Table of Contents
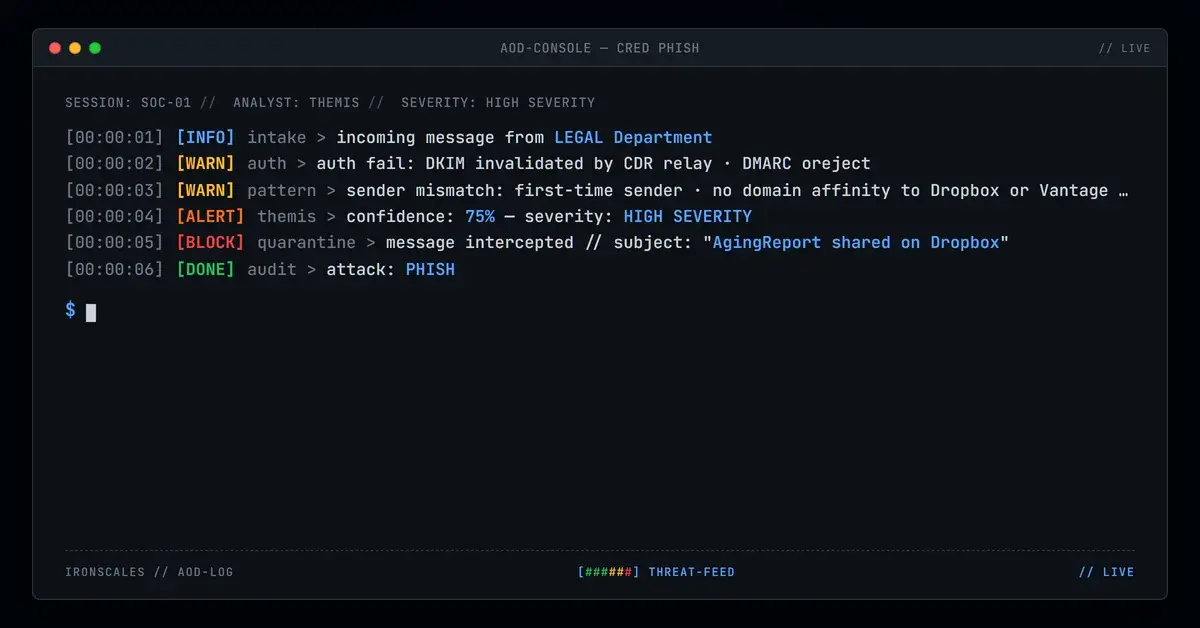
The email said "LEGAL Department (vantagebank[.]com)" shared an "AgingReport" on Dropbox. The From address was legal@smleather[.]com. The link went to neither domain. And the inline security tool that was supposed to protect the recipient destroyed the only authentication signal that would have caught it.
This credential harvesting campaign exploited a gap that most security stacks never account for: what happens when your own Content Disarm and Reconstruction (CDR) tool breaks email authentication in transit.
Authentication That Passed, Then Failed
At the Amazon SES sending hop (IP 54[.]240[.]48[.]119), the message had clean authentication. SPF passed for smleather[.]com. DKIM passed with a valid signature tied to the same domain. DMARC passed.
Then the message hit the Votiro CDR relay at votiro-relay1[.]prod[.]votiro[.]com (IP 44[.]206[.]213[.]130). Votiro sanitized the content, modifying the message body in transit. That modification invalidated the DKIM signature. With DKIM broken, DMARC re-evaluated and failed, returning an action=oreject disposition. SPF also failed at the next hop because the Votiro relay IP was not authorized for the original sender domain.
The CDR tool did its job on the content. In the process, it stripped the authentication markers that downstream filters use to make trust decisions.
A Redirect Chain Built on Trusted Infrastructure
The "View on Dropbox" CTA did not link to Dropbox. It routed through awstrack[.]me, Amazon's legitimate SES click-tracking service, before landing on dropbox[.]traunitz[.]com. That is a classic brand subdomain impersonation pattern: placing "dropbox" as a subdomain on an attacker-controlled domain, fronted by Cloudflare.
At scan time, the landing page returned a 404. This is consistent with time-gated credential harvesting pages that activate only for targeted recipients, then disappear.
The Behavioral Signal That Survived
With authentication destroyed by the CDR relay, the only remaining detection surface was behavioral. The sender domain (smleather[.]com) had no relationship to the claimed brand (Dropbox) or the referenced organization (vantagebank[.]com). The sender was contacting the recipient for the first time.
Adaptive AI identified the sender-content mismatch and first-time sender signal, flagging the message despite the ambiguous authentication results.
See Your Risk: Calculate how many threats your SEG is missing
Indicators of Compromise
| Type | Indicator | Context |
|---|---|---|
| Sender Email | legal@smleather[.]com | Sender address, Amazon SES origin |
| Sending IP | 54[.]240[.]48[.]119 | Amazon SES infrastructure |
| CDR Relay | votiro-relay1[.]prod[.]votiro[.]com | Votiro CDR that broke authentication |
| CDR Relay IP | 44[.]206[.]213[.]130 | Votiro relay IP |
| Redirect | awstrack[.]me | Amazon SES click-tracking redirect |
| Credential Harvest | dropbox[.]traunitz[.]com | Brand subdomain, Cloudflare-fronted |
MITRE ATT&CK Mapping
| Technique | ID | Relevance |
|---|---|---|
| Phishing: Spearphishing Link | T1566.002 | Delivery via embedded redirect chain |
| Masquerading | T1036.005 | Dropbox brand impersonation |
| Acquire Infrastructure: Domains | T1583.001 | Brand subdomain registration |
Related attacks
| Attack | What happened |
|---|---|
| The Subdomain That Fused Two Trusted Brands Into One Convincing Lie | Attackers fused two real brand names into a single subdomain, routed the message through Zix infrastructure to inherit enterprise authentication. |
| The Email That Passed Every Security Check (Because Adobe Sent It) | A phishing campaign targeting school district staff used Adobe's own sending infrastructure, real DKIM signatures. |
| The Funding Approval That Passed Every Authentication Check | A typosquatted lending domain with one extra letter was registered as a Salesforce Marketing Cloud sending identity. |
| When the Sender Domain Is Also the Phishing Kit Host: Dual-Purpose Domain Compromise | An attacker compromised a legitimate manufacturing company domain and used it two ways at once: as the authenticated sending address and as the host for... |
| Two Security Vendors Scanned This Link and Both Said Clean | Attackers chained TitanHQ and Cisco link wrappers on the same malicious URL so each vendor scanned the other's wrapper and returned Clean. |
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)