Table of Contents
What Happened
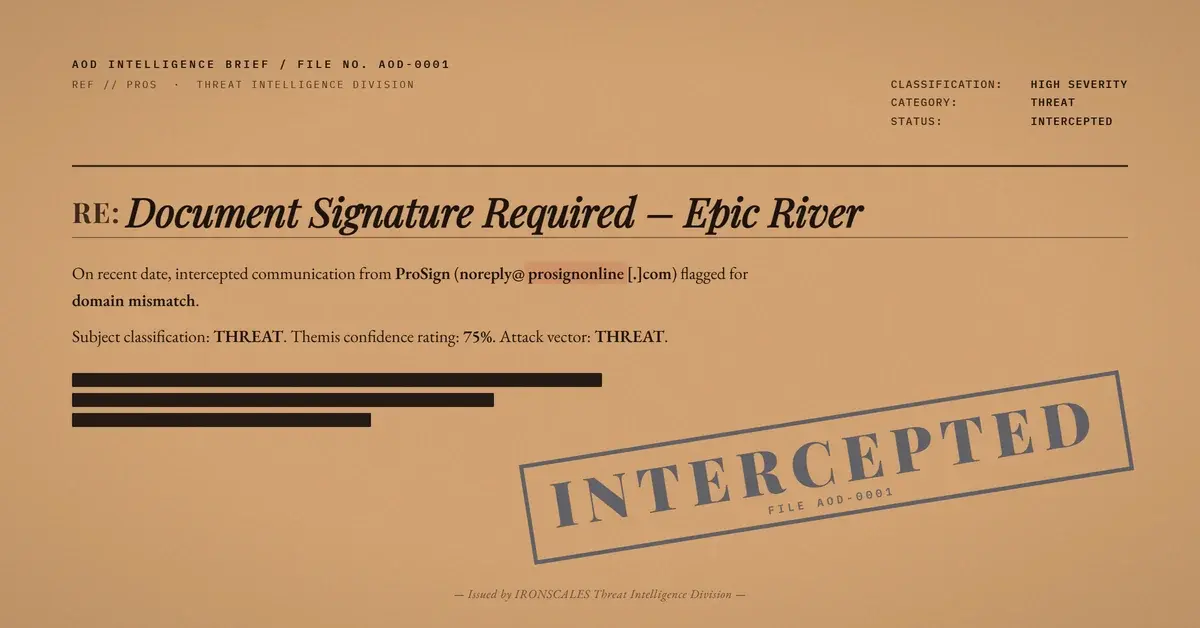
An email presented as an e-signature notification arrived from prosignonline[.]com, a domain registered in 2017 and hosted on AWS infrastructure. The message wove together three brand identities: Epic River appeared as the document originator, Home State Bank as the financial institution involved in the transaction, and ProSign as the electronic signing platform facilitating the process.
DKIM passed. DMARC passed. SPF returned a softfail because the message was relayed through mxthunder[.]net at 208[.]53[.]48[.]218, an IP not included in the prosignonline[.]com SPF record. The softfail disposition meant most gateways treated the message as suspicious but deliverable rather than rejecting it outright.
The call-to-action directed recipients to prosign[.]online, a separate domain from the sender address. URL scanners returned mixed verdicts: some flagged it as suspicious, others marked it clean. The page was designed to harvest credentials under the guise of a document signing login.
Why It Matters
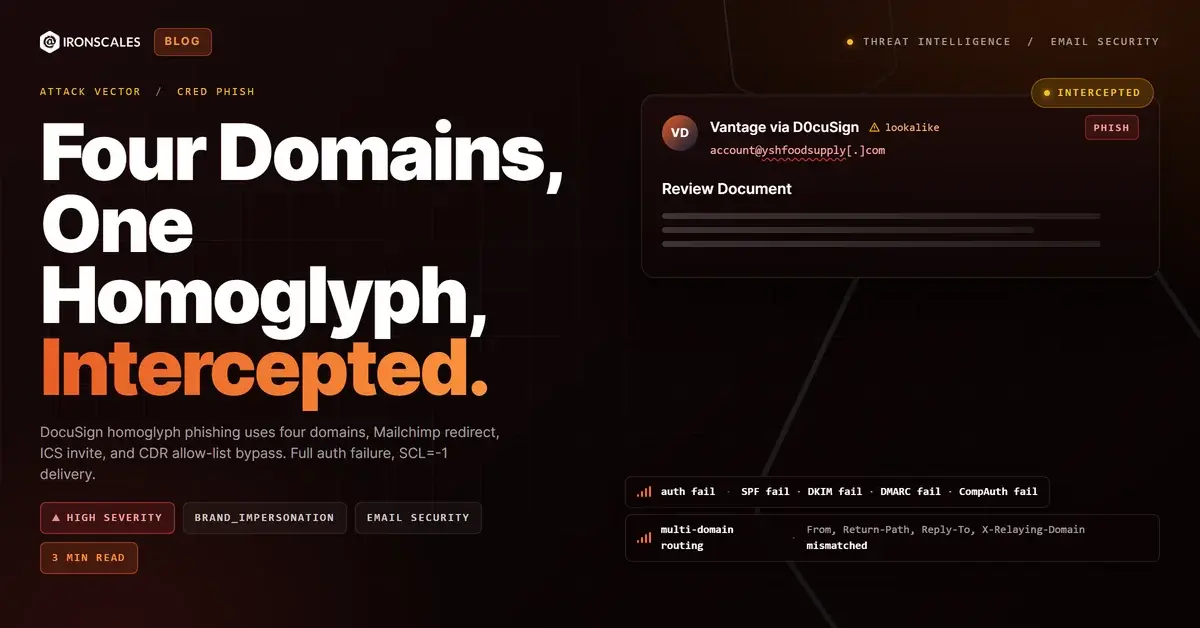
Multi-brand phishing represents an evolution in social engineering sophistication. Rather than impersonating a single entity, the attacker constructed a plausible multi-party transaction scenario. In legitimate business, e-signature workflows routinely involve a document sender (Epic River), a financial counterparty (Home State Bank), and a signing platform (ProSign). A recipient who recognizes even one of these brands may extend trust to the entire chain.
