Table of Contents
The most dangerous link in this email was not the one that looked suspicious. It was the bright yellow "REVIEW & SIGN DOCUMENT" button sitting inside a pixel-perfect DocuSign template. Clicking it did not open DocuSign. It opened Google Maps Belgium, which silently redirected to an Amazon S3 bucket hosting a credential harvesting page. The remaining 15 links in the email? All clean. Law firm websites, court Zoom meetings, Google Maps address lookups. Every one of them legitimate, every one of them there for the same reason: to make automated scanners trust the message.
This attack, which targeted an employee at a mid-size technology company in February 2026, combined three techniques that individually might not trigger an alert but together created a near-invisible credential theft pipeline. A trusted redirect proxy (Google), trusted hosting infrastructure (AWS), and a hijacked email thread full of real legal correspondence designed to suppress threat scoring across every layer of defense.
Without adaptive AI analysis that evaluates sender behavior, CTA-destination mismatches, and link chain resolution simultaneously, this email would have reached the inbox looking like routine legal paperwork.
A Button That Goes to Belgium First
The CTA pointed to maps[.]google[.]be/url?q=, with the q parameter set to an Amazon S3 URL. Google Maps regional domains accept redirect parameters, and because the initial URL resolves under google.be, most URL reputation systems score it as safe. The redirect landed on bucket-secure-cdn-cdn-media-static[.]s3[.]us-east-1[.]amazonaws[.]com/about.html, a public S3 bucket hosting a credential harvesting page designed to capture login credentials.
This is an open redirect attack (T1566.002). The technique is not new. What makes this instance notable is the choice of redirect proxy. Google Maps is one of the most universally allowlisted domains in corporate environments. According to the Microsoft Digital Defense Report 2024, adversaries increasingly abuse legitimate cloud services and trusted platforms as intermediary infrastructure to evade URL-based detection. This campaign is a textbook example.
The S3 bucket naming convention is also worth noting. The name bucket-secure-cdn-cdn-media-static is deliberately engineered to look like legitimate CDN infrastructure. For an analyst triaging URLs in bulk, that name blends into the noise of real content delivery infrastructure.
15 Clean Links, 1 Credential Trap
The email body was not a simple DocuSign notification. Below the branded header and CTA button, the attacker embedded an entire forwarded email thread from a real Florida family law case. This thread contained correspondence between attorneys at two law firms ([Law Firm A] and [Law Firm B]), a judicial assistant, and a court-appointed guardian ad litem. The thread included real office addresses, phone numbers, Zoom meeting links for a [Circuit Court], and Constant Contact newsletter signup URLs.
None of these links were malicious. That was the point.
Email security gateways that calculate composite threat scores based on link analysis face a math problem when 15 out of 16 links are clean. The Verizon 2024 Data Breach Investigations Report found that credential theft remains the primary objective in phishing attacks, and the sophistication of delivery mechanisms continues to outpace static detection. Link dilution is one of those mechanisms. By padding the email with legitimate URLs, the attacker drives the malicious-to-benign link ratio below the threshold where many gateways flag the message.
See Your Risk: Calculate how many threats your SEG is missing
Mangled Headers and a Kagoya Mailserver
The From and Return-Path headers in this message were not normal email addresses. They contained embedded AWS SES tracking URLs, Spectrum Business billing paths, and Zoom meeting links, all concatenated into a single string before the @lcivy[.]co[.]jp domain. This kind of header manipulation (T1566.001) serves multiple purposes. It confuses header-parsing logic in security tools, it can inject tracking tokens into email processing pipelines, and it obscures the real sender identity behind a wall of URL fragments.
The email originated from ms542[.]kagoya[.]net (IP 133[.]18[.]69[.]23), a server belonging to Kagoya, a Japanese web hosting provider. The true connecting IP was 23[.]81[.]42[.]158, which submitted the message via authenticated SMTP. SPF passed for the envelope domain lcivy[.]co[.]jp because the Kagoya server is an authorized sender. DKIM was absent entirely. DMARC returned bestguesspass, meaning no published DMARC policy existed for the domain and the receiving server applied heuristic evaluation. According to CISA advisories on email authentication, organizations without enforced DMARC policies remain vulnerable to domain spoofing and abuse.
