Table of Contents
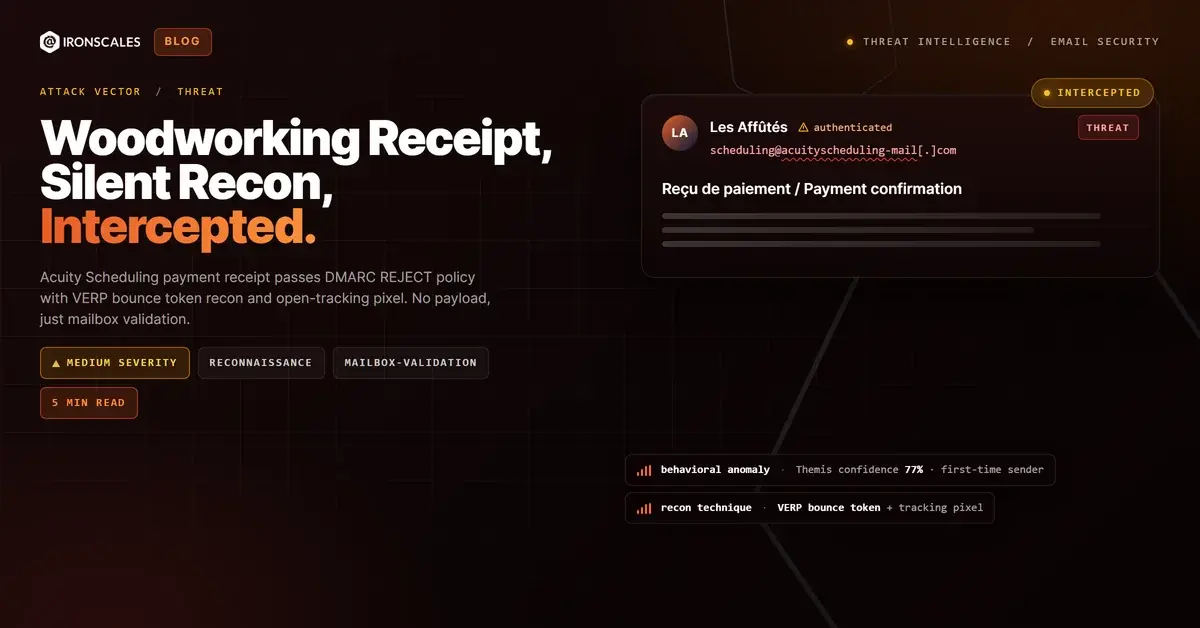
A bilingual payment receipt for a Canadian woodworking class landed in an employee's inbox at a digital advertising firm. The subject line: "Reçu de paiement / Payment confirmation." The body showed a 180-minute woodworking workshop booking, a $113.83 CAD subtotal, a $100 gift voucher discount, and a final charge of $13.83 CAD. The branding, layout, and formatting were pixel-perfect Acuity Scheduling. SPF passed. DKIM passed. DMARC passed under a REJECT enforcement policy. There were no attachments. No clickable links in the body. No credential form.
Nobody at this company signed up for a woodworking class in Montreal.
The email contained exactly two things worth paying attention to, and neither was visible to the recipient: a VERP-encoded bounce token in the Return-Path and an HTTP open-tracking pixel in the message body. Together, they form a silent mailbox validation system that confirms whether the recipient address is live, whether the mailbox renders external resources, and exactly when the message was opened.
Anatomy of a Zero-Payload Recon Message
The email originated from scheduling@acuityscheduling-mail[.]com with display name "Les Affûtés," a real woodworking studio in Montreal. It was sent through Acuity Scheduling infrastructure (owned by Squarespace) and relayed via SendGrid at IP 198[.]21[.]4[.]208, resolving to o9.ptr858.acuityscheduling-mail[.]com.
The authentication chain was spotless:
- SPF: Pass (198[.]21[.]4[.]208 designated as permitted sender for acuityscheduling-mail[.]com)
- DKIM: Pass (selector
s1, domain acuityscheduling-mail[.]com) - DMARC: Pass (policy p=REJECT, sp=REJECT, disposition=NONE)
- ARC: Intact chain through Google MX
WHOIS for acuityscheduling-mail[.]com shows registration through MarkMonitor with Squarespace, Inc. as the registrant, created 2024-01-23. This is not a lookalike domain or a compromised relay. It is the legitimate sending domain for Acuity Scheduling transactional emails. That is what makes this case instructive.
The Bounce Token: Confirming Mailboxes Without a Click
The Return-Path header contained: bounces+55675-2363-{recipient}={domain}[.]com@em582.acuityscheduling-mail[.]com
This is a VERP (Variable Envelope Return Path) encoding. The recipient's full email address is embedded directly in the bounce address, with the @ symbol replaced by =. In this case, the employee's username and corporate domain appeared verbatim in the Return-Path. If the target mailbox does not exist, the resulting Non-Delivery Report routes back to a sender-controlled bounce address that identifies the exact failed recipient. If no bounce comes back, the address is confirmed live.
This technique requires zero interaction from the recipient. The mailbox validation happens at the SMTP layer before the email is even rendered. A threat actor who sends 10,000 of these receipts through a legitimate scheduling platform gets a validated target list back purely from bounce and non-bounce responses.
