Table of Contents
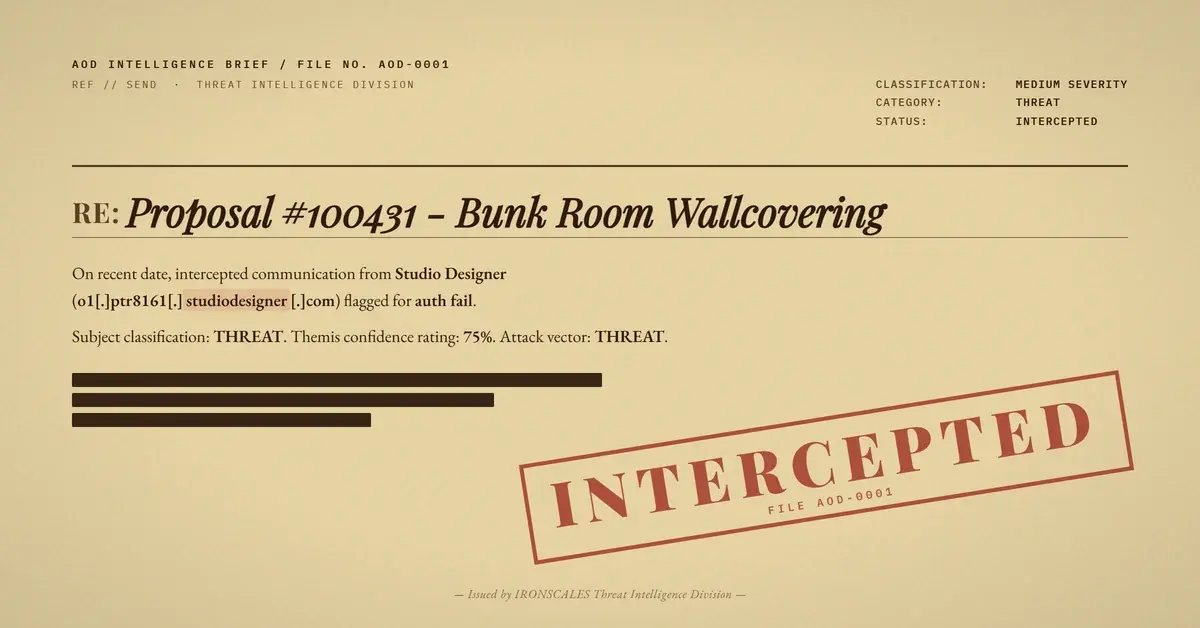
An interior design firm's client received a polished email proposing wallcovering for a bunk room renovation. The branding was pixel-perfect, the subject line referenced a real proposal number, and the "View Proposal" button linked to a legitimate SaaS client portal. On the surface, it looked like a routine business transaction between a design firm and their customer.
Beneath the surface, every layer of email authentication told a different story. DMARC failed. SPF broke across relay hops. The only valid cryptographic signature belonged to SendGrid, not the company whose name sat in the From header. This email slipped through a secure email gateway, landed in production mailboxes across the organization, and triggered no quarantine action on any of them.
The case is a textbook example of how attackers (or compromised accounts) weaponize trusted SaaS infrastructure to deliver phishing that traditional defenses can not distinguish from real business email.
Bunk Room Proposal, Broken Authentication
The email arrived on April 7, 2026, addressed to a client at an interior design firm. Subject: "Proposal #100431 - Bunk Room Wallcovering." The sender appeared to be an employee at a related design company, and the message body followed the exact template used by Studio Designer, a SaaS platform popular with interior designers for managing client proposals, invoices, and payments.
The email included Studio Designer branding, a personalized greeting, a "View Proposal" call-to-action button, and a "Powered by Studio Designer" footer. Images were hosted on Amazon S3, consistent with how the legitimate platform delivers media assets. Nothing in the visible content raised obvious red flags.
But the authentication headers painted a completely different picture.
The message originated from o1[.]ptr8161[.]studiodesigner[.]com (IP 149[.]72[.]87[.]120), a SendGrid relay subdomain configured for Studio Designer. It then passed through us1-smtp3[.]titanhq[.]com (IP 18[.]116[.]252[.]179), a TitanHQ secure email gateway in Columbus, Ohio, before reaching Microsoft 365 frontends for final delivery.
