Table of Contents
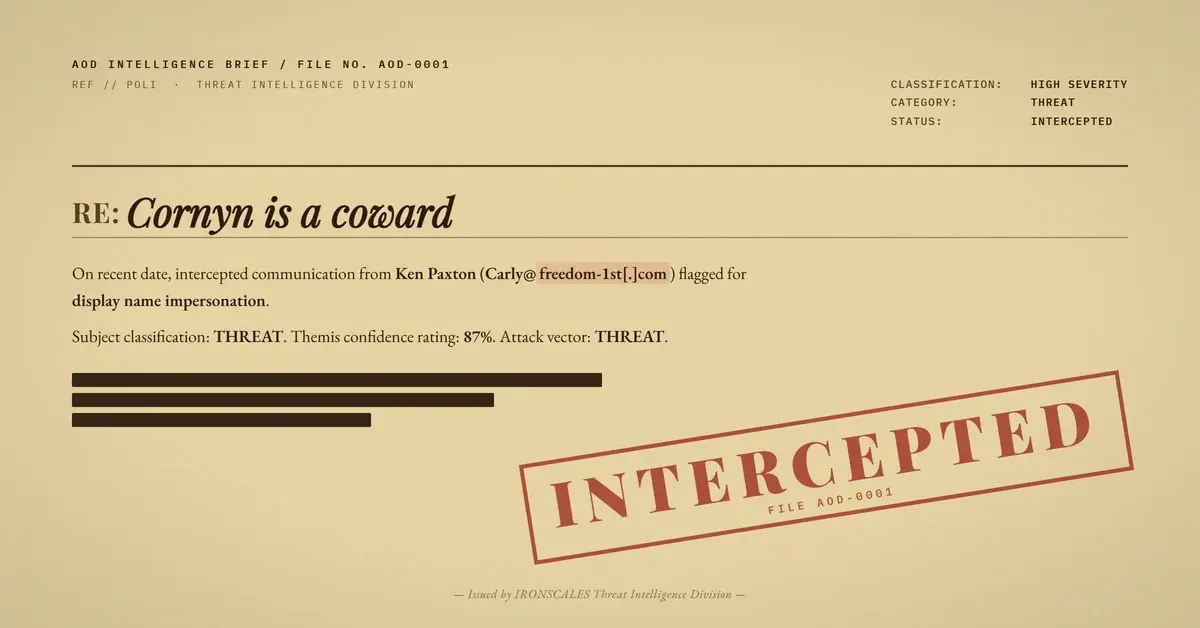
SPF passed. DKIM passed. DMARC passed. Composite authentication scored a perfect 100. And the email was a fraudulent donation solicitation impersonating a state attorney general.
This case is a clean example of why email authentication protocols alone cannot stop impersonation. The attacker registered a fresh domain, configured a legitimate email marketing platform to handle delivery, and exploited the gap between "authenticated sender" and "trusted sender" to solicit money from employees at a mid-market professional services firm.
The email hit four mailboxes. Every one was quarantined, not because authentication failed, but because behavioral and community signals flagged what protocol checks could not.
Fresh Domain, Full Authentication, Zero Friction
The attack began with domain registration. On July 23, 2025, someone registered freedom-1st[.]com through GoDaddy with full WHOIS privacy protection. DNSSEC was left unsigned. The domain sat for roughly eight months before being weaponized.
The attacker then connected the domain to EmailOctopus, a legitimate email marketing platform that routes sends through SparkPost infrastructure. This gave the campaign three things for free: SPF alignment via eom.freedom-1st[.]com, a valid DKIM signature with selector eo and header.d=freedom-1st[.]com, and a DMARC policy that passed with action=none. The Return-Path used a VERP-encoded bounce address (msprvs1=20549db1AH1yo=bounces-1873-57986@eom.freedom-1st[.]com) consistent with standard ESP campaign sends.
From a protocol perspective, this email was indistinguishable from a legitimate marketing campaign.
The Impersonation: A Public Figure's Name, Someone Else's Mailbox
The From header read "Ken Paxton" . The display name matched a sitting state attorney general. The actual sending address belonged to someone (or something) named "Carly" on the attacker-controlled domain.
This is display-name impersonation at its most effective. Most email clients render the display name prominently and tuck the address behind a click or hover. A recipient scanning their inbox sees a recognizable public figure's name, not an unfamiliar domain.
