Table of Contents
The development team lead had been trading emails with the vendor since Thursday. Pricing questions. Subscription tiers. Custom domain configurations. Four days of perfectly normal SaaS procurement, the kind of thread that engineering managers process on autopilot. Then Monday's reply arrived with a link that wasn't what it seemed.
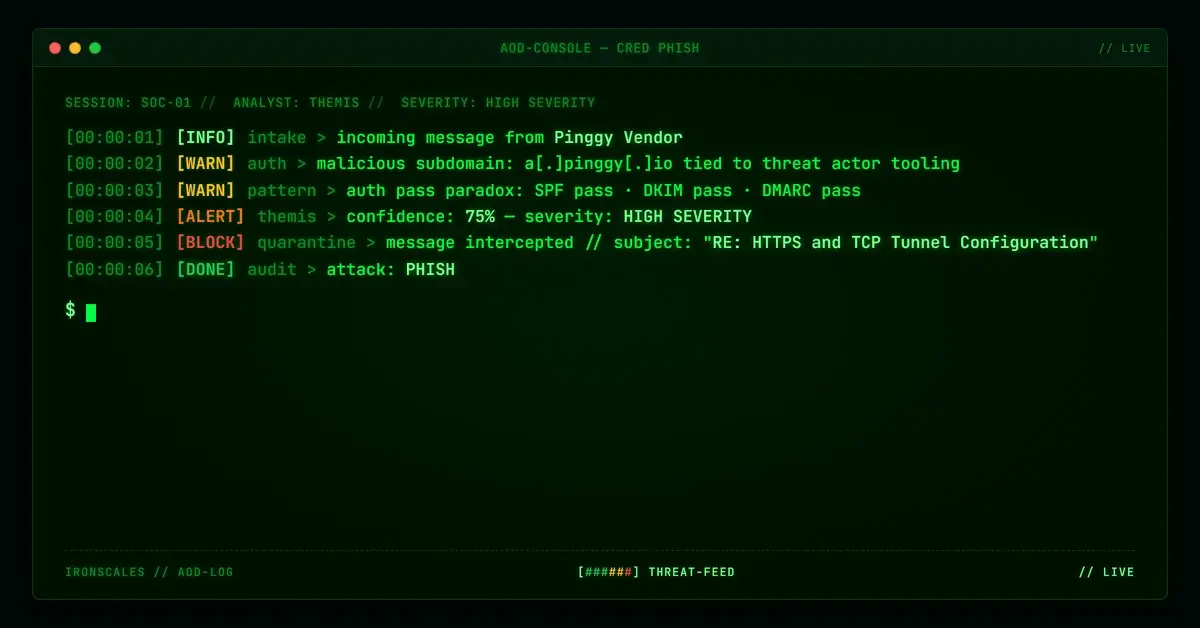
The email passed SPF (Sender Policy Framework). It passed DKIM (DomainKeys Identified Mail). It passed DMARC (Domain-based Message Authentication, Reporting, and Conformance). And buried in a paragraph about firewall allowlisting sat a subdomain tied to known threat actor tooling.
Four Days of Normal Conversation, Then a Link That Wasn't
The development team lead (call him David) had been emailing back and forth with a tunneling service vendor since Thursday morning. Pricing questions. Subscription tiers. Custom domain configurations. The kind of mundane SaaS procurement thread that fills engineering inboxes every week.
By Sunday, David had asked about running HTTPS and TCP tunnels simultaneously. The vendor replied Monday morning with a straightforward answer: separate subscriptions required, and here are the subdomains to whitelist in your network proxy.
One of those subdomains was a trap.
The link to a[.]pinggy[.]io, buried in a paragraph about firewall allowlisting, pointed to infrastructure tied to known threat actor tooling. Sandbox reports had already flagged PowerShell artifacts using the same brand name. The subdomain itself dropped HTTPS connections and returned nothing on HTTP probes (behavior consistent with an endpoint waiting for the right victim at the right time).
And this email passed every authentication check your Secure Email Gateway (SEG) trusts: SPF, DKIM, and DMARC, all green. If you're still relying on those signals alone to determine whether an email is safe, this calculator shows what you're likely missing.
Why This Thread Was the Perfect Weapon
This wasn't a cold phishing email from a stranger. It was the fifth message in a legitimate vendor conversation, a thread that included real pricing data, real product documentation links, and real answers to real questions.
The attacker (or the compromised vendor account) exploited something no authentication protocol can measure: conversational trust.
According to the 2024 Verizon Data Breach Investigations Report, 68% of breaches involved a human element, and social engineering through trusted channels is the fastest-growing vector. The FBI's IC3 2023 report documented $2.9 billion in Business Email Compromise (BEC) losses, with vendor impersonation and thread hijacking among the most common tactics.
This case hits multiple MITRE ATT&CK techniques simultaneously:
- T1566.002: Spearphishing Link. A malicious URL delivered inside a targeted email conversation
- T1199: Trusted Relationship. Exploiting an existing vendor-customer communication channel
- T1572: Protocol Tunneling. Using tunneling infrastructure to host or proxy attack payloads
- T1036.005: Masquerading. The malicious subdomain mimics the legitimate vendor's naming conventions
The thread also exposed an active access token in the quoted reply history. Even if the link itself were blocked, an attacker with access to this thread had a credential ready for reuse. Microsoft's 2024 Digital Defense Report found that token theft attacks increased by 111% year over year, and email threads are a primary harvesting ground.
