Table of Contents
Look at this URL and decide in two seconds whether it is safe: reviewdocpdfreader[.]com/docprivatepremiumfile/allfile/adobe.com/. Did your eye catch "adobe.com" and move on? That is exactly what the attacker counted on.
The domain is reviewdocpdfreader[.]com. The directory path contains adobe.com/. The actual destination has nothing to do with Adobe. But the human brain, scanning a link under time pressure, latches onto the familiar brand name and fills in the rest. This is URL path deception, and it is surprisingly effective against both people and automated scanners that weight path content in their reputation scoring.
A Construction Bid That Never Existed
In April 2026, IRONSCALES detected a credential harvesting campaign targeting an employee at a construction materials supplier. The phishing email used a construction bid pretext, referencing a fabricated RFI (Request for Information) number as the hyperlink display text.
This industry targeting is deliberate. Construction companies exchange bid documents, RFIs, and project specifications with unfamiliar external parties as part of normal business operations. A subcontractor the recipient has never emailed before sending a document link is not unusual. It is Tuesday. The Verizon 2024 Data Breach Investigations Report identified manufacturing and construction as increasingly targeted sectors, with phishing as the dominant initial access vector.
The email arrived from a Yahoo account. No corporate domain, no authentication infrastructure beyond Yahoo's default. Microsoft assigned a Spam Confidence Level (SCL) of 5, flagging it as likely spam but not blocking delivery outright. In many organizations, SCL 5 messages land in the junk folder. In organizations with custom transport rules (common in construction firms that receive legitimate external bid communications), they may reach the inbox.
How the URL Tricks Both Eyes and Algorithms
The full URL path tells the story: reviewdocpdfreader[.]com/docprivatepremiumfile/allfile/adobe.com/.
Three deception layers are stacked here. First, the domain name itself (reviewdocpdfreader) contains words associated with legitimate document review. Second, the directory path (docprivatepremiumfile/allfile/) reinforces the "private document" pretext. Third, adobe.com/ sits in the path, visually anchoring the URL to a trusted brand.
This technique exploits a well-documented cognitive bias. When humans scan URLs, they do not parse the domain hierarchy the way a browser does. They scan for recognizable patterns. "adobe.com" anywhere in a URL registers as "Adobe" to a reader who is not pausing to identify where the actual domain ends and the path begins. The Microsoft Digital Defense Report 2024 notes that URL obfuscation techniques, including path-based brand embedding, have increased as defenders have improved detection of lookalike domains and homoglyph attacks.
The display text compounded the deception. Rather than showing the full URL, the hyperlink text displayed what appeared to be an RFI reference number. The recipient would see a plausible document identifier, not the suspicious URL behind it. Hovering over the link would reveal the full path, but in practice, hover-to-inspect rates are low, particularly on mobile devices. According to Osterman Research, more than 60% of business email is now read on mobile, where URL preview behavior varies by client and is frequently truncated.
See Your Risk: Calculate how many threats your SEG is missing
The Infrastructure Behind the Deception
The attacker registered reviewdocpdfreader[.]com in November 2025, five months before this campaign. That registration timeline is notable. Many phishing campaigns use domains registered hours or days before an attack, making domain age a useful (if imperfect) detection signal. A five-month-old domain bypasses age-based heuristics that flag newly registered infrastructure.
DNS resolution routed through Cloudflare, giving the domain valid SSL certificates, DDoS protection, and CDN-level performance. Cloudflare's infrastructure is used by millions of legitimate websites. The presence of Cloudflare in the resolution chain adds no reputational signal in either direction, which is precisely why attackers choose it. The FBI IC3 2024 Annual Report documented a continued rise in phishing infrastructure hosted behind legitimate CDN and cloud providers, complicating IP-based and domain-based blocklist approaches.
The Yahoo sender account provided minimal authentication. Yahoo's outbound infrastructure handles SPF and DKIM for its own domain, but the email carried no organizational authentication signals. Combined with the SCL 5 score, the message sat in a gray zone: suspicious enough to flag, not definitive enough to block. That gray zone is where the most effective phishing campaigns operate.
MITRE ATT&CK Mapping
This attack maps to several MITRE ATT&CK techniques:
- T1566.002 (Phishing: Spearphishing Link): The email contained a malicious link to an external credential harvesting page.
