Table of Contents
A 14-Day-Old Domain Passed Every Authentication Check Because Zoho Vouched for It
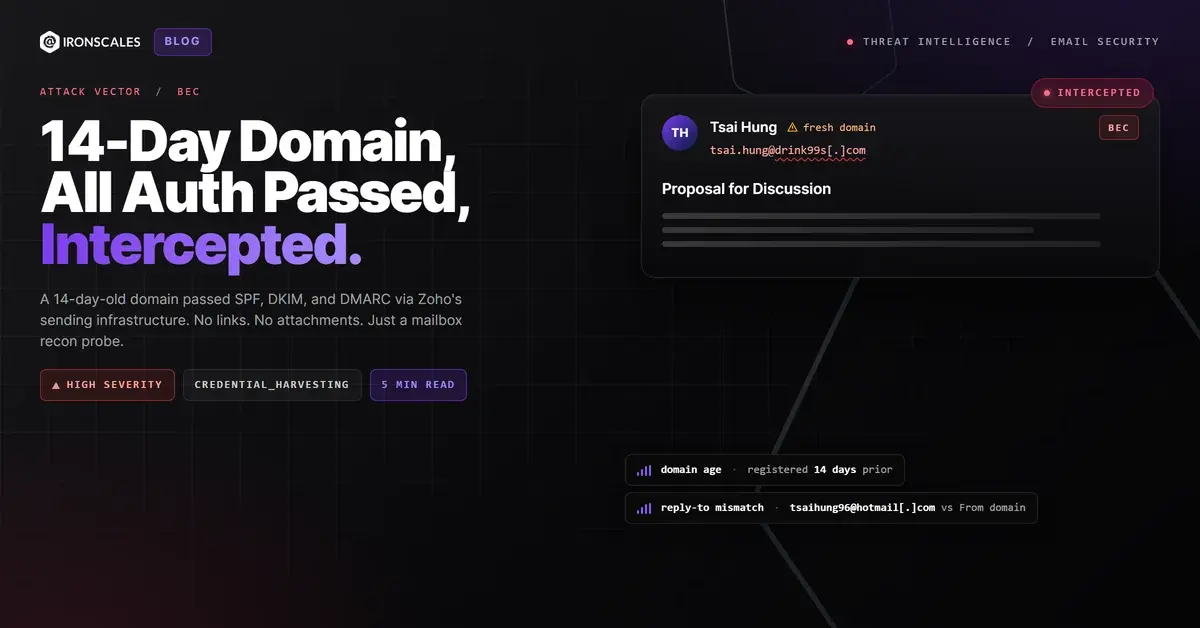
On April 1, 2026, an email with the subject line "Proposal for Discussion" landed in a corporate inbox at a North American professional services firm. SPF passed. DKIM passed. DMARC returned bestguesspass. ARC validation cleared.
The sending domain, drink99s.com, had existed for exactly 14 days.
There were no links in the email. No attachments. No brand impersonation. No urgency. Just four sentences asking to schedule a meeting, signed "Tsai Hung." By every traditional gateway metric, this message looked like a routine cold outreach from a legitimate sender.
It was a reconnaissance probe, and the authentication stack was the weapon.
How a Disposable Domain Became a Trusted Sender in Minutes
The attacker registered drink99s.com on March 18, 2026, through Regery.com (DevExpanse Ltd), a low-cost registrar. WHOIS records show privacy-shielded registration data with a registrant state of Wando-Gun, South Korea. The domain was configured with Google Cloud DNS (ns-cloud-a1.googledomains.com through a4).
Within that same registration window, the attacker connected the domain to Zoho's ZeptoMail transactional email service. ZeptoMail is designed for application-triggered emails: order confirmations, password resets, notification alerts. It provides authenticated sending infrastructure out of the box. When you verify a domain with ZeptoMail, Zoho publishes the necessary SPF and DKIM records automatically.
That is all it takes. Register a domain for under $10. Point it at a reputable ESP. Let the ESP handle authentication. The result: a domain that passes every check any secure email gateway will run.
The relay chain confirms it. The email originated from sender4-g6-187.zohomail360.com (IP 136.143.188.187), traversed mx.zohomail.com, and arrived at Microsoft 365's protection.outlook.com edge. The Return-Path used Zoho's bounce infrastructure: bounce-zem.drink99s.com. The DKIM signature was valid, signed with selector 121419 under drink99s.com. Every hop was real. Every signature checked out.
According to the FBI's 2024 Internet Crime Report, business email compromise accounted for $2.9 billion in reported losses. The attacks that generate those numbers rarely start with a malicious link. They start with emails exactly like this one.
The Reply-To Header Was the Only Crack in the Armor
The From address read tsai.hung@drink99s[.]com. Authenticated. Aligned. Clean.
The Reply-To header pointed somewhere else entirely: tsaihung96@hotmail[.]com.
This is the ESP abuse pattern in its purest form. The attacker builds a sender identity on disposable infrastructure (drink99s.com via Zoho), but routes all responses to a free webmail account they actually monitor. If the recipient replies to the meeting request, the conversation moves to Hotmail, completely disconnected from the authenticated domain.