Here is where authentication collapsed:
- DKIM passed, but the signature domain was
sendgrid.net, notbluejacknational[.]com(the domain in the From header). - SPF passed at the first hop (SendGrid's IP was authorized for
sendgrid.net) but registered a softfail at the final delivery hop, where TitanHQ's relay IP was not authorized bysendgrid.net. - DMARC failed outright. The header From domain (
bluejacknational[.]com) had no alignment with either the DKIM signing domain or the SPF-authenticated domain.
According to the Microsoft Digital Defense Report 2024, email authentication failures remain one of the most reliable indicators of spoofed or compromised sender infrastructure. In this case, the compauth=none reason=905 result in Microsoft's headers confirmed that composite authentication could not validate the sender.
Three Hops, Zero Alignment
The relay path reveals exactly how authentication eroded at each stage, a pattern increasingly common in SaaS-routed phishing that exploits the gap between platform delivery and domain-level authentication.
| Hop | Host | IP | Authentication Result |
|---|---|---|---|
| 1 (Origin) | o1[.]ptr8161[.]studiodesigner[.]com | 149[.]72[.]87[.]120 | SPF pass (sendgrid.net), DKIM pass (sendgrid.net) |
| 2 (Gateway) | us1-smtp3[.]titanhq[.]com | 18[.]116[.]252[.]179 | SPF softfail (IP not in sendgrid.net SPF record) |
| 3 (Delivery) | Microsoft 365 (EOP) | Various | DMARC fail (header.from=bluejacknational[.]com) |
The Verizon DBIR 2024 found that 68% of breaches involved a human element, and attacks exploiting legitimate delivery infrastructure make that human element even more vulnerable. When the email looks right, comes from a real platform, and references real business context, the recipient has almost no visual signal that something is wrong.
The DMARC policy for bluejacknational[.]com was set to p=none, meaning even though DMARC evaluation failed, no enforcement action was taken. This is the authentication equivalent of installing a smoke detector and disconnecting the alarm. The domain owner knows about failed authentication (if they monitor reports), but nothing actually blocks delivery.
See Your Risk: Calculate how many threats your SEG is missing
The Redirect Chain Problem
Every clickable element in the email funneled through a multi-layer redirect chain: Microsoft SafeLinks rewrote the URLs, which pointed to SendGrid click-tracking endpoints (u1085689[.]ct[.]sendgrid[.]net), which redirected to client[.]studiodesigner[.]com/proposals/6856536.
Additionally, the recipient organization's TitanHQ gateway wrapped certain links through its own linklock[.]titanhq[.]com analysis endpoint, adding a fourth layer of URL processing before the user would reach any destination.
This kind of redirect stacking creates a specific problem for security teams. Each intermediary evaluates the link at scan time, but the final destination can change after delivery. An attacker controlling the SendGrid account (or the proposal resource on Studio Designer) could swap the landing page from a legitimate proposal to a credential harvesting form at any point.
The FBI IC3 2024 Annual Report documented $2.9 billion in losses from business email compromise, with invoice fraud representing a significant share. Attacks like this one, where the infrastructure is legitimate but the intent is not, are exactly the vector driving those numbers.
MITRE ATT&CK maps this behavior to T1566.002 (Spearphishing Link) for the delivery mechanism and T1078.004 (Valid Accounts: Cloud Accounts) for the likely compromise of a legitimate SaaS account used to send the email.
Defanged IOC Table
| Indicator | Type | Context |
|---|---|---|
| bluejacknational[.]com | Domain | Spoofed From header domain (DMARC fail) |
| o1[.]ptr8161[.]studiodesigner[.]com | Domain | SendGrid relay subdomain |
| u1085689[.]ct[.]sendgrid[.]net | Domain | Click tracking subdomain |
| 149[.]72[.]87[.]120 | IP | SendGrid origin server |
| 18[.]116[.]252[.]179 | IP | TitanHQ gateway relay (Columbus, OH) |
| hxxps://client[.]studiodesigner[.]com/proposals/6856536 | URL | Proposal destination page |
| bounces+1085689-0ae9[at]sendgrid[.]net | Return-Path envelope sender |
What This Case Teaches Defenders
Traditional email gateways evaluated this email and took no action. Four affected mailboxes received the message, and mitigation status across all of them showed "Email was not in Quarantine or in the Junk folder." The secure email gateway (TitanHQ) scanned it, Microsoft EOP processed it, and both let it through.
