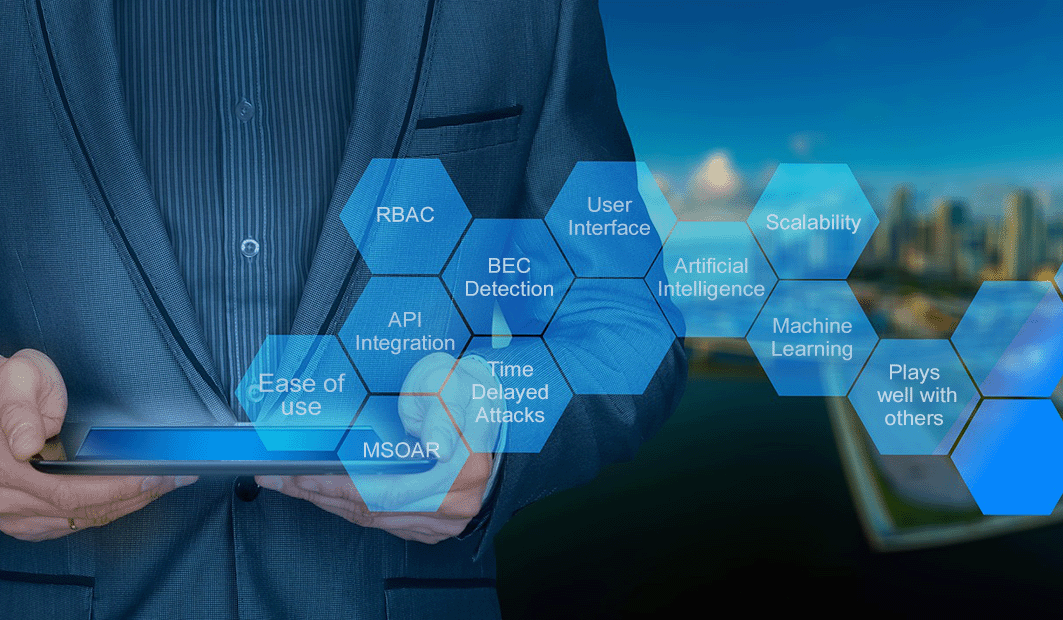
IRONSCALES Winter '26 Release: Preemptive Email Security
/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)
A few months ago, I wrote about the Phishing Renaissance and how AI hasn't invented new attack types so much as perfected the classics. Credential theft, vendor impersonation, executive fraud. Same...
Read more
/Concentrix%20Case%20Study.webp?width=568&height=326&name=Concentrix%20Case%20Study.webp)


















.jpeg)