Table of Contents
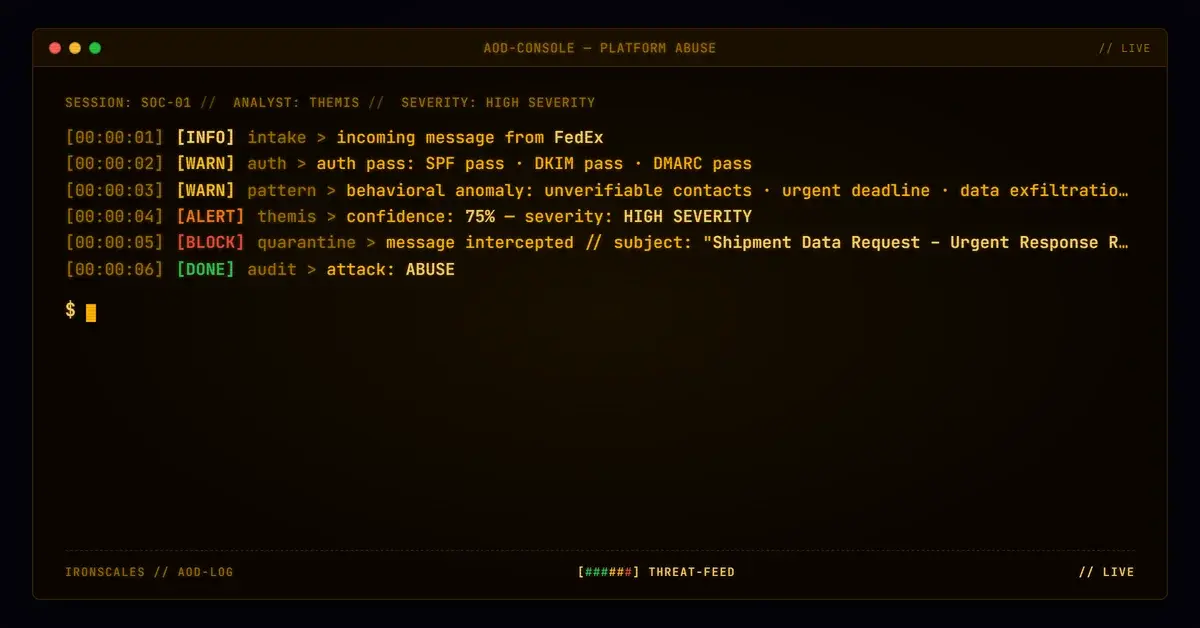
SPF passed. DKIM passed. DMARC passed with compauth=100. Every link in the email resolved to the sender's real corporate website. There were zero attachments. The body contained no credential requests, no urgency cues, no threats of account suspension. Microsoft assigned a spam confidence level of 1 (lowest possible above zero).
By every measurable technical standard, this email was legitimate.
Adaptive AI flagged it anyway. The label: Vishing Attack.
Here is how a perfectly authenticated email from a Fortune 500 company's customer portal became a case study in why authentication alone cannot protect your organization.
A Welcome Nobody Asked For
On March 30, 2026, an employee at a mid-size metals fabrication firm received a "Welcome to myBLDR" email from CustomerPortalSupport@bldr[.]com. The message was clean, polished, and branded with the correct corporate logo, footer, and copyright notice. It congratulated the recipient on creating an account with the sender's B2B procurement portal and offered a support phone number for any issues.
The problem: nobody at the recipient's organization had requested this account.
The email originated from a Fortune 500 building materials distributor (NYSE-listed, domain registered since 1998) and was sent through Microsoft 365 outbound protection infrastructure. The relay chain showed the message transiting outbound.protection.outlook.com with valid ARC signatures at every hop. The DKIM signature verified against the sender's published selector1 key. SPF confirmed the sending IP was authorized. DMARC policy evaluation returned action=none under the sender's p=quarantine policy because alignment was perfect.
In other words, the message was exactly what it claimed to be: a real transactional email from a real company's real portal.
The Behavioral Signals That Technical Controls Missed
Authentication protocols answer one question: did this email come from who it says it came from? They do not answer the more important question: should this recipient be receiving it?
Three behavioral signals converged to trigger the vishing classification:
First-time external sender. The recipient's organization had no prior communication history with this sender domain. A B2B procurement portal welcome email arriving with zero relationship context is anomalous. Legitimate onboarding follows a sales cycle, a purchase order, or at minimum, an employee's deliberate account creation.
