Table of Contents
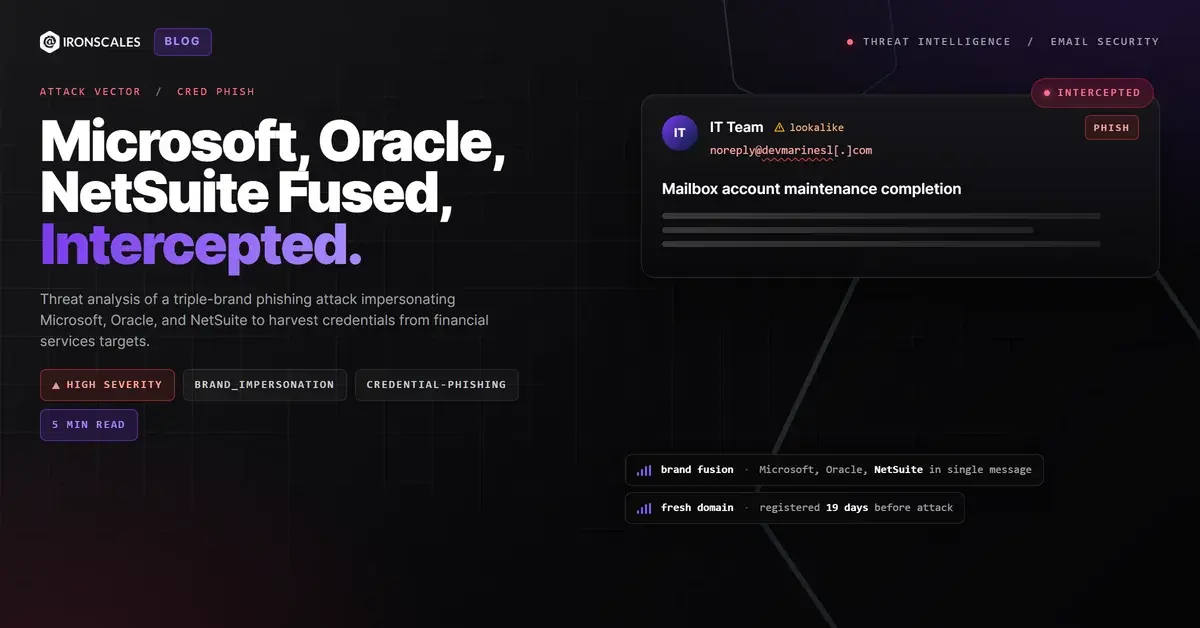
A credential-harvest email landed in the inbox of a Chief Mortgage Officer at a mid-market financial institution on March 11, 2026. The message passed DKIM. It passed SPF. It cleared the organization's Secure Email Gateway (SEG). And it carried the branding of three separate enterprise vendors: Microsoft, Oracle, and NetSuite, in a single message body.
That kind of brand layering is not accidental. It is a deliberate evasion technique designed to exploit how both humans and machines evaluate email trust. See how IRONSCALES catches what your gateway misses.
Three Brands, One Payload, Zero Legitimate Senders
The email presented a Microsoft logo in the header banner with Segoe UI typography and the four-color tile mark. The body referenced a "Mailbox account" maintenance completion (language that mimics Microsoft 365 admin notifications). The footer, however, was a pixel-perfect replica of Oracle NetSuite's corporate email template: NetSuite logo, Oracle copyright, social media icons linking to legitimate NetSuite profiles, and a 2300 Oracle Way address block.
The signature? A fabricated internal IT team name, matching neither Microsoft nor Oracle and bearing no relationship to the target organization.
This triple-brand construction exploits a cognitive weakness: recipients who recognize any of the three brands are more likely to trust the message, even when the combination makes no logical sense. For automated detection systems, the presence of legitimate Oracle and NetSuite URLs in the footer dilutes the overall malicious-link ratio, a tactic that helps phishing emails bypass traditional gateway filters.
Anatomy of a Disposable Attack Domain
The sender address traced to a .cz domain registered on February 20, 2026, just 19 days before the attack. The attacker configured DKIM signing and routed the message through Amazon Simple Email Service (SES) infrastructure in the sa-east-1 (Sao Paulo) region, which provided:
- Valid DKIM signatures for both the sender domain and
amazonses[.]com - SPF pass at the originating SES IP (
23[.]249[.]215[.]4) - DMARC bestguesspass because the newly registered domain had no published DMARC policy, Microsoft Exchange Online Protection (EOP) applied a permissive "best guess" evaluation
This is the infrastructure playbook that IBM X-Force documented in their 2025 Threat Intelligence Index: register a domain, configure basic authentication records, plug it into a legitimate cloud email service, and launch before reputation systems catch up. According to CISA advisory AA23-131A, abuse of cloud-hosted infrastructure for phishing delivery has become one of the most persistent threats to enterprise email security.
The Verizon 2025 DBIR found that phishing remains the initial access vector in over a third of breaches, with credential harvesting as the primary objective. This attack fits that profile exactly.
The CTA Redirects to a Compromised Third Party
The call-to-action button, styled in Microsoft's signature blue, was wrapped in a Microsoft SafeLinks URL. Unwrapping it reveals the true destination: hxxps://devmarinesl[.]com/cdn/default/.
