Table of Contents
What Happened
A SharePoint sharing notification arrived from a U.S. municipal government domain registered in 2004. The email was structurally identical to every legitimate SharePoint sharing notification: standard Microsoft formatting, proper sender headers, and tokenized links containing sdata and xsdata parameters unique to the share event.
SPF passed. DKIM passed. DMARC passed. ARC passed. The sending infrastructure was Microsoft SharePoint Online operating under the government tenant. There was no spoofing, no relay abuse, and no authentication failure of any kind. The email was genuinely sent from the government SharePoint tenant because an attacker had compromised an account within that tenant.
The tokenized links scanned clean across all URL scanners that evaluated them. The sdata and xsdata parameters contain encrypted session data that varies per recipient, making each URL unique and preventing signature-based detection. The links led to a credential harvest page designed to capture Microsoft 365 login credentials.
Why It Matters
Government domain compromise represents one of the highest-trust attack vectors available. A .gov domain carries implicit authority across every reputation system, threat intelligence feed, and email security gateway. When combined with SharePoint Online as the sending platform (a Microsoft first-party service), the authentication profile is essentially perfect.
The tokenized link structure adds another layer of evasion. Unlike static phishing URLs that can be blocklisted after first detection, SharePoint sharing links with sdata and xsdata parameters are cryptographically unique per recipient. Each URL that reaches a scanner is a URL that scanner has never seen before and will never see again. Feed-based and signature-based detection cannot keep pace with this approach.
This attack exploits a fundamental assumption in email security architecture: that authentication equals legitimacy. When the compromised account belongs to a government entity, that assumption is reinforced by every layer of the security stack.
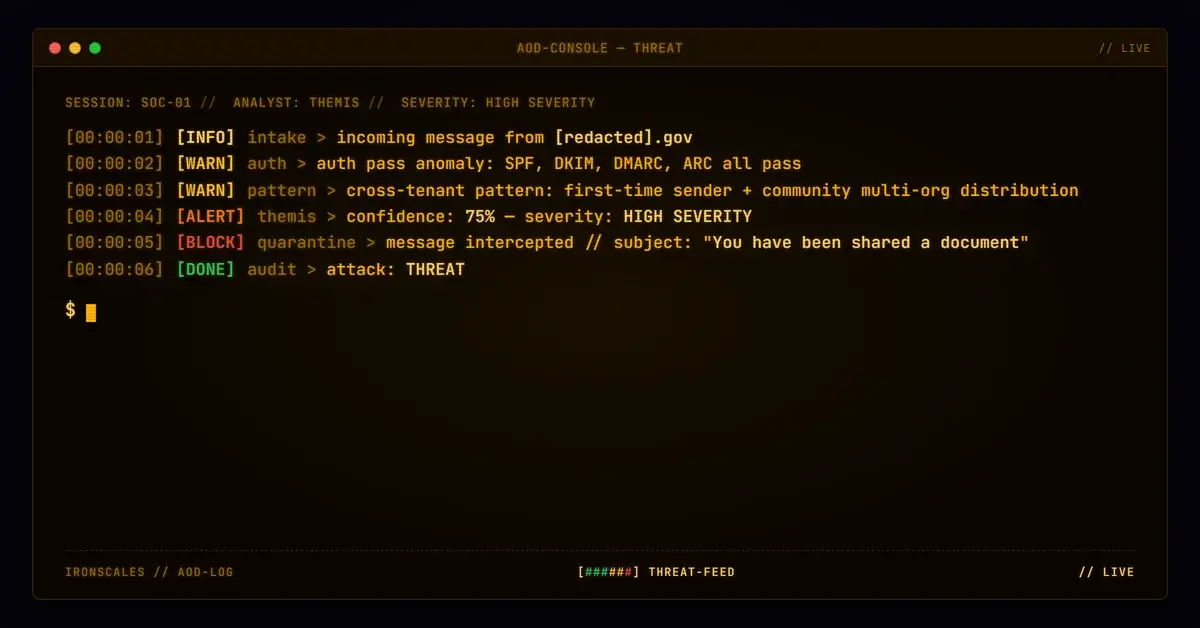
How IRONSCALES Caught It
Community intelligence across the IRONSCALES network identified a pattern of SharePoint sharing notifications from this government tenant reaching multiple unrelated organizations. While each individual email and URL appeared legitimate, the cross-tenant distribution pattern was anomalous for a municipal government SharePoint account.
Adaptive AI email security correlated the first-time sender signal (a government SharePoint account that had never previously shared documents with the target organization) with the cross-tenant community intelligence to escalate the risk assessment. The combination of behavioral analysis and community-sourced threat data caught what every authentication protocol and URL scanner missed.
See Your Risk. Run a free phishing simulation to discover whether compromised-tenant phishing emails would reach your users.
Indicators of Compromise
| Indicator | Type | Value |
|---|---|---|
| Case ID | Internal | 7827864d409bee7fc0c705d271b8a9df |
| Sender Domain | Domain | [redacted].gov |
| Domain Created | WHOIS | 2004 |
| Platform | Infrastructure | SharePoint Online |
| Link Parameters | URL | sdata, xsdata (tokenized) |
| SPF | Authentication | pass |
| DKIM | Authentication | pass |
| DMARC | Authentication | pass |
| ARC | Authentication | pass |
| URL Scanner Verdicts | Detection | Clean |
MITRE ATT&CK Mapping
| Tactic | Technique | ID | Notes |
|---|---|---|---|
| Initial Access | Phishing: Spearphishing Link | T1566.002 | Tokenized SharePoint sharing links |
| Resource Development | Compromise Accounts: Email Accounts | T1586.002 | Government employee account compromised |
| Credential Access | Input Capture: Web Portal Capture | T1056.003 | Microsoft 365 credential harvest page |
| Defense Evasion | Trusted Relationship | T1199 | .gov domain inherits maximum trust score |
Related attacks
| Attack | What happened |
|---|---|
| The Password Reset That Came From an Auth0 Dev Tenant | A password reset email from a manufacturing company passed every authentication check and linked to real Auth0 infrastructure. |
| Best of the Worst: Five Attacks That Looked Broken (and Worked) | The other story in inbox phishing this month: kits that shipped broken and got delivered anyway. |
| The Webinar Invite That Came With an Apple Wallet Pass and a Three-Hop Redirect Chain | A Google Calendar invite for a fake AI webinar passed full authentication and carried an .ics file, an Apple Wallet .pkpass. |
| E-Sign Credential Harvest Chains Three Brands: Epic River, Home State Bank, and ProSign | A credential harvesting campaign chained three legitimate brands into a single e-signature phishing flow. |
| Single Malicious SafeLinks-Wrapped URL Hidden Among Legitimate SharePoint Trust Anchors | One malicious SafeLinks-wrapped URL hid among legitimate SharePoint links in a professional event-coordination thread. |
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)