Table of Contents
A Domain That Didn't Exist at Breakfast Delivered Phishing by Lunch
At 07:55 UTC on March 30, 2026, someone registered the domain ddorrgkgtv[.]com through Namecheap with full WHOIS privacy protection. Nine hours and twenty-four minutes later, a phishing email carrying a link to that domain landed in a K-12 school district mailbox in Virginia. The domain had no history, no reputation, and no reason to exist. It was built for one purpose and would be abandoned before anyone could investigate.
The email passed SPF. It passed DKIM. It passed ARC. It passed DMARC. Every authentication check returned green because the message was sent from a legitimate Microsoft 365 tenant belonging to a Russian technical university. The attacker didn't spoof the infrastructure. They owned it, or at least they owned someone's account on it.
According to the FBI's 2024 Internet Crime Report, phishing remains the most reported cybercrime category, with educational institutions ranking among the most frequently compromised sectors for account takeover. This case shows exactly why.
The Attack Chain: Compromised Account, Clean Authentication, Disposable Infrastructure
The email arrived from the address selfsz@stud[.]kai[.]ru, a student account at Kazan National Research Technical University (KNITU-KAI) in Russia. The display name read "[Display Name]," a name the recipient's organization had previously seen associated with a completely different email address at a Brazilian university (uninove[.]edu[.]br). That mismatch is the first crack in the facade: the attacker picked a familiar display name and sent it from an unrelated account on the other side of the world.
The subject line was casual: "Re: PHOTO (1)." The body was a single sentence: "I am 100% sure this pic will bring vivid flashbacks," followed by a bare URL. No attachment. No HTML formatting tricks. No urgency language. Just a conversational hook and a link.
Below the message body sat a professional-looking bilingual signature block: "Stay online with KAI!" with links to kai[.]ru (the university's legitimate website, registered since 1997), its VK social page, and its official Telegram channel. The signature did real work here. It framed the malicious link within a context of institutional legitimacy. The university branding wasn't the lure. It was the cover story.
This maps to MITRE ATT&CK T1078.004 (Valid Accounts: Cloud Accounts) for the compromised university mailbox and T1566.002 (Spearphishing Link) for the delivery mechanism. The display name manipulation falls under T1036.005 (Masquerading: Match Legitimate Name or Location).
The Payload Domain: Built, Armed, and Abandoned
The actual credential harvesting destination tells the infrastructure story. The link pointed to hxxps://tmntvu[.]ddorrgkgtv[.]com:8443/AR4BhQad. Three things stand out immediately.
The domain itself is gibberish. ddorrgkgtv[.]com is a randomized string with no brand association, no dictionary words, no attempt to look legitimate. It doesn't need to. The recipient sees the display name "[Display Name]" and the kai[.]ru branding in the signature. They're not scrutinizing the URL character by character.
Port 8443 is not standard. Most legitimate HTTPS traffic runs on port 443. Port 8443 is commonly used for application servers, staging environments, and temporary web services. Attackers favor it because some URL scanning tools only evaluate links on standard ports. Microsoft's 2024 Digital Defense Report notes that threat actors increasingly use nonstandard ports and ephemeral infrastructure to evade automated analysis.
The subdomain is randomized. "tmntvu" is another throwaway string, likely generated programmatically. Combined with the randomized parent domain, this creates a URL that leaves no forensic breadcrumbs. No brand typosquatting. No SEO poisoning history. Just a clean, disposable payload delivery mechanism.
WHOIS data confirms the infrastructure timeline. The domain was registered at 07:55:32 UTC on March 30, 2026 through Namecheap. The name servers (ns1[.]siuneccdns[.]com, ns2[.]siuneccdns[.]com) point to custom DNS infrastructure rather than the registrar's defaults, suggesting pre-staged configuration. The domain still showed an "addPeriod" EPP status at the time of analysis, meaning it was within its initial registration grace period. This maps to T1584.001 (Compromise Infrastructure: Domains).
See Your Risk: Calculate how many threats your SEG is missing
Why Authentication Alone Failed
Every email authentication check passed. Here's why that didn't matter.
SPF passed because the email was sent from Microsoft's outbound protection servers (2a01:111:f403:c200::3), which are authorized senders for stud[.]kai[.]ru. DKIM passed because the message was signed with a valid selector (selector2-kairu-onmicrosoft-com) under the university's Microsoft 365 tenant. ARC passed because the intermediate hops maintained cryptographic chain integrity. DMARC passed because the From domain aligned with both SPF and DKIM.
The Verizon 2024 Data Breach Investigations Report found that 68% of breaches involved a human element. Authentication protocols verify the sending infrastructure, not the human behind the keyboard. When an attacker controls a legitimate account, the protocols do exactly what they're designed to do: confirm the email came from where it claims to come from. They just can't confirm whether the person sending it is the account owner.
