Table of Contents
In our last blog post, we discussed the complexities of email phishing and the role of automation in expediting the forensics phase. In it, we highlighted that, despite a phishing-informed workforce identifying suspicious emails more frequently, the forensics process often stalls significantly from there, especially for companies that rely on SOC teams for analysis and remediation. And while it can certainly be daunting for employees to wait for the SOC team to confirm an attack or determine it to be a false positive, there’s still more to do before it’s business as usual.
The remedy for phishing attacks has traditionally centered on human intelligence, or the belief that extensive training can transform ordinary workers into hyper-vigilant phishing detectives. This method relies on employees to identify any suspicious emails and report them to the SOC team, who then must manually respond to reports in the order they are received as well as create rules/signatures to prevent the same email from breaching the system again. Unfortunately, however, this hyper-vigilant workforce often gets a little trigger happy with reporting suspicious emails, resulting in an alarmingly high rate of false alarms. In fact, according to the Ponemon Institute, by the end of 2017, the average SOC team will have spent around 20,000 hours on false alarms – hours better spent remediating the increasingly frequent, sophisticated and legitimate attacks.
According to Symantec’s July’s Latest Intelligence, the phishing rate increased up to one in 1,968 emails in July, making it the highest rate seen for the past 12 months. Making matters worse, the significant shortage in the cybersecurity workforce means companies’ SOC teams are understaffed and overburdened. The result? The time from identification to remediation is up to several months – leaving the hacker with free reign to roam the networks and steal corporate proprietary and customer information without consequence, despite an employee sounding the alarm.
To better understand the process SOC teams must undertake after confirming that a phishing email is a legitimate attack, we’ve broken down the next phase of email phishing response: remediation and prevention. The following steps, without exception, must be performed for each and every identified phishing email:
- Once a phishing email is identified as legitimate, the SOC team must then block the mail source (IP) and sender address in the Firewall and mail GW.
- If a link was attached to the mail, then it’s recommended that they also block it in the web gateway so that people will not be able to access it.
- If it is a malware infection, you might need to update your IPS signatures, as well, to block further inspection.
- Then, the team must delete it from all mailboxes using commands by the provider platform.
- Finally, they must discover who opened the mail in order to examine all of their endpoint devices.
While this may seem like a short list, the remediation and prevention process alone can take the SOC team several hours to as much as several days to complete. Multiply that by the hundreds to thousands of reported suspicious phishing attacks each month and the backlog of forensics to conduct begins to grow and grow.
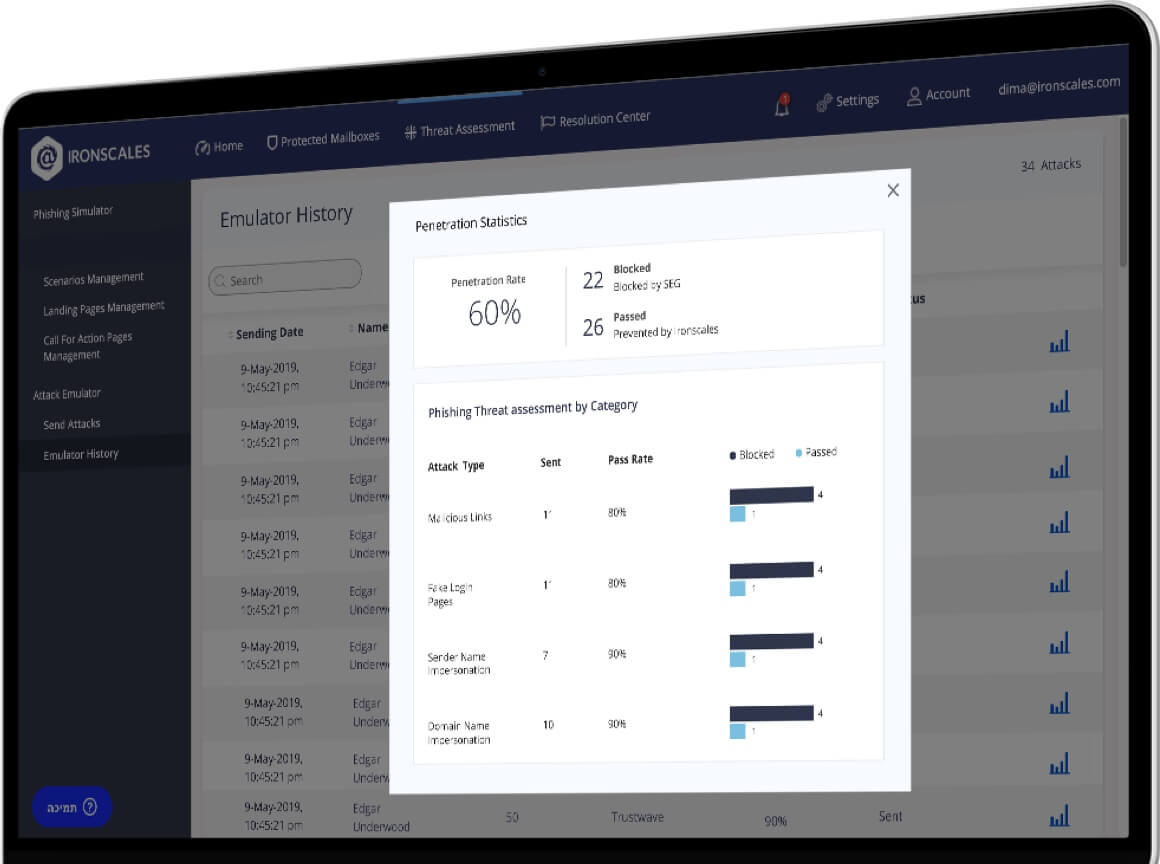
To relieve the SOC team’s workload, we built IronTraps, an automatic phishing incident response technology that empowers employees to seamlessly report suspicious emails in real-time. With just the click of one button, an immediate automated deep forensics scan is triggered, followed by an enterprise-wide remediation response that significantly reduces the time malicious emails lie idle in employees’ inboxes.
With IronTraps, organizations benefit from the ability to expedite incident response and reduce SOC workload burden by fully automating:
- Forensics
- Orchestration
- Mitigation
- Remediation (endpoint + server side)
- Intelligent Spam Handling
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)










/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)