Table of Contents
Read the body of this email without looking at the links and it sounds like any other workplace message. A staff member at a social services nonprofit asking a colleague about saving uploaded items, specifically GL accounts, licenses, and leases. Routine operational housekeeping. No urgency language. No unusual requests. No call to action beyond a casual question.
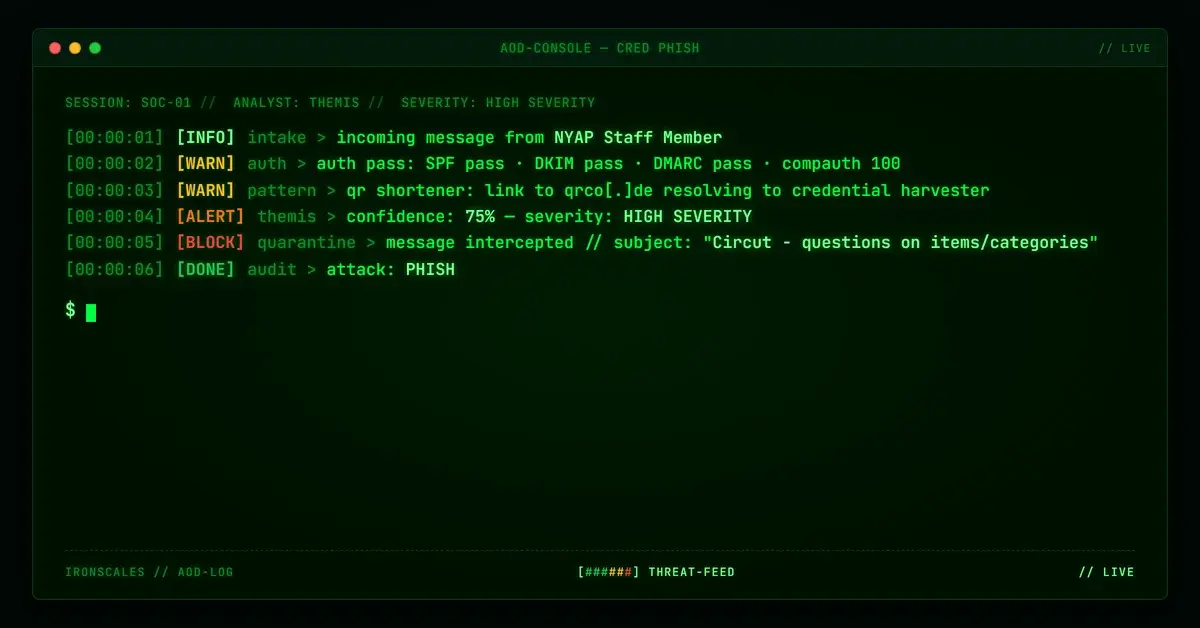
SPF passed. DKIM passed. DMARC passed. Composite authentication returned a perfect 100. ARC validated cleanly. The sender domain has been registered since 1998. The DKIM signature verified against the organization's own domain.
Every signal a Secure Email Gateway evaluates said this email was trustworthy. The single malicious element was a shortened URL from qrco[.]de, a QR code and link shortener service, sitting quietly in the message body. That link was the entire attack.
A Perfect Authentication Score from a Compromised Account
The email was sent from [user]@nyap[.]org, a domain belonging to a national youth advocacy nonprofit organization. The domain has been registered since 1998, predating the commercial internet era for most organizations. It runs Microsoft 365 for email with properly configured authentication records.
The authentication results at the recipient's environment were flawless:
- SPF: Pass (sending IP authorized)
- DKIM: Pass (d=nyap[.]org, signature verified)
- DMARC: Pass (policy alignment confirmed)
- Composite Authentication: 100 (compauth=pass, reason=100)
- ARC: Pass (chain of custody intact)
This is what compromised-account phishing looks like. The attacker did not need to register a lookalike domain, configure an ESP, or build a relay chain. They gained access to a legitimate account on a legitimate domain with legitimate authentication, and sent a single email that inherited every trust signal the organization's mail infrastructure could provide.
According to the Microsoft Digital Defense Report 2024, compromised legitimate accounts are among the most effective delivery mechanisms for phishing precisely because they eliminate the authentication signals that filtering stacks rely on. When the account is real, the authentication is real. The only thing that is not real is the intent.
The Body Was the Disguise. The Link Was the Weapon
The email subject, "Circut - questions on items/categories," referenced an internal system. The body asked about saving uploaded items to a platform, mentioning GL accounts, licenses, and leases by name. An attached organizational logo image (41 KB, scanned clean) reinforced the organizational context. Nothing in the text or the attachment raised a flag.
The sole malicious element was a link to qrco[.]de/bdOyYY. The qrco[.]de domain is a legitimate QR code generation and URL shortening service. It is not inherently malicious. It is, however, one of the most commonly abused shortener services in quishing campaigns because it provides both QR code generation and URL redirection in a single service, and its domain reputation is clean.
The FBI IC3 2024 Internet Crime Report documented phishing as the highest-volume cybercrime category, with losses exceeding $9.3 billion. QR-based phishing has emerged as a growing subset of that volume because it exploits a gap in how most email security tools analyze URLs. A shortener link is one hop removed from the actual destination, and many scanners evaluate only the immediate URL rather than following the redirect chain to the landing page.
The Landing Page That Wore the Sender's Own Brand
The qrco[.]de shortened link resolved to a landing page hosted on AWS CloudFront and S3 infrastructure. The page was designed to look like an official portal for the same nonprofit organization whose account was compromised. the nonprofit's own branding, a "Connect with us on social media" header, and organizational styling created a consistent visual thread from the email to the landing page.
This is a deliberate design choice by the attacker. When the sending domain is legitimate, the email is authentic-looking, and the landing page matches the same organization's branding, the entire chain feels internally consistent. A recipient following the link sees exactly what they would expect to see: their own organization's portal. The credential harvesting form sits inside that trusted wrapper.
Hosting the page on CloudFront and S3 adds a second layer of infrastructure trust. AWS domains carry clean reputation scores across virtually every URL scanning service. The Verizon 2024 Data Breach Investigations Report documented the increasing abuse of legitimate cloud infrastructure for phishing delivery, noting that trusted hosting platforms have become a preferred evasion technique because domain reputation checks give them a pass by default.
See Your Risk: Calculate how many threats your SEG is missing
Microsoft Caught It. After Delivery
Microsoft's anti-spam classifier assigned this message a CAT:HPHISH verdict (high-confidence phishing) with an SFV:SKQ flag, indicating the message was released from quarantine at some point in its lifecycle. The HPHISH classification is Microsoft's strongest phishing signal, reserved for messages that its classifiers determine are phishing with high confidence.
The timing matters. The message was initially delivered, then reclassified. This post-delivery detection pattern is common with quishing attacks because the malicious signal (the shortened URL's final destination) requires redirect chain analysis that may not complete before the message reaches the inbox. Microsoft's classifier caught it, but not before the email was available to the recipient.
This is the quishing detection gap in practice. The email body contains nothing malicious. The authentication stack sees a verified sender. The attachment is a clean logo image. The only threat indicator is a shortened URL that resolves, through a redirect, to a credential harvesting page on trusted cloud infrastructure. Each component in isolation scans clean. The attack lives in the relationship between them.
What Behavioral Detection Caught First
Themis flagged this message at 90% confidence. The detection was based on the behavioral fingerprint: a shortened URL from a known quishing-abuse service embedded in an otherwise routine message, combined with anomalous link patterns for the sender's historical communication behavior. The system reverted the single affected mailbox automatically.
The distinction between Themis's detection and the HPHISH classification is the detection surface. Microsoft's classifier eventually reached the correct verdict through content and URL analysis. Themis reached it through behavioral signals, the presence of a QR shortener link in a message type where such links have no legitimate purpose, evaluated against the sender's established communication patterns within the recipient's organization.
For security teams, this case illustrates why quishing defense cannot rely solely on URL scanning or post-delivery reclassification. The window between initial delivery and post-delivery quarantine is the window in which an employee clicks the link. Closing that window requires pre-delivery behavioral analysis that evaluates the link in context, not in isolation.
Indicators of Compromise
| Type | Indicator | Context |
|---|---|---|
| Sender Domain | nyap[.]org | Legitimate nonprofit, registered 1998, likely compromised account |
| Sender Address | [user]@nyap[.]org | Display name redacted |
| Malicious URL | qrco[.]de/bdOyYY | QR code shortener, flagged MALICIOUS |
| Landing Infrastructure | CloudFront / S3 | AWS-hosted credential harvesting page with NYAP branding |
| Attachment | image001.jpg (41 KB) | NYAP logo, scanned clean |
| SPF | Pass | Authorized sending IP |
| DKIM | Pass | d=nyap[.]org, signature verified |
| DMARC | Pass | Full policy alignment |
| Composite Auth | 100 | compauth=pass, reason=100 |
| Microsoft Verdict | CAT:HPHISH, SFV:SKQ | High-confidence phishing, released from quarantine |
MITRE ATT&CK Mapping: - T1566.002: Phishing, Spearphishing Link (shortened URL delivery in email body) - T1036.005: Masquerading, Match Legitimate Name or Location (landing page impersonating sender organization's branding) - T1586.002: Compromise Accounts, Email Accounts (legitimate nonprofit account used for phishing delivery)
Related attacks
| Attack | What happened |
|---|---|
| The QR Code That Knew Your Email Address Before You Scanned It | A phishing PDF embeds a QR code with the recipient's email pre-encoded in base64. |
| Sign Here, Get Phished: Inside an Adobe Sign Lure With a Multi-Hop Redirect to Credential Theft | An Adobe Sign e-signature lure routed recipients through a multi-hop redirect chain ending at fameklinik[.]com. |
| When the Safety Wrapper Becomes the Disguise: Brazilian NF-e Phishing via Safe Links Rewrite | A Portuguese-language invoice lure authenticated through a compromised Brazilian domain used is.gd to hide its payload. |
| The Email That Shipped With Its Template Tokens Still In It (And Still Worked) | An attacker's mail merge failed. |
| DocuSign Plus Invoice: A 12-Day-Old Domain and an esvalabs Redirect Chain That Scanners Missed | A phishing campaign combined DocuSign branding with an invoice thread pretext, sent from a 12-day-old privacy-protected domain via Amazon SES. |
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)