Table of Contents
Business email compromise losses exceeded $2.9 billion in 2024 according to the FBI IC3 Internet Crime Report 2024, with vendor and partner impersonation among the most consistently effective pretexts. Few impersonation scenarios are more targeted than one that uses a real law firm's name, a real patent number, and a real statutory deadline.
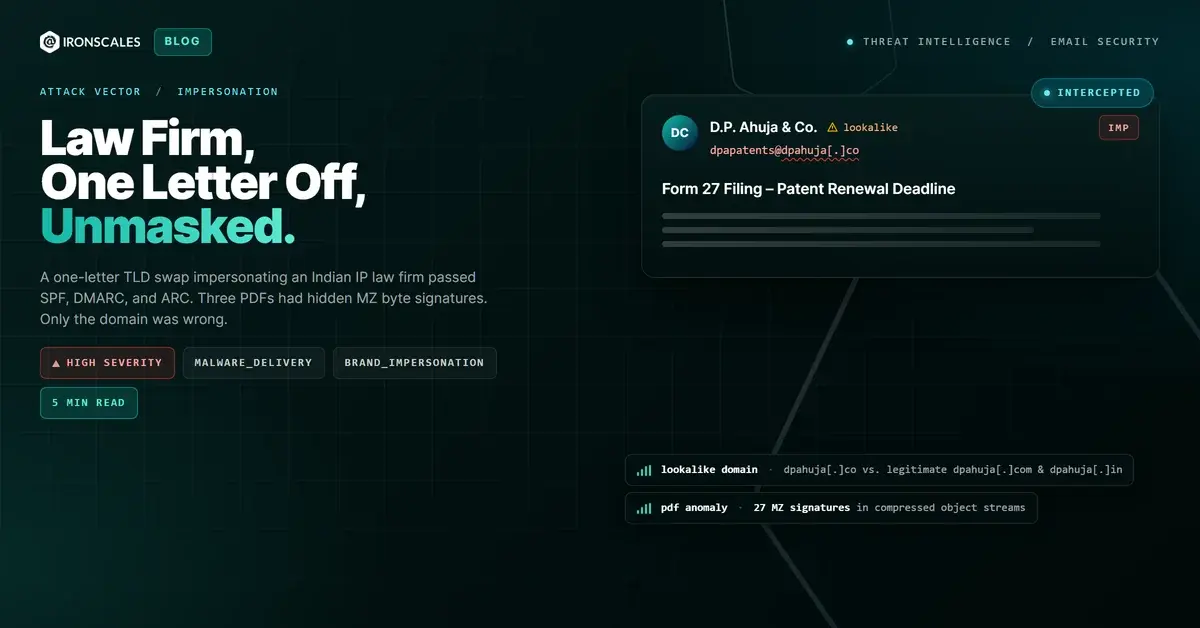
The email looked exactly like something a patent attorney would send. Letterhead from D.P. Ahuja & Co., a real and well-regarded Indian intellectual property law firm. A real patent number. The recipient's actual name in the salutation. Internal client reference codes that matched prior correspondence. A fee schedule in Indian rupees with a statutory filing deadline. Three Form 27 PDFs attached, each covering a separate Indian financial year.
Every authentication check passed. SPF: pass. DMARC: pass. ARC: pass. The message traveled through Microsoft Office 365 infrastructure without raising a flag.
The sender domain was dpahuja[.]co. The firm's actual domains are dpahuja[.]com and dpahuja[.]in. One letter. That was the entire tell.
What the Attacker Knew Before Sending
This was not a spray-and-pray campaign. The attacker demonstrated knowledge that does not come from a Google search.
The email referenced a specific granted Indian patent (Application No. 1629/KOLNP/2007), the correct patentee of record, and the internal client reference number used by the targeted organization's IP department. It named the patent department contact by first and last name in the attention line. It was addressed to three specific people at the organization (the director, a colleague, and a third contact), suggesting the attacker had access to prior correspondence from the legitimate firm.
The social engineering hook was real compliance pressure. Under the Indian Patents Act, patentees must file annual Form 27 statements (Working Reports) for all renewed granted patents by September 30 each year. The statutory nature of this requirement is not widely known outside IP legal circles. The attacker knew it, and used it accurately. The fee schedule quoted (INR 13,000 for year one, INR 8,700 for each subsequent year, total INR 30,400) is consistent with what a real firm of this type would charge.
This maps to MITRE ATT&CK T1566.001 (Spearphishing Attachment) combined with T1036.005 (Masquerading: Match Legitimate Name or Location) for the lookalike domain technique. The goal appears to have been to get the recipients to return filled-in forms containing detailed commercial exploitation data for the patent (information that carries significant competitive and legal value) to an attacker-controlled address, while potentially paying a fraudulent invoice in the process.
How the Domain Infrastructure Was Built
The legitimate firm operates from dpahuja[.]com and dpahuja[.]in. The [.]in domain has DKIM and DMARC configured. The [.]com domain is the publicly published website.
The attacker registered dpahuja[.]co and configured it with valid SPF and DMARC records pointing to Microsoft-hosted infrastructure. The sending IP (2a01:111:f403:c408::3) is a Microsoft outbound protection server, meaning the message originated from an Office 365 tenant set up under the lookalike domain. This is a deliberate choice: using Microsoft infrastructure means the relay chain looks entirely legitimate and PTR records resolve cleanly.
Because SPF authorizes the sending IP for dpahuja[.]co and DMARC passes under that same domain, the email clears the authentication layer without issue. Authentication passes tell you that the infrastructure is authorized for the claimed domain. They do not tell you whether that domain is the one the recipient thinks they are dealing with. The Microsoft Digital Defense Report 2024 highlights lookalike domain registration as one of the most consistently successful initial access techniques precisely because authentication controls treat the lookalike domain as legitimate on its own terms.
