Table of Contents
What Happened
A payment notification arrived claiming to be from the Taulia supplier portal, a legitimate supply chain finance platform used by enterprise organizations to manage supplier payments. The email was sent from suppliermail.dfamilk[.]com via Amazon SES and passed SPF, DKIM, and DMARC authentication without any failures.
The notification referenced a payment for DFA (Dairy Farmers of America) with a redacted payment amount. Every link in the email body pointed to real Taulia subdomains. The formatting matched legitimate Taulia payment notifications closely enough to pass visual inspection.
Two anomalies revealed the impersonation. First, the footer address listed 95 3rd St, while the real Taulia corporate address is 795 Folsom. Second, the email contained duplicated template blocks where sections of the notification were repeated, a common artifact of copy-paste template construction rather than programmatic template rendering.
Why It Matters
Supplier portal impersonation targets the payment workflow directly. When a finance team receives what appears to be a legitimate payment notification from a platform they already use, the natural response is to click through and process the payment. The attacker does not need to convince the recipient that a new vendor exists or that an unusual payment is justified. They simply need to replicate an existing, expected communication.
The use of real Taulia subdomains for all embedded links makes URL-based detection ineffective. Every link in the email resolves to a legitimate Taulia domain. Scanners that evaluate link destinations find no malicious infrastructure. The fraud is embedded in the context of the notification itself, not in the payload.
Amazon SES as the sending infrastructure provides full authentication coverage. The attacker configured SPF and DKIM correctly for the dfamilk[.]com subdomain, and DMARC alignment passed. From an email authentication perspective, this email is indistinguishable from a legitimate automated notification.
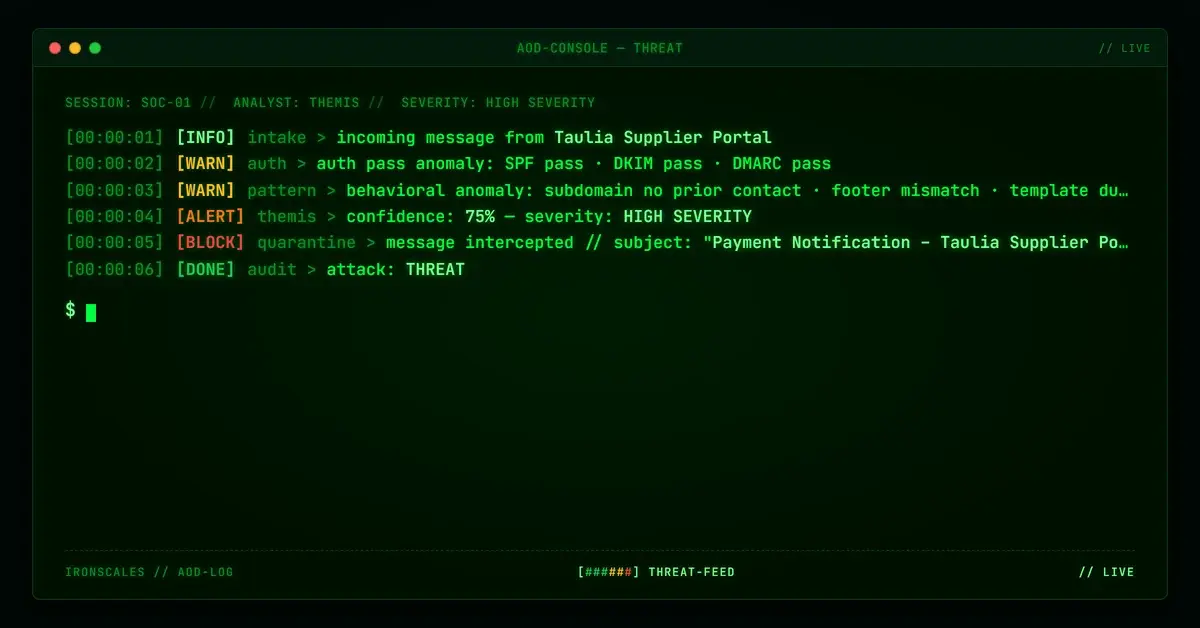
How IRONSCALES Caught It
Adaptive AI email security identified the behavioral anomaly: a supplier portal notification arriving from a subdomain (suppliermail.dfamilk[.]com) that had no established communication pattern with the target organization. The footer address mismatch and duplicated template blocks provided additional confidence signals that the template was constructed rather than generated by the real Taulia platform.
Community intelligence across the IRONSCALES network confirmed that multiple organizations received similar Taulia impersonation notifications from the same sending infrastructure, establishing the campaign pattern.
See Your Risk. Run a free phishing simulation to test whether supplier portal impersonation emails would reach your finance team.
Indicators of Compromise
| Indicator | Type | Value |
|---|---|---|
| Case ID | Internal | ccfdc47c3cf23e49fff1b6d021fad3ba |
| Sender Domain | Domain | suppliermail.dfamilk[.]com |
| Impersonated Platform | Brand | Taulia |
| Payment Entity | Organization | DFA |
| ESP | Infrastructure | Amazon SES |
| Footer Address (Fake) | Template Anomaly | 95 3rd St |
| Footer Address (Real) | Reference | 795 Folsom |
| Template Anomaly | Indicator | Duplicated template blocks |
| SPF | Authentication | pass |
| DKIM | Authentication | pass |
| DMARC | Authentication | pass |
MITRE ATT&CK Mapping
| Tactic | Technique | ID | Notes |
|---|---|---|---|
| Initial Access | Phishing: Spearphishing Link | T1566.002 | Payment notification with portal links |
| Defense Evasion | Masquerading | T1036 | Taulia supplier portal template impersonation |
| Defense Evasion | Trusted Relationship | T1199 | All links to legitimate Taulia subdomains |
| Impact | Financial Theft | T1657 | Payment diversion through supplier portal workflow |
Related attacks
| Attack | What happened |
|---|---|
| When the Sender Domain Is Also the Phishing Kit Host: Dual-Purpose Domain Compromise | An attacker compromised a legitimate manufacturing company domain and used it two ways at once: as the authenticated sending address and as the host for... |
| The B2B Content Marketing Email That Borrowed a Brand, a Relay Allow-List, and a Security Vendor's Own URL Wrapper | A polished B2B research report offer used SelectHub branding, passed through an allow-listed mail relay at SCL -1. |
| Every Authentication Check Passed. There Was Nothing to Scan. The Attack Was the Reply. | A fully authenticated email with no links, no attachments, and no malicious content asked recipients to reply all. |
| The Email That Passed Every Security Check (Because Adobe Sent It) | A phishing campaign targeting school district staff used Adobe's own sending infrastructure, real DKIM signatures. |
| Best of the Worst: Five Attacks That Already Knew Your Name | Five phishing attacks we published this week shared a single uncomfortable quality: precision. |
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)