Table of Contents
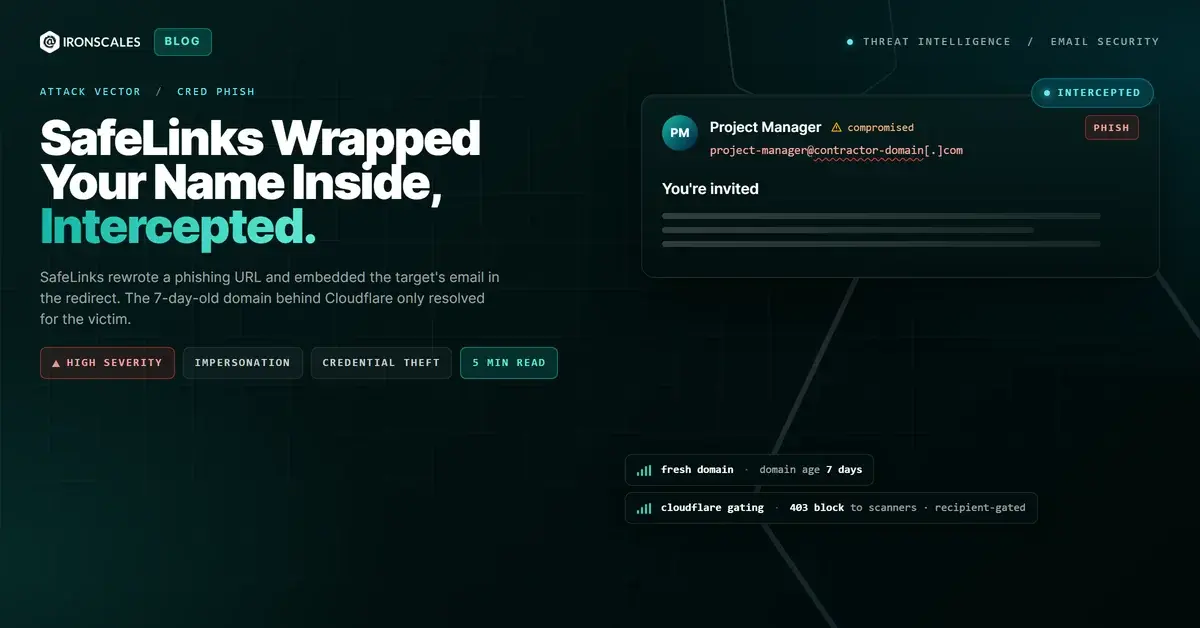
The URL in the email looked like it had already been vetted. It carried the full Microsoft SafeLinks wrapper, that long safelinks.protection.outlook.com prefix that employees in M365 environments see on every legitimate link, every day. But buried inside the SafeLinks redirect was something most recipients would never notice: the target's own email address, encoded into the URL parameters, telling the destination exactly who was clicking.
The destination behind that wrapper was invitationsh.top. Registered seven days earlier. Hidden behind Cloudflare's challenge page. Returning a flat 403 to any automated scanner that tried to check it.
SafeLinks is supposed to protect you. In this case, it packaged the phishing link with your name on it.
The Invitation That Passed Every Authentication Check
The email arrived on March 24, 2026, with the subject line "You're invited." It impersonated a Greenvelope digital invitation, complete with a pink envelope graphic reading "For you!" and a "Powered by Greenvelope" footer. The visual branding was convincing enough that a quick glance would register it as a legitimate event invitation.
The sender was a project manager at a Sarasota-based general contracting company. The email was sent from the company's real M365 tenant: SPF passed, DKIM passed, DMARC passed, ARC passed. The sending domain has been registered since 2007. There was nothing in the authentication chain to flag.
That is the hallmark of a compromised account. The attacker sent from the sender's actual infrastructure, inheriting every authentication credential the domain had earned over 19 years.
The email went to more than 60 recipients across dozens of external organizations: architects, electricians, plumbers, surveyors, county employees, pool companies. The recipient list reads like a general contractor's entire contact book. Every one of them received a SafeLinks-wrapped URL with their own email address embedded in it.
How SafeLinks Became Part of the Attack Chain
Microsoft SafeLinks rewrites URLs in M365-protected email so they route through Microsoft's scanning infrastructure before reaching the destination. When SafeLinks processes a link, it can embed the recipient's email address into the rewritten URL parameters. The intent is tracking and protection. The effect, in this case, was personalization of a phishing link.
Here is why that matters.
A standard phishing link points every recipient to the same destination. Any sandbox or analyst can click it and see what the victim sees. But when the URL includes the target's email address, the attacker's server can validate the visitor. Intended recipient? Serve the phishing page. Automated scanner or researcher? Return a block page.
The destination, invitationsh.top, sat behind Cloudflare. Security tools received a 403 "Sorry, you have been blocked" response. A records resolved to Cloudflare anycast addresses (172[.]67[.]170[.]25 and 104[.]21[.]39[.]88). No credential form was visible to scanners. The attack only activates for the right person, in the right browser, at the right time.
This is recipient-gated phishing infrastructure, and SafeLinks handed the attacker the gating key.
See Your Risk: Calculate how many threats your SEG is missing
Seven Days Old, Zero Reputation, Maximum Cover
WHOIS records for invitationsh.top show a creation date of March 22, 2026, at 22:05 UTC, via NameSilo. The phishing email landed on March 24. The domain was two days past registration when it was weaponized.
The domain name is a typosquat: "invitationsh" instead of "invitations." Close enough to pass a wrapped URL at a glance. Nameservers pointed to Cloudflare. DNSSEC was unsigned. No SPF, DMARC, or meaningful DNS records existed.
This is disposable infrastructure. Register cheap on a .top TLD, point to Cloudflare for bot gating, run the campaign, walk away. The domain had no reputation history, so URL reputation databases returned neutral verdicts. That neutral verdict is all the attacker needs to survive the SafeLinks scan at delivery time.
According to the FBI IC3 2024 Internet Crime Report, phishing and its variants remain the most-reported cybercrime category. Newly registered domains are a persistent factor: the Microsoft Digital Defense Report 2024 notes that attackers increasingly use cloud services and CDN proxying to obscure malicious infrastructure from scan-time analysis.
The Signals the Gateway Did Not Weigh
SPF passed. DKIM passed. SafeLinks wrapped the URL. The gateway's job, as far as it was concerned, was done.
But IRONSCALES Adaptive AI and community intelligence evaluated a different set of signals. Across the IRONSCALES platform, this email triggered multiple behavioral anomalies:
- Destination domain age: 7 days old at time of delivery, with no prior reputation
- Cloudflare gating: The destination returned a 403 to automated analysis, a pattern strongly associated with credential harvesting infrastructure
- Mass external distribution: A single sender from a construction company sending identical party invitations to 60+ recipients across unrelated industries
- Visual brand impersonation: Greenvelope branding and formatting used to create false familiarity
- Recipient email embedded in URL: The SafeLinks-rewritten link carried the recipient's identity, enabling target-specific content gating
Themis classified the email as phishing with high confidence. The email was quarantined across affected mailboxes within seconds of delivery, before any recipient could reach the gated destination. The Verizon 2024 DBIR reports that 74% of breaches involve a human element. In this case, the human element never got the chance to engage.
Defending Against Weaponized URL Rewriting
URL rewriting was designed to add protection. Attackers have turned it into social engineering. The wrapper itself is now the trust signal.
- Do not treat SafeLinks-wrapped URLs as inherently safe. The wrapper means the URL was scanned at delivery. It does not mean the destination is safe at click time.
- Flag newly registered domains behind CDN gating as high-risk. Under 30 days old, proxied through Cloudflare, returning 403 to scanners. Each factor alone is ambiguous. Together they are diagnostic.
- Investigate mass-recipient patterns from single senders. A construction PM sending party invitations to 60+ external recipients across unrelated industries is not normal. Behavioral baselines catch what authentication cannot.
- Deploy M365-augmented email security that evaluates post-delivery behavior. Scan-at-delivery cannot catch infrastructure that gates content by recipient identity.
- Educate users that URL wrappers are not safety endorsements. A wrapped URL has been scanned, not cleared. The CISA phishing guidance recommends verifying destination domains independently.
Indicators of Compromise
| Type | Indicator | Context |
|---|---|---|
| Domain | invitationsh[.]top | Attacker-controlled phishing destination, registered 2026-03-22, Cloudflare-proxied |
| URL | hxxps://invitationsh[.]top/home | Final destination behind SafeLinks wrapper |
| IP | 172[.]67[.]170[.]25 | Cloudflare anycast address resolving for attacker domain |
| IP | 104[.]21[.]39[.]88 | Cloudflare anycast address resolving for attacker domain |
| Nameserver | mitchell.ns.cloudflare[.]com | DNS infrastructure for attacker domain |
| Nameserver | rayne.ns.cloudflare[.]com | DNS infrastructure for attacker domain |
| Sender | Jmehaffie@sccsarasota[.]com | Compromised or abused legitimate account (Southern Cross Contracting) |
| Hash (MD5) | 97b8ec2db2d966730f0b0f9920339b63 | Attached PNG image used as social engineering lure |
MITRE ATT&CK: T1566.002 Spearphishing Link, T1036.005 Masquerading: Match Legitimate Name or Location, T1204.001 User Execution: Malicious Link
Sources: IRONSCALES platform analysis; Verizon 2024 DBIR; Microsoft Digital Defense Report 2024; FBI IC3 2024 Internet Crime Report; CISA Cybersecurity Advisories; MITRE ATT&CK
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)