The impersonation signal Themis flagged: the sender address dpapatents@dpahuja[.]co closely matches an existing contact at dpapatents@dpahuja[.]sg, a related legitimate entity. That similarity, combined with the domain not matching the firm's primary TLDs, is what elevated the sender risk score to high.
Inside the PDFs
Three PDFs were attached. Each nominally covers a different Indian financial year (2023-2024, 2024-2025, 2025-2026) and is formatted as a fillable AcroForm with 48 fields.
The first PDF is where it gets interesting forensically. Static analysis returned a clean verdict overall: no JavaScript, no OpenAction launch, no embedded files in the traditional sense, not encrypted. But the scanner found 27 occurrences of MZ byte signatures inside compressed object streams.
MZ (hex: 4D 5A) is the magic bytes that mark the start of a Windows PE executable. Finding them inside a PDF's compressed cross-reference or object streams is an anomaly. It does not automatically mean a functional executable is hiding inside, but it means object-level extraction is required before the file can be conclusively cleared. The absence of a nearby PE header (PE\x00\x00) around each MZ occurrence is reassuring, but compressed object streams can obscure the full context. The static scanner flagged this as medium-severity, warranting offline YARA analysis and sandbox detonation of the extracted streams.
The second PDF could not be independently verified by the sandbox at analysis time (file path access issue). The third was produced by Ghostscript, contains AcroForm fields, and scanned clean with no anomalies.
No in-body URLs were present. No credential harvesting links in the PDFs. The attack vector is data exfiltration via returned forms and fraudulent payment, not a traditional phishing link.
See Your Risk: Calculate how many threats your SEG is missing
Indicators of Compromise
| Type | Indicator | Context |
|---|---|---|
| Sender email | dpapatents@dpahuja[.]co | Lookalike of legitimate dpahuja[.]com / dpahuja[.]in |
| Sender domain | dpahuja[.]co | Registered TLD swap. Legitimate domains are dpahuja[.]com and dpahuja[.]in |
| Sending IP | 2a01:111:f403:c408::3 | Microsoft outbound protection (PNZPR01CU001.outbound.protection.outlook[.]com) |
| Attachment hash | 20476c7258b685f1b302f666e491b122 | WORKING REPORT FORM 27 FOR FY 2023-2024.pdf (contains MZ byte anomalies) |
| Attachment hash | dd58b11a2fcb8aa819be4d853fba6026 | WORKING REPORT FORM 27 FOR FY 2025-2026.pdf (unverified) |
| Attachment hash | 7ea20cd7d542568662a8ed56a0a1f2ed | WORKING REPORT FORM 27 FOR FY 2024-2025.pdf (clean) |
| External image | hxxp://wptn[.]com/signature/DPA_logo[.]jpg | Logo loaded from third-party domain, not the firm's own infrastructure |
What This Attack Means for IP-Holding Organizations
According to the Verizon 2024 DBIR, pretexting and social engineering attacks that rely on impersonating a known trusted party (a vendor, a law firm, an institutional contact) are more likely to succeed than generic phishing because they exploit an existing relationship the target already trusts. IBM's 2024 Cost of a Data Breach Report puts the average cost of a social engineering breach at $4.55 million, with targeted impersonation attacks causing above-average losses due to delayed detection.
Organizations that hold intellectual property and work with external patent counsel face a specific threat model that most security teams underestimate. IP departments receive routine correspondence from law firms around the world containing: real case numbers, real deadlines, named contacts, payment requests, and attached forms. The volume and legitimacy of that communication creates an environment where a well-researched impersonation blends in almost perfectly.
The attack in this case required no malicious link, no credential harvesting page, and no macro-enabled document. The attacker's goal was to receive completed forms containing detailed commercial patent working data and, in all likelihood, to issue a follow-up payment request for the quoted fees. Both objectives are accomplished through normal email reply behavior.
For organizations with IP portfolios, the controls that matter are not the ones checking whether a PDF contains JavaScript. They are the ones that flag when the sending domain does not match the expected vendor domain, even when every authentication header is green. Behavioral AI that tracks domain history, detects lookalike registration patterns, and surfaces sender anomalies before a message reaches the inbox is what catches this class of attack.
IRONSCALES detected the domain discrepancy through similarity analysis and elevated the sender risk score accordingly. The affected mailboxes were quarantined before any forms were returned or payments initiated.
One letter in a TLD is enough surface area for a targeted attack against someone who handles your patents. The authentication layer will not save you.
Related attacks
| Attack | What happened |
|---|---|
| When 'Release from Quarantine' Is the Attack | A fake quarantine digest weaponized email security workflows, embedding JWT tokens in 'Allow' and 'Manage' buttons while masking one link's true... |
| The Email That Passed Every Security Check (Because Adobe Sent It) | A phishing campaign targeting school district staff used Adobe's own sending infrastructure, real DKIM signatures. |
| Every Link Is Amazon: How Legitimate Infrastructure Becomes the Phishing Payload | A phishing email passed SPF, DKIM, and DMARC with a perfect compauth score of 100. |
| The Phishing Infrastructure Was Canva. The Delivery Mechanism Was Canva. The Authentication Was Canva. | An attacker signed up for Canva, built a phishing lure as a design, and used the platform's own sharing feature to deliver it. |
| When the Sender Domain Is Also the Phishing Kit Host: Dual-Purpose Domain Compromise | An attacker compromised a legitimate manufacturing company domain and used it two ways at once: as the authenticated sending address and as the host for... |
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)