Table of Contents
"Priority: You have 3 messages on hold." The exclamation mark icon appeared next to the message in Outlook before the recipient even read the subject line. The X-Priority header was set to 1. The Importance header was set to High. And the sender had never emailed this organization before.
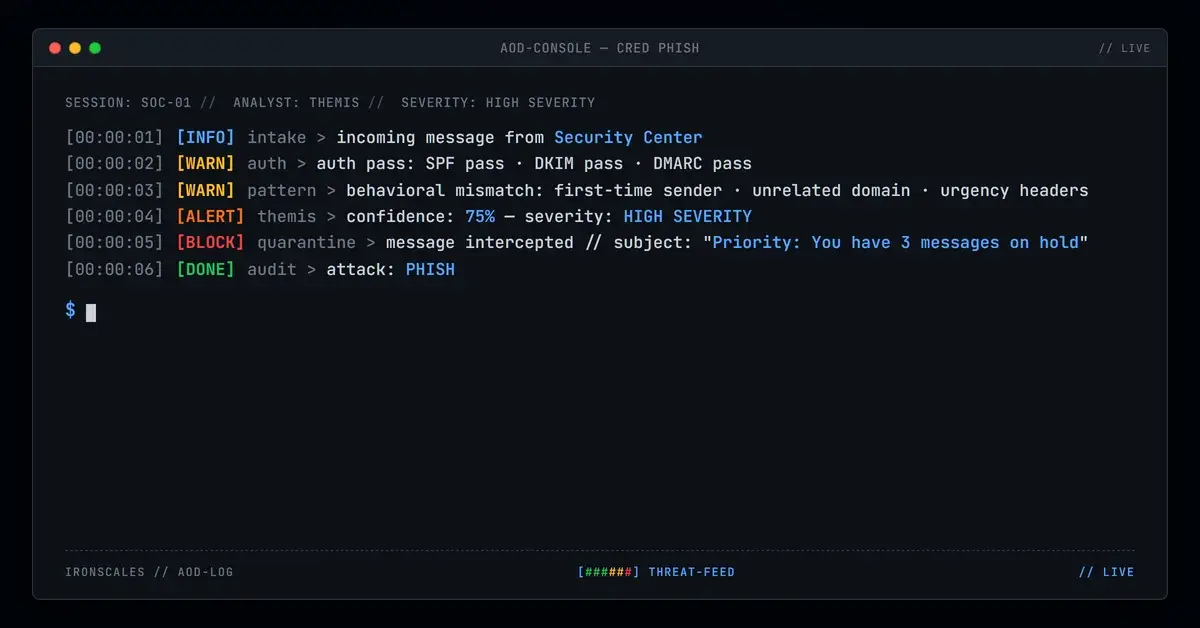
In April 2026, IRONSCALES flagged a credential harvesting campaign that weaponized urgency at every layer. The email arrived from reddscups[.]com[.]au, an authenticated Australian domain, but branded itself as a "Security Center" notification. The call-to-action buttons routed through crm[.]webguruz[.]in, a CRM platform used as a redirect hop to obscure the final credential harvesting destination. Every authentication check passed. The message was quarantined anyway.
The Verizon 2024 Data Breach Investigations Report found that credentials are the most common data type compromised in breaches, involved in over 50% of incidents. Attacks like this one show why: the lure is simple, the infrastructure is layered, and the authentication is clean.
Urgency as a Technical Weapon
Most phishing relies on social engineering to create urgency through language: "Act now," "Your account will be suspended," "Immediate action required." This campaign went further. It embedded urgency into the email's technical headers.
The X-Priority: 1 and Importance: High headers are not cosmetic. They instruct email clients to display visual priority indicators. In Microsoft Outlook, this means a red exclamation mark appears in the inbox list view before the recipient opens the message. In mobile clients, the email may be sorted or highlighted differently. The recipient sees urgency before reading a single word.
Combined with the subject line ("Priority: You have 3 messages on hold") and a "Security Center" sender identity, the psychological pressure stacks. The recipient is being told that something security-related requires their immediate attention, and their email client is confirming the urgency with a visual flag. According to the Microsoft Digital Defense Report 2024, social engineering attacks that combine multiple urgency signals have significantly higher click-through rates than single-vector approaches.
The CRM Redirect Problem
The call-to-action links in the email pointed to crm[.]webguruz[.]in, a CRM (Customer Relationship Management) platform subdomain. This is not the final destination. It is a redirect hop.
The technique exploits how URL reputation systems work. When a Secure Email Gateway (SEG) or link scanner evaluates a URL, it checks the domain's reputation. CRM platforms, by design, have high reputation scores. They send millions of legitimate transactional emails daily. A link pointing to a CRM subdomain does not trigger the same risk scoring as a link to a newly registered domain or a known phishing host.
