Table of Contents
The subject line read: Important VN ##NUMRANDOM5## - ##DATE##.
Not a substitution. Not a rendered value. The raw template tokens, exactly as they appear in the attacker's campaign builder, shipped to every recipient. The mail merge failed. The attacker either didn't notice or didn't care, hit send anyway, and the email landed in the finance team's inbox.
Microsoft Exchange Online Protection scored it a 1 on the spam confidence scale. Not spam. Not suspicious. Delivered.
What the Finance Team Actually Saw
The body looked like an Oracle NetSuite notification. Microsoft logo colors at the top (the colored tile grid), an Oracle NetSuite wordmark in the dark footer, a legitimate-looking address in Austin. The heading said: "Here Is The Important Voice Mail You Just Received."
The salutation: "Dear Finance."
Not a name. Not a role. The word "Finance," addressed to a team distribution alias. The message said a voicemail had been delivered by "Ironscales Voip service" on 6/11/2025, duration 1:44. There was a teal button labeled PLAY NOW.
A few things were off to a careful reader. The typos: "voicing mailbox" instead of "voice mailbox," "Durationn" with two n's. The fact that Oracle NetSuite does not deliver voicemails. The fact that the subject line was visibly broken. But finance teams process dozens of automated notifications daily, and this one had the right visual weight: corporate template, branded footer, a specific duration timestamp, an urgent action prompt. The "PLAY NOW" button is exactly the kind of thing that gets clicked in a busy queue.
The Infrastructure Behind the Button
The PLAY NOW button pointed to a free Wix subdomain (david42511[.]wixsite[.]com). From there, the redirect chain ran four more hops before resolving to anything definitive.
Hop 1: Wix subdomain. Free hosting, frequently abused for phishing staging, legitimate domain reputation. Hop 2: y7zpl9811m345vx6[.]click[.]mailersend[.]net — MailerSend click tracker. A legitimate transactional email platform's tracking infrastructure. Hop 3: 10vv6[.]mjt[.]lu — Mailjet tracking hop. Another legitimate email service provider's redirect. Hop 4: backup[.]dapteknik[.]com — the penultimate destination. Domain registered March 10, 2025. Twenty-seven days old at the time of delivery. Turkish registrar, unsigned DNSSEC, no registrant data, nameservers pointing to ajansay[.]com. Nothing about this domain belongs near an Oracle NetSuite notification. Hop 5: host[.]com — a 403. Geo-gated or user-agent filtered. Automated scanners see a dead end. Real victims in the right geography with the right browser get the payload.
This is the architecture of scanner evasion. Each of the first three hops is a platform with genuine domain reputation. URL reputation checks see MailerSend and Mailjet and pass. By the time the chain reaches the young, unregistered-looking domain at hop 4 and the gated 403 at hop 5, any scanner that followed the chain has already timed out or given up. The payload never had to reveal itself to any automated system.
See Your Risk: Calculate how many phishing emails your gateway is missing right now
Authentication Passed. That Was Never the Problem.
The sender was beth@newdayranch[.]org, a nonprofit organization's domain, routed through Amazon SES. SPF passed because SES is a permitted sender for the domain. DKIM passed with valid signatures for both newdayranch.org and amazonses.com. DMARC was not published at all (_dmarc.newdayranch.org returned NXDOMAIN), so EOP defaulted to a best-guess pass with no enforcement action.
The email was technically legitimate from a transport perspective. The delivery path was: Amazon SES in us-west-2, to Microsoft EOP, to internal Exchange Online transports, to the recipient mailboxes. TLS 1.3 the whole way. Clean relay chain.
This is the authentication gap that practitioners run into constantly. SPF tells you whether the sending server is authorized by the domain owner. DKIM tells you the message wasn't tampered with in transit. Neither tells you anything about whether the person controlling that domain intends to phish your employees. A compromised nonprofit account, or one set up specifically to abuse SES at low volume, passes every authentication check cleanly. According to the Verizon 2024 Data Breach Investigations Report, phishing remains a top initial access vector specifically because attackers have adapted to authentication controls, not because those controls don't work.