The IRONSCALES platform had previously seen the same display name associated with a different sender address (news@magacitizen[.]com), triggering an exact display-name impersonation detection. That prior association was the first behavioral signal that something was wrong.
Political Urgency as Social Engineering Fuel
The subject line, "Cornyn is a coward," was designed to provoke an emotional reaction. The body doubled down with politically charged language attacking a sitting U.S. senator, framing the solicitation as urgent support for a rival campaign. The call-to-action button ("RUSH SUPPORT HERE >>") pushed recipients toward a donation page on secure.winred[.]com, a legitimate political fundraising processor.
This is where the attack gets clever. Every link in the email resolved to either the attacker's tracking infrastructure (eot.freedom-1st[.]com redirects, berrima.eomail8[.]com tracking pixels) or to a real donation platform. Automated URL scanners returned clean verdicts across the board. The WinRed page itself appeared functional. There was nothing technically malicious about the destination. The fraud was entirely in the false identity behind the solicitation.
The email also included standard ESP footers: an unsubscribe link, an EmailOctopus "Powered by" badge, and a "Paid for by" disclosure with a mailing address. These elements added a veneer of compliance that could trick both automated systems and human recipients into treating the message as legitimate political outreach.
See Your Risk: Calculate how many threats your SEG is missing
What the Headers Revealed
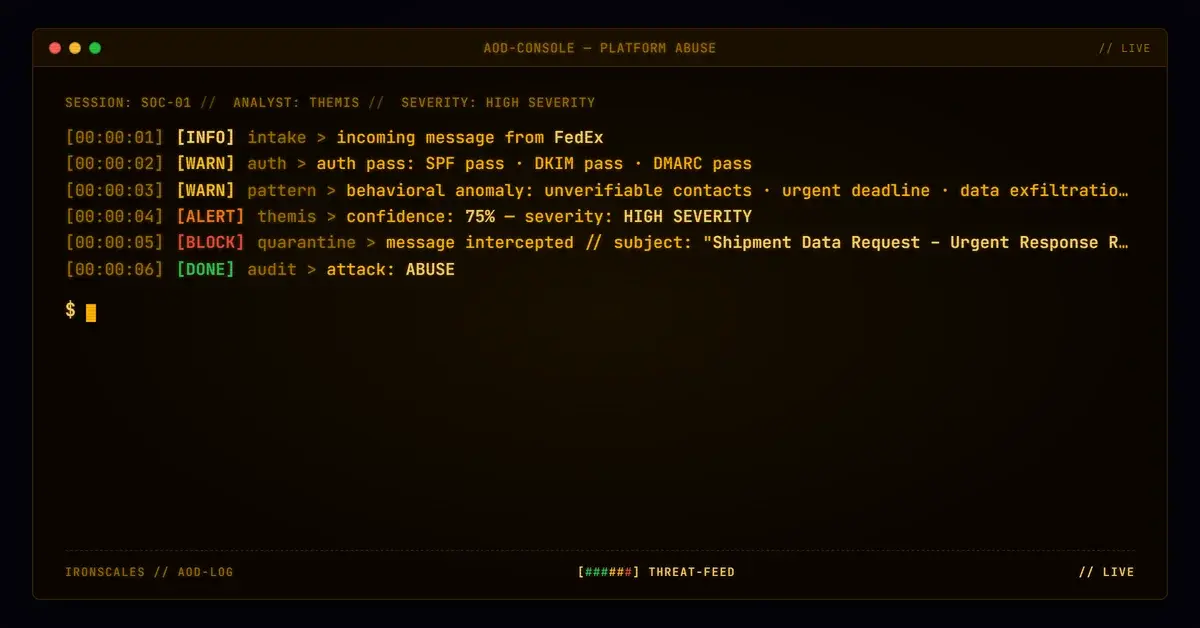
Microsoft's own anti-spam stack was not fooled. The X-MS-Exchange-Organization-SCL value was 9 (the highest spam confidence level). The X-Forefront-Antispam-Report flagged the message as HSPM (high-confidence spam) with SFTY:9.25, a safety score indicating phishing characteristics. The Bulk Complaint Level hit 7. Despite clean authentication, the email was routed to quarantine via SFV:SPM.
