Table of Contents
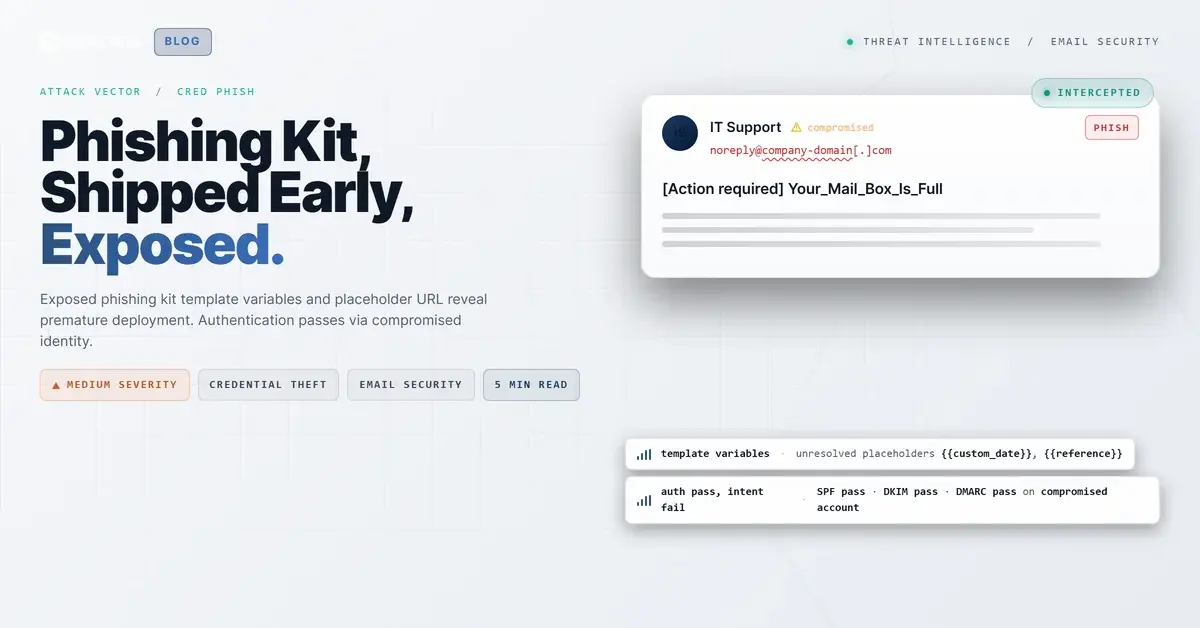
The subject line read: [Action required] Your_Mail_Box_Is_Full. The email body referenced a CPL_Agreement_ #. And the single link in the message pointed to hxxp://vm/. This was not a sophisticated attack. It was a phishing kit that shipped before the operator finished setting it up.
In April 2026, IRONSCALES intercepted a credential harvesting attempt that arrived from a first-time sender flagged as high risk. The email passed SPF, DKIM, and DMARC authentication, meaning the sending account was not spoofed. It was compromised. And the unresolved template variables in the body gave security analysts something attackers rarely provide: a look at the kit before obfuscation.
The Kit Before It Was Ready
Phishing kits are commodity tools. They are sold, shared, and reused across campaigns with minimal customization. The typical workflow is straightforward: the operator loads the kit, configures target-specific variables (dates, reference numbers, recipient names, credential harvesting URLs), and launches the campaign. What happened here is that the operator launched before configuring.
The template string CPL_Agreement_ # uses double-brace syntax common in templating engines like Jinja2, Mustache, and Handlebars. These variables were meant to be populated with a date and a unique reference number that would make the email appear tailored to the recipient. Instead, the raw tokens were delivered to the inbox.
The Verizon 2024 Data Breach Investigations Report found that phishing was involved in 36% of breaches, with credential theft as the primary objective. Most of those attacks use kits exactly like this one. The difference is that competent operators test before sending.
Mailbox Full: The Urgency That Works
The subject line, [Action required] Your_Mail_Box_Is_Full, targets a specific user anxiety. Mailbox storage warnings are routine IT communications that most employees have encountered and acted on without a second thought. The [Action required] prefix mimics the tagging format used by IT helpdesk systems and automated alerts.
According to the FBI IC3 2024 Annual Report, phishing remains the most reported cybercrime category with over 298,000 complaints in 2024. Storage-related pretexts are particularly effective because they create urgency without triggering the "too good to be true" skepticism that financial lures sometimes produce. The recipient is not being offered something. They are being told they are about to lose something.
The underscore formatting (Your_Mail_Box_Is_Full) is another kit artifact. Many phishing kits use underscores as word separators in subject lines because the kit's template engine processes them more reliably than spaces in certain configurations. To a casual reader, the underscores might look slightly odd but not alarming.
See Your Risk: Calculate how many threats your SEG is missing
The Placeholder That Tells the Story
The email contained a single link labeled "VM" pointing to hxxp://vm/. This is not a real URL. It is a placeholder, likely the default value in the kit's link field before the operator inserts the actual credential harvesting domain. In a fully configured deployment, this would point to a lookalike login page hosted on attacker infrastructure.
The placeholder reveals something important about the attack pipeline. This operator either sent a test email to a live target list by mistake, or they are running at a volume where quality control does not exist. Neither scenario is reassuring. The MITRE ATT&CK framework documents Spearphishing Link (T1566.001) as one of the most common initial access techniques, and commodity kits lower the barrier to entry so far that operators do not need to understand what they are sending.
Authentication Without Authorization
The email passed SPF, DKIM, and DMARC. That means the sending infrastructure was authorized by the domain's DNS records, the DKIM signature validated against the domain's public key, and DMARC alignment confirmed both protocols matched the From header domain. This is consistent with a compromised account (MITRE ATT&CK T1078, Valid Accounts).
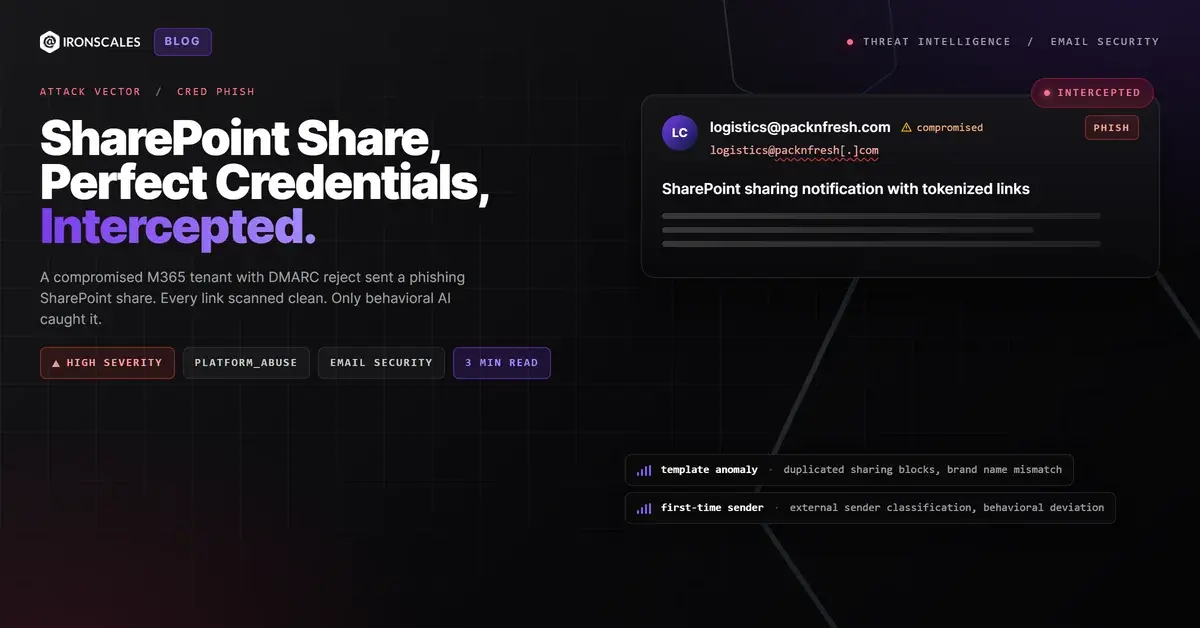
The Microsoft Digital Defense Report 2024 notes that compromised accounts are increasingly used as launch platforms for phishing campaigns because they inherit the domain's full authentication posture. A SEG that relies on authentication results as a primary trust signal will give this email a clean pass. The authentication is technically correct. The intent behind it is not.
Account compromise for phishing delivery maps to MITRE ATT&CK T1586.002 (Compromise Accounts: Email Accounts). The attacker gains access to a legitimate mailbox, uses it to send authenticated phishing emails, and moves on before the account owner notices.
MITRE ATT&CK Mapping
- T1566.001 (Phishing: Spearphishing Link): Email containing a link (placeholder) intended for credential harvesting.
- T1586.002 (Compromise Accounts: Email Accounts): Compromised email account used to deliver authenticated phishing.
- T1078 (Valid Accounts): Legitimate credentials used to access and abuse the sending platform.
Indicators of Compromise
| Type | Indicator | Context |
|---|---|---|
| Subject Line | [Action required] Your_Mail_Box_Is_Full | Mailbox storage urgency pretext |
| Template Variable | CPL_Agreement_ # | Unresolved phishing kit tokens |
| URL | hxxp://vm/ | Placeholder credential harvesting link |
| Authentication | SPF/DKIM/DMARC pass | Compromised authenticated identity |
| Sender Context | First-time sender, high risk | No prior communication with recipient |
What a Broken Kit Still Teaches
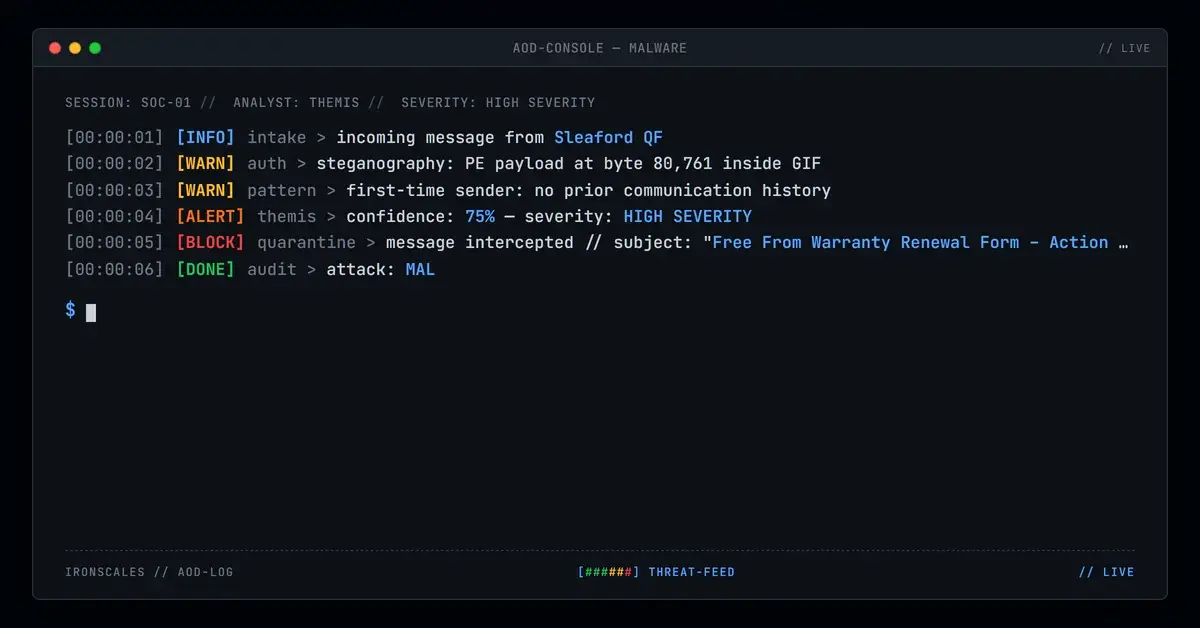
Themis, the IRONSCALES Adaptive AI, flagged this message before any user interaction. The detection was not based on URL reputation (the placeholder URL has no reputation to check) or content filtering (the template variables are not in standard blocklists). It was based on behavioral signals: first-time sender, anomalous message structure, and communication patterns inconsistent with the recipient's normal email flow.
The exposed template variables are a gift to defenders. They reveal the kit's naming convention (CPL_Agreement), its variable syntax (double-brace Mustache/Jinja2 style), and its intended pretext (a compliance or legal agreement with a dated reference). According to CISA's phishing guidance, sharing these indicators across security communities strengthens collective defense. This particular kit will ship again, likely with the variables properly filled in next time. The question is whether your detection can identify the pattern when the surface-level mistakes are corrected.
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)