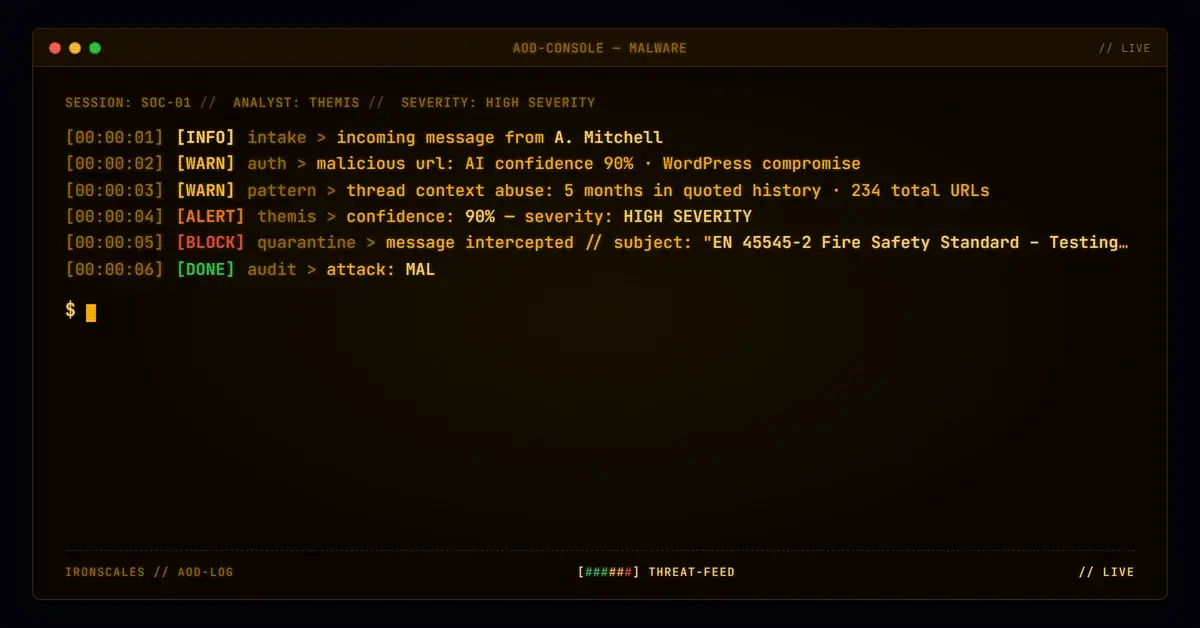
The IRONSCALES community intelligence network had already flagged similar patterns from Kagoya-hosted infrastructure across multiple customer environments, enabling Themis to correlate this sender profile with known phishing behavior before the recipient could interact with the message.
Signal Fingerprint
| Type | Indicator | Context |
|---|---|---|
| URL | hxxps://maps[.]google[.]be/url?q=hxxps%3A%2F%2Fbucket-secure-cdn-cdn-media-static[.]s3[.]us-east-1[.]amazonaws[.]com%2Fabout[.]html | Google Maps redirect to credential harvest |
| URL | hxxps://bucket-secure-cdn-cdn-media-static[.]s3[.]us-east-1[.]amazonaws[.]com/about[.]html | S3-hosted credential harvesting page |
| Domain | lcivy[.]co[.]jp | Sender/envelope domain (Kagoya-hosted) |
| IP | 133[.]18[.]69[.]23 | Kagoya mailserver (ms542[.]kagoya[.]net) |
| IP | 23[.]81[.]42[.]158 | True origin IP (SMTP submission) |
| URL | hxxps://lp[.]constantcontactpages[.]com/su/RWsIoV2/signup | Embedded clean link (medium risk, historical abuse) |
| Header | Malformed From/Return-Path with embedded tracking URLs | Header manipulation indicator |
Why Link Reputation Alone Cannot Solve This
This attack exploited a fundamental limitation in URL-based detection: the assumption that the domain hosting a link reflects its intent. When the initial URL is google.be and the hosting infrastructure is amazonaws.com, both domains carry enormous implicit trust. The IBM Cost of a Data Breach Report 2024 found that stolen credentials remain the most expensive initial attack vector, averaging $4.81 million per breach. Attacks like this one are how those credentials get stolen.
Security teams dealing with open redirect abuse need to evaluate the full redirect chain, not just the initial domain. That means resolving URLs to their final destination before scoring, flagging CTA-destination mismatches (a DocuSign button that resolves to S3 is inherently suspicious), and treating emails with abnormally high clean-to-malicious link ratios as potential dilution attempts. Credential harvesting protection that combines behavioral AI with real-time URL chain resolution catches what static reputation lookups miss.
The attacker in this case got almost everything right: trusted redirect proxy, trusted hosting, authenticated delivery, and a convincing cover story buried in real legal correspondence. The one thing they could not fake was the behavioral pattern that Themis flagged before the recipient ever saw the email.
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)