See Your Risk: Calculate how many threats your SEG is missing
The Tracking Pixel: Confirming Engagement
The second recon mechanism was an HTTP open-tracking pixel hosted at hxxp://url860.acuityscheduling-mail[.]com/wf/open?upn=... with encoded token parameters. When the email client renders the message (even in a preview pane), this pixel fires an HTTP request back to the sender infrastructure, confirming:
- The mailbox is not only live but actively monitored
- The recipient's email client renders external content (not blocked by proxy or policy)
- The exact timestamp of the open event
Combined with the bounce token, this creates a two-signal confirmation loop. Bounce analysis confirms the mailbox exists at the SMTP level. The tracking pixel confirms a human is reading messages. According to the Verizon 2024 DBIR, reconnaissance is a consistent precursor to targeted spearphishing. Validated email lists are the raw material for BEC and credential harvesting campaigns that the FBI IC3 2024 Report estimated at over $2.9 billion in losses.
Why Authentication Did Not Help
Every authentication mechanism worked as designed. SPF confirmed the sending IP was authorized. DKIM confirmed message integrity. DMARC confirmed domain alignment under a REJECT policy.
None of that matters here. Authentication answers "who sent this?" It does not answer "why did they send it?" or "should this recipient receive it?" The Microsoft Digital Defense Report 2024 documents a steady rise in attacks leveraging legitimate cloud services, precisely because authentication creates a false sense of safety. CISA phishing guidance warns that even messages from trusted senders can be malicious. A DMARC REJECT policy protects the sending domain's reputation. It does nothing to protect the recipient from unsolicited messages sent through that domain's legitimate infrastructure.
This is the structural gap that behavioral detection models are designed to fill. The IRONSCALES Adaptive AI flagged this message at 77% confidence based on behavioral anomalies: first-time sender, no prior relationship between the recipient organization and the sender, and a mismatched context (a French-language woodworking receipt sent to an English-speaking ad-tech firm).
Traditional secure email gateways would pass this message without hesitation. Every link resolves to Acuity/Squarespace CDN infrastructure. There is no payload to detonate, no attachment to sandbox, and no URL reputation signal to trigger on.
The Recon Pipeline: What Comes Next
This receipt is not the attack. It is the setup. An adversary using legitimate transactional platforms for mailbox validation is building a target list for subsequent campaigns. The MITRE ATT&CK framework classifies this under T1598 (Phishing for Information) and T1589.002 (Gather Victim Identity Information: Email Addresses).
The progression is predictable: validate the mailbox, confirm the recipient reads messages, then deliver the real payload in a follow-up email that references the prior receipt or mimics the same platform branding. The IBM Cost of a Data Breach Report 2024 found that phishing remains the most expensive initial attack vector at $4.88 million per breach on average, and that cost starts with exactly this kind of target validation. The second email will also pass authentication because it will also come from a legitimate service.
Organizations that block based solely on sender reputation, domain age, or link scanning will miss both stages.
Defensive Recommendations for Recon-Stage Threats
Block HTTP tracking pixels at the mail gateway. Proxy all external image loads through a gateway-level image proxy, or strip tracking pixels entirely. This breaks the engagement confirmation loop.
Monitor for VERP-encoded bounce tokens. Return-Path values that embed the recipient address in the bounce path are a signal. Unexpected VERP-encoded messages from first-time senders warrant scrutiny.
Flag first-time sender plus contextual mismatch. A French-language woodworking receipt sent to an ad-tech company is a context gap that community-driven threat intelligence can catch when static analysis cannot. Across 1,921 organizations and 35,000+ security professionals, collective behavioral signals surface these mismatches in real time.
Treat clean recon emails as threat indicators. If a mailbox receives an unsolicited transactional receipt with no prior business relationship, the address may already be on a validated target list. Increase monitoring for follow-up phishing within 7 to 14 days.
| Type | Indicator | Context |
|---|---|---|
| Sender Email | scheduling@acuityscheduling-mail[.]com | Legitimate Acuity Scheduling sending address |
| Return-Path | bounces+55675-2363-{recipient}@em582.acuityscheduling-mail[.]com | VERP-encoded bounce token with recipient address |
| Sending IP | 198[.]21[.]4[.]208 | Resolves to o9.ptr858.acuityscheduling-mail[.]com |
| Tracking Pixel | hxxp://url860.acuityscheduling-mail[.]com/wf/open?upn=... | HTTP open-tracking pixel for engagement confirmation |
| Logo CDN | hxxps://cdn-s.acuityscheduling[.]com/logo16985997.png | Hosted brand asset on Acuity CDN |
| DKIM Selector | s1.acuityscheduling-mail[.]com | Valid DKIM signing selector |
| Internal Relay | churchill-backend-production-qw-notifications | Acuity/Squarespace internal relay hostname |
| Internal Relay | geopod-ismtpd-canary-0 | SendGrid canary relay infrastructure |
Related attacks
| Attack | What happened |
|---|---|
| Purpose-Built Look-Alike Sending Domain Passes Full Authentication to Impersonate Training Brand | An attacker registered a purpose-built sending domain that mirrors a legitimate training company's naming pattern. |
| The Marketing Email That Forgot to Fill In Its Own Template | A phishing email arrived with the recipient's address still inside an unsubstituted template variable in the greeting. |
| Six Words, No Payload: How a Fabricated Gmail Thread Turned a Law Firm Into a Reconnaissance Relay | A six-word email with zero links and zero attachments passed authentication by routing through a legitimate law firm's Mimecast gateway. |
| The Datadog Alert That Came From the Wrong Domain: Authenticated Brand Impersonation With All Links Pointing to Real Infrastructure | A fully authenticated Datadog monitor alert arrived from dtdg.co, not datadoghq.com. |
| The Web Design Pitch That Routed Through a Mailing List Nobody Subscribed To | A vendor-scam email was sent via a Gmail account but routed through a Google Groups mailing list on a privacy-protected domain registered seven months... |
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)