Table of Contents
In the latest evolution of phishing tactics, attackers are taking a low-tech approach that’s proving remarkably effective. By disguising CAB files as harmless GZ archives, threat actors are slipping malware past defenses, triggering native Windows execution, and achieving inbox delivery with high success rates.
It’s not a zero-day. It’s not a new malware strain. But it works—because it abuses trust in file formats, user expectations, and overlooked gaps in email analysis.
In just 48 hours, this technique showed up in 217 emails across 86 companies. And based on what we’re seeing in the wild, it’s likely just the beginning.
The Setup - An Innocent-Looking GZ File
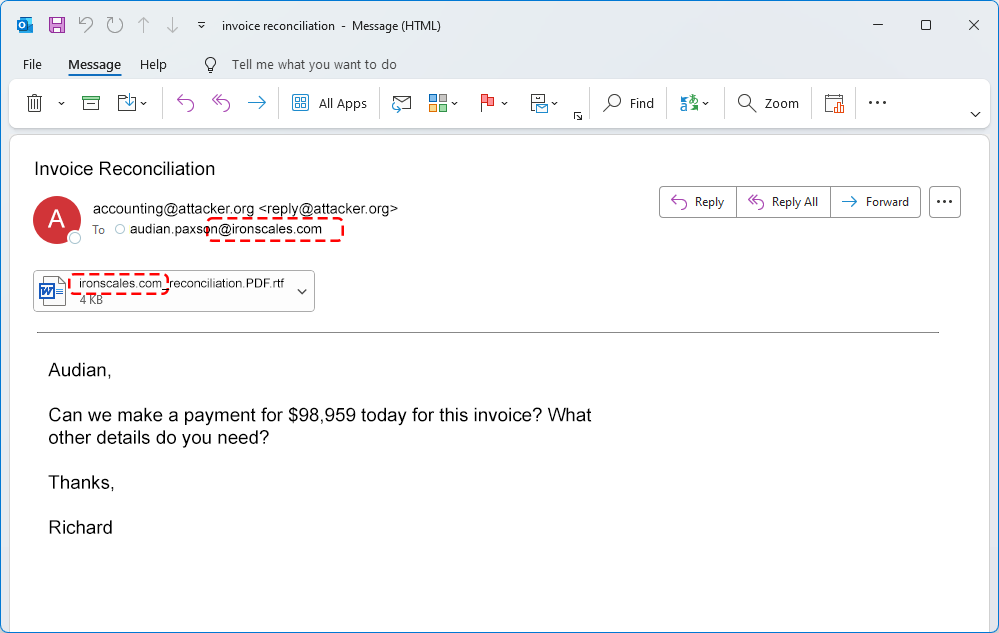
At first glance, the email attachment looks routine:
PO_ZB895885748.GZ
The filename is typical of a purchase order or invoice, nothing unusual for recipients in procurement or technical operations. But while it says .gz, the file is actually a .cab archive. No complex spoofing here...just a renamed file.
There’s no MIME manipulation either. The email’s content-type remains "multipart/mixed" — a standard header for attachments in most business email.
This subtle misdirection plays on a simple but powerful assumption: that .gz means "compressed and safe." But when the archive is extracted, the truth is revealed.

Inside the Archive (A Scripted Execution Chain)
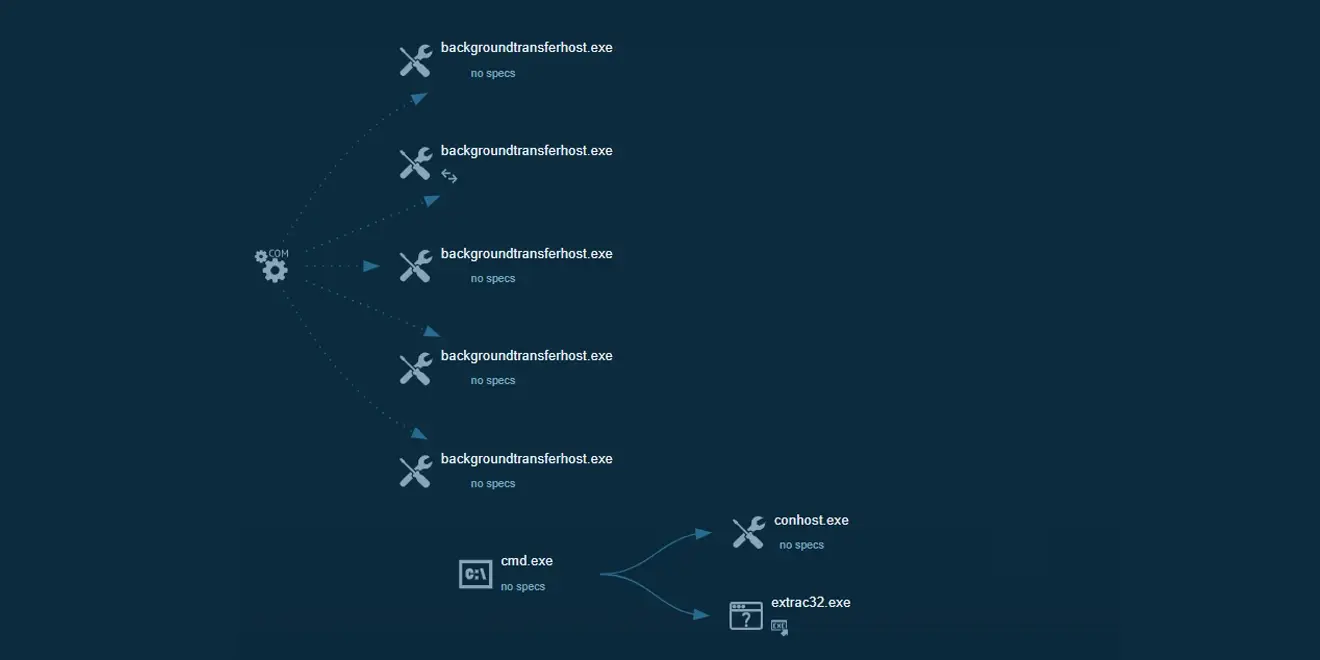
Once the CAB file is opened, particularly via tools like WinRAR, the user is exposed to its real payload: a Windows command script (.cmd) designed to launch a hidden execution chain.
This script spawns:
cmd.execonhost.exewith0xffffffff -ForceV1parameters to hide the console window- PowerShell v1 in stealth mode
- A call to
extrac32.exe, a legitimate Windows utility frequently abused by malware
The result is a stealthy, script-based compromise that avoids dropping obvious binaries and blends into system activity.

What’s particularly dangerous here is how little user interaction is needed. In some environments, simply extracting the archive in a GUI tool like WinRAR can trigger execution—without requiring a double-click on the script itself.
Encoded Sender, Familiar Story
The deception doesn’t stop at the file. The attacker also encoded the sender’s display name using Base64, like this:
=?UTF-8?B?...?= <info@...>
To the user, the name appears as a plausible person, matching the "PO" theme of the message. But under the hood, this technique helps bypass detection systems that look only at the decoded display string and not the raw header.
It’s a small trick, but when combined with a believable name and a familiar attachment, it increases the odds the email will be trusted (and the file opened).
For M365 and GWS Admins: Make sure your anti-phishing protections decode and inspect Base64-encoded display names. Native configurations may only analyze the rendered text.
Detection Gaps and Low Visibility
Here’s where it gets concerning. Despite the payload being executable and behaving like malware, detection was inconsistent at best.
In one scan, the file was analyzed by 60 different antivirus engines. Only six flagged it as malicious.

This isn’t unusual. Signature-based tools often struggle with scripts and native tools like conhost.exe or extrac32.exe, which are commonly used by Windows itself.
That’s exactly what this campaign is counting on, low-prevalence tactics that fall into the gray space between “suspicious” and “allowed.”
Here's a snapshot of this particular campaign:
- Incidents: 84 in 2 days
- Targeted Companies: 86
- Total Emails: 217+
- File Name:
PO_ZB895885748.GZ(actually CAB) - MIME Type: multipart/mixed (unchanged)
- Payload:
.cmdscript →cmd.exe→conhost.exe→powershell v1 - AV Detections: 6 of 60 engines
While the overall volume remains relatively low, this attack technique is clearly gaining traction. We observed more incidents using this rare file extension tactic in a two-day burst than in the last two full years combined. So...yeah, attackers are testing and scaling this type of attack method.
What to Watch For
Even mature security stacks can miss attacks like this. Here’s what defenders (especially those managing email in native M365 or GWS) should be aware of:
File-type validation
Don’t trust extensions or MIME types. Instead, inspect file content (magic bytes) to determine the true file format.
Block rare archives
If .cab, .img, or .iso files aren’t part of your business workflows, consider flagging or quarantining them by default.
Go beyond signature detection
Behavioral analysis and sandboxing can catch tactics that traditional AVs miss—especially when native OS tools are abused.
Decode headers
Ensure encoded sender names and subjects are fully decoded before anti-phishing analysis. Obfuscation at the header level is often overlooked.
Final Thoughts
This campaign didn’t need a novel exploit to succeed. It relied on user trust, native tooling, and subtle evasion techniques, exactly the kinds of gaps that persist in hybrid environments or email systems relying on default rules.
Whether you’re using AI-driven threat detection or managing security manually in cloud-native environments, it’s worth taking a second look at how your stack handles low-prevalence, high-deception threats like this.
We'll continue tracking this campaign and will share deeper analysis, indicators, and behavior profiles as more samples are analyzed.
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)