The relay chain confirmed the delivery path: SparkPost's mta-253-220-155.emailoctopus[.]com[.]sparkpostmail[.]com (IP 147[.]253[.]220[.]155, geolocated to the UK) handed the message to Microsoft's Exchange Online Protection frontend, which processed it through standard filtering before delivery to the target tenant.
Community threat intelligence provided additional confidence. Similar incidents from the same sender fingerprint had been resolved as phishing across the IRONSCALES network, giving our Adaptive AI an 87% confidence score before any human analyst reviewed the case.
The Technique Chain Behind Authenticated Impersonation
| Technique | ID | Application |
|---|---|---|
| Phishing: Spearphishing Link | T1566.001 | Email with embedded donation link targeting specific recipients |
| Masquerading: Match Legitimate Name | T1036.005 | Display name set to a state attorney general |
| Acquire Infrastructure: Domains | T1583.001 | Privacy-shielded domain registered 8 months prior to campaign |
| Establish Accounts: Email Accounts | T1585.002 | EmailOctopus account configured with full authentication for attacker domain |
Attacker Infrastructure and IOCs
| Type | Indicator | Context |
|---|---|---|
| Domain | freedom-1st[.]com | Attacker-registered sending domain (GoDaddy, 2025-07-23, WHOIS privacy) |
| Domain | eom.freedom-1st[.]com | SPF envelope/Return-Path subdomain |
| Domain | eot.freedom-1st[.]com | Click-tracking redirect subdomain |
Carly@freedom-1st[.]com | From address (display name impersonated a state attorney general) | |
| Domain | berrima.eomail8[.]com | EmailOctopus tracking/unsubscribe infrastructure |
| IP | 147[.]253[.]220[.]155 | Sending MTA (SparkPost, UK-geolocated) |
| URL | hxxps://secure[.]winred[.]com/ken-paxton-for-senate/pg_rs-e_1183-bmd-cornyn-is-a-coward-83p_20260326_a | Donation page (legitimate platform, potentially fraudulent campaign) |
| URL | hxxps://eot[.]freedom-1st[.]com/f/a/YcyINyKc51w3wwaeJ0lwsQ~~/ | Click-tracking redirect |
| Header | X-EmailOctopus-Team-Id: 9dbec888-8927-11f0-b621-25f7ebdda224 | ESP team identifier |
| Header | X-EmailOctopus-List-Id: 9dc5c5c0-8927-11f0-9f9a-25f7ebdda224 | ESP mailing list identifier |
| DKIM Selector | eo | DKIM selector for freedom-1st[.]com (EmailOctopus default) |
Why Authentication Alone Will Never Be Enough
This case is a textbook illustration of a gap the FBI IC3 2024 report keeps quantifying: BEC and impersonation-driven fraud cost organizations $2.9 billion in reported losses last year. The Verizon DBIR 2024 found that pretexting (which includes impersonation for financial gain) now accounts for over 40% of social engineering incidents. And the Microsoft Digital Defense Report 2024 explicitly warns that threat actors are increasingly weaponizing legitimate cloud services for delivery.
DMARC, SPF, and DKIM answer one question: "Did this email come from the domain it claims?" They do not answer: "Is the person named in the display name actually the sender?" When attackers register their own domain and configure authentication correctly, every protocol check passes by design.
Defending against this pattern requires:
- Display-name correlation. Track display names against known sender addresses. When "Ken Paxton" appears from a new domain, that mismatch should trigger inspection, exactly as it did here.
- Domain age and WHOIS analysis. A privacy-shielded domain less than a year old sending political solicitations to a professional services firm is anomalous. Weight that signal.
- Community intelligence. Across IRONSCALES data from 35,000+ security professionals, similar messages from the same sender fingerprint had already been classified as phishing. Sharing verdicts across organizations catches campaigns that any single tenant might miss.
- ESP header inspection. The
X-EmailOctopus-*headers, campaign IDs, and VERP-encoded bounce paths provide forensic markers. Organizations can build detection rules around ESP metadata patterns that correlate with known-bad campaigns. - User reporting. Per CISA guidance, even technically clean emails warrant scrutiny when they solicit money under a public figure's name. Empower users to flag. The FTC's Consumer Sentinel data shows impersonation of government officials is a top fraud vector.
Authentication is necessary. It is not sufficient. When every protocol check says "pass" and the email is still a scam, the only remaining defense is understanding who is really writing to you and why.
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)