Table of Contents
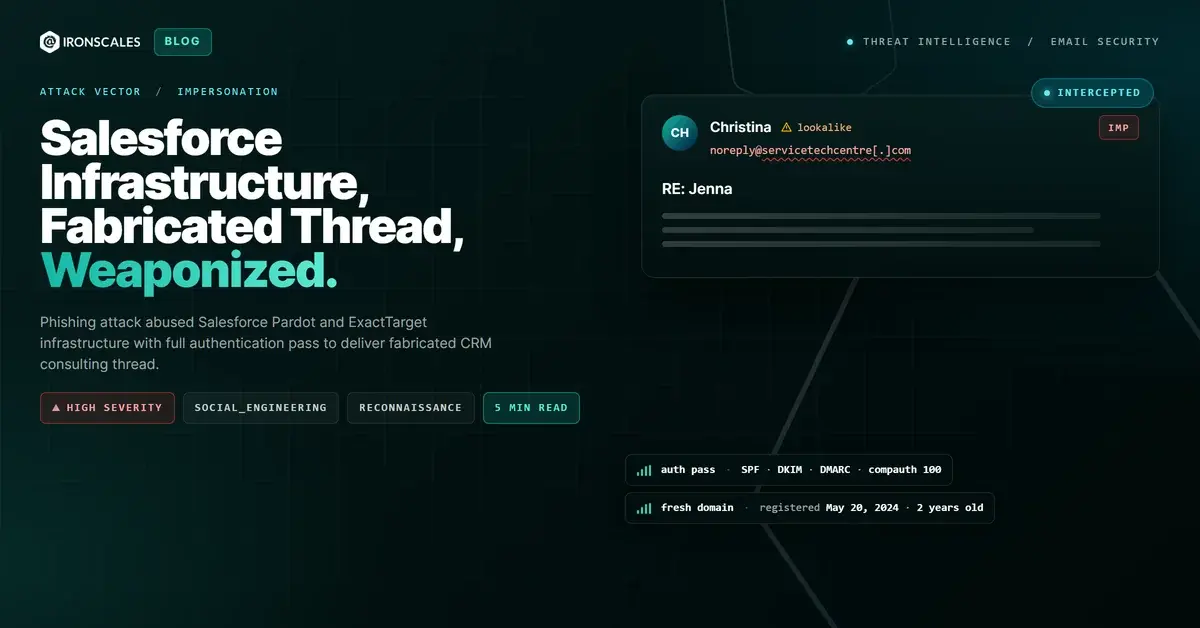
Every link in this email pointed to Salesforce-owned infrastructure. Every authentication check passed. The sending IP belonged to a Salesforce Marketing Cloud relay. And the Pardot unsubscribe endpoint at the bottom functioned exactly as expected. The only problem: the entire message was a phishing lure built on a fabricated email thread, sent from a privacy-shielded domain registered less than two years earlier.
This case demonstrates why authentication alone cannot stop phishing. When attackers provision accounts on trusted marketing platforms, they inherit the sending reputation of billion-dollar SaaS companies. The technical signals say "legitimate." The behavioral signals say otherwise.
Salesforce Infrastructure as a Phishing Delivery Vehicle
The attack used Salesforce Marketing Cloud (formerly ExactTarget) as its mail transfer agent (MTA). The message originated from amg5.mta.exacttarget.com at IP 128.245.249.5, a Salesforce-owned relay. The envelope return-path pointed to bounce[.]s13[.]mc[.]pd25[.]com, another Salesforce domain handling bounce processing for Marketing Cloud sends.
Authentication results reflected this legitimate infrastructure:
- SPF: Pass (128.245.249.5 is an authorized sender for
bounce[.]s13[.]mc[.]pd25[.]com) - DKIM: Pass (signature domain
servicetechcentre[.]com) - DMARC: Pass
- compauth: Pass, reason=100 (Microsoft's composite authentication score, the highest possible)
The attacker registered servicetechcentre[.]com on May 20, 2024, through Cosmotown, Inc., a budget registrar. WHOIS records are fully privacy-shielded. DNS runs through Cloudflare. The domain was less than two years old at the time of the attack, yet it carried a perfect composite authentication score because Salesforce's infrastructure vouched for it.
