Table of Contents
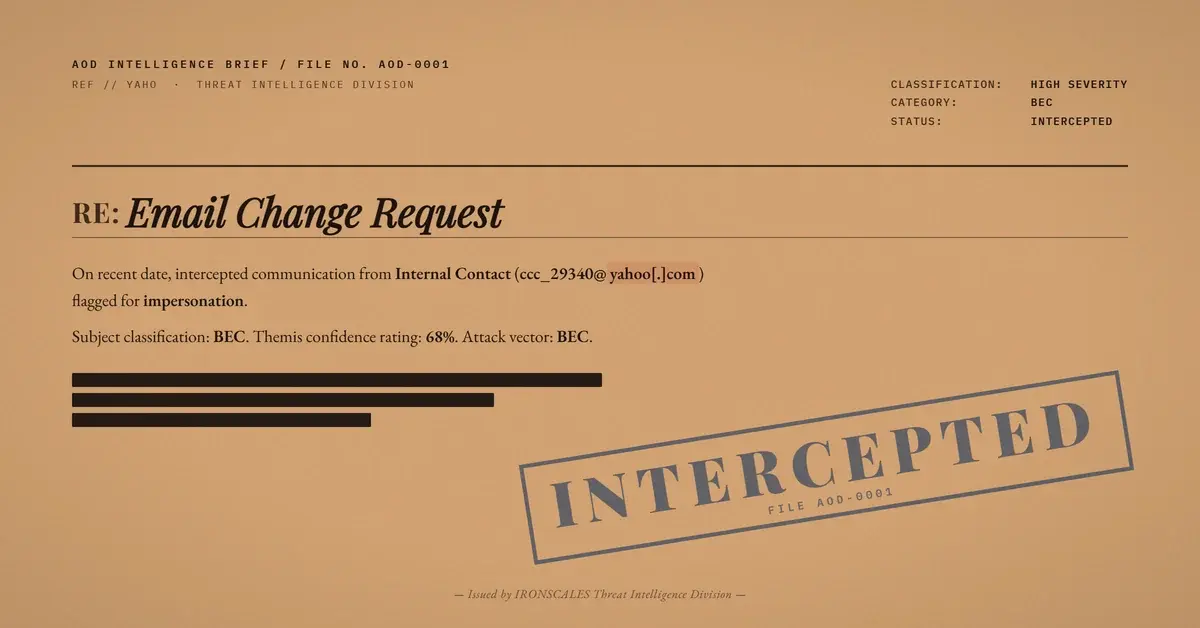
The email had no links. No attachments. No embedded images. Just a short message with the subject line "Email Change Request," sent from a Yahoo free-mail account to an employee at a state government health agency.
Every authentication check passed. SPF, DKIM, DMARC, compauth=100. Yahoo's infrastructure is legitimate, and the attacker used it exactly as designed. The only weapon was a display name.
The Name Was Right, the Address Was Wrong
The display name matched a known internal contact, someone the recipient had exchanged email with before. But that contact's real address was on a completely different domain. This message came from ccc_29340@yahoo[.]com, a free-mail account with no connection to the organization.
The subject line, "Email Change Request," was the social engineering payload. The attacker wanted the recipient to respond with updated account or contact details, a classic precursor to account takeover and business email compromise. No technical exploit needed. Just a reply.
Microsoft Saw It, Microsoft Didn't Stop It
The email headers tell a revealing story. Microsoft's own impersonation detection triggered a safety tip (SFTY:9.25), meaning the system recognized the display name was associated with a different known sender address. The Spam Confidence Level sat at 1, well below any quarantine threshold.
Microsoft identified this as a likely impersonation attempt and delivered it anyway. The safety tip is informational, not blocking. For a government employee processing dozens of emails a day, a subtle banner is easy to overlook when the display name looks familiar.
The Signal That Mattered
Themis, the IRONSCALES Adaptive AI, flagged the email at 68% confidence based on sender fingerprint analysis. The platform maintains a history of which display names correspond to which sending addresses. When a known name appeared from an unknown address, the mismatch triggered elevated scrutiny.
This is the detection surface that zero-payload BEC deliberately targets. No artifacts to scan, no URLs to detonate, no files to sandbox. The only signal is behavioral: this name has never come from this address before.
One mailbox was quarantined. The reporter confirmed the message as phishing.
Indicators of Compromise
| Type | Indicator | Context |
|---|---|---|
| Sender Email | ccc_29340@yahoo[.]com | Yahoo free-mail, display name impersonation |
| SPF | Pass (34[.]2[.]64[.]18, sonic.asd.mail.yahoo.com) | Legitimate Yahoo infrastructure |
| DKIM | Pass (d=yahoo.com) | Yahoo-signed |
| DMARC | Pass (compauth=100) | Full authentication alignment |
| SFTY | 9.25 | Microsoft impersonation safety tip triggered |
| SCL | 1 | Below quarantine threshold |
MITRE ATT&CK Mapping
| Technique | ID | Relevance |
|---|---|---|
| Impersonation | T1656 | Exact display name matched a known internal contact |
| Phishing for Information | T1598 | Account change request designed to elicit sensitive response |
Authentication tells you the infrastructure is real. It does not tell you the person is who they claim to be. When the payload is a name and a polite request, the only defense is a system that remembers who sends from where.
Related attacks
| Attack | What happened |
|---|---|
| The Payroll Change Request That Passed Every Authentication Check | A zero-payload BEC email requesting a payroll direct deposit change passed SPF, DKIM, and DMARC using a free Gmail account. |
| No Links. No Attachments. No Malware. Just Five Sentences That Almost Started a Wire Fraud. | A BEC attack impersonating a cybersecurity company's CEO contained zero links, zero attachments, and zero malware. |
| The CEO's Name Was Real. The Mailjet Account Behind It Wasn't. | An attacker impersonated the CEO of an email security company using a legitimate Mailjet ESP account with full SPF/DKIM pass. |
| No Links. No Attachments. Just a Polite Request for Every Employee's W-2. | An email requesting complete W-2 forms for all employees contained zero links, zero attachments, and zero malicious indicators. |
| The Anonymous Complaint That Was Actually a Data Extraction Operation | An anonymous complaint from a Gmail account passed SPF, DKIM, and DMARC, contained no links and no attachments, and requested Jira audit logs. |
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)