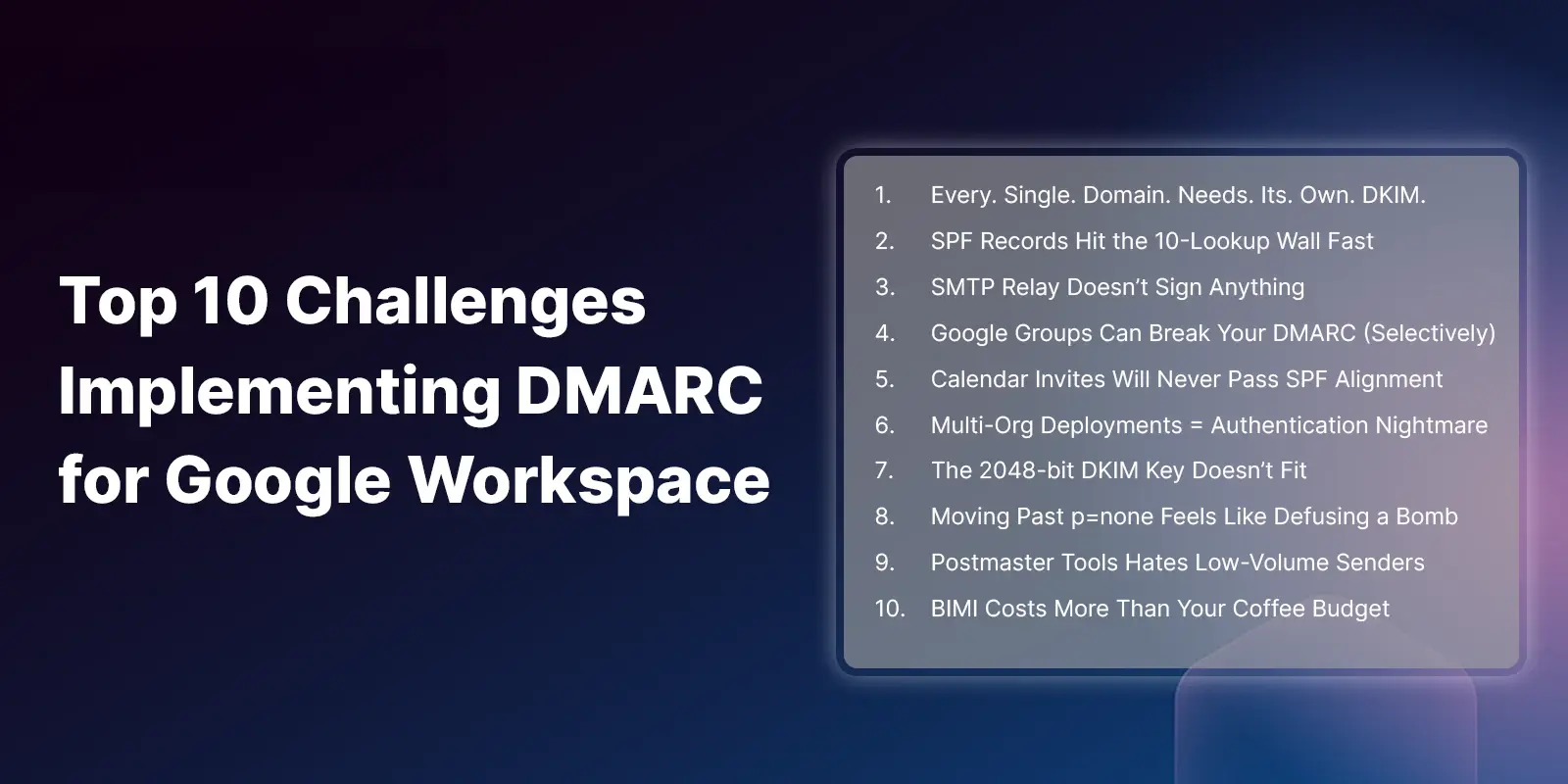
Top 10 Challenges Implementing DMARC in GWS
.webp?width=100&height=100&name=PXL_20220517_081122781%20(1).webp)
Let's talk about the real story behind Google's DMARC maze, shall we? (You might want to go pour yourself a cup of coffee, this’ll take ~14 minutes, but it’s the guide I wish I had.)
Read more
/Concentrix%20Case%20Study.webp?width=568&height=326&name=Concentrix%20Case%20Study.webp)