This maps to MITRE ATT&CK T1585.002 (Establish Accounts: Email Accounts) and T1566.002 (Phishing: Spearphishing Link). The attacker provisioned a Marketing Cloud account, configured DKIM signing for their domain, and leveraged Salesforce's sending reputation to bypass gateway filters.
Fabricated Thread and Social Engineering Construction
The subject line read "RE: Jenna," mimicking a reply to an ongoing conversation. This is a deliberate social engineering choice. Recipients who see "RE:" in a subject line assume prior context exists and lower their guard. The FBI IC3 2024 report documents business email compromise (BEC) as the costliest cybercrime category, and fabricated thread techniques are a core BEC tactic.
The email body reinforced the deception with a two-layer structure:
- Outer message: A short, personalized scheduling request ("Does Tuesday at 2:15 PM EST or Thursday at 11:00 AM EST work?") signed by "Christina." This mimics a genuine reply to create familiarity.
- Embedded "forwarded" message: A full marketing pitch from "V360," a supposed Salesforce consulting firm, offering "on-demand Salesforce consultants" and a "free CRM Health Checkup and issue discovery session." The forwarded block included fabricated headers (From, Sent, To, Subject) to simulate a prior email exchange.
The physical address in the signature (1047 Brea Mall, CA 92821) maps to a shopping mall in Brea, California. Not a registered business address for any Salesforce consulting partner.
This maps to MITRE ATT&CK T1598.003 (Phishing for Information: Spearphishing Link). The goal was reconnaissance and engagement, not immediate credential theft.
See Your Risk: Calculate how many threats your SEG is missing
Five-Layer Tracking and Reconnaissance Apparatus
The message contained no credential harvesting links. The only visible hyperlink pointed to a legitimate Pardot unsubscribe confirmation endpoint:
hxxp://go[.]pardot[.]com/unsubscribeConfirm/1103432/32eb6f8ec51d874f9776dd3af1f2b83bca8459a48de013c724919de7750a1a99/1641155776
But the absence of a malicious URL does not mean the absence of a payload. Hidden in the HTML source were five distinct tracking mechanisms:
| Tracking Method | Domain | Purpose |
|---|---|---|
| Pardot open pixel | go[.]pardot[.]com/r/.../open/1 | Standard open tracking via 1x1 image |
| emltrk light mode pixel | wo27degz.emltrk[.]com/v2/wo27degz?rl | Detects light-mode email client opens |
| emltrk dark mode pixel | wo27degz.emltrk[.]com/v2/wo27degz?rd | Detects dark-mode email client opens |
| emltrk print pixel | wo27degz.emltrk[.]com/v2/wo27degz?p | Detects when recipient prints the email |
| emltrk forward detection | wo27degz.emltrk[.]com/v2/wo27degz?f | Detects Outlook/Thunderbird forwarding via header-table CSS selectors |
The CSS-based tracking is particularly sophisticated. Instead of relying on standard image tags that many email clients block by default, the attacker embedded tracking URLs inside CSS @media queries and element-specific background-image rules. The prefers-color-scheme media queries differentiate between dark and light mode users. The div.OutlookMessageHeader and table.moz-email-headers-table selectors fire specifically when the email is forwarded in Outlook or Thunderbird, respectively. According to the Microsoft Digital Defense Report 2024, reconnaissance operations like this feed attacker targeting databases for higher-confidence follow-up campaigns.
The emltrk[.]com domain has been registered since 2010 and runs on AWS infrastructure. It functions as a dedicated email tracking service.
How IRONSCALES Detected What Authentication Could Not
Microsoft's own spam filter assigned this message an SCL (Spam Confidence Level) of 5, flagging it for junk delivery. But SCL scoring is a blunt instrument. The Forefront anti-spam headers show category SPM (spam), not phishing. The message would have landed in junk, not been quarantined.