That domain was registered in 2012 and belongs to an entity unrelated to Microsoft, Oracle, or NetSuite. The /cdn/default/ path suggests either a compromised web application or a purpose-built credential-capture page staged on legitimate infrastructure, a technique mapped in MITRE ATT&CK as T1608.005 (Stage Capabilities: Link Target).
By routing the harvest page through an established domain rather than the freshly registered sender domain, the attacker avoids URL-reputation blocklists that key on domain age. The legitimate Oracle and NetSuite footer links, all pointing to real oracle[.]com, netsuite[.]com, and social media destinations, further dilute automated link-risk scoring.
Targeted Delivery to a High-Value Financial Executive
This was not a spray-and-pray campaign. The sender relation analysis confirmed several targeting indicators:
- First-time sender: no prior communication between the sender domain and the target organization
- No bidirectional relationship: the recipient had never emailed this domain, and the domain had never contacted anyone else in the organization
- Recipient profile: a C-suite officer in mortgage banking, a role with direct access to wire transfer approvals, customer PII, and loan documentation systems
- Personalization: the email body included an account identifier and name, lending false specificity to the maintenance-completion pretext
The FBI IC3 2024 Internet Crime Report reported $2.77 billion in Business Email Compromise (BEC) losses, with financial services among the top three targeted sectors. Credential harvesting against C-suite banking executives is a common precursor to BEC wire fraud: the attacker captures credentials first, then pivots to internal account takeover operations.
How Themis Detected What the SEG Passed
IRONSCALES Themis Adaptive AI classified this email as phishing at 85% confidence and automatically quarantined it across four affected mailboxes before any recipient clicked the CTA. Request a demo to see Themis in action.
The detection relied on multi-signal correlation that no single rule could replicate:
| Detection Signal | What It Caught |
|---|---|
| New-domain fingerprinting | Sender domain registered 19 days prior; first-time sender to organization |
| Brand-consistency analysis | Microsoft header + Oracle/NetSuite footer + unrelated IT team signature (three-way identity mismatch) |
| CTA destination mismatch | Primary link resolves to an unrelated third-party domain, inconsistent with any claimed brand |
| Community threat intelligence | Pattern matched previously reported phishing campaigns with high community confidence |
| Behavioral anomaly scoring | External sender to C-suite recipient with no prior communication history |
This multi-layered detection approach maps directly to MITRE ATT&CK T1566.002 (Spearphishing Link) and demonstrates why AI-powered email security must operate beyond authentication-header parsing. Domain-based Message Authentication, Reporting, and Conformance (DMARC), Sender Policy Framework (SPF), and DomainKeys Identified Mail (DKIM) all passed here. The attack was technically authenticated but operationally malicious.
What Defenders Should Do Now
Check your new-domain policies. If your SEG is not flagging or quarantining emails from domains less than 30 days old, you are leaving the front door open. This domain was 19 days old and sailed through.
Audit DMARC "bestguesspass" behavior. Microsoft EOP applies bestguesspass when no DMARC record exists. Treat this as a yellow flag, not a green light, especially when combined with a first-time sender.
Correlate brand signals across the entire message. Header, body, footer, and CTA destination should tell a consistent story. When they do not, that inconsistency is a detection opportunity. The Microsoft Digital Defense Report 2024 noted that brand impersonation remains one of the most prevalent phishing techniques in enterprise environments.
Prioritize protection for high-value roles. Chief financial officers, mortgage officers, and treasury managers are disproportionately targeted because their credentials unlock wire-transfer and account-management workflows. Start a free trial of IRONSCALES to see which executives in your organization are most at risk.
---
MITRE ATT&CK Mapping
| Technique ID | Technique Name | Application in This Attack |
|---|---|---|
| T1566.002 | Phishing: Spearphishing Link | Email with credential-harvest link targeting financial executive |
| T1585.002 | Establish Accounts: Email Accounts | Newly registered .cz domain configured with DKIM/SPF for phishing delivery |
| T1036.005 | Masquerading: Match Legitimate Name or Location | Microsoft, Oracle, and NetSuite branding impersonation |
| T1608.005 | Stage Capabilities: Link Target | Credential-capture page hosted on compromised third-party domain |
| T1078 | Valid Accounts | Intended post-compromise objective: harvested credentials for account access |
Indicators of Compromise
| Indicator | Type | Context |
|---|---|---|
capitalmarketresearch[.]cz | Domain | Sender domain: registered 2026-02-20 |
support@capitalmarketresearch[.]cz | Email Address | Sender address |
hxxps://devmarinesl[.]com/cdn/default/ | URL | Credential-harvest destination (defanged) |
23[.]249[.]215[.]4 | IP Address | Amazon SES sending IP (sa-east-1) |
44[.]206[.]213[.]130 | IP Address | Votiro relay IP (legitimate gateway, contextual only) |
d215-4.smtp-out.sa-east-1.amazonses[.]com | Hostname | SES outbound mail server |
0103019cddf2eeba-a9bc1ee0-39d0-4e1b-863b-7cbcd931323a-000000@sa-east-1.amazonses[.]com | Message-ID | Unique email message identifier |
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)