The SPF softfail is a deliberate choice. Attackers who route through relays like mxthunder[.]net accept the softfail because they know most gateway configurations will still deliver the message. The DKIM and DMARC passes provide enough authentication cover to offset the SPF result in most scoring algorithms.
The mixed scanner verdicts on prosign[.]online highlight a persistent gap in URL-based detection. When a phishing page is hosted on AWS and the domain is relatively new without negative reputation history, scanners that rely on infrastructure reputation and feed-based blocklists will return clean results. Only scanners performing real-time content analysis of the landing page would identify the credential harvest form.
How IRONSCALES Caught It
Adaptive AI email security evaluated the full behavioral context of the message: a multi-brand e-signature notification, SPF softfail through a third-party relay, and a CTA pointing to a domain different from the sender domain. Community intelligence confirmed the pattern across multiple organizations, with the prosign[.]online domain appearing in credential harvest reports from other tenants.
The sender-to-link domain mismatch (prosignonline[.]com sending, prosign[.]online harvesting) is a signal that static gateway rules frequently miss because both domains share the prosign brand name, making the discrepancy appear intentional rather than suspicious.
See Your Risk. Run a free phishing simulation to test whether multi-brand credential harvesting emails bypass your current defenses.
Indicators of Compromise
| Indicator | Type | Value |
|---|---|---|
| Case ID | Internal | b7f13fe9f763896e8a98c49be8c213f7 |
| Sender Domain | Domain | prosignonline[.]com |
| Harvest Domain | Domain | prosign[.]online |
| Relay Service | Infrastructure | mxthunder[.]net |
| Relay IP | IP Address | 208[.]53[.]48[.]218 |
| Hosting | Infrastructure | AWS |
| Domain Created | WHOIS | 2017 |
| SPF | Authentication | softfail |
| DKIM | Authentication | pass |
| DMARC | Authentication | pass |
| Scanner Verdicts | Detection | Mixed (clean/suspicious) |
MITRE ATT&CK Mapping
| Tactic | Technique | ID | Notes |
|---|---|---|---|
| Initial Access | Phishing: Spearphishing Link | T1566.002 | CTA link to credential harvest page |
| Credential Access | Input Capture: Web Portal Capture | T1056.003 | Fake e-signature login page |
| Defense Evasion | Masquerading | T1036 | Three legitimate brands chained for trust |
| Resource Development | Acquire Infrastructure: Domains | T1583.001 | prosign[.]online registered for harvesting |
Related attacks
| Attack | What happened |
|---|---|
| The B2B Content Marketing Email That Borrowed a Brand, a Relay Allow-List, and a Security Vendor's Own URL Wrapper | A polished B2B research report offer used SelectHub branding, passed through an allow-listed mail relay at SCL -1. |
| The HubSpot Account Suspension That Came From Flodesk | An account suspension email claimed to be from the HubSpot Team but was sent from a personal domain via Amazon SES. |
| The Law Firm Document That Linked to a Cleaning Company | A fully authenticated email from a UAE law firm domain delivered a document-signing lure where the CTA button linked to a US cleaning company's subdomain. |
| The Email That Passed Every Security Check (Because Adobe Sent It) | A phishing campaign targeting school district staff used Adobe's own sending infrastructure, real DKIM signatures. |
| The Password Reset That Came From an Auth0 Dev Tenant | A password reset email from a manufacturing company passed every authentication check and linked to real Auth0 infrastructure. |
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)