Table of Contents
What Happened
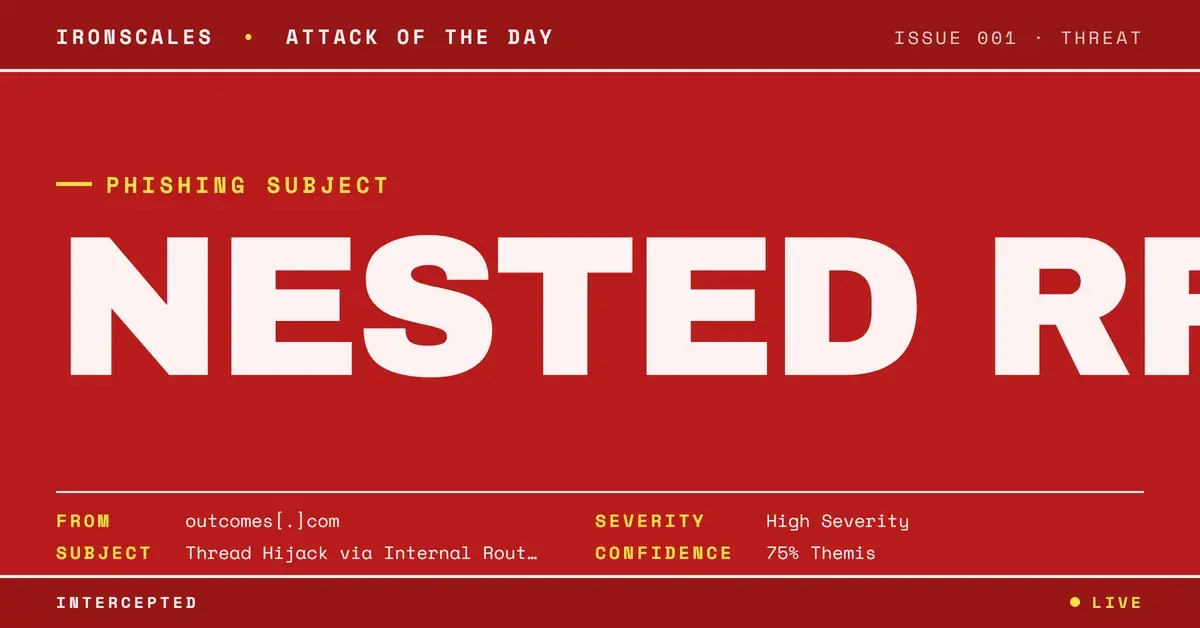
An email arrived from outcomes[.]com, a domain registered in 1995. The message carried a nested RFC822 attachment: a complete email message embedded as a file within the outer email. When automated scanners attempted to inspect the attachment, they could not open it. The nested message format created a processing barrier that prevented content extraction and analysis.
The outer email carried no DKIM signature. The sending domain had no DMARC record published. For a domain that has existed for 30 years, the complete absence of modern email authentication is notable. There was no mechanism to verify that the message was genuinely sent by an authorized user of that domain or that the message content had not been modified in transit.
An EXTERNAL sender warning banner was present on the message, indicating the recipient organization's gateway correctly identified the email as originating from outside the organization. However, the email also contained internal routing headers suggesting it was part of an ongoing internal conversation. This contradiction is a hallmark of thread hijacking: the attacker injects themselves into an existing internal thread by replying from an external address.
All links visible in the message body scanned clean across URL scanners. The malicious content, if present, was contained within the nested RFC822 attachment that scanners could not access.
Why It Matters
Nested RFC822 attachments exploit a structural limitation in email scanning pipelines. Most scanners can inspect common attachment types (PDFs, Office documents, images, HTML files) and can follow links to evaluate landing pages. But a message/rfc822 content type contains a complete MIME message with its own header set, body, and potential sub-attachments. Parsing these correctly requires recursive MIME processing, and many gateway scanners either skip them entirely or fail silently.
The absent DKIM and DMARC records mean that any authentication-based filtering is impossible. The domain cannot be validated, the message cannot be integrity-checked, and no policy can be enforced. The 30-year domain age provides enough reputation to avoid age-based blocklisting, creating a scenario where the message carries maximum historical trust with zero verifiable authentication.
The thread hijack signal (EXTERNAL banner plus internal routing) is particularly dangerous because it exploits context trust. Recipients who see a message that appears to continue an internal conversation are far more likely to engage with it, especially if the original thread was a legitimate business discussion.
How IRONSCALES Caught It
Community intelligence across the IRONSCALES network identified the pattern: nested RFC822 attachments from outcomes[.]com reaching multiple unrelated organizations with similar thread-hijack characteristics. While each individual email appeared benign to automated scanners, the cross-tenant distribution pattern was anomalous.
Adaptive AI email security evaluated the combination of missing authentication, unopenable attachment, and EXTERNAL/internal routing contradiction as a high-confidence threat signal, escalating the message before the recipient engaged with the nested content.
See Your Risk. Run a free phishing simulation to find out whether nested attachment attacks would bypass your current scanning pipeline.
Indicators of Compromise
| Indicator | Type | Value |
|---|---|---|
| Case ID | Internal | 0b60a9412a51d9fff23f84affa9bf330 |
| Sender Domain | Domain | outcomes[.]com |
| Domain Created | WHOIS | 1995 |
| Attachment Type | MIME | message/rfc822 (nested) |
| Scanner Result | Detection | Attachment could not be opened |
| DKIM | Authentication | none |
| DMARC | Authentication | none |
| EXTERNAL Banner | Header | Present with internal routing headers |
| Link Verdicts | Detection | All clean |
MITRE ATT&CK Mapping
| Tactic | Technique | ID | Notes |
|---|---|---|---|
| Initial Access | Phishing: Spearphishing Attachment | T1566.001 | Nested RFC822 email-within-email |
| Defense Evasion | Obfuscated Files or Information | T1027 | Nested MIME structure blocks scanner inspection |
| Defense Evasion | Masquerading | T1036 | Thread hijack with internal routing context |
| Collection | Email Collection | T1114 | Thread interception to insert malicious content |
Related attacks
| Attack | What happened |
|---|---|
| The Spreadsheet That Arrived Twice: CR/LF Filename Obfuscation and a Base64 Shadow Payload | A clinical data report arrived as a .xlsx with CR/LF control characters in the filename and a companion .b64 base64 payload. |
| The PDF That Passed Every Scan Without Being Read | A PDF attachment with CR/LF control characters injected into its filename caused automated file analyzers to return a clean verdict on a zero-byte... |
| Sign Here, Get Phished: Inside an Adobe Sign Lure With a Multi-Hop Redirect to Credential Theft | An Adobe Sign e-signature lure routed recipients through a multi-hop redirect chain ending at fameklinik[.]com. |
| When SPF, DKIM, and DMARC All Pass. And the Email Is Still Phishing | A fully authenticated phishing email (SPF pass, DKIM pass, DMARC pass) used a legitimate nonprofit platform to deliver credential-harvesting links with... |
| The Azure Alert That Billed You $459: When Microsoft's Own Infrastructure Delivers the Phish | A phishing campaign used Azure's own notification system to send fraudulent billing alerts from Microsoft's authenticated infrastructure. |
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)