The Microsoft Digital Defense Report 2024 makes the same point: high-volume phishing campaigns increasingly route through legitimate cloud email infrastructure to inherit trusted reputation scores. The message in this case scored SCL:1. That is one step above absolute zero on EOP's confidence scale.
What Caught It
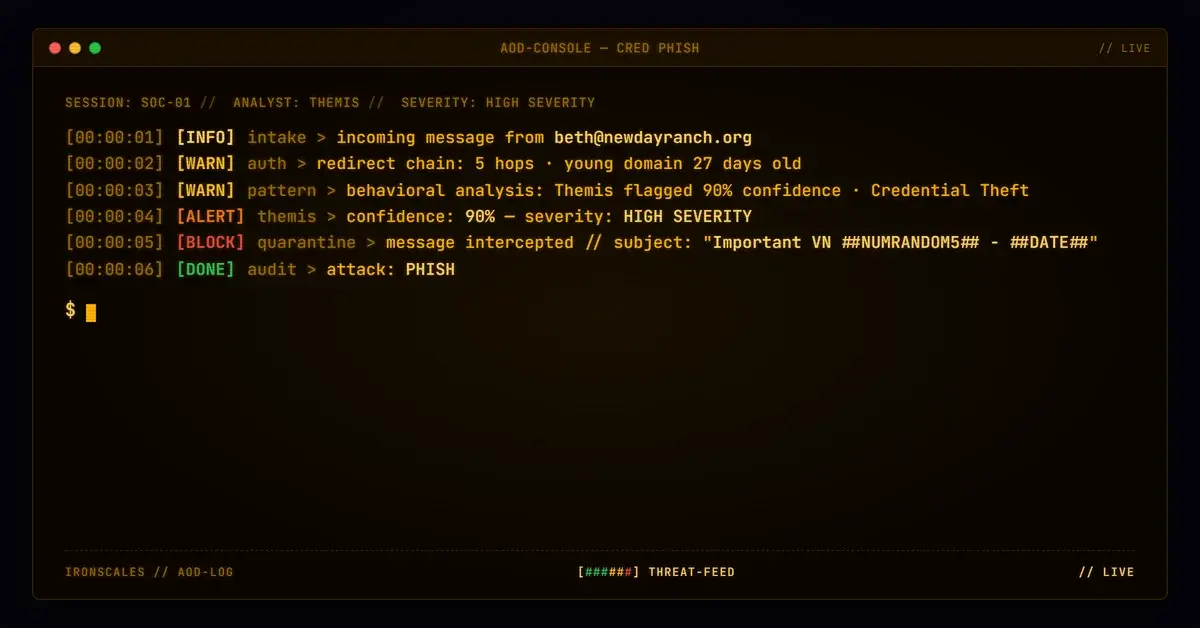
Themis flagged the PLAY NOW link at 90% confidence, labeled it Credential Theft, and noted the VIP Recipient signal (the finance distribution alias). IRONSCALES quarantined the email across four mailboxes. The first quarantine action happened roughly 30 minutes after delivery. All four were resolved the same day.
No one clicked the button. Or if they did, the quarantine happened before the credential page loaded.
The detection relied on behavioral signals and community intelligence, not on the redirect chain resolving to something identifiable. Across the IRONSCALES platform's global community of over 35,000 security professionals, the structural pattern of stacked click-tracker hops ending on a young, privacy-shielded domain had already been flagged in similar incidents. The community signal combined with link behavior analysis is what the IRONSCALES Adaptive AI engine uses to evaluate threats that authentication and static URL reputation checks can't reach.
The Broken Template Problem
The unreplaced tokens deserve a moment. ##NUMRANDOM5## and ##DATE## are placeholder syntax from whatever campaign tool the attacker was using. The template engine failed to substitute them before the batch fired. This is the kind of error that occasionally gets used as evidence that phishing campaigns are easy to spot.
It is not evidence of that.
The email still passed every authentication control. It still got a benign spam score. It still had polished visual design with real brand assets. The only thing the broken tokens reveal is that the attacker is running campaigns at scale, using templating infrastructure to randomize subjects and dates across thousands of sends. The failed substitution is a production error, not a competence indicator. According to the FBI IC3 2024 Internet Crime Report, BEC and phishing losses exceeded $2.9 billion last year. Those campaigns were not stopped by visible typos.
