message" button in a styled table cell.
The header read: "New Zix secure email message from The Baker Firm - Fidelity National Title."
The CTA linked to hxxps://fidelityusa[.]secureemailportal[.]com/s/e?m=ABAqJQldBKKwN6vp16AKCIBp.
An expiration notice added pressure: "The secure message expires on Apr 17, 2026 @ 04:09 PM (GMT)." Two weeks, not two hours. That pacing is deliberate. It reduces urgency that might prompt a call to verify, while still creating a deadline that pushes toward action.
There was no personalization. No recipient name, no account number, no transaction detail. That absence is a signal, because legitimate Zix secure-message notifications from financial institutions typically include some identifying context. This was a generic lure, sent at scale.
Four mailboxes at the target organization received the message.
See how many phishing emails are getting through your filters.
The Signal That Gave It Away
The Reply-To header pointed somewhere else entirely.
While the sender was fidelityusa-notification@fidelityusa[.]secureemailportal[.]com, the Reply-To was ecook@fidelity-usa[.]com. Different domain. Different registrar. Different nameservers.
fidelity-usa.com was registered in 2011 via Bluehost on iPowerWeb nameservers. Not Zix infrastructure. Not Fidelity National Title infrastructure. And it was quietly updated on February 24, 2026, roughly five weeks before this campaign ran.
That update is the tell. Someone refreshed a dormant domain to prepare it for operational use. The result is a two-domain attacker setup: the Zix subdomain handles inbound trust and authentication, and fidelity-usa[.]com handles reply-to collection, the actual phishing destination control.
Any reply from the recipient, any credential submission that routes through a reply, goes to attacker-controlled infrastructure. The two-domain structure is intentional: one domain for appearing legitimate, one for collecting the harvest.
Themis flagged the mismatch between sender domain and Reply-To domain as a behavioral anomaly. The sender's identity, cross-referenced against IRONSCALES community threat intelligence and authentication header analysis, did not support the claimed institutional relationship. The message was quarantined before any of the four affected mailboxes interacted with the "Open Message" link.
What Security Teams Should Do Differently Here
Static email authentication checks (SPF, DKIM, DMARC) are necessary but insufficient for this attack class. The message passed all three at origin. The threat was not in the authentication. It was in the identity claim.
A few specific controls matter here:
Reply-To domain inspection. If the Reply-To domain does not match the From domain or share the same organizational parent, that's a divergence signal worth flagging. It is not proof of phishing, but it warrants additional scrutiny before delivery.
Subdomain authority verification. The existence of a subdomain under a legitimate platform does not confirm that the subdomain operator has any relationship with the brand names in the subdomain label. fidelityusa.secureemailportal.com says nothing about Fidelity National Title authorizing that subdomain. This requires behavioral or community-intelligence signals, not just DNS or authentication checks.
Business banking inbox hardening. High-value inboxes like business email compromise targets, treasury addresses, and banking portals warrant stricter filtering thresholds than standard employee mailboxes. The expected email profile for a BusinessOnline address is narrow. An unexpected secure-portal notification from a real estate title firm falls outside that profile.
Age-of-relationship signals. The sending domain and the organization had no prior communication history. First-contact messages from unknown senders should carry elevated scrutiny regardless of authentication status, especially when they include a credential-requesting CTA.
The 2024 Verizon DBIR found phishing involved in 68% of financially motivated breaches, and the FBI's 2024 IC3 Report logged over $2.9 billion in BEC losses, with credential harvesting as the primary enabler. The Microsoft Digital Defense Report 2024 specifically flags trusted third-party platform abuse as an accelerating attacker technique, exactly what this case illustrates.
The defensive answer is not better authentication. It is behavioral detection that evaluates identity coherence across sender domain, Reply-To, brand claims, and relationship history, the kind of signal that flagged this message before any recipient clicked.
Indicators of Compromise
| Type | Indicator | Context |
|---|---|---|
| Domain | fidelityusa[.]secureemailportal[.]com | Attacker-provisioned subdomain on Zix infrastructure. Sender and link destination. |
| URL | hxxps://fidelityusa[.]secureemailportal[.]com/s/e?m=ABAqJQldBKKwN6vp16AKCIBp | "Open Message" CTA. Credential harvesting portal entry point. |
| Domain | fidelity-usa[.]com | Reply-To domain. Attacker-controlled. Updated Feb 24, 2026. Bluehost/iPowerWeb nameservers. |
ecook@fidelity-usa[.]com | Reply-To address. Attacker collection infrastructure. | |
fidelityusa-notification@fidelityusa[.]secureemailportal[.]com | Sender address. Zix subdomain, authenticated at origin. | |
| IP | 199[.]30[.]236[.]16 | Zix outbound relay. Origin authentication passed at this hop. |
| IP | 44[.]206[.]213[.]130 | Votiro sanitization relay (EC2). Post-processing DKIM break occurred here. |
| Domain | mail3239[.]smtp25[.]com | Initial sending infrastructure origin. |
---
For deeper context on how spear phishing campaigns exploit trusted third-party infrastructure, see the IRONSCALES threat intelligence blog.
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)