IRONSCALES Adaptive AI classified this incident with 90% confidence based on behavioral and community intelligence signals. Two mailboxes were quarantined. The detection relied on first-time sender analysis, sender/brand mismatch (the From domain servicetechcentre[.]com promoting a brand called "V360"), and community reputation data from similar incidents across the IRONSCALES network of 17,000+ customer environments.
The Verizon DBIR 2024 confirms that pretexting (fabricated scenarios) now accounts for over 40% of social engineering incidents. This case is a textbook example: the attacker built a false business relationship through a fabricated thread, used a legitimate platform for credibility, and deployed reconnaissance tracking to identify which recipients engaged.
Pardot Campaign Infrastructure
| Indicator | Type | Context |
|---|---|---|
servicetechcentre[.]com | Domain | Sender/DKIM domain, registered 2024-05-20 via Cosmotown |
christina@servicetechcentre[.]com | From address | |
bounce-N26EPGSYXE7E7IXOWB5GGQLMGY.130014@bounce[.]s13[.]mc[.]pd25[.]com | Envelope return-path (SFMC bounce handler) | |
128.245.249.5 | IP | ExactTarget MTA (amg5.mta.exacttarget.com) |
hxxp://go[.]pardot[.]com/unsubscribeConfirm/1103432/... | URL | Pardot unsubscribe endpoint |
hxxp://go[.]pardot[.]com/r/1103432/1/1641155776/open/1 | URL | Pardot open tracking pixel |
hxxps://wo27degz[.]emltrk[.]com/v2/wo27degz | URL | CSS-based multi-signal tracking pixel |
wo27degz | Tracking ID | emltrk campaign identifier |
Blocking Marketing Platform Abuse Before the Follow-Up Campaign
Do not trust authentication results as a proxy for sender legitimacy. SPF, DKIM, and DMARC confirm authorization, not intent. Any attacker who provisions a Marketing Cloud account and configures DNS records will pass all three checks. Per CISA guidance on phishing recognition, organizations should layer behavioral detection on top of authentication verification.
Treat marketing automation infrastructure as a potential threat vector. Pardot, HubSpot, Mailchimp, and SendGrid accounts are trivial to provision. Security teams should monitor for first-time senders using known marketing platform relays, especially when the sending domain is recently registered or privacy-shielded.
Block or flag CSS-based tracking techniques. The emltrk[.]com tracking pattern (CSS media queries for dark/light/print/forward detection) is reusable across campaigns. Adding this domain to blocklists disrupts the attacker's reconnaissance loop. Organizations using email security platforms should ensure pixel-stripping extends beyond standard image tags to include CSS-embedded tracking URLs.
Scrutinize "RE:" and "FW:" prefixes on first-time sender messages. A reply or forward from someone who has never emailed your organization before is a strong behavioral signal. Automated detection systems should weight this combination heavily in risk scoring.
Related attacks
| Attack | What happened |
|---|---|
| The Datadog Alert That Came From the Wrong Domain: Authenticated Brand Impersonation With All Links Pointing to Real Infrastructure | A fully authenticated Datadog monitor alert arrived from dtdg.co, not datadoghq.com. |
| Purpose-Built Look-Alike Sending Domain Passes Full Authentication to Impersonate Training Brand | An attacker registered a purpose-built sending domain that mirrors a legitimate training company's naming pattern. |
| The Partner Invite That Used the Wrong Sending Domain | A calendar invite appeared to be from an IRONSCALES employee arranging an ANZ distribution call. |
| The Benefits Handbook That Came With a Marketing Footer: Homoglyph Domain Meets ESP Abuse | An attacker registered a homoglyph domain (zero replacing the letter O), routed an HR benefits announcement through MailerLite. |
| The Trademark Cancellation Notice That Passed Every Authentication Check Because WIPO Actually Sent It | A trademark cancellation notice passed SPF, DKIM, and DMARC for wipo.int because it was genuinely sent from WIPO infrastructure. |
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)