Table of Contents
A Lab Result From a Platform Nobody Faked
A staff member at a regional healthcare organization received a notification: a patient had an updated lab result waiting in the portal. The email carried the branding of a pediatric care practice, complete with logo, HIPAA confidentiality disclaimer, and a direct phone number that matched publicly listed records for the clinic.
Every automated security check approved the message. SPF passed. DKIM passed. DMARC passed. Microsoft's spam confidence level scored it a 1, the lowest non-zero risk rating. The organization's own external email banner fired, but the content looked exactly like a legitimate patient engagement notification.
It was a credential harvest.
The platform that sent it, bridgeinteract.io, is a real HIPAA-adjacent patient engagement system used by pediatric and specialty practices across the United States. The attacker did not need to spoof it. They used it.
How a Real Platform Becomes the Attack Vector
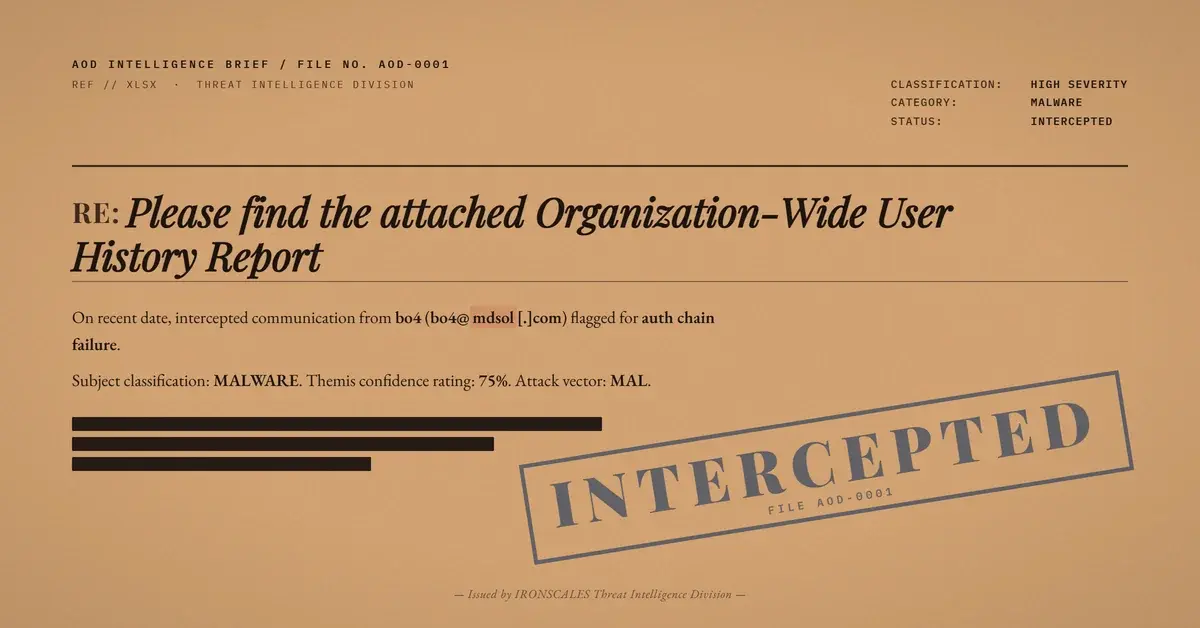
The attack followed a precise five-step chain, each designed to exploit the trust healthcare organizations place in third-party clinical platforms.
Step 1: Platform access. The attacker gained access to a bridgeinteract.io account configured for a pediatric practice. Whether through compromised credentials, a trial account, or social engineering of the platform's onboarding process, the attacker obtained the ability to send authenticated emails through the platform's SendGrid-based infrastructure (T1078: Valid Accounts).
Step 2: Authenticated delivery. The email was sent from noreply@bridgeinteract[.]io with a Return-Path routed through em7412.bridgeinteract[.]io, a SendGrid subdomain configured for the platform. The DKIM signature validated against bridgeinteract.io. SPF passed for the sending IP 159[.]183[.]108[.]7, which belongs to SendGrid's outbound mail infrastructure. DMARC passed with action=none. From the perspective of every authentication protocol, this email was legitimate (T1566.001: Spearphishing Attachment).