Generic support alias. The From header used CustomerPortalSupport@bldr[.]com with a display name of "Customer Portal Support." The Reply-To pointed to a different generic alias: MyBFSBuilderSupport@bldr[.]com. Neither mailbox maps to an identifiable human. According to the FBI's 2024 IC3 Report, BEC and related social engineering attacks caused over $2.9 billion in losses, with impersonation of support functions being a primary vector.
Phone number as primary CTA. The email's only actionable element was a phone number: +1 (888) 444-8399. No credential forms. No login buttons. No links requiring clicks beyond the corporate homepage. This matches the vishing playbook precisely: deliver a legitimate-looking pretext, then redirect engagement to a voice channel where there are no URL scanners, no link rewriting, and no attachment sandboxes. The Verizon 2024 DBIR found that social engineering attacks increasingly combine email delivery with voice-channel exploitation, specifically because phone calls bypass every automated email security control.
See Your Risk: Calculate how many threats your SEG is missing
The Attack Chain: Business Process Abuse as Reconnaissance
This case maps to multiple MITRE ATT&CK techniques, though not in the traditional phishing sense:
T1078 (Valid Accounts): If an attacker created the portal account using the recipient's email address, they now have a confirmed valid business email tied to an active procurement relationship. This is account takeover reconnaissance.
T1598.003 (Phishing for Information: Spearphishing Link): The welcome email itself serves as a probe. If the recipient clicks through to the portal, the attacker learns the account is active and the email is monitored. If the recipient calls the support number, they may be socially engineered into providing additional credentials or business information.
T1566.001 (Phishing: Spearphishing Attachment): While this specific email contained no malicious payload, the established portal relationship creates a trusted channel for future attacks. Invoices, order confirmations, and shipping notifications from this domain will now pass every authentication check and carry the weight of an established business relationship.
The Microsoft Digital Defense Report 2024 documented this exact pattern: attackers increasingly abuse legitimate business processes to establish trusted communication channels before deploying their actual payload. The initial email is not the attack. It is the foundation.
Infrastructure Analysis
| Type | Indicator | Context |
|---|---|---|
| Domain | bldr[.]com | Sending domain. Fortune 500 building materials company. Registered 1998-05-26 via Network Solutions. DMARC p=quarantine. |
CustomerPortalSupport@bldr[.]com | From address. Generic departmental alias, no named individual. | |
MyBFSBuilderSupport@bldr[.]com | Reply-To address. Different alias than From, both generic. | |
| URL | hxxps://www[.]bldr[.]com/ | Link in email body. Resolves to legitimate corporate site. Clean verdict. |
| URL | hxxps://bldr[.]com/ | Footer link. Resolves to legitimate corporate site. Clean verdict. |
| Phone | +1 (888) 444-8399 | Support number in body and footer. Matches published company contact. Primary CTA. |
| IP | 2a01:111:f403:c105::7 | Sending IP. Microsoft outbound protection (PTR: mail-northcentralusazlp170130007[.]outbound[.]protection[.]outlook[.]com). |
| Auth | SPF=pass, DKIM=pass, DMARC=pass | Full authentication suite. compauth=100. SCL=1. |
Every IOC in this table is legitimate. That is precisely the point.
What This Means for Defenders
Authentication is necessary but insufficient. CISA's phishing guidance emphasizes SPF, DKIM, and DMARC as foundational controls. They are. But they verify sender identity, not sender intent. When the sender identity is real, authentication becomes invisible to the attack.
Monitor for unsolicited account creation. If your organization receives welcome emails from B2B portals that nobody requested, treat it as a potential indicator of compromise. Someone has your employee's business email and is establishing infrastructure for future social engineering.
Behavioral baselines matter more than signature databases. This email contained zero indicators that any static rule, blocklist, or signature engine would catch. The detection came from relationship analysis (first-time sender), communication pattern analysis (generic alias to specific employee), and CTA structure analysis (phone-only engagement path). These are the signals that AI-driven platforms evaluate and that legacy secure email gateways do not.
Treat vishing pretexts with the same urgency as credential harvesting. The IBM Cost of a Data Breach Report 2024 found that social engineering attacks involving phone-based vectors had among the highest average breach costs. An email that moves the conversation to a phone call is not less dangerous than one with a malicious link. It is more dangerous, because it exits every automated defense you have.
This case resolved as a false positive. The email was, in fact, a legitimate welcome message. But the behavioral signals that triggered the detection were real, and the attack pattern they describe is active in the wild. The difference between a false positive and a successful account takeover is often nothing more than the attacker's patience.
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)