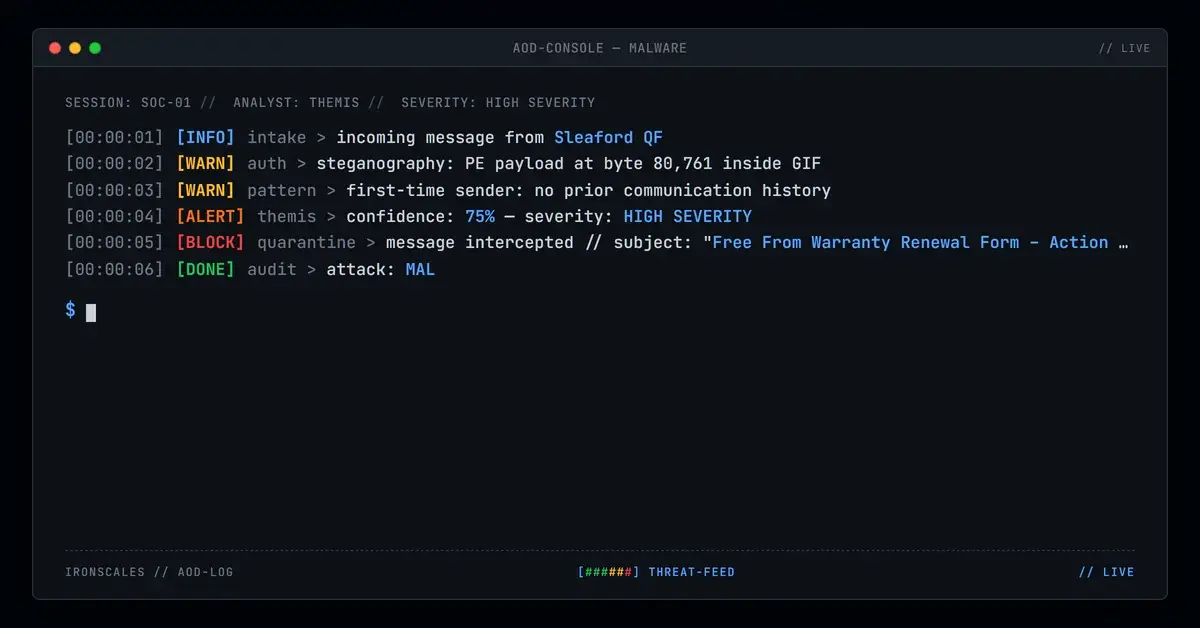
IRONSCALES Adaptive AI analyzed the email's content structure alongside sender authentication signals and identified indicators commonly associated with phishing. Themis classified the email as invoice phishing with 80% confidence, correctly flagging the authentication mismatch that every other layer missed.
This case reinforces several defensive priorities:
Enforce DMARC at p=reject. A p=none policy provides visibility but zero protection. Organizations that publish DMARC records without enforcement give attackers a free pass to spoof their domain. The CISA guidance on email authentication consistently recommends moving to reject policies after a monitoring period.
Treat SaaS-routed email as a distinct threat category. When platforms like SendGrid, Mailgun, or SES deliver email on behalf of compromised accounts, the sending infrastructure is technically legitimate. Reputation-based filtering will pass it. Only behavioral analysis and authentication alignment checks catch the gap.
Audit redirect chains, not just final destinations. Link scanning at delivery time evaluates the chain at a single point. Post-delivery link changes, account compromises, and time-delayed swaps all happen after that scan completes. Real-time link analysis at click time is the only defense that accounts for this.
Train employees on invoice and proposal phishing. The IBM Cost of a Data Breach 2024 report found that phishing remains the most expensive initial attack vector at $4.88 million per breach. Employees who handle proposals, invoices, and payments need specific training on verifying sender authenticity before clicking through to payment portals.
The email looked perfect. The branding was accurate. The proposal number was real. And every authentication check that should have stopped it was either misconfigured or ignored. That is the gap between how email security is designed to work and how it actually works in production.
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)