Table of Contents
Most authentication failures produce a binary result. Pass or fail. SPF PermError is neither. When a domain publishes malformed or duplicate SPF records, the evaluating gateway gets an undefined result, and what happens next depends entirely on how that gateway is configured. Some treat PermError as a soft fail. Some treat it as neutral. A few, critically, treat it as a pass.
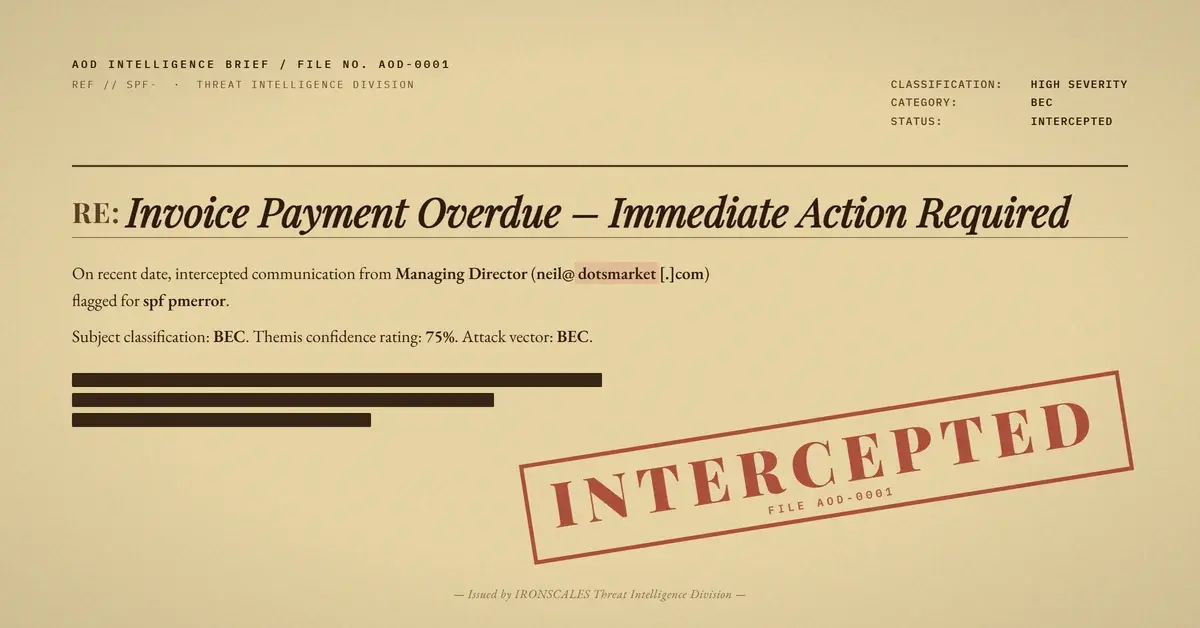
An attacker sending invoice fraud through a domain with a broken SPF record exploited exactly this ambiguity. The email impersonated a managing director at a financial services firm, fabricated a multi-message accounting thread, and demanded same-day payment on an overdue invoice. The Reply-To address pointed to a domain registered less than 24 hours before the attack landed.
Four mailboxes received the message before it was flagged.
A Broken SPF Record as Deliberate Cover
The sending domain, dotsmarket[.]com, has been registered since September 1999. It is not a throwaway. But its DNS configuration contains multiple SPF TXT records, which is an explicit violation of RFC 7208. When an email gateway encounters duplicate SPF records, it cannot determine which one to evaluate and returns a PermError.
PermError is not a fail. That distinction matters. A fail result triggers rejection policies. A PermError triggers... nothing standard. The Verizon 2024 DBIR documents that credential and pretexting attacks now account for the majority of breaches, and authentication edge cases like PermError give attackers a reliable way to avoid the hard rejections that SPF is designed to produce.
In this case, DKIM was present but signed by the relay gateway (oxsus-vadesecure[.]net), not the claimed sending domain. DMARC evaluated against the header From domain (dotsmarket[.]com), found no aligned SPF pass and no aligned DKIM signature, and returned a failure. Composite authentication (compauth) also failed. Microsoft Exchange Online Protection assigned an SCL of 5 and categorized the message as phishing (CAT:PHISH, SFTY:9.25).
The email still reached recipient inboxes.
The Fabricated Thread and Reply-To Trap
The attacker constructed a convincing multi-layer invoice thread. The visible email body opened with an urgent request: "Kindly arrange the payment for this invoice today please, as it is already overdue. Unfortunately, it ended up in my spam folder when it was sent." Below that sat a fabricated forwarded message, formatted to look like a reminder from a senior accounting advisor at a partner firm, complete with invoice metadata.
Invoice Number: 325-08. Invoice Date: November 20, 2025. Due Date: December 13, 2025.
The thread structure implied this was the second or third touch in an ongoing exchange, not a cold request. The fabricated "original" message included a professional signature block with a title, email address, and accounting department attribution. All of it was manufactured.
The From header displayed the name of a real managing director at the target organization, but the actual sending address was neil@dotsmarket[.]com. The Reply-To header pointed to admin@tracdh[.]com. Anyone who replied would send their response directly to the attacker without noticing the domain switch.
See Your Risk: Calculate how many threats your SEG is missing
One-Day-Old Domain, Privacy-Shielded Registration
WHOIS data on tracdh[.]com reveals it was registered on April 16, 2026, through NameSilo with PrivacyGuardian protection. The attack landed on April 17. That is a one-day turnaround from domain registration to delivery, a timeline consistent with BEC campaigns that spin up disposable infrastructure for single-use operations.
The domain uses DNSOwl name servers (ns1.dnsowl[.]com, ns2.dnsowl[.]com, ns3.dnsowl[.]com), a hosting configuration commonly seen with NameSilo bulk registrations. No MX records, no website, no legitimate history. The domain existed solely to receive replies from compromised payment conversations.
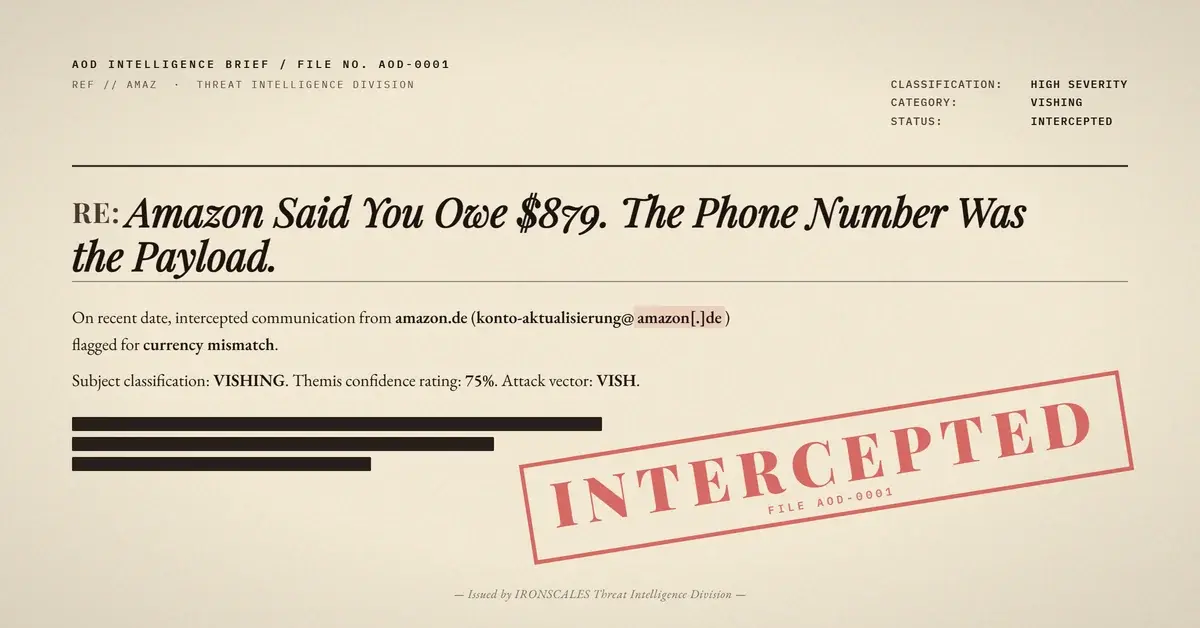
According to the FBI IC3 2024 report, BEC losses exceeded $2.9 billion. Invoice fraud with Reply-To diversion is one of the most common patterns because it requires no malware, no malicious links, and no attachments. The entire payload is social engineering.
How the Impersonation Was Constructed
The attacker chose to impersonate a real managing director at the victim organization. The display name in the From header matched the target employee exactly. IRONSCALES Adaptive AI flagged this as a similar display name impersonation, identifying that the sender name matched a known internal contact.
The email targeted the organization's accounting department directly. Four mailboxes were affected. The impersonation tag "VIP Recipient" was applied, indicating the targeted individuals held roles with financial authorization.
This combination (internal name impersonation, accounting department targeting, same-day payment urgency, fabricated thread history) is the textbook BEC playbook. No links to scan. No attachments to detonate. The only malicious infrastructure is a Reply-To address on a domain that did not exist 48 hours earlier.
MITRE ATT&CK Alignment
| Technique | ID | Application |
|---|---|---|
| Phishing: Spearphishing Link | T1566.002 | Targeted email with Reply-To diversion to attacker domain |
| Impersonation | T1656 | Display name matched real internal managing director |
| Match Legitimate Name or Location | T1036.005 | Fabricated thread mimicked legitimate accounting correspondence |
IOC Summary Table
| Type | Indicator | Context |
|---|---|---|
| Sending Domain | dotsmarket[.]com | From header domain, SPF PermError due to malformed records |
| Sending Email | neil@dotsmarket[.]com | Envelope sender and Return-Path |
| Reply-To Domain | tracdh[.]com | Registered April 16, 2026, privacy-shielded, attacker-controlled |
| Reply-To Email | admin@tracdh[.]com | Diversion target for payment replies |
| Relay IP | 15[.]204[.]3[.]5 | Vade Secure outbound MTA (mta-231b.oxsus-vadesecure[.]net) |
| Gateway Domain | oxsus-vadesecure[.]net | DKIM signing domain (gateway, not sender) |
| Fabricated Contact Domain | hpssspartners[.]com | Used in fake accounting signature block |
| SPF Result | PermError | Invalid/duplicate SPF TXT records on sending domain |
| DMARC Result | Fail | No aligned authentication for header.from |
| CompAuth Result | Fail (reason=001) | Microsoft composite authentication failure |
| SCL | 5 | Microsoft spam confidence level |
| EOP Category | PHISH (SFTY:9.25) | Microsoft Exchange Online Protection classification |
What This Case Demands From Your Stack
SPF PermError is not a theoretical edge case. It is a real authentication gap that DMARC policies alone cannot close when the sending domain publishes broken records. Here is what defenders should prioritize.
Treat PermError as suspicious, not neutral. If your gateway defaults PermError to a neutral or pass-equivalent disposition, you are giving attackers a free lane. Audit your SPF evaluation policies and confirm that PermError triggers at minimum a quarantine action, not delivery.
Flag Reply-To mismatches automatically. The From domain and Reply-To domain in this attack shared zero infrastructure. Any email where the Reply-To domain differs from the From domain, especially when the Reply-To domain is less than 30 days old, should trigger an alert. Domain age checks on Reply-To addresses are underused relative to their signal value.
Detect fabricated threads. The presence of a forwarded message chain with no corresponding inbound history in the recipient's mailbox is a strong behavioral signal. Community threat intelligence across 35,000+ security professionals helps identify these patterns at scale, surfacing invoice fraud campaigns that share structural fingerprints across organizations.
Verify payment requests out of band. No technology replaces a phone call to a known number when someone asks for same-day payment on a six-figure invoice. Build that verification step into your accounts payable process as a policy, not a suggestion.
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)