Step 3: Brand overlay. The From display name read "Pediatric Care Specialists," but the authenticated domain was bridgeinteract.io. This is the critical mismatch. The recipient's mail client displayed a trusted clinic name. The authentication headers validated a completely different domain. No standard email filter flags this because third-party sending platforms are common in healthcare.
Step 4: Redirect chain obfuscation. The "View Result" button linked through a SendGrid click-tracking URL (u56329932.ct.sendgrid[.]net), which was then wrapped by Microsoft SafeLinks. The redirect chain meant the actual destination was never visible to the recipient. Both the tracking domain and SafeLinks resolved to a page hosted on pcs.portal.officepracticum[.]com, a legitimate patient portal domain.
Step 5: Credential collection. The landing page presented a fully functional login form with email and password fields, branded to the pediatric practice, and powered by Bridge Interact v3.141.0. The page included "Login with mobile phone number" and "Recover password" options, reinforcing the appearance of a real portal. Any credentials entered here would be captured by the attacker (T1556: Modify Authentication Process).
The Authentication Paradox in Healthcare Email
This attack exploits a fundamental gap in how email authentication works. SPF, DKIM, and DMARC answer one question: did the email come from the domain it claims to come from? In this case, the answer was yes. The email did come from bridgeinteract.io. The protocols worked exactly as designed.
What they cannot answer is whether the entity using that platform is authorized to represent the brand displayed in the email. "Pediatric Care Specialists" appeared in the From name and throughout the email body, but bridgeinteract.io was the authenticated sender. This is not a spoofing failure. It is a trust model failure.
Healthcare is uniquely vulnerable to this technique. The industry relies heavily on third-party patient engagement platforms, electronic health record notification systems, and clinical communication tools that all send email on behalf of practices. Staff members are trained to expect emails from platforms they did not set up and may not recognize by domain name. The HIPAA Journal has documented hundreds of breaches originating from compromised healthcare communication platforms, and the pattern continues to accelerate.
According to the IBM Cost of a Data Breach Report 2024, healthcare remains the most expensive industry for data breaches at $9.77 million per incident. Credential theft is the most common initial access vector across all industries, according to the Verizon DBIR 2024.
See Your Risk: Calculate how many threats your SEG is missing
What the Sending Domain Revealed (and What the Filters Missed)
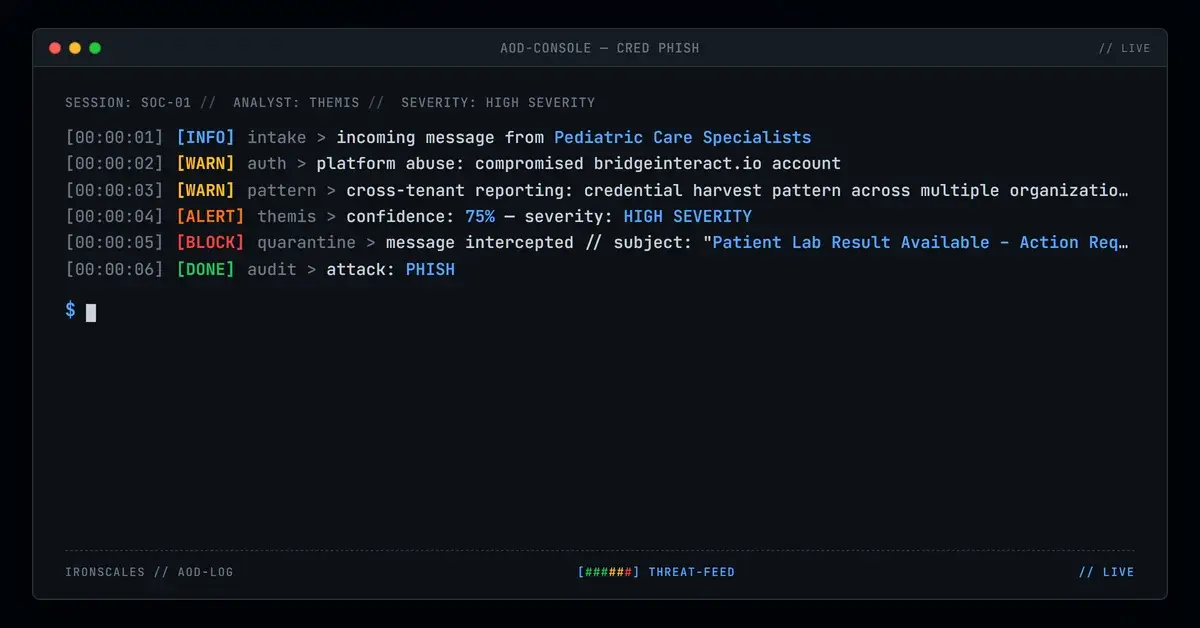
The IRONSCALES community flagged this email based on behavioral signals that authentication protocols do not evaluate. The platform identified a high sender risk level for noreply@bridgeinteract[.]io based on cross-tenant reporting. Multiple organizations had received similar messages from this sender, and the community confidence for a phishing classification was high.