The Authentication Paradox That SEGs Can't Solve
Here's the part that keeps security teams up at night: every gateway signal said this email was clean.
| Check | Result |
|---|---|
| SPF | PASS (136[.]143[.]188[.]12 authorized for pinggy[.]io) |
| DKIM | PASS (signature verified, d=pinggy[.]io) |
| DMARC | PASS (p=quarantine, action=none) |
| ARC | PASS (chain intact through Zoho and Microsoft relays) |
The sending IP traced to Zoho's mail infrastructure in the United States. The domain had been registered since 2021 through Porkbun LLC, five years of clean history. No traditional reputation system would flag this sender.
This is the fundamental limitation of authentication-only defenses. CISA's email authentication guidance rightly encourages organizations to deploy SPF, DKIM, and DMARC, but these protocols answer one question: "Is this sender who they claim to be?" They do not answer: "Is this content dangerous?"
When the sender is who they claim to be and the content is dangerous, traditional email security gateways have no mechanism to intervene. This is the gap that Adaptive AI-powered detection was built to close, analyzing content, link behavior, and contextual signals independent of sender reputation. If your current stack can't do that, see it in action.
Three Mailboxes, Five Seconds, Zero User Intervention
IRONSCALES Themis, the Adaptive AI engine analyzing every inbound message, didn't care about the SPF result. It evaluated the email on what mattered:
Link behavior analysis flagged a[.]pinggy[.]io as malicious. The subdomain's failure to respond to HTTPS probes, combined with threat intelligence tying the brand to sandboxed malicious artifacts (including a PowerShell payload named pinggy.ps1), produced a risk score that triggered immediate action.
Community intelligence correlated the sender's behavioral patterns with previously reported spam and bulk-mail activity across IRONSCALES' global network, signals invisible to any single organization's SEG.
Content-context analysis identified the promotional language patterns embedded in what appeared to be a vendor support thread, a mismatch that raised the behavioral confidence score.
Themis classified the email as phishing with 90% confidence and quarantined it across all three affected mailboxes in under five seconds. No user saw the message. No one clicked the link. No token was harvested.
The IBM Cost of a Data Breach Report 2024 found that organizations using AI-driven security tools contained breaches 108 days faster than those without. In this case, containment wasn't measured in days; it was measured in seconds.
What This Attack Teaches Security Teams
This incident isn't exotic. It's the new normal. Attackers don't need to spoof domains or craft pixel-perfect brand impersonations when they can ride inside legitimate vendor threads with fully authenticated infrastructure.
Three things to act on now:
- Audit your tunneling and developer tool vendors. Services that create public endpoints from private infrastructure (tunneling, ngrok-style tools, reverse proxies) are increasingly abused as phishing infrastructure. Monitor subdomains, not just root domains.
- Treat exposed tokens in email threads as compromised. If an access token, API key, or credential appears in any email thread, revoke it immediately, regardless of sender legitimacy. Email threads are forwarded, replied to, and stored in ways that extend exposure far beyond the original conversation.
- Deploy detection that evaluates content independently of authentication. SPF, DKIM, and DMARC are necessary but insufficient. You need AI-powered email security that analyzes link behavior, content patterns, and community signals in real time, especially for messages that pass every traditional check.
The line between vendor and threat actor has never been thinner. When authentication says "trust" and content says "danger," your security stack needs to know which signal to follow. Start a free trial to see how IRONSCALES handles it.
---
Indicators of Compromise (IOCs)
| Indicator | Type | Context |
|---|---|---|
a[.]pinggy[.]io | Domain | Malicious tunneling subdomain; failed HTTPS probes; tied to sandboxed threat artifacts |
136[.]143[.]188[.]12 | IP Address | Sending IP (Zoho infrastructure, US); authorized for pinggy[.]io SPF |
pinggy[.]io | Domain | Legitimate tunneling service; subdomains abused for malicious hosting |
pro[.]pinggy[.]io | Domain | Additional subdomain referenced in email; unscanned |
sender4-op-o12[.]zoho[.]com | Hostname | Originating mail relay |
Related attacks
| Attack | What happened |
|---|---|
| The Auth0 Developer Tenant That Passed Every Security Check (Because It Was Real) | An attacker weaponized Auth0's free developer tenant to build a phishing chain that passed DKIM, DMARC, and every link scanner. |
| The Lab Result Notification That Every Security Check Approved (Because the Platform Was Real) | A credential harvest targeting healthcare portal logins arrived through bridgeinteract.io, a legitimate HIPAA-adjacent patient engagement platform. |
| A Google Redirect, a Monday.com Tracker, and a Fake NDA: Credential Harvesting Through Trusted Infrastructure | A DocuSign NDA impersonation routed its primary CTA through a three-hop redirect chain: Google.com to Monday.com tracking service to a Zimbabwean domain. |
| The Credential Page Was Real. The Domain Was One Extension Off. | A credential-harvesting email impersonating a healthcare vendor used a .net domain instead of the vendor's legitimate .com domain. |
| The Quarantine Portal That Looked Exactly Like the Real One | A fake quarantine notification delivered a pixel-perfect replica of a quarantine management portal, complete with JWT-embedded action links. |
Explore More Articles
Say goodbye to Phishing, BEC, and QR code attacks. Our Adaptive AI automatically learns and evolves to keep your employees safe from email attacks.

/case_study_thumb_telit.webp?width=1136&height=639&name=case_study_thumb_telit.webp)







/Leadership%20Headshots/Audian%20Paxson%20Headshot%201000x1000%20032026.webp?width=100&height=100&name=Audian%20Paxson%20Headshot%201000x1000%20032026.webp)