Microsoft's own filters noticed. The email received an SCL score of 5 and was flagged as SPM (spam) in the X-Forefront-Antispam-Report header. It landed in Junk. But SCL 5 is the threshold edge. A slightly different phrasing, a corporate signature block, or a warm-up period on the domain could have tipped it into the inbox.
The Microsoft Digital Defense Report 2024 notes that threat actors increasingly abuse legitimate cloud services to bypass reputation-based detection. Zoho is not malicious infrastructure. It is a trusted ESP that millions of businesses use daily. That trust is precisely what makes it valuable to attackers.
See Your Risk: Calculate how many threats your SEG is missing
Zero Payload Is the Point
This email contained no links, no attachments, and no call to action beyond "let me know if you are available." That is not a failed attack. That is a successful reconnaissance operation.
Zero-payload emails serve three purposes. First, they validate that the target mailbox is active and monitored. A bounce means the address is dead. Silence means it might be filtered. A reply confirms a live human reading their inbox. Second, they test the target organization's detection posture. If a newly registered domain sending through a known ESP lands in the inbox (not Junk), the attacker knows the path is clear for the follow-up. Third, they establish sender history. Even landing in Junk creates a record. The next email from the same domain or a related one benefits from that prior delivery.
The Verizon 2024 Data Breach Investigations Report found that pretexting (which includes reconnaissance-stage social engineering) was involved in 25% of breaches. The initial contact often looks nothing like the attack that follows.
IRONSCALES Themis AI flagged this email with a phishing classification, noting the newly registered return path domain as a primary indicator. The recipient was tagged as a VIP, which triggered elevated scrutiny. Even with a modest 56% confidence score (expected for a zero-payload email with no overt malicious indicators), the combination of new domain plus Reply-To mismatch plus ESP-mediated authentication was enough to surface the threat. Traditional gateways that rely on link scanning, attachment sandboxing, or content-based heuristics had nothing to analyze. The IRONSCALES platform detected what was suspicious about the sender, not the content.
What Defenders Should Check Tomorrow Morning
This attack pattern, registering disposable domains on legitimate ESPs to achieve authenticated delivery, is scalable and cheap. The domain cost under $10. ZeptoMail's free tier allows 10,000 emails per month. The attacker can burn the domain after a single campaign and register another one tomorrow.
Defenders should audit Reply-To mismatches against authenticated From domains, especially when the Reply-To points to free webmail providers. Monitor for inbound email from domains less than 30 days old, regardless of authentication status. The MITRE ATT&CK framework classifies this under T1583.001 (Acquire Infrastructure: Domains) and T1598.003 (Phishing for Information: Spearphishing Link), reflecting the reconnaissance intent behind the infrastructure investment.
Domain age alone is not a silver bullet (legitimate businesses register new domains constantly), but domain age combined with ESP bounce infrastructure, Reply-To divergence, and zero-payload content creates a signal profile that deserves automatic escalation. If your security stack cannot correlate those signals, you are relying on the attacker to make a mistake. This one did not.
Indicators of Compromise
| Type | Indicator | Context |
|---|---|---|
| Domain | drink99s[.]com | Sending domain, registered 2026-03-18 |
| Domain | bounce-zem[.]drink99s[.]com | Return-Path / bounce subdomain (Zoho ZeptoMail) |
| tsai[.]hung@drink99s[.]com | From address | |
| tsaihung96@hotmail[.]com | Reply-To address (free webmail callback) | |
| IP | 136[.]143[.]188[.]187 | Sending IP (sender4-g6-187.zohomail360.com, Zoho infrastructure) |
| Registrar | Regery[.]com (DevExpanse Ltd) | Domain registrar, privacy-shielded, registrant state Wando-Gun, KR |
| DNS | ns-cloud-a1[.]googledomains[.]com | Google Cloud DNS nameservers |
| Header | X-MS-Exchange-Organization-SCL: 5 | Microsoft spam confidence level (threshold edge) |
| Header | SFV:SPM | Microsoft anti-spam verdict: spam |
Related attacks
| Attack | What happened |
|---|---|
| The Zoho Invoice That Was Four Months Late (And Kept Its Receipts on Google Drive) | A Zoho Books invoice for $802.50 arrived four months past due, passed initial authentication checks. |
| Mimecast SafeLinks Phishing: Wrapped URLs Hide Lookalike Domains | Attackers routed a credential-harvesting link through Mimecast SafeLinks so the recipient saw a Mimecast-rewritten URL. |
| The Graduation Sash Invoice That Every Security Check Approved | A $3,645 invoice for 55 custom graduation sashes arrived at a school district, sent through Shopify's legitimate email infrastructure. |
| The Audit Request That Passed Every Authentication Check: How a Compromised Nonprofit Account Weaponized URL Shorteners | A phishing campaign hijacked a legitimate nonprofit email account to send fraudulent audit requests with malicious URL shortener links. |
| When the Sender Domain Is Also the Phishing Kit Host: Dual-Purpose Domain Compromise | An attacker compromised a legitimate manufacturing company domain and used it two ways at once: as the authenticated sending address and as the host for... |
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)