The email was quarantined across three affected mailboxes within seconds of detection. The key signal was not a failed authentication check. It was the pattern of a platform-authenticated sender distributing credential harvesting lures across multiple unrelated healthcare organizations simultaneously.
A minor grammatical error in the body ("a updated lab result" instead of "an updated lab result") provided one additional surface-level indicator. But relying on grammatical tells is a losing strategy. The next iteration of this attack will fix the typo. The behavioral pattern (authenticated platform, brand mismatch, cross-tenant distribution) will remain.
Indicators of Compromise
| Type | Indicator | Context |
|---|---|---|
| Domain | bridgeinteract[.]io | Authenticated sending domain |
| Domain | em7412.bridgeinteract[.]io | Return-Path subdomain (SendGrid) |
| Domain | u56329932.ct.sendgrid[.]net | SendGrid click-tracking subdomain |
| Domain | pcs.portal.officepracticum[.]com | Credential harvest landing page |
| IP | 159[.]183[.]108[.]7 | Sending IP (SendGrid outbound) |
noreply@bridgeinteract[.]io | Envelope sender | |
| URL | hxxps://u56329932[.]ct[.]sendgrid[.]net/ls/click?upn=u001.olYBg0au8VGhVvR... | Tracked redirect to portal login |
| Header | DKIM d=bridgeinteract[.]io | Authenticated DKIM domain |
Platform Abuse Detection for Healthcare Security Teams
Standard authentication checks will not catch this class of attack. The email is, by every protocol definition, "authentic." Here is what security teams in healthcare should look for instead.
Monitor brand-to-domain mismatches. When the display name references a clinic, hospital, or practice, but the authenticated domain belongs to a platform vendor, that mismatch deserves scrutiny. Automated rules can flag emails where the From display name does not match the DKIM signing domain.
Track cross-tenant sender patterns. A legitimate patient engagement platform sends to patients of a specific practice. When the same sender distributes identical lures to staff members at unrelated organizations, that is a distribution pattern consistent with credential harvesting, not patient communication. The IRONSCALES community detection model identified exactly this pattern.
Enforce MFA on all patient portals. Even if credentials are stolen, multi-factor authentication prevents direct account compromise. CISA's phishing guidance consistently recommends MFA as the single most effective mitigation against credential theft.
Audit third-party platform access. Healthcare organizations should maintain an inventory of every platform authorized to send email on their behalf. The Microsoft Digital Defense Report 2024 highlights third-party platform abuse as a growing vector in regulated industries.
The attacker did not compromise any email infrastructure or forge a single header. They logged into a real platform, sent a real notification, and pointed it at a real login page. The only defense that worked was behavioral analysis that asked a different question: why is this platform sending credential prompts to organizations that are not its customers?
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)