A defender who sees ##NUMRANDOM5## in a subject line and thinks "obvious, caught it" is correct exactly once. The same campaign template, working correctly, would have shipped a numeric string and a date. It would have looked like every other voicemail notification in the queue.
IOCs
| Type | Indicator | Context |
|---|---|---|
| Domain | dapteknik[.]com | Penultimate redirect destination. Registered 2025-03-10, Turkish registrar, no registrant data |
| Subdomain | backup[.]dapteknik[.]com | Direct link target at hop 4 of redirect chain |
| URL | hxxps://david42511[.]wixsite[.]com/so/96PfQFT_U/c | Initial PLAY NOW button destination, Wix-hosted redirect |
| URL | hxxps://y7zpl9811m345vx6[.]click[.]mailersend[.]net/tl/cws/[...] | MailerSend click tracker, hop 2 |
| URL | hxxps://10vv6[.]mjt[.]lu/lnk/[...] | Mailjet tracking hop, hop 3 |
| Sender domain | newdayranch[.]org | Legitimate nonprofit domain used as sending envelope; SPF/DKIM pass |
| Sending IP | 54[.]240[.]27[.]209 | Amazon SES us-west-2 egress; PTR resolves to expected SES hostname |
What to Do With This Pattern
The five-hop tracker chain is not exotic. It is a repeatable evasion template that attackers assemble from publicly available, free-tier services. Any combination of Wix, SendGrid, MailerSend, Mailjet, and a freshly registered parking domain can produce this structure in an afternoon.
Three things to evaluate in your environment:
- Domain age as a signal. A 27-day-old domain in a redirect chain should trigger escalated scrutiny regardless of what the earlier hops look like. If your email security stack is not factoring domain registration recency into link scoring, you are missing a high-signal indicator. The IRONSCALES advanced URL protection layer evaluates this as part of multi-signal link analysis.
- DMARC enforcement gaps. The sending domain had no DMARC record at all. NXDOMAIN on the
_dmarcsubdomain means there is no policy to enforce and no reporting to learn from. DMARC absence is not a blocker for mail delivery. It is a gap that reduces your visibility into abuse of domains that are routing through your trust perimeter. IRONSCALES DMARC management provides visibility and enforcement across sender domains in your ecosystem.
- Voicemail lures going to group aliases. A phishing email addressed generically to "Finance" and delivered to a distribution alias is not spear phishing. It is spray phishing with brand impersonation. The fact that it hit a finance alias specifically, one that presumably receives legitimate Oracle NetSuite notifications, suggests some degree of targeting. Security awareness training that includes voicemail lure simulations helps finance and accounting teams build the skepticism reflex before the real version arrives.
The broken tokens were an accident. The landing was not.
Related attacks
| Attack | What happened |
|---|---|
| The Password Expiry Email That Hid Its Destination in a Base64 Fragment | A password-expiry lure used a Base64-encoded URL fragment to hide its Shopify-hosted credential harvesting page from link scanners. |
| When the Safety Wrapper Becomes the Disguise: Brazilian NF-e Phishing via Safe Links Rewrite | A Portuguese-language invoice lure authenticated through a compromised Brazilian domain used is.gd to hide its payload. |
| The Button Text Was the Weapon: Unicode RTL Obfuscation Inside a DocuSign Lure | Attackers embedded Unicode right-to-left marks directly inside a CTA button label to scatter the string for NLP scanners. |
| Sign Here, Get Phished: Inside an Adobe Sign Lure With a Multi-Hop Redirect to Credential Theft | An Adobe Sign e-signature lure routed recipients through a multi-hop redirect chain ending at fameklinik[.]com. |
| DocuSign Plus Invoice: A 12-Day-Old Domain and an esvalabs Redirect Chain That Scanners Missed | A phishing campaign combined DocuSign branding with an invoice thread pretext, sent from a 12-day-old privacy-protected domain via Amazon SES. |
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)