- T1036.005 (Masquerading: Match Legitimate Name or Location): The URL path embedded "adobe.com" to impersonate a trusted brand.
- T1608.005 (Stage Capabilities: Link Target): The attacker pre-staged a credential harvesting page on a dedicated domain with Cloudflare infrastructure.
Indicators of Compromise
| Type | Indicator | Context |
|---|---|---|
| Phishing Domain | reviewdocpdfreader[.]com | Attacker-controlled credential harvest host |
| URL Path | /docprivatepremiumfile/allfile/adobe.com/ | Brand embedding in path for visual deception |
| DNS Provider | Cloudflare | Infrastructure routing |
| Domain Registration | November 2025 | Five months pre-campaign |
| Sender Platform | Yahoo | Free email, minimal authentication |
| SCL Score | 5 | Microsoft spam confidence (flagged, not blocked) |
| Display Text | Fabricated RFI number | Hid malicious URL behind document reference |
Where the Domain Ends and the Lie Begins
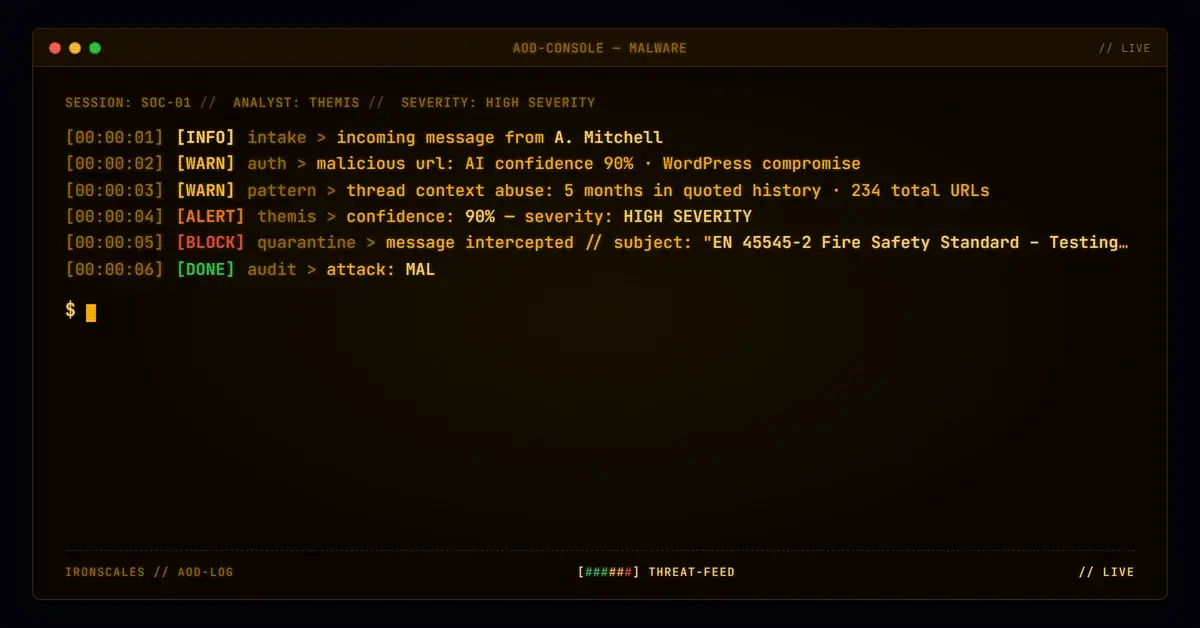
Themis flagged this message based on link structural analysis, identifying the mismatch between the display text, the actual destination domain, and the brand reference embedded in the path. The IRONSCALES Adaptive AI evaluates URL structure beyond simple reputation lookups, parsing the relationship between the displayed link text, the true hosting domain, and any trust signals embedded in the path or parameters.
Domain reputation and URL scanning remain necessary components of email security. But they are not sufficient when the attacker's entire strategy is designed to manipulate how those systems (and humans) evaluate links. The IBM Cost of a Data Breach 2024 report found that phishing-initiated breaches cost an average of $4.88 million, and the time to detect phishing-based intrusions continues to lengthen as evasion techniques improve.
The fix is not more blocklists. It is structural link analysis that understands the difference between where a URL appears to go and where it actually goes. If "adobe.com" appears in the path rather than the domain, that is not Adobe. That is the attacker betting you will not notice the difference.
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)