The redirect chain from crm[.]webguruz[.]in passed through at least one additional hop before reaching the credential harvesting page. Microsoft Dynamics scanning provided partial coverage of the chain but did not follow it to termination. This is a known limitation. URL scanners that evaluate only the first hop miss the payload entirely.
See Your Risk: Calculate how many threats your SEG is missing
The MITRE ATT&CK framework documents this as T1204.001 (User Execution: Malicious Link), where the attacker depends on user interaction with a link that appears legitimate but delivers a malicious payload through obfuscation or redirection.
Authentication Passed. Behavior Did Not.
The sending domain reddscups[.]com[.]au had valid SPF records, a properly configured DKIM signature, and a passing DMARC policy. From a protocol perspective, the email was authorized. This is the same pattern seen across ESP and compromised-domain phishing: the infrastructure is legitimate, but the intent is not.
What stood out was the behavioral profile. This sender had never communicated with the target organization. The domain, an Australian commercial entity, had no business relationship with the recipient. The "Security Center" branding bore no relationship to the sending domain's actual identity. And the combination of urgency headers with a first-time sender profile is a high-confidence indicator of social engineering.
Themis, the IRONSCALES Adaptive AI, evaluated these signals in combination. No single indicator was definitive. A first-time sender is not inherently suspicious. Urgency headers are used in legitimate communications. CRM redirect links appear in marketing emails constantly. But the convergence of all three, from an unrelated Australian domain claiming to be a security notification, produced a behavioral signature that warranted quarantine.
Across the IRONSCALES platform, this pattern has accelerated. The FBI IC3 2024 Annual Report documented over 298,000 phishing complaints in 2024, with credential harvesting identified as the primary objective in the majority of cases. The IBM Cost of a Data Breach 2024 report found that stolen credentials as an initial attack vector resulted in an average breach cost of $4.81 million.
MITRE ATT&CK Mapping
- T1566.001 (Phishing: Spearphishing Link): Email containing a malicious link disguised behind a CRM redirect chain.
- T1036.005 (Masquerading: Match Legitimate Name or Location): "Security Center" branding on an unrelated commercial domain.
- T1204.001 (User Execution: Malicious Link): Attack depends on the user clicking through the redirect chain to the credential harvesting page.
Indicators of Compromise
| Type | Indicator | Context |
|---|---|---|
| Sender Domain | reddscups[.]com[.]au | Authenticated sending domain (Australian) |
| Sender Identity | "Security Center" | Spoofed brand identity in display name |
| Redirect URL | crm[.]webguruz[.]in | CRM platform used as redirect hop |
| Header | X-Priority: 1 | Urgency manipulation |
| Header | Importance: High | Urgency manipulation |
| Subject | "Priority: You have 3 messages on hold" | Urgency pretext |
| Sender History | First-time sender to target organization | No prior communication relationship |
The Stack That Urgency Builds
This attack is effective because it stacks psychological pressure across multiple channels simultaneously. The subject line creates concern. The priority headers trigger a visual alert. The "Security Center" branding invokes authority. And the "3 messages on hold" claim creates a specific, countable problem that feels solvable with one click.
Each layer is individually unremarkable. Together, they form a conversion funnel optimized for the same goal as any marketing campaign: get the recipient to click. The difference is that the landing page harvests credentials instead of leads. Organizations relying on SEG-level filtering alone miss attacks like this because every technical indicator, authentication results, domain age, sender reputation, passes inspection. The behavioral layer, the question of whether this communication pattern makes any sense at all, is the only thing that catches it. When a domain that sells cups in Australia starts sending security center notifications to organizations it has never contacted, something is wrong. The protocols cannot see that. Behavioral analysis can.
Related attacks
| Attack | What happened |
|---|---|
| Sign Here, Get Phished: Inside an Adobe Sign Lure With a Multi-Hop Redirect to Credential Theft | An Adobe Sign e-signature lure routed recipients through a multi-hop redirect chain ending at fameklinik[.]com. |
| DocuSign Plus Invoice: A 12-Day-Old Domain and an esvalabs Redirect Chain That Scanners Missed | A phishing campaign combined DocuSign branding with an invoice thread pretext, sent from a 12-day-old privacy-protected domain via Amazon SES. |
| When the Phishing Kit Ships Early: Exposed Template Variables Reveal Attack Infrastructure | A premature phishing kit deployment exposed raw template variables in the subject line and a placeholder URL. |
| Funding Agreement, Forged Approval: How a Three-Layer Redirect Chain Targeted Finance Leadership | A phishing campaign impersonating a document-signing platform targeted a VP of Finance with a forged funding agreement. |
| The PDF Scanner Couldn't Open the Attachment (But the Victim Could) | A password-protected PDF bypassed every automated scanner because none of them could open it. |
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)