This is the core problem with authentication-only defenses. They answer "did this email come from this domain?" They don't answer "should this person be sending this email to this recipient with this content?"
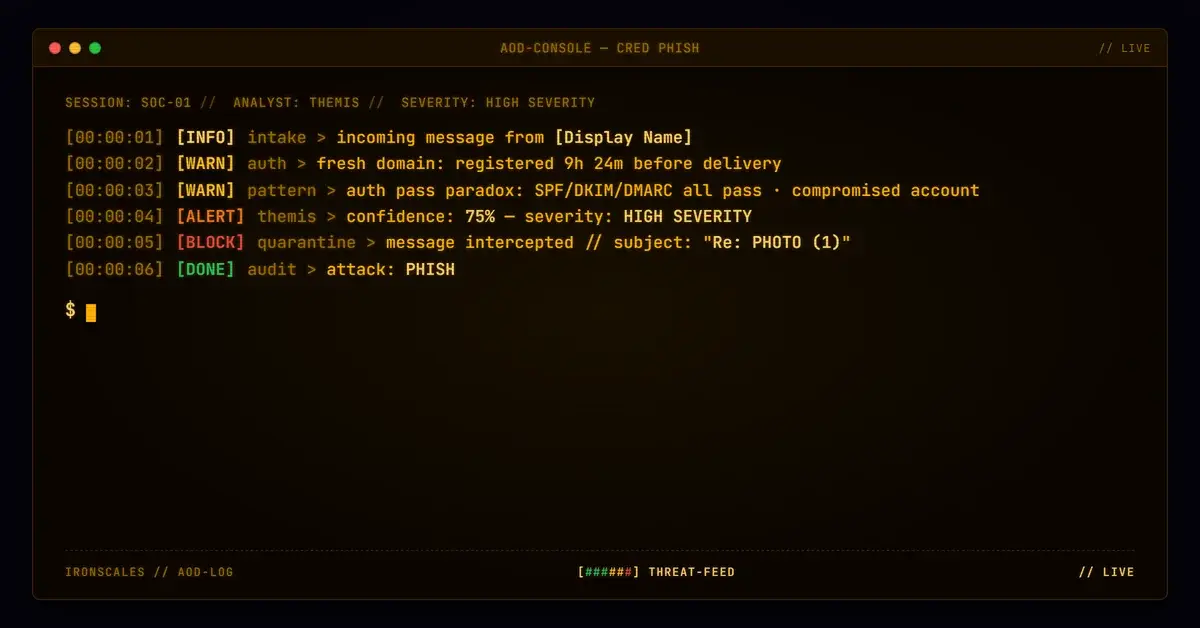
How IRONSCALES Caught It
The attack was quarantined within 36 seconds of delivery. IRONSCALES Adaptive AI identified the display name "[Display Name]" as previously associated with a different sender address. That behavioral signal, combined with community-sourced intelligence flagging similar patterns, triggered automatic quarantine before anyone could click.
No secure email gateway relying on domain reputation or authentication results alone would have caught this. The domain had no negative reputation (it was nine hours old). The authentication was flawless. The content contained no known malicious signatures. Only behavioral analysis of sender relationships detected the threat.
Indicators of Compromise
| Type | Indicator | Context |
|---|---|---|
| Domain | ddorrgkgtv[.]com | Payload domain, registered 2026-03-30 via Namecheap, privacy-protected |
| URL | hxxps://tmntvu[.]ddorrgkgtv[.]com:8443/AR4BhQad | Credential harvesting destination |
| Sender | selfsz@stud[.]kai[.]ru | Compromised student account at KNITU-KAI |
| Name Servers | ns1[.]siuneccdns[.]com, ns2[.]siuneccdns[.]com | Custom DNS infrastructure for payload domain |
| Port | 8443 | Nonstandard HTTPS port for payload delivery |
| Display Name | "[Display Name]" | Impersonation of known contact |
What to Do About It
Same-day registered domains with privacy protection delivering payloads on nonstandard ports through compromised .edu accounts represent a pattern, not an anomaly. CISA's advisories have repeatedly flagged educational institutions as high-value targets for account compromise.
Three specific actions reduce exposure to this attack pattern. First, implement display name impersonation detection that cross-references sender names against known contact addresses. Second, flag or block links to domains less than 24 hours old, regardless of authentication status. Third, treat emails from .edu domains with the same scrutiny as any external sender. The .edu TLD carries institutional trust that attackers actively exploit.
Authentication tells you where an email came from. It tells you nothing